Gaining Control over Your Digital Certificates
Digital certificate management is in an inadequate state at most organizations, a serious problem, considering that SSL/TLS certificates are critical for a host of e-business functions.
“If you’re doing something on the Internet, you’re using SSL,” Asif Karel, a Qualys Director of Product Management, said at the RSA Conference 2018.
Specifically, digital certificates are used to ensure the confidentiality, authenticity, integrity and non-repudiation of public-facing online services, internal services, machine-to-machine communications, public cloud services and API integrations.
During his presentation, Karel outlined the current challenges organizations face with certificate visibility, and explained how Qualys can help with CertView, a free app available now.
The problems start with limited visibility
Qualys SSL Labs’ SSL Pulse, which monitors the quality of SSL/TLS support across 150,000 websites, rated 43% of the sites monitored as having inadequate security in its latest report. Faults included expired or soon-to-expire certificates, weak or insecure cipher suites, and use of obsolete protocols such as SSLv2, SSLv3 and TLSv1.
“This is all because the certificates and TLS configurations aren’t being monitored or managed,” Karel said.
Hackers feast on weak certificates and TLS configurations, exploiting them to use encrypted traffic to transmit malware, power botnets, launch man-in-the-middle attacks, communicate with malicious command and control centers, and exfiltrate data.
It’s important to understand that while certificates and TLS offer protection, encrypted traffic can also be a problem, Karel said. Gartner recently predicted that 70% of network attacks against enterprises will hide in encrypted traffic by 2020, he added.

What’s at the root of the problem? Most businesses lack full and continuously updated inventories of their certificates, a faulty foundation that must be addressed as a first priority.
“Most organizations don’t have visibility into where their certificates are. They don’t know where they’re being used. They have limited ownership information. This all leads to the unknown,” Karel said. “The unknown is very difficult to manage.”
As a result, certificates expire taking IT admins by surprise, and causing outages and interruptions of online services and communications. This, in turn, tarnishes the company’s brand, hurts sales and harms customer and partner satisfaction.
Another problem is the adoption, often unwittingly, of certificates from unapproved Certificate Authorities, which creates its own set of security and compliance risks.
For example, DevOps teams, which release code quickly and continuously, often can’t wait days for the IT department to get them certificates from preferred sources, and instead get them themselves from free services.
Another issue is organizations’ reliance on manual processes for managing certificates, often via the use of spreadsheets, which yields errors and outdated information. With a manual approach, the inventory is limited to the certificates the IT department is aware of, so it will lack unreported certificates that may be in your environment.
“If you’re using a manual process, it hinders the innovation and growth of the company,” Karel said.
In fact, the average Global 5000 company spends $15 million to recover from the loss of business caused by a certificate-related outage, and faces another $25 million in costs related to compliance issues, according to Ponemon Institute.
Downsides of niche products
Existing certificate management products often suffer from a variety of weak spots arising from their design as narrow point solutions. As a result, they work in a vacuum and don’t communicate with other security systems, creating data silos and making it difficult for teams to collaborate and share information.
These products are also hard to scale, requiring multiple deployments to cover large environments, which increases cost of ownership and management complexity. In addition, these tools are often designed to work either only on premises, or only in cloud environments, but not in both.
The solution: Automate and centralize your visibility and tracking of global certificate deployments with a tool that works across hybrid IT environments.
Qualys CertView
With the free Qualys CertView, organizations can discover, inventory and monitor their Internet-facing digital certificates, along with their host SSL/TLS configurations and vulnerabilities.
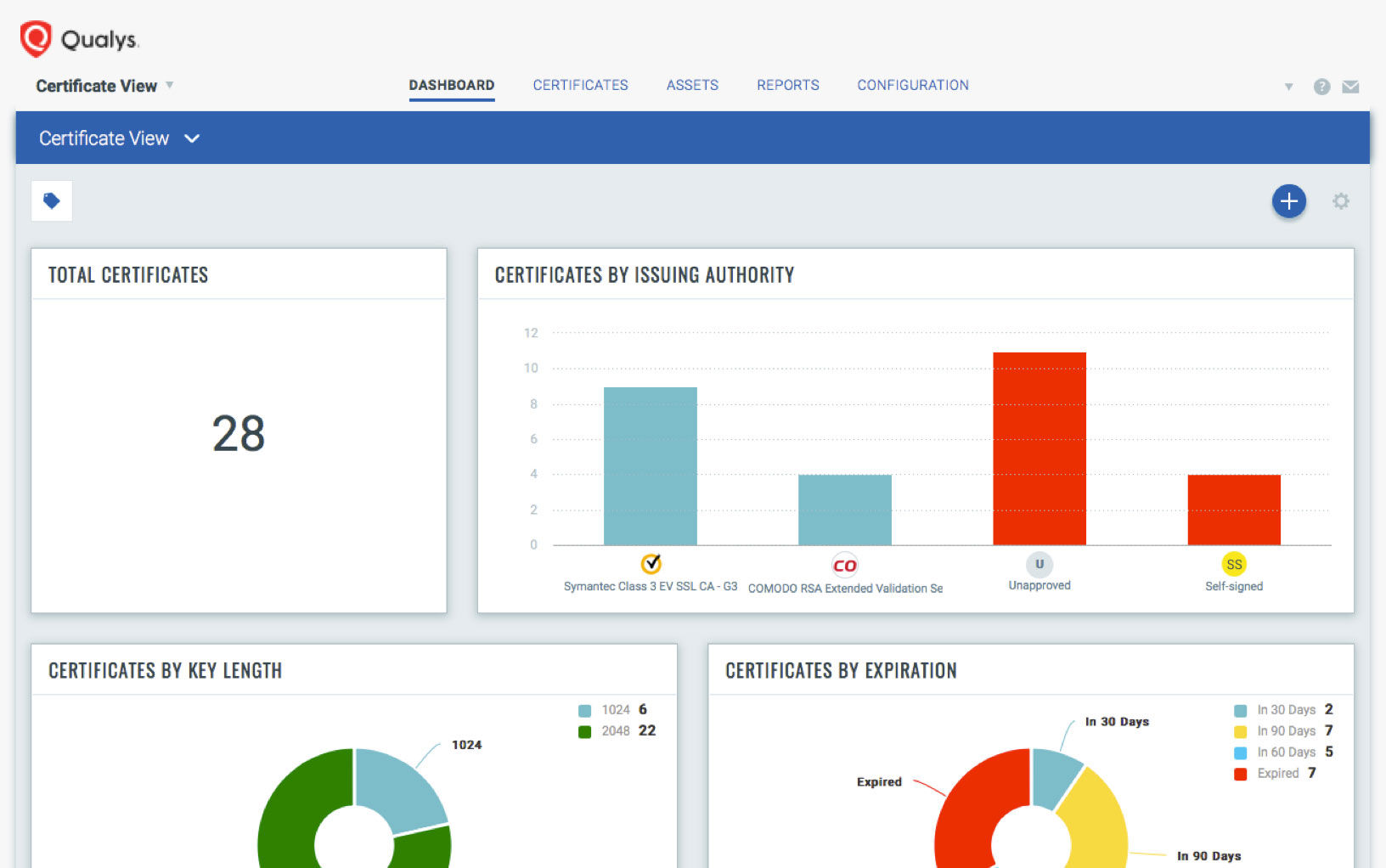
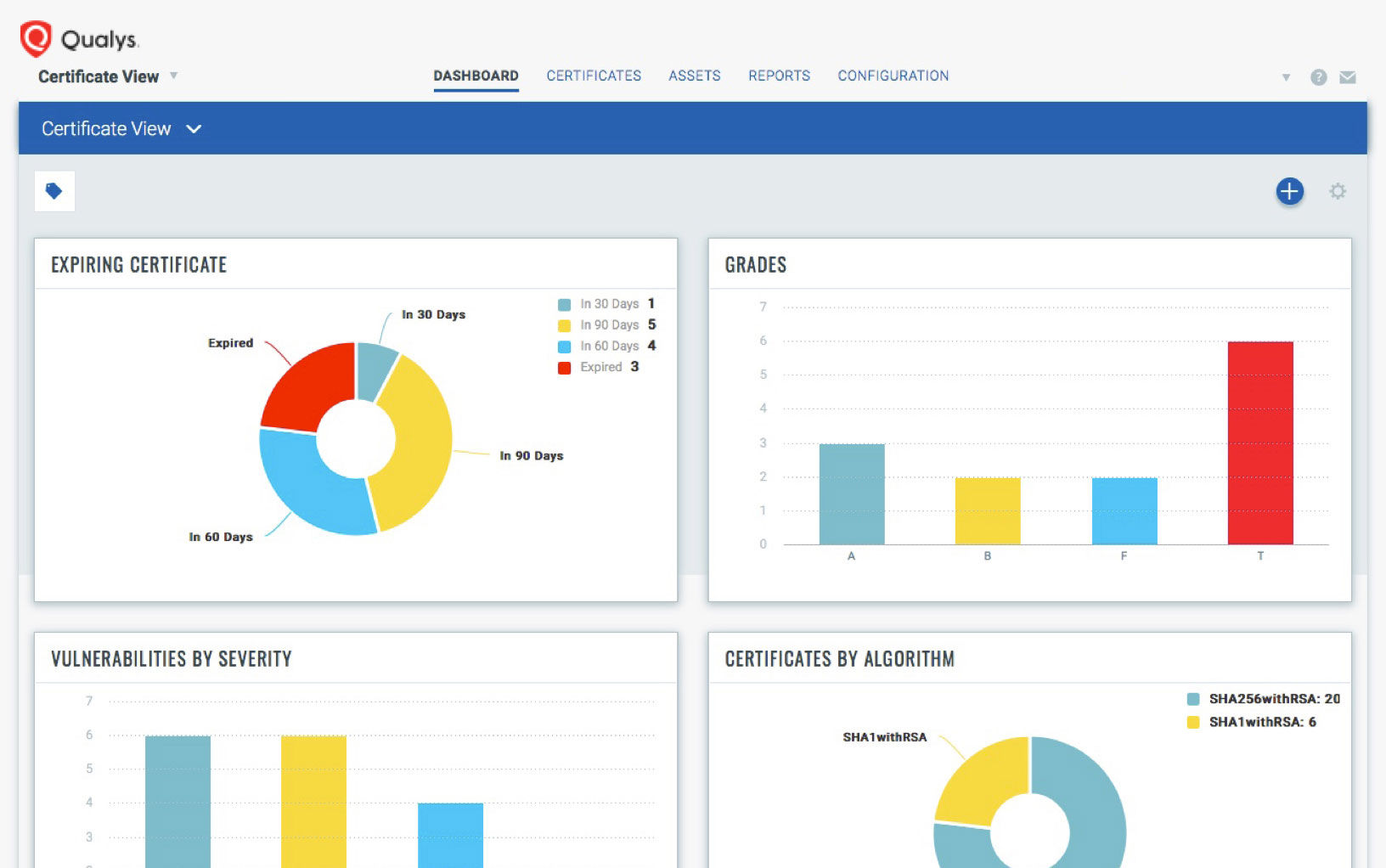
They will obtain a graded assessment that takes into account elements such as the host, port, service and certificate of assets both on premises and in cloud environments, so that they can address common use cases such as:
- Preventing downtime and outages caused by expired certificates
- Assessing the strength of SSL/TLS configurations via intuitive certificate grades (A, B, C, D, …) using SSL Labs’ methodology
- Detecting certificate-related anomalies
- Obtaining full certificate visibility via continuous discovery and inventorying, and managing them from a single-pane-of-glass interface with a powerful elastic search engine
- Achieving audit success with automated, downloadable reports
- Carrying out fast, precise remediation
A key advantage of Qualys CertView is that it uses the same Qualys scanners that existing customers have deployed for other Qualys Cloud Apps, such as Qualys Vulnerability Management and Qualys Policy Compliance.
Like the other Qualys Cloud Apps, Qualys CertView is a software-as-a-service product that’s built on top of the robust, highly scalable Qualys Cloud Platform, where all data is stored and analyzed.
Learn more and sign up for Qualys CertView. If you are an existing Qualys customer, you can activate a trial from within the Qualys console. With an upgrade, you can extend inventory and assessment of your Internet-facing certificates to include your internal network where your most critical data resides.
