How to Scan Across an Air Gap with QualysGuard
Last updated on: September 6, 2020
An air gap network, sometimes called an isolated network, is a set of systems that are intentionally isolated from the Internet or other networks for increased security. If there is an air gap, i.e. no physical connection between your systems and unsecured networks or the Internet, then you have better protection against data leakage or intrusion.
Air gap networks are most common in production or manufacturing environments, such as nuclear power plants or where SCADA-type systems are installed; in military or government organizations; and in sensitive financial applications like stock exchanges. Despite the air gap, these environments still can require security audits to ensure that other defense-in-depth controls are in place and working properly. For example, it is believed that the well-known Stuxnet virus entered the systems via a USB stick, showing how an air gap is not a foolproof security measure. In these cases, Qualys sees demand from our customers for a QualysGuard scan across the air gap.
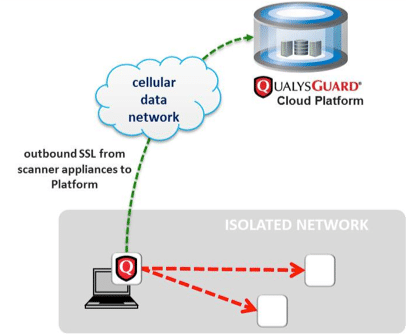
Scanning an air gap network can be done using a QualysGuard Virtual Scanner appliance on a laptop connected over a MiFi connection. In this configuration, the laptop runs a wireless router acting as a mobile Wi-Fi hotspot providing Internet access via a cellular network and a mobile carrier. The virtual appliance is usually more convenient than a physical appliance, especially for consultants who prefer to run the virtual appliance on their own laptop.
Security
In terms of security, the air gap network owner should look at both the configuration of the laptop attached to the network and the QualysGuard Virtual Scanner Appliance installed on the laptop.
For the laptop, the network owner typically vets the consultants running the scans and requires them to demonstrate the security controls they have implemented on the computer.
For the QualysGuard Scanner Appliance, Qualys has built a series of features to ensure that only scan data is transmitted out of the network and only to the QualysGuard platform. Specifically, the appliance is designed as a client-only device with no persistent services or daemons listening to the network. The scanner appliance runs a specifically hardened operating system kernel designed to prevent shell-code and buffer overflow attacks.
The scanner appliance does not require inbound Internet connections; it initiates all communications to the QualysGuard platform using HTTPS on port 443 over the Internet, so there is no need for inbound firewall rules. The QualysGuard platform IP networks are known and can be used to create outbound firewall rules that restrict all outbound Internet IP communications from the scanner appliance to only the QualysGuard platform IP networks.
The QualysGuard Scanner Appliance is limited in its function as a pure host on the network; it has no ability to route packets, even when multiple network interfaces are active in the split network configuration that is used for air gap networks. The appliance scans local systems, processes the resulting data, and then sends the processed data to the QualysGuard platform. The appliance runs no routing or bridging service.
The QualysGuard Scanner Appliance is packaged as a network appliance, pre-installed with Scanner Appliance software, and pre-configured for ease of installation and deployment within an enterprise. It is available as a physical device or a virtual image that can be deployed on various hypervisors, including virtual solutions for desktop and laptops such as VMware Player, VMware Fusion and Oracle VirtualBox.
Performance
The network performance of a QualysGuard scanner appliance connected via MiFi to the QualysGuard platform is equivalent to performance of scans performed with a virtual scanner appliance and a laptop with “regular” Internet connectivity. The results of the performance tests demonstrate this, even for slower MiFi connections. The amount of data sent from the appliance to the QualysGuard data center is small enough that performance is not impacted.
Defense in Depth
The use of QualysGuard by organizations with greater-than-normal security requirements is a validation of both the value of the service and the strength of its security controls. But more importantly, it is a reminder that no matter the environment, the best practice is always to use defense in depth, i.e. multiple layers of security controls throughout all IT systems.
Please read the associated technical note, based on a recent customer RFP, for more information on How to use QualysGuard Virtual Appliance on a laptop connected to the Internet via MiFi.