Get Emerging Threats Visibility with Qualys IOC Widgets
Two new built-in widgets for detecting the GravityRAT and GhostSecret advanced threats are now available in Qualys Indication of Compromise (IOC). These threats are of specific concern as they target industries like finance, entertainment, telecommunication and healthcare and have capability to exfiltrate data as well as cause extensive damage to the affected systems. Importing these widgets into your dashboard gives 2-second visibility across your enterprise to identify assets affected by these threats.
GravityRAT
Security Researchers have recently reported about remote access trojan GravityRAT which has evolved over last 18 months.
GravityRAT’s initial infection vector is an email attachment containing malicious macros.The Visual Basic macro gets executed when the document is opened. It extracts embedded executable file inside malicious document as ‘%temp%\image4.exe’. As a way to achieve persistence on the system, the macro creates scheduled task with the name ‘wordtest’ to execute the extracted file.
The purpose of this threat is data exfiltration of important documents from the victim’s system. It includes file types like Microsoft Office documents and PDF files along with system information like MAC address, hostname, username, IP address etc. New variants of GravityRAT incorporated several techniques, including system profiling, running process analysis and user details, in order to avoid execution in virtual machine environments and minimize detection. Recent variants analyzed continue to use the same Command and Control (C&C) servers. However, added functionality includes looking for documents on removable storage devices attached to the infected system.
GhostSecret
Thailand’s Computer Emergency Response Team (ThaiCERT) has recently seized a server operated by the North Korea-linked Hidden Cobra APT, which is used to control the global GhostSecret espionage campaign. The GhostSecret campaign targeted critical infrastructure, finance, entertainment, healthcare and telecommunication in at least 17 countries. It uses multiple implants, tools and malware variants associated with Hidden Cobra and has the ability to gather data and launch further attacks.
Recommendation
- It is recommended to disable Macros for Microsoft Office and never enable them for documents received from untrusted sources.
- Do not open links and email attachments from unknown sources.
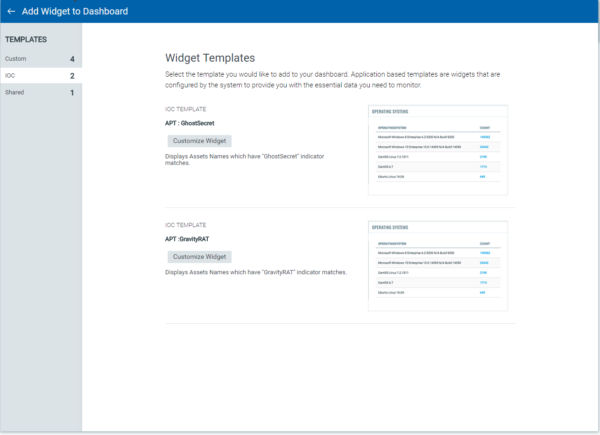
How to Add System Widgets to the Qualys IOC Dashboard
To start using the two new widgets, follow these steps:
- Click the Add Widget icon on your dashboard.
- Pick one of the system widget templates.
- The widget can be customized by selecting either Bar chart, Pie chart, Count or Table for displaying the result. Count widget type allows to set threshold value which triggers change in color of the widget based on result.
- Click on Add to Dashboard button.
- Once installed the widget automatically displays asset names of infected systems.
The widget will now be available on the active dashboard.
Learn More
Qualys Indication of Compromise expands the capabilities of the Qualys Cloud Platform to deliver threat hunting, detect suspicious activity, and confirm the presence of known and unknown malware for devices both on and off the network.