SANS Study: To Take On New InfoSec Challenges, First Get the Basics Right
A major challenge for enterprise InfoSec teams is keeping their finger on the pulse of two constantly changing elements: external cyber threats and internal technology needs.
Staying a step ahead and proactively adjusting their organization’s security posture accordingly is a must in order to keep attack risks as low as possible. So what are the major shifts in threats and business technology use that CISOs and their staff face in 2017? And how should they respond to these changes?
You will find comprehensive answers to those and other critical InfoSec questions in a new SANS Institute whitepaper written by security analyst John Pescatore.
“Cybercriminals and other attackers will continue to develop new threat vectors,” Pescatore writes in the report, titled “Cyber Security Trends: Aiming Ahead of the Target to Increase Security in 2017”.
“Even more importantly, and more rapidly, new technologies and new demands by businesses to use those technologies will threaten to break even the most secure foundations,” he adds.
Here we highlight key insights and recommendations from the study, which was sponsored by Qualys.
Threat Trends
Pescatore identifies three main threat trends that InfoSec teams will need to grapple with this year.
- Known vulnerabilities remain a big problem: While exploits of zero-day vulnerabilities grab all the headlines, they account for a minority of successful attacks. Most security incidents – estimates range between 80% and 99% – involve vulnerabilities that have been disclosed and for which patches have been available often for more than a year. This reality underscores the importance of rapid vulnerability detection and remediation via patching or mitigation.
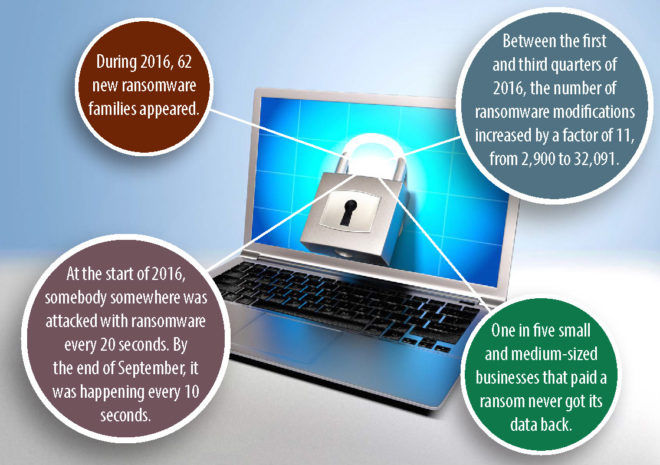 Hackers will double down on ransomware: With organizations focused on preventing and disrupting stealthy data breach attempts, hackers have shifted their focus to ransomware, a type of attack they have had outstanding success with. Pescatore expects ransomware attacks to continue increasing both in number and in variety. For example, he warns of a ransomware type called “badness planting” where embarrassing files are downloaded to PCs and servers, and victims are then extorted for money in return for the removal of these pictures and videos.
Hackers will double down on ransomware: With organizations focused on preventing and disrupting stealthy data breach attempts, hackers have shifted their focus to ransomware, a type of attack they have had outstanding success with. Pescatore expects ransomware attacks to continue increasing both in number and in variety. For example, he warns of a ransomware type called “badness planting” where embarrassing files are downloaded to PCs and servers, and victims are then extorted for money in return for the removal of these pictures and videos.
- The risk from vendors and other third parties deepens: Third party risk is a well-known security and compliance problem in which an organization is successfully attacked after hackers obtain access to its systems by hacking one of its trusted vendors, contractors or partners and stealing login credentials. Now, Pescatore warns, it’s not enough to mitigate risk among third parties. Bad guys are diving deeper into supply chains in search of security gaps among “fourth parties” still linked but further removed from the target organization, such as subcontractors and device manufacturers.
Business Technology Trends
The other major risk factor InfoSec teams must contend with is the adoption of new tech products within the organization, which Pescatore warns “often cause much larger breakage to existing security processes and controls” than external attacks. These are the trends to watch:
- Continued adoption of mobility and cloud computing: While the use of mobile devices and of cloud services has yielded significant benefits to businesses, it has also created new security dangers, largely related to an erosion of control by the IT department over these new wares. The variety and fast-changing nature of mobile devices, combined with the use of hundreds of approved and unapproved cloud services, require that InfoSec teams find ways to apply rigorous security processes to them such as vulnerability management, continuous monitoring and policy compliance.
- IoT security concerns materialize: Although warnings about IoT security aren’t new, the Mirai botnet attack against Dyn in October proved that the concerns aren’t just theoretical. Pescatore forecasts an increase particularly in IoT attacks that target what he calls “single-purpose” devices embedded in infrastructure used by enterprises, such as smart buildings, smart cars and environmental monitors. An associated increase in heterogeneity will disrupt security processes such as discovery, vulnerability assessment and management controls and processes, allowing hackers to hijack these “things” to launch attacks.
- Intensifying oversight and involvement by boards of directors: Massive data breaches have made cyber security a higher priority for boards of directors than it was just a few years ago. This means that CISOs are finding themselves in the boardroom spotlight, briefing directors and upper management on the organization’s security strategies and processes, and being held to high expectations regarding the safety of systems and data. As a result, CISOs and security managers need to learn to communicate effectively with board directors and top executives.
To Tackle New Risks You Need a Strong Security Foundation
The new security challenges will require new architectures, processes, controls and skills. But it’s essential to first have a solid InfoSec underpinning.
Pescatore recommends beginning with the Center for Internet Security’s Critical Security Controls, a set of 20 practices designed to protect organizations from the most common and dangerous cyber attacks.
“By focusing on the first five CIS, enterprises can build a strong foundation for dealing with the trends identified in this paper and mitigate or prevent many common security incidents.,” Pescatore writes.
The CIS controls provide “basic security hygiene” by leading organizations to focus on such core principles as having complete IT asset visibility and comprehensive vulnerability management.
Getting the basics right – such as hardware/software inventory, vulnerability assessment and mitigation, governance and business continuity planning – are essential for:
- protecting data from advanced threats
- allowing the business to safely use new business processes and technologies
Another important practice is embedding security into software development, acquisition and supply chain processes.
“Extending continuous monitoring and vulnerability awareness and mitigation into software development/DevOps processes and into the evaluation and acceptance criteria for procured software and cloud services not only efficiently reduces attack surfaces, but it has been proven to reduce time to market for secure business services,” Pescatore writes.
Indeed, at Qualys we firmly believe that CISOs and their teams should become evangelists of secure DevOps practices — DevSecOps — if they’re not already, and enthusiastically champion embedding security controls into DevOps processes, such as continuous integration and continuous delivery.
DevSecOps defines how security delivered as a service helps InfoSec teams work with DevOps to embed continuous security into the IT and application infrastructure for improved and automated auditing, compliance and control of applications.
Other recommendations:
- Implement security processes, tools and services that allow less experienced security staff to deal with base-level tasks, freeing up highly-skilled InfoSec pros to deal with more complex issues.
- Create a collaborative relationship between IT operations and InfoSec in order to flag flawed processes, controls and configurations that are at the root cause of many vulnerabilities.
- Extend security architectures, processes and visibility into the cloud, which Pescatore writes will give you “an integrated situational awareness view of risk, vulnerability and incident status”
Read more in the SANS whitepaper, Cyber Security Trends: Aiming Ahead of the Target to Increase Security in 2017.