Patch Tuesday May 2014
Last updated on: October 27, 2022
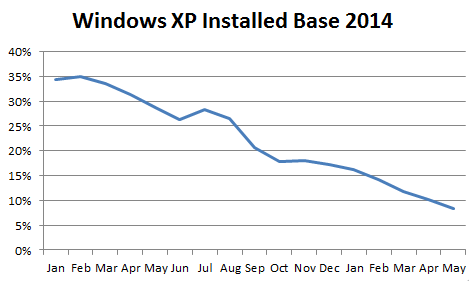
It’s May 2014 and time for the first Microsoft Patch Tuesday after the end-of-life of Windows XP and Office 2003. Microsoft is publishing eight bulletins, and Adobe is publishing two software updates. The majority of the vulnerabilities addressed in the updates probably affect Windows XP/Office 2003 (our guess internally is eight out of the lineup of 10), but only users who have Microsoft’s extended support agreement can get the patches. Fortunately, the XP user base continues to shrink. In our enterprise user statistics we are now looking at under 10% (close to 8%) installed:
But back to the currently supported operating systems. At the top of our list this month is Microsoft Internet Explorer’s Bulletin MS14-029. Unlike what we expected, this is another surgical fix, similar to the out-of-band MS14-021 from May 1. MS14-021 addressed the zero-day CVE-2014-1776, which had been found in the wild by FireEye on April 26. In a similar fashion MS14-029 addresses CVE-2014-1815, which was detected as having attacks in the wild by the Google Security Team. For good measure Microsoft also included MS14-021/CVE-2014-1776 in this bulletin, so if you have not installed it yet, you can just install MS14-029 and address both issues at the same time. The remaining issues in Internet Explorer that were originally scheduled (PWN2OWN, for example) will have to be included in next month’s bulletin. Note that you need the last cumulative update to IE installed for this update to be applicable.
MS14-024 and MS14-025 are next on our list. They both provide fixes for issues that have been abused by malware, pen-testers and hackers alike. MS14-024 is a new version of the MSCOMCTL DLL that has ASLR set, an easy fix for the developers to implement (basically a recompile), but one that took extensive testing as this DLL is widely used. With ASLR set ON the DLL attacks that were addressed by MS12-027, MS12-060, MS13-096 and MS14-017 could have been avoided. MS14-025 prevents the storage of credentials in Group Policies, where they are relatively easily accessed by hackers and pen-testers alike. Both fixes are highly recommended and will go a long way to making your setup more robust.
Next on our list are the patches from Adobe for Adobe Reader (APSB14-15) which addresses the vulnerabilities found on OWN2OWN and Adobe Flash (APSB14-14http://helpx.adobe.com/security/products/reader/apsb14-16.html). Flash has been especially popular with attackers. In addition, both Reader and Flash have “priority ratings” of 1, which indicates that Adobe considers them to be easily exploitable once the patches have been reverse engineered. Note that Adobe also does not provide patches for Windows XP anymore after this one last release in May.
If you run SharePoint you need to take a look at MS14-022, especially if you expose SharePoint to the Internet. An attacker that can upload files to SharePoint can cause a remote code execution on the server and take over control of the machine. SharePoint administrators need to address this one as quickly as possible.
Getting back to Windows XP, we believe that the majority of vulnerabilities applies to the OS that recently lost support after its 12-year run. In essence, we can assume that any vulnerability that for Windows Server 2003 is applicable to XP as well. For this month, that means at least: MS12-029 (IE), MS12-024 (ASLR), MS12-025 (Group Profile), MS14-023 (not XP but Office 2003), Adobe Reader and Flash. However, as we have seen, its market share is shrinking. If that tendency continues we will be close to 0% in another four months, even though we will probably see the inevitable flattening at the long-tail of the machine substitution. Stay tuned for more on the subject on this blog.