Device Vulnerabilities Fixed: Garrettcom Magnum Series
Last updated on: September 6, 2020
Would you buy a cellphone with a hardcoded password? Definitely not. I wouldn’t either.
But as is sometimes the case with non-mass-market devices, security can be overlooked in favor of convenience, even if in retrospect it’s clearly a mistake to do so. Fortunately, this story has a happy ending, thanks to responsible disclosure and quick vendor response.
 As a vulnerability research engineer at Qualys, I routinely audit various devices, and today Qualys is releasing information on three new vulnerabilities I found on the Garrettcom Magnum 6k and Magnum 10k Series managed switches.
As a vulnerability research engineer at Qualys, I routinely audit various devices, and today Qualys is releasing information on three new vulnerabilities I found on the Garrettcom Magnum 6k and Magnum 10k Series managed switches.
These devices had the following security issues:
- The firmware contained hardcoded password linked to a privileged account used for support and maintenance operations. A malicious person who discovered the password and had access to the device could execute commands or shut down the device. Even worse, a Shodan search indicated that at least seven of these devices are connected to the Internet and publicly discoverable.
 The firmware also contained hardcoded RSA private keys and certificate files. An attacker having access to these certificates and keys could not only decrypt the HTTPS secure traffic but also log in via ssh without a username/password to any device running the same version of the firmware.
The firmware also contained hardcoded RSA private keys and certificate files. An attacker having access to these certificates and keys could not only decrypt the HTTPS secure traffic but also log in via ssh without a username/password to any device running the same version of the firmware.- Less interesting but still important to fix were some cross-site scripting (XSS) vulnerabilities.
In accordance with Qualys’ responsible disclosure policy, we notified the vendor and ICS-CERT, the vendor has released fixes for the Magnum 6k series and for the Magnum 10k series, and now we are going forward with coordinated disclosure following publication of the ICS-CERT advisory.
About Garretcom Magnum
Garrettcom Magnum devices are a range of managed switches specially designed and hardened to withstand some of the most grueling industrial environments with high EMI, extended temperature range and significant atmospheric contamination. GarrettCom estimates the affected products are deployed primarily in the United States with a small percentage in Europe and Asia. According to GarrettCom, the devices are deployed across several U.S. critical infrastructure sectors including critical manufacturing, defense industrial base, energy, water, and transportation. According to their website the devices are used in the power industries, smart grid backbones, intelligent traffic systems and other industries / systems.
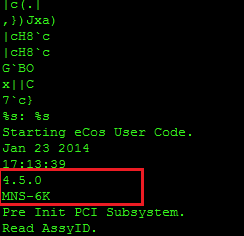
All tests were performed on firmware (Rel_6K_A450.bin) version 4.5.0 for Magnum 6k series as shown in the image below of the string output for the firmware binary.
I found three classes of vulnerabilities.
1. CVE-2015-3959: Hardcoded Passwords (A5: Security Misconfiguration)
CVSS Score: AV:N/AC:L/Au:N/C:C/I:N/A:N (how to read)
Firmware with hardcoded credentials or backdoors leave any device at a huge risk of getting hacked if an attacker gains knowledge of this information, allowing complete control of the device, as the accounts are generally high privileged accounts meant for support or maintenance operations. The firmware contained a hardcoded password for a high-privilege user : “factory” as shown in below snapshot:
The account was meant to provides an elevated access to the device, meaning an attacker having access to the device could gain elevated access to the device and change the device setting or initiate a complete shutdown causing a denial of service. Search results returned by Shodan reveal 17 active devices that are accessible over the internet, which are still having vulnerable versions of firmware running on them. The vulnerability were reported to be patched in earlier versions of the firmware, but we found that the account and password still exist. The newer firmware revision 4.5.6 fixes this issue, and users are advised to upgrade to the latest version.
2. CVE-2015-3960: Hardcoded RSA private key (A5: Security Misconfiguration)
CVSS Score: AV:N/AC:L/Au:N/C:C/I:N/A:N (how to read)
During the reverse engineering process of the firmware, it was discovered that the firmware had hardcoded RSA private keys and certificate files, which were used by the server for SSH and HTTPS connections. Any firmware using hardcoded private keys and certificates pose a greater security risk, as the firmwares are meant for a series of multiple devices, all the devices running the affected or earlier versions of that firmware are by default vulnerable, which means that an attacker just has to gain access to the keys/certificates and he would be exploit any similar devices with ease. An attacker having access to these certificates and keys can not only decrypt the HTTPS secure traffic but can also log in via ssh without username/password to any device running the same version of the firmware.
A general best practice that should be followed while developing the firmware is to:
- Avoid use of any hardcoded keys
- The private keys should not be stored unencrypted format
- The private key should be protected with a strong passphrase which is long and hard enough to crack in case anyone gains access to the keys
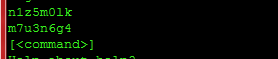
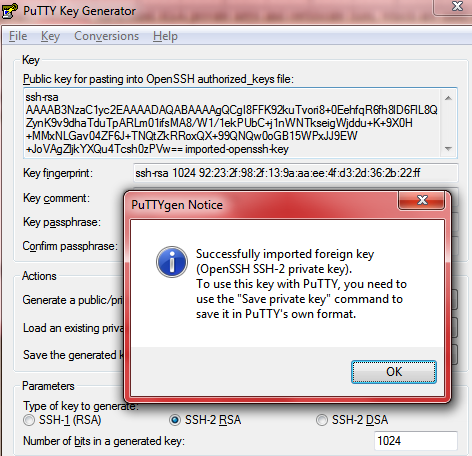
In case with Garrettcom Magnum 6k and 10k device series, the firmware contained hardcoded key which were used for ssh connection to the device. The key are meant to provide ssh access to the device without any password, the key were protected using a passphrase that was easy to guess as demonstrated in the below snapshot.
Proof-of-Concept:
The snapshot below shows the key used for SSH connections to the device. The key is being protected by passphrase: “magnum6k” which was verified using PuTTY Key Generator, as shown below in next snapshot.
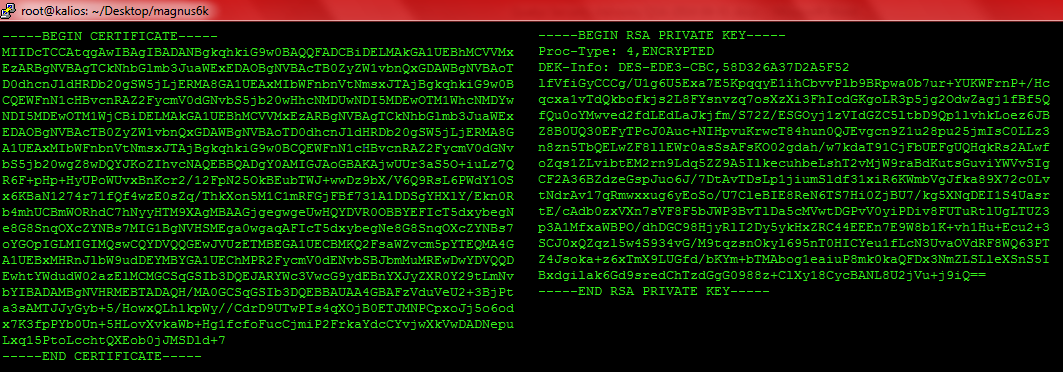
The firmware also had keys and certificates that were meant for HTTPS communication. Access to these certificates and private keys means that any attacker intercepting the traffic between the device and the users can decrypt the communication channel and tamper the data or conduct replay attacks. The below snapshot is for the key and cert used for HTTPS connections.
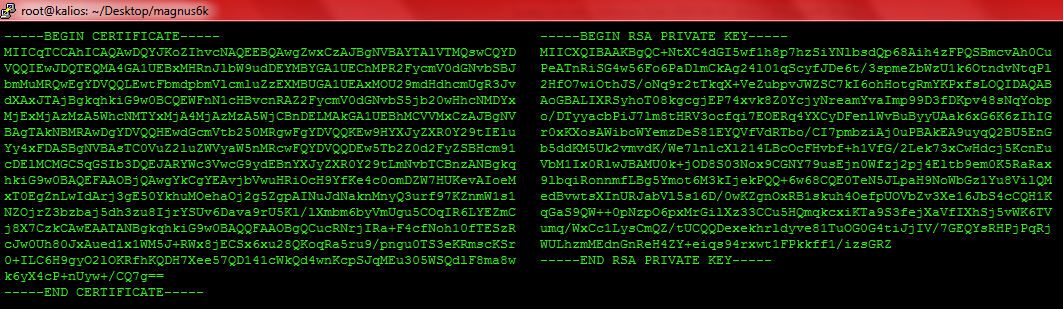
The private key above present in the firmware was tested using the HTTPS traffic captured between the browser and device and was successfully decrypted using the above key obtained from the firmware.As the private keys are hardcoded in the firmware, same keys were used across range of devices.
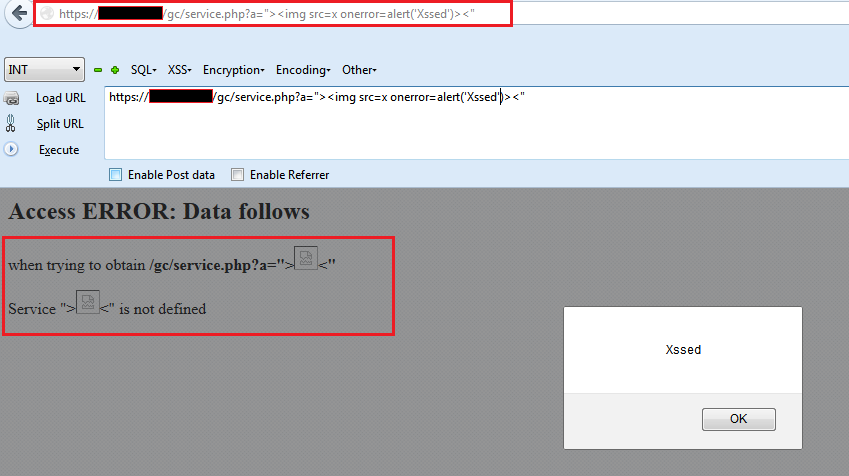
3. CVE-2015-3942: Improper Sanitization of user input (A3: Cross-Site Scripting XSS)
CVSS Score: AV:N/AC:L/Au:N/C:N/I:P/A:N (how to read)
Multiple XSS vulnerabilities were discovered in the web server which is present on the device. These vulnerabilities exist due to improper sanitization of user input which can be leveraged by an un-authenticated attacker to carry out cross-site scripting (XSS) attacks. As the web server and files remain same across all the devices, all the Magnum 6k and Magnum 10k devices are vulnerable
Proof-of-concept:
Below is the demonstration of the vulnerability, which shows that the device is vulnerable to XSS.
http://<server_url>/ gc/service.php?a="><img src=x onerror=alert('Xssed')><"
http://<server_url>/"><img src=x onerror=alert('Xssed')><"
http://<server_url>/gc/flash"><img src=x onerror=alert('Xssed')><"
Below is a snapshot of the vulnerability.
Private Keys and Certificates
Below are the private keys and certificates that were extracted from the firmware. The first Certificate and RSA key pair is for SSH connection. The rsa key is protected using passphrase: “magnum 6k” and can be verified by loading it in PuTTY Key Generator.
—–BEGIN CERTIFICATE—–
MIIDcTCCAtqgAwIBAgIBADANBgkqhkiG9w0BAQQFADCBiDELMAkGA1UEBhMCVVMx
EzARBgNVBAgTCkNhbGlmb3JuaWExEDAOBgNVBAcTB0ZyZW1vbnQxGDAWBgNVBAoT
D0dhcnJldHRDb20gSW5jLjERMA8GA1UEAxMIbWFnbnVtNmsxJTAjBgkqhkiG9w0B
CQEWFnN1cHBvcnRAZ2FycmV0dGNvbS5jb20wHhcNMDUwNDI5MDEwOTM1WhcNMDYw
NDI5MDEwOTM1WjCBiDELMAkGA1UEBhMCVVMxEzARBgNVBAgTCkNhbGlmb3JuaWEx
EDAOBgNVBAcTB0ZyZW1vbnQxGDAWBgNVBAoTD0dhcnJldHRDb20gSW5jLjERMA8G
A1UEAxMIbWFnbnVtNmsxJTAjBgkqhkiG9w0BCQEWFnN1cHBvcnRAZ2FycmV0dGNv
bS5jb20wgZ8wDQYJKoZIhvcNAQEBBQADgY0AMIGJAoGBAKAjwUUr3aS5O+iuLz7Q
R6F+pHp+HyUPoWUvxBnKcr2/12FpN25OkBEubTWJ+wwDz9bX/V6Q9RsL6PWdY1OS
x6KBaN1274r71fQf4wzE0sZq/ThkXon5M1C1mRFGjFBf731A1DDSgYHXlY/Ekn0R
b4mhUCBmWORhdC7hNyyHTM9XAgMBAAGjgegwgeUwHQYDVR0OBBYEFIcT5dxybegN
e8G8SnqOXcZYNBs7MIG1BgNVHSMEga0wgaqAFIcT5dxybegNe8G8SnqOXcZYNBs7
oYGOpIGLMIGIMQswCQYDVQQGEwJVUzETMBEGA1UECBMKQ2FsaWZvcm5pYTEQMA4G
A1UEBxMHRnJlbW9udDEYMBYGA1UEChMPR2FycmV0dENvbSBJbmMuMREwDwYDVQQD
EwhtYWdudW02azElMCMGCSqGSIb3DQEJARYWc3VwcG9ydEBnYXJyZXR0Y29tLmNv
bYIBADAMBgNVHRMEBTADAQH/MA0GCSqGSIb3DQEBBAUAA4GBAFzVduVeU2+3BjPt
a3sAMTJJyGyb+5/HowxQLhlkpWy//CdrD9UTwPIs4qXOjB0ETJMNPCpxoJj5o6od
x7K3fpPYb0Un+5HLovXvkaWb+Hg1fcfoFucCjmiP2FrkaYdcCYvjwXkVwDADNepu
Lxq15PtoLcchtQXEob0jJMSDld+7
—–END CERTIFICATE—–
—–BEGIN RSA PRIVATE KEY—–
Proc-Type: 4,ENCRYPTED
DEK-Info: DES-EDE3-CBC,58D326A37D2A5F52
lfVfiGyCCCg/U1g6U5Exa7E5KpqqyE1ihCbvvPlb9BRpwa0b7ur+YUKWFrnP+/Hc
qcxa1vTdQkbofkjs2L8FYsnvzq7osXzXi3FhIcdGKgoLR3p5jg2OdwZagj1fBf5Q
fQu0oYMwved2fdLEdLaJkjfm/S72Z/ESGOyj1zVIdGZC5ltbD9Qp1lvhkLoez6JB
Z8B0UQ30EFyTPcJ0Auc+NIHpvuKrwcT84hun0QJEvgcn9Z1u28pu25jmIsC0LLz3
n8zn5TbQELwZF8llEWr0asSsAFsKO02gdah/w7kdaT91CjFbUEFgUQHqkRs2ALwf
oZqs1ZLvibtEM2rn9Ldq5ZZ9A5IlkecuhbeLshT2vMjW9raBdKutsGuviYWVvSIg
CF2A36BZdzeGspJuo6J/7DtAvTDsLp1jiumSldf31xiR6KWmbVgJfka89X72c0Lv
tNdrAv17qRmwxxug6yEoSo/U7CleBIE8ReN6TS7Hi0ZjBU7/kg5XNqDEI1S4Uasr
tE/cAdb0zxVXn7sVF8F5bJWP3BvTlDa5cMVwtDGPvV0yiPDiv8FUTuRtlUgLTUZ3
p3A1MfxaWBPO/dhDGC98HjyRlI2Dy5ykHxZRC44EEEn7E9W8b1K+vh1Hu+Ecu2+3
SCJ0xQZqzl5w4S934vG/M9tqzsnOkyl695nT0HICYeu1fLcN3UvaOVdRF8WQ63PT
Z4Jsoka+z6xTmX9LUGfd/bKYm+bTMAbog1eaiuP8mk0kaQFDx3NmZLSLleXSnS5I
Bxdgilak6Gd9sredChTzdGgG0988z+ClXy18CycBANL8U2jVu+j9iQ==
—–END RSA PRIVATE KEY—–
The below key and certificate are being used for HTTPS connections:
—–BEGIN RSA PRIVATE KEY—–
MIICXQIBAAKBgQC+NtXC4dGI5wf1h8p7hzSiYNlbsdQp68Aih4zFPQSBmcvAh0Cu
PeATnRiSG4w56Fo6PaDlmCkAg24l01qScyfJDe6t/3spmeZbWzU1k6OtndvNtqPl
2HfO7wiOthJS/oNq9r2tTkqX+VeZubpvJWZSC7kI6ohHotgRmYKPxfsLOQIDAQAB
AoGBALIXRSyhoT08kgcgjEP74xvk8Z0YcjyNreamYvaImp99D3fDKpv48sNqYobp
o/DTyyacbPiJ7lm8tHRV3ocfqi7EOERq4YXCyDFenlWvBuByyUAak6xG6K6zIhIG
r0xKXosAWiboWYemzDeS81EYQVfVdRTbo/CI7pmbziAj0uPBAkEA9uyqQ2BU5EnG
b5ddKM5Uk2vmvdK/We7lnlcXl214LBcOcFHvbf+h1VfG/2Lek73xCwHdcj5KcnEu
VbM1Ix0RlwJBAMU0k+jOD8S03Nox9CGNY79usEjn0Wfzj2pj4Eltb9em0K5RaRax
9lbqiRonnmfLBg5Ymot6M3kIjekPQQ+6w68CQE0TeN5JLpaH9NoWbGz1Yu8VilQM
edBvwtsXInURJabVl5s16D/0wKZgnOxRB1skuh4OefpUOVbZv3Xe16JbS4cCQH1K
qGaS9QW++0pNzpO6pxMrGilXz33CCu5HQmqkcxiKTa9S3fejXaVfIXhSj5vWK6TV
umq/WxCc1LysCmQZ/tUCQQDexekhrldyve81TuOG0G4tiJjIV/7GEQYsRHPjPqRj
WULhzmMEdnGnReH4ZY+eiqs94rxwt1FPkkff1/izsGRZ
—–END RSA PRIVATE KEY—–
—–BEGIN CERTIFICATE—–
MIICqTCCAhICAQAwDQYJKoZIhvcNAQEEBQAwgZwxCzAJBgNVBAYTAlVTMQswCQYD
VQQIEwJDQTEQMA4GA1UEBxMHRnJlbW9udDEYMBYGA1UEChMPR2FycmV0dGNvbSBJ
bmMuMRQwEgYDVQQLEwtFbmdpbmVlcmluZzEXMBUGA1UEAxMOU29mdHdhcmUgR3Jv
dXAxJTAjBgkqhkiG9w0BCQEWFnN1cHBvcnRAZ2FycmV0dGNvbS5jb20wHhcNMDYx
MjExMjAzMzA5WhcNMTYxMjA4MjAzMzA5WjCBnDELMAkGA1UEBhMCVVMxCzAJBgNV
BAgTAkNBMRAwDgYDVQQHEwdGcmVtb250MRgwFgYDVQQKEw9HYXJyZXR0Y29tIElu
Yy4xFDASBgNVBAsTC0VuZ2luZWVyaW5nMRcwFQYDVQQDEw5Tb2Z0d2FyZSBHcm91
cDElMCMGCSqGSIb3DQEJARYWc3VwcG9ydEBnYXJyZXR0Y29tLmNvbTCBnzANBgkq
hkiG9w0BAQEFAAOBjQAwgYkCgYEAvjbVwuHRiOcH9YfKe4c0omDZW7HUKevAIoeM
xT0EgZnLwIdArj3gE50YkhuMOehaOj2g5ZgpAINuJdNaknMnyQ3urf97KZnmW1s1
NZOjrZ3bzbaj5dh3zu8IjrYSUv6Dava9rU5Kl/lXmbm6byVmUgu5COqIR6LYEZmC
j8X7CzkCAwEAATANBgkqhkiG9w0BAQQFAAOBgQCucRNrjIRa+F4cfNoh10fTESzR
cJw0Uh80JxAued1x1WM5J+RWx8jECSx6xu28QKoqRa5ru9/pngu0TS3eKRmscKSr
0+ILC6H9gyO2lOKRfhKQDH7Xee57QD141cWkQd4wnKcpSJqMEu305WSQdlF8ma8w
k6yX4cP+nUyw+/CQ7g==
—–END CERTIFICATE—–
the passphrase is "magnum6k", not "magnum 6k".
Thanks for the heads-up. This has been fixed.
Thanks for pointing it out, it was a typo error.