Microsoft and Adobe Patch Tuesday, January 2026 Security Update Review
Table of Contents
- Microsoft Patch Tuesday forJanuary2026
- Adobe Patches for January 2026
- Zero-day Vulnerabilities Patched inJanuaryPatch Tuesday Edition
- Critical Severity Vulnerabilities Patched inJanuaryPatch Tuesday Edition
- Other Microsoft Vulnerability Highlights
- Microsoft Release Summary
- Discover and Prioritize Vulnerabilities inVulnerability Management, Detection & Response (VMDR)
- Rapid Response with TruRisk Eliminate
- EVALUATE Vendor-Suggested Mitigation withPolicy Audit(PA)
- Qualys Monthly Webinar Series
Starting the year on a security-first note, Microsoft’s January 2026 Patch Tuesday resolves several vulnerabilities that could impact enterprise environments. Here’s a quick breakdown of what you need to know.
Microsoft Patch Tuesday for January 2026
This month’s release addresses 115 vulnerabilities, including eight critical and 106 important-severity vulnerabilities.
In this month’s updates, Microsoft has addressed three zero-day vulnerabilities. One of them was exploited, and two are publicly disclosed.
Microsoft addressed one vulnerability in Microsoft Edge (Chromium-based) that was patched earlier this month.
Microsoft Patch Tuesday, January edition, includes updates for vulnerabilities in Windows Ancillary Function Driver for WinSock, Windows Client-Side Caching (CSC) Service, Windows NTFS, Windows NTLM, Windows Remote Assistance, Windows Remote Procedure Call, Windows Server Update Service, Windows Cloud Files Mini Filter Driver, Windows Management Services, and more.
From elevation of privilege flaws to remote code execution risks, this month’s patches are essential for organizations aiming to maintain a robust security posture.
The January 2026 Microsoft vulnerabilities are classified as follows:
| Vulnerability Category | Quantity | Severities |
| Spoofing Vulnerability | 5 | Important: 5 |
| Denial of Service Vulnerability | 2 | Important: 2 |
| Elevation of Privilege Vulnerability | 57 | Critical: 2 Important: 55 |
| Information Disclosure Vulnerability | 22 | Important: 22 |
| Remote Code Execution Vulnerability | 22 | Critical: 6 Important: 16 |
| Security Feature Bypass Vulnerability | 3 | Important: 3 |
Adobe Patches for January 2026
Adobe has released 11 security advisories to address 25 vulnerabilities in Adobe DreamWeaver, Adobe InDesign, Adobe Illustrator, Adobe InCopy, Adobe Bridge, Adobe Substance 3D Modeler, Adobe Substance 3D Modeler, Adobe Substance 3D Painter, Adobe Substance 3D Sampler, Adobe Coldfusion, and Adobe Substance 3D Designer. 17 of these vulnerabilities are given critical severity ratings. Successful exploitation of these vulnerabilities may lead to arbitrary code execution and arbitrary file system read.
Zero-day Vulnerabilities Patched in January Patch Tuesday Edition
CVE-2026-20805: Desktop Window Manager Information Disclosure Vulnerability
An unauthenticated attacker may exploit the vulnerability to disclose information locally. Upon successful exploitation, an attacker can expose a section address from a remote ALPC port, which is user-mode memory.
CISA acknowledged the active exploitation of the vulnerability by adding it to its Known Exploited Vulnerabilities Catalog. CISA urges users to patch the vulnerability before February 3, 2026.
MITRE: CVE-2023-31096 Windows Agere Soft Modem Driver Elevation of Privilege Vulnerability
Microsoft mentioned in the advisory that “the vulnerabilities in the third-party Agere Soft Modem drivers that ship natively with supported Windows operating systems.” Successful exploitation of the vulnerability may allow an attacker to gain SYSTEM privileges. Microsoft fixes this vulnerability by removing agrsm64.sys and agrsm.sys drivers.
CVE-2026-21265: Secure Boot Certificate Expiration Security Feature Bypass Vulnerability
Upon successful exploitation of the vulnerability, an attacker could bypass Secure Boot.
Microsoft has informed that Windows Secure Boot certificates issued in 2011 are nearing expiration, and systems that are not updated will have an increased risk of threat actors bypassing Secure Boot.

Critical Severity Vulnerabilities Patched in January Patch Tuesday Edition
CVE-2026-20822: Windows Graphics Component Elevation of Privilege Vulnerability
A use-after-free flaw in the Microsoft Graphics Component may allow an authenticated attacker to elevate privileges locally. An attacker must win a race condition to exploit the vulnerability. Successful exploitation of the vulnerability may allow an attacker to gain SYSTEM privileges.
CVE-2026-20876: Windows Virtualization-Based Security (VBS) Enclave Elevation of Privilege Vulnerability
A heap-based buffer overflow flaw in Windows Virtualization-Based Security (VBS) Enclave could allow an authenticated attacker to elevate privileges locally. An attacker who successfully exploited this vulnerability could gain Virtual Trust Level 2 (VTL2) privileges.
CVE-2026-20944: Microsoft Word Remote Code Execution Vulnerability
An out-of-bounds read flaw in Microsoft Office Word may allow an unauthenticated attacker to achieve remote code execution. An attacker must send the user a malicious file and convince them to open it for the vulnerability to be successfully exploited.
CVE-2026-20952 & CVE-2026-20953: Microsoft Office Remote Code Execution Vulnerability
A use-after-free flaw in Microsoft Office could allow an unauthenticated attacker to achieve remote code execution.
CVE-2026-20955: Microsoft Excel Remote Code Execution Vulnerability
Successful exploitation of the vulnerability may allow an unauthenticated attacker to achieve remote code execution.
CVE-2026-20854: Windows Local Security Authority Subsystem Service (LSASS) Remote Code Execution Vulnerability
The Local Security Authority Subsystem Service (LSASS) is a core Windows process that handles user authentication, enforces security policies, and manages sensitive credentials (like passwords, NTLM hashes) by generating access tokens for users.
A use-after-free flaw in the Windows Local Security Authority Subsystem Service allows an authorized attacker to execute code over a network.
CVE-2026-20957: Microsoft Excel Remote Code Execution Vulnerability
An integer underflow flaw in Microsoft Office Excel allows an unauthenticated attacker to achieve remote code execution.
Other Microsoft Vulnerability Highlights
- CVE-2026-20816 is an elevation of privilege vulnerability in the Windows Installer. Successful exploitation of the vulnerability may allow an attacker to gain SYSTEM privileges.
- CVE-2026-20817 is an elevation of privilege vulnerability in the Windows Error Reporting Service. An authenticated attacker may exploit the vulnerability to gain SYSTEM privileges.
- CVE-2026-20820 is an elevation of privilege vulnerability in the Windows Common Log File System Driver. A heap-based buffer overflow flaw could allow an authenticated attacker to gain SYSTEM privileges.
- CVE-2026-20840 & CVE-2026-20922 are remote code execution vulnerabilities in Windows NTFS. A heap-based buffer overflow flaw could allow an authenticated attacker to achieve remote code execution.
- CVE-2026-20860 is an elevation of privilege vulnerability in the Windows Ancillary Function Driver for WinSock. A type confusion flaw may allow an authenticated attacker to gain SYSTEM privileges.
- CVE-2026-20843 is an elevation of privilege vulnerability in the Windows Routing and Remote Access Service (RRAS). Successful exploitation of the vulnerability may allow an attacker to gain SYSTEM privileges.
- CVE-2026-20871 is an elevation of privilege vulnerability in Desktop Windows Manager. An attacker who successfully exploited this vulnerability could gain SYSTEM privileges.
Microsoft Release Summary
This month’s release notes cover multiple Microsoft product families and products/versions affected, including, but not limited to, Windows Deployment Services, SQL Server, Windows Hello, Desktop Window Manager, Printer Association Object, Windows Kernel Memory, Windows Win32K – ICOMP, Windows LDAP – Lightweight Directory Access Protocol, Graphics Kernel, Capability Access Management Service (camsvc), Windows Installer, Windows Error Reporting, Windows Kernel, Windows Virtualization-Based Security (VBS) Enclave, Windows Common Log File System Driver, Microsoft Graphics Component, Windows File Explorer, Windows Hyper-V, Tablet Windows User Interface (TWINUI) Subsystem, Windows Internet Connection Sharing (ICS), Windows TPM, Windows Remote Procedure Call Interface Definition Language (IDL), Windows Kerberos, Windows Shell, Windows Media, Windows DWM, Windows Routing and Remote Access Service (RRAS), Windows Clipboard Server, Windows SMB Server, Windows WalletService, Windows Local Security Authority Subsystem Service (LSASS), Windows Kernel-Mode Drivers, Connected Devices Platform Service (Cdpsvc), Windows Local Session Manager (LSM), Windows HTTP.sys, Windows Telephony Service, Windows NDIS, Host Process for Windows Tasks, Microsoft Office, Microsoft Office Word, Microsoft Office Excel, Microsoft Office SharePoint, Dynamic Root of Trust for Measurement (DRTM), Windows Admin Center, Inbox COM Objects, Azure Connected Machine Agent, Azure Core shared client library for Python, Windows Secure Boot, Agere Windows Modem Driver, Windows Motorola Soft Modem Driver, and Microsoft Edge (Chromium-based).
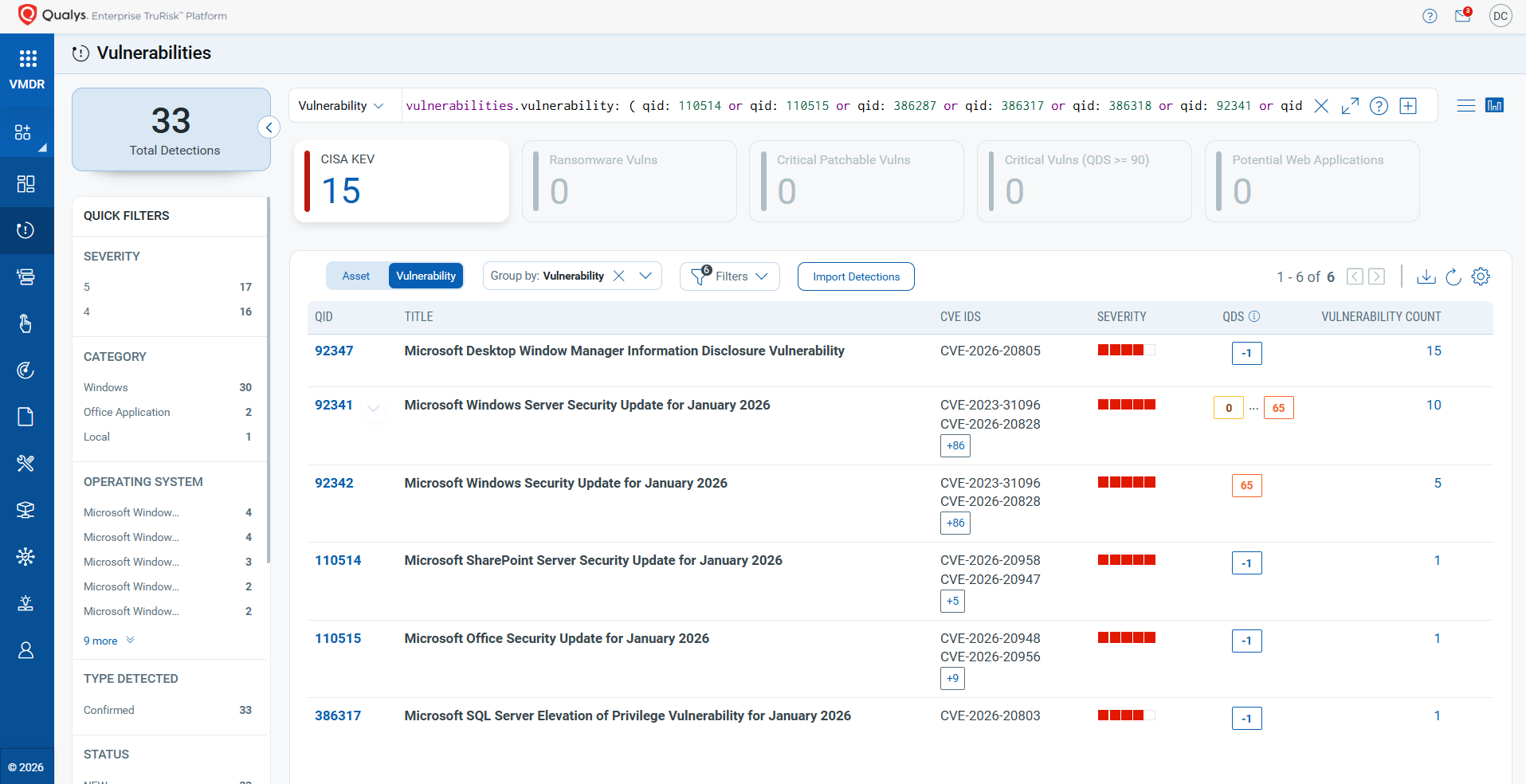
Discover and Prioritize Vulnerabilities in Vulnerability Management, Detection & Response (VMDR)
Qualys VMDR automatically detects new Patch Tuesday vulnerabilities using continuous updates to its Knowledgebase (KB).
You can see all your impacted hosts by these vulnerabilities using the following QQL query:
vulnerabilities.vulnerability: ( qid: 110514 or qid: 110515 or qid: 386287 or qid: 386317 or qid: 386318 or qid: 92341 or qid: 92342 or qid: 92343 or qid: 92344 or qid: 92347 )
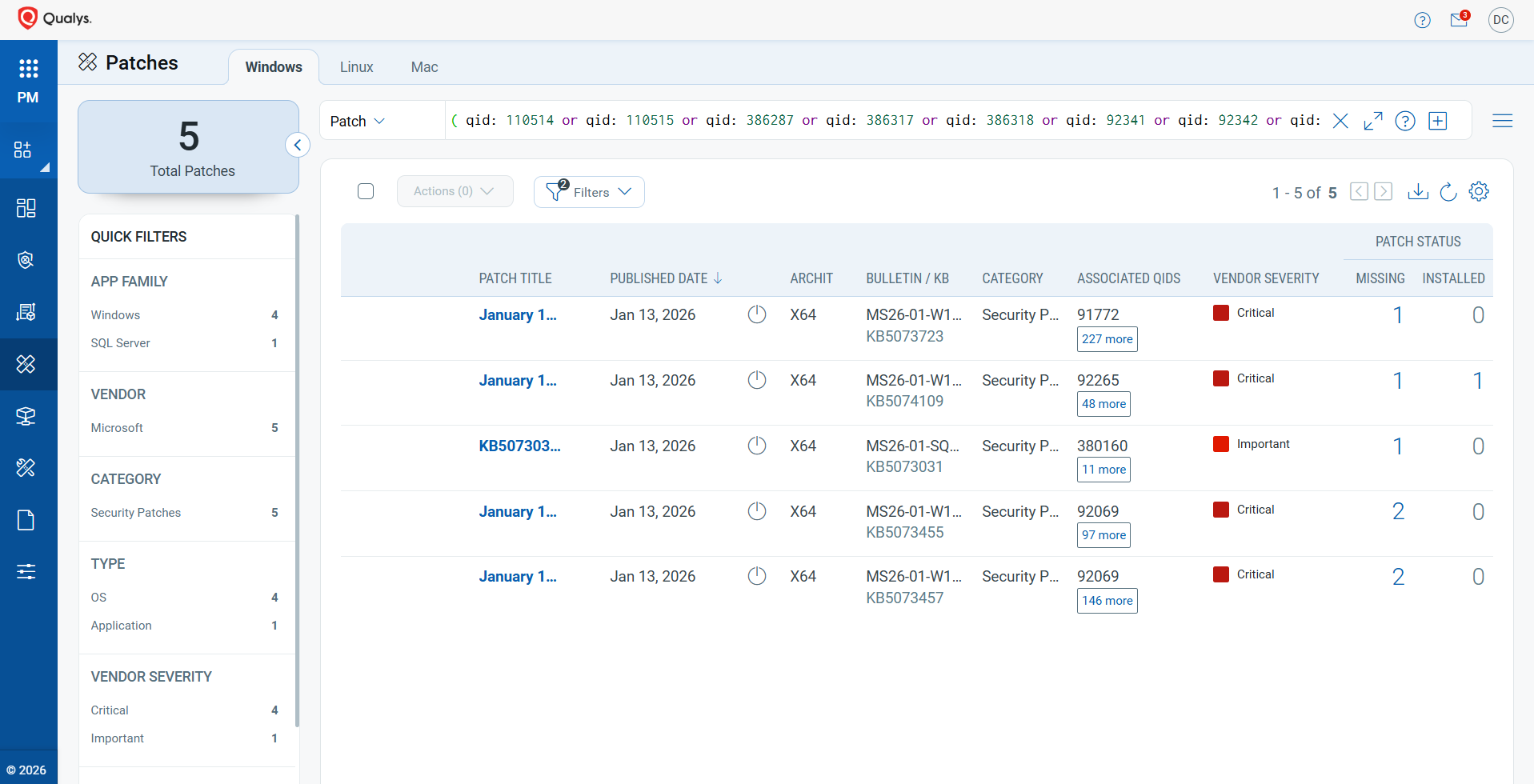
Rapid Response with TruRisk™ Eliminate
Patch to the Latest Version
VMDR rapidly remediates Windows hosts by deploying the most relevant and applicable per-technology version patches. You can simply select respective QIDs in the Patch Catalog and filter on the “Missing” patches to identify and deploy the applicable, available patches with one click.
The following QQL will return the missing patches for this Patch Tuesday:
( qid: 110514 or qid: 110515 or qid: 386287 or qid: 386317 or qid: 386318 or qid: 92341 or qid: 92342 or qid: 92343 or qid: 92344 or qid: 92347 )
Mitigation: Reducing Risk Until Remediation
Not every team can patch immediately due to operational challenges. TruRisk™ Eliminate enables security teams to apply mitigation controls that immediately lower exposure and reduce the Qualys Detection Score (QDS).
As a first set of our mitigant signature set, we have Qualys-created mitigations for the following 61 vulnerabilities: CVE-2026-20851, CVE-2026-20830, CVE-2026-21221, CVE-2026-20815, CVE-2026-20835, CVE-2026-20827, CVE-2026-20826, CVE-2026-20958, CVE-2026-20963, CVE-2026-20947, CVE-2026-20951, CVE-2026-20959, CVE-2026-20840, CVE-2026-20922, CVE-2026-20864, CVE-2026-20808, CVE-2026-20839, CVE-2026-20940, CVE-2026-20857, CVE-2026-20843, CVE-2026-20868, CVE-2026-20931, CVE-2026-20824, CVE-2026-20821, CVE-2026-20920, CVE-2026-20863, CVE-2026-20811, CVE-2026-20870, CVE-2026-20924, CVE-2026-20874, CVE-2026-20873, CVE-2026-20867, CVE-2026-20866, CVE-2026-20862, CVE-2026-20923, CVE-2026-20858, CVE-2026-20861, CVE-2026-20877, CVE-2026-20918, CVE-2026-20865, CVE-2026-20869, CVE-2026-20854, CVE-2026-20875, CVE-2026-20849, CVE-2026-20833, CVE-2026-21222, CVE-2026-20818, CVE-2026-20809, CVE-2026-20838, CVE-2026-20859, CVE-2026-20812, CVE-2026-20932, CVE-2026-20937, CVE-2026-20939, CVE-2026-20823, CVE-2026-20946, CVE-2026-20955, CVE-2026-20956, CVE-2026-20957, CVE-2026-20950, CVE-2026-20949, CVE-2026-20943, CVE-2026-20953, CVE-2026-20952, CVE-2026-20944, CVE-2023-31096, and CVE-2026-20856.
For vulnerabilities in Windows services where local or remote exploitation vectors exist, our mitigants modify configuration by modifying registry keys and, where applicable, service policy files. These mitigations apply to affected components, including the Routing and Remote Access Service (RRAS), Capability Access Manager Services, Hyper-V, Microsoft SharePoint, Connected Devices Platform, Telephony API service, Windows Tablet Input services, Windows Wallet Service, and Client-Side Caching. Additionally, this mitigant set addresses denial-of-service, elevation-of-privilege, remote code execution, and information disclosure risks in these core Windows subsystems.
Qualys TruRisk Mitigate product customers receive these scripts as part of the monthly Patch Tuesday signature set.
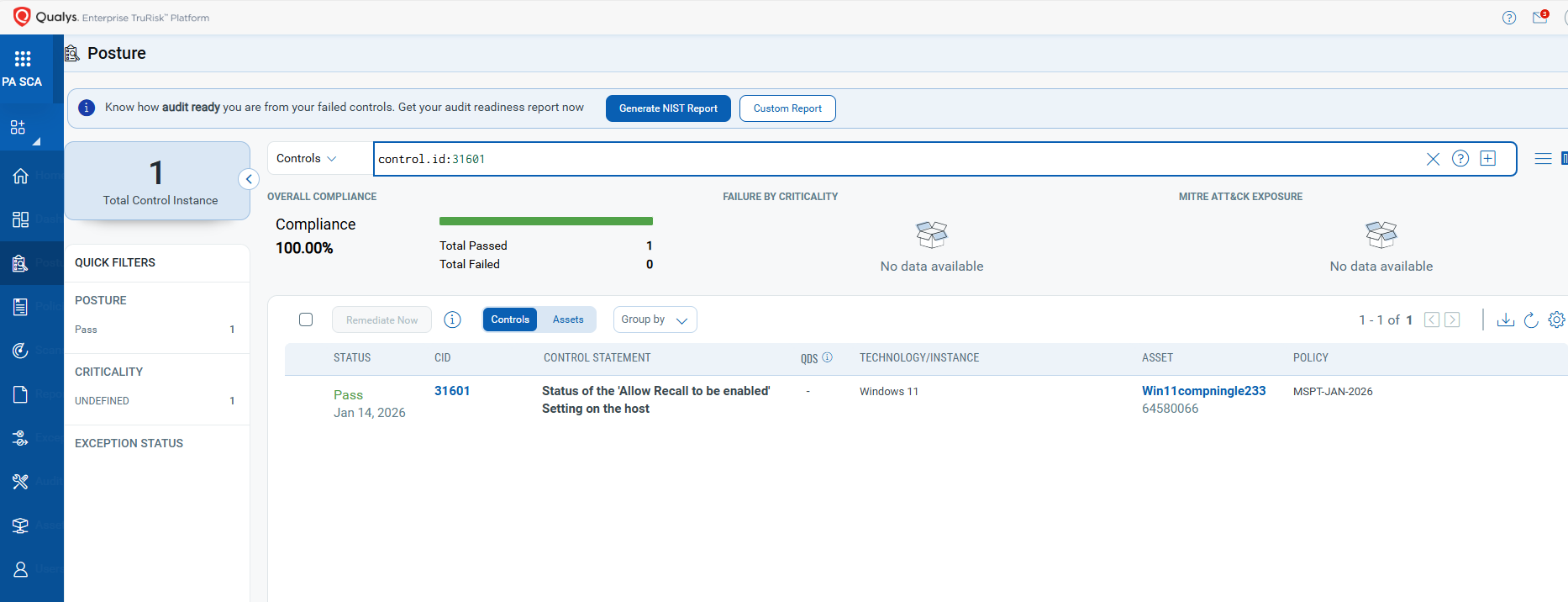
EVALUATE Vendor-Suggested Mitigation with Policy Audit (PA)
With Qualys Policy Audit’s out-of-the-box mitigation or Compensatory Controls, which reduce the risk of a vulnerability being exploited because the remediation (fix/patch) cannot be done immediately, these security controls are not recommended by any industry standards, such as CIS and DISA-STIG.
The Qualys Policy Audit team releases these exclusive controls based on vendor-suggested mitigation and workarounds.
Mitigation refers to a setting, common configuration, or general best practice that, in its default state, can reduce the severity of vulnerability exploitation.
A workaround is a method, sometimes used temporarily, for achieving a task or goal when the usual or planned method isn’t working. Information technology often employs workarounds to overcome hardware, programming, or communication issues. Once a problem is fixed, a workaround is usually abandoned.
The following Qualys Policy Audit Control IDs (CIDs) and System Defined Controls (SDC) have been updated to support Microsoft-recommended mitigation(s) for this Patch Tuesday:
CVE-2026-20941: Host Process for Windows Tasks Elevation of Privilege Vulnerability
This vulnerability has a CVSS:3.1 7.8 / 6.8
Policy Audit Control IDs (CIDs):
- 31601 Status of the ‘Allow Recall to be enabled’ Setting on the host
The following QQL will return a posture assessment for the CIDs for this Patch Tuesday:
control.id: [31601]
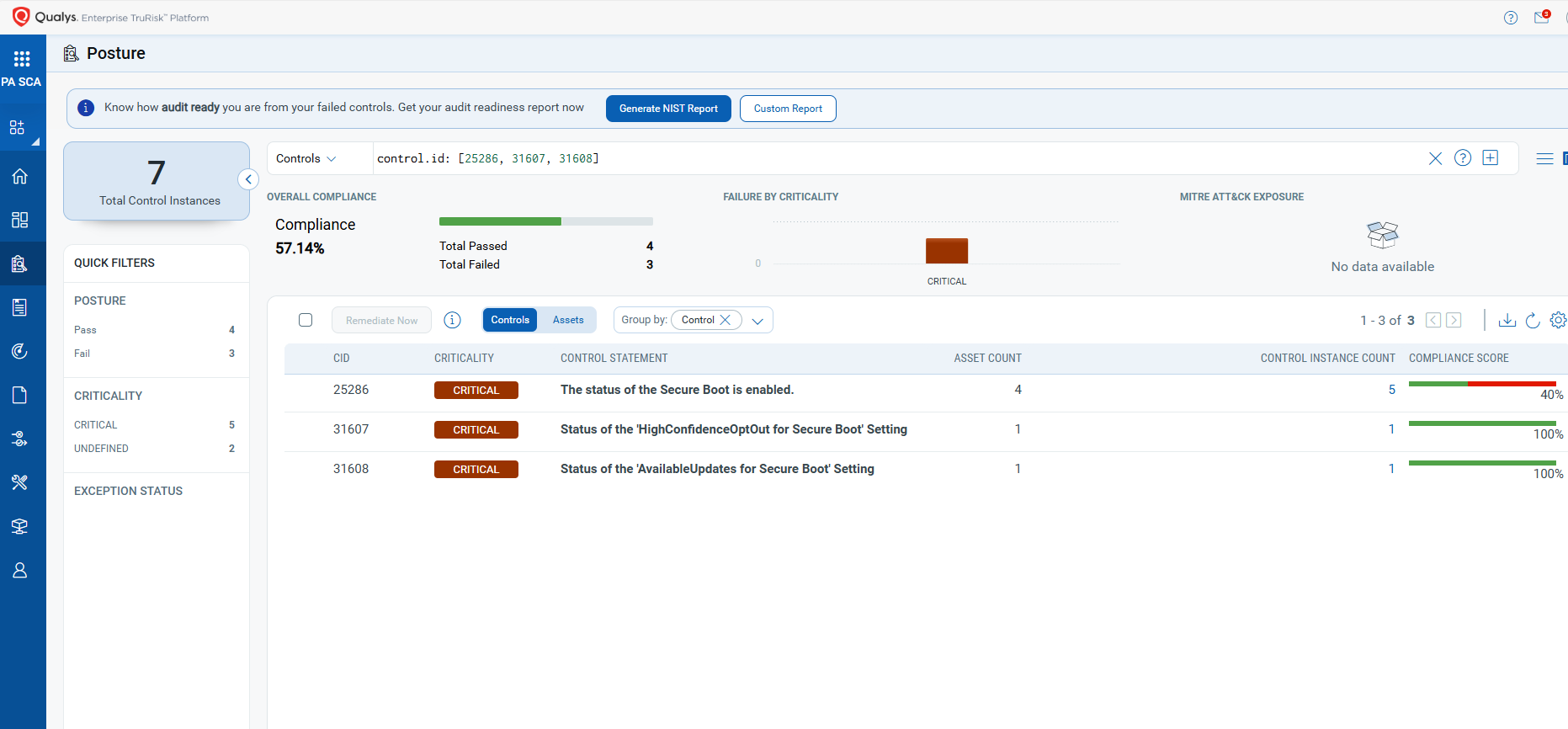
CVE-2026-21265: Secure Boot Certificate Expiration Security Feature Bypass Vulnerability
This vulnerability has a CVSS:3.1 6.4 / 5.6
Policy Audit Control IDs (CIDs):
- 25286 The status of the Secure Boot is enabled
- 31607 Status of the ‘HighConfidenceOptOut for Secure Boot’ Setting
- 31608 Status of the ‘AvailableUpdates for Secure Boot’ Setting
The following QQL will return a posture assessment for the CIDs for this Patch Tuesday:
control.id: [25286, 31607, 31608]
The next Patch Tuesday is scheduled for February 10, and we will provide details and patch analysis at that time. Until next Patch Tuesday, stay safe and secure. Be sure to subscribe to the ‘This Month in Vulnerabilities and Patches’ webinar.’
Qualys Monthly Webinar Series
The Qualys Research team hosts a monthly webinar series to help our existing customers leverage the seamless integration between Qualys Vulnerability Management, Detection & Response (VMDR), and Qualys Patch Management. Combining these two solutions can reduce the median time to remediate critical vulnerabilities.
During the webcast, we will discuss this month’s high-impact vulnerabilities, including those highlighted in this month’s Patch Tuesday alert. We will walk you through the necessary steps to address the key vulnerabilities using Qualys VMDR and Qualys Patch Management.
Join the webinar
This Month in Vulnerabilities & Patches
Good Day
Any idea of when the Unified Dashboard: 2026 Patch Tuesday (QID Based) Dashboard will be released?
What is QID for customers search?
What is the QID that customers search?
Can you please release the 2026 Patch Tuesday dashboard?
It’s a really useful tool to monitor the OS updates installations.
I hope you wull soon release the 2026 Patch Tuesday dashboard: it’s a really useful tool to monitor the OS updates installations.