Webcast Q&A: The GDPR Deadline Readiness and Impact to Global Organizations Outside the EU

With the EU’s General Data Protection Regulation (GDPR) going into effect in late May, organizations are hungry for clarifying information regarding its vaguely-worded requirements, in particular as they apply to cyber security and IT compliance. This interest in better understanding how to comply with GDPR was evident among participants of a recent Qualys webcast titled “The GDPR deadline readiness and impact to global organizations outside the EU.”
Here we’re providing an edited transcript of their questions and of the answers provided by webcast host and Qualys Director of Product Management Tim White. Darron Gibbard, Qualys‘ Chief Technical Security Officer and Managing Director of the EMEA North region, contributed to some of the answers.
Are there any recommended frameworks for implementing controls and processes for information security that I could follow to ensure GDPR readiness?
There are a variety of different ways of implementing general security best practices. There are some specific recommendations and each member country is starting to post the requirements. The most advanced one is the U.K.’s ICO (Information Commissioner’s Office). They provided a lot more depth about what InfoSec requirements you should put in place, but even their recommendations are still very vague. This isn’t like PCI where they say you have to implement a change detection solution to monitor critical changes to configuration files, and you must monitor log files on a regular basis. GDPR doesn’t have prescriptive controls like that. GDPR indicates that you have to implement the controls that are appropriate for the level of risk and that you need to protect the data from breaches of confidentiality, integrity and availability. So they basically say: “Do a good job at security.”
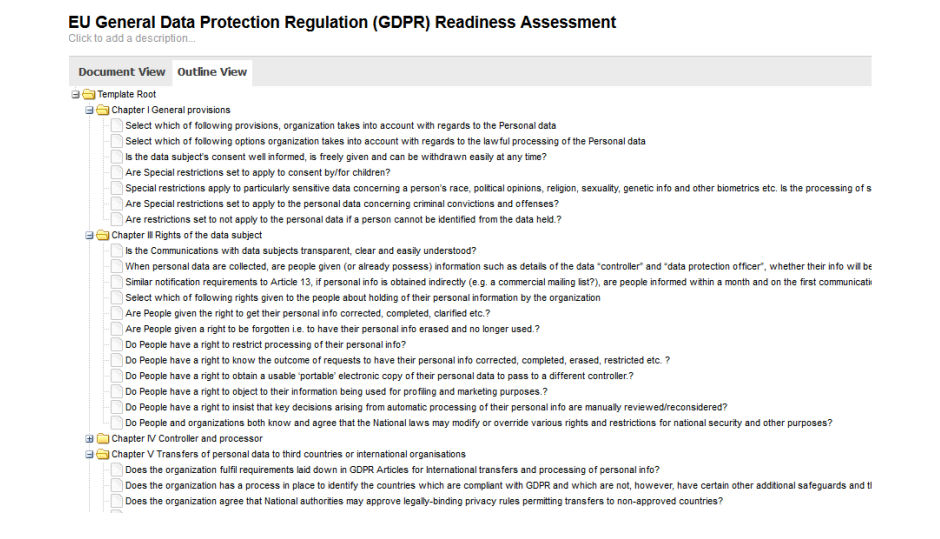
With that in mind, the framework that I like the best is the SANS Top 20 Security Controls. We’ve got a blog entry and a white paper on that on our website that walks you through how you could use that framework to implement general best practices for good security hygiene for any organization, and it covers all of the critical areas of IT security. It gives you a framework for implementing a good security program. NIST 800.53 is another good way to track things. We support all of these through our Security Assessment Questionnaire (SAQ) and Policy Compliance (PC) products, so you can pick the framework you’re most comfortable with. If you’re in the UK, you probably have ISO or other standards that you use. We support a lot of those as well.
How do I ensure my partners are held accountable for their end of GDPR?
You must build security requirements, metrics, SLAs, and other terms into the contract. They need to be measurable and enforceable. You can then automate assessment of the controls and gather evidence using Qualys Security Assessment Questionnaire (SAQ).
Should I segregate my data to reduce exposure to varying requirements across the EU?
Data crossing borders significantly complicate compliance – and are subject to potentially different and even conflicting regulatory requirements. In many cases, organizations find it easier to segregate the data or even maintain data physically within a specific regional boundary. You should assess the risk of data exposure, and classification of the data for each application and determine if data segregation would be worth the effort.
What implications does GDPR have on use of ‘data lakes’ and other Big Data initiatives?
Ensuring you have rights to process and that the processing doesn’t violate data subject rights can be a significant challenge. And when storing large volumes of data for data mining, it can be easy to accidentally violate GDPR requirements. You should evaluate the risks and classification of the data and determine if your terms of service and opt-ins from data subjects meet your requirements. If any doubt exists, you should discuss with leadership and council.
Where is the best place to track cross-functional infosec requirements and controls?
Automating assessment of controls is key to ensuring controls are appropriate and properly enforced. Using a tool like Policy Compliance (PC) and Security Assessment Questionnaire (SAQ) can help with measuring compliance against multiple regulations and reduce the effort required by enabling you to collect data once and view that data from the point of view of multiple regulations or auditing frameworks.
We do meetings worldwide with global attendees. Meetings are often in the U.S., but worldwide as well. Is it a requirement for data for a meeting in the EU to be housed on EU servers, or can we house on U.S. servers if we follow GDPR? Does GDPR apply to EU citizens at meetings in the U.S.?
Well, this depends on what the data are. If you are collecting attendee identifying information, or any other type of data that is of that risk level or higher, then you are most likely required to protect those data under GDPR. It may not be critical to host the data on an EU server, but it depends on the sensitivity level of the data, how you are using it, and what consent you have received from attendees. GDPR may apply to EU citizens at meetings in the U.S., and depending on data and sensitivity level, it may have varying levels of need for compliance.

We’re a U.S.-based non-profit organization with some EU members. How do we know if GDPR applies to us, and how do we avoid falling under the requirements of GDPR?
If you collect information on EU citizens, GDPR applies to you – regardless of where you are based. Enforcement may be a challenge if you have little EU exposure, but you should discuss with proper legal counsel if you are concerned.
To avoid falling under the requirements of GDPR, you have to not collect any data from or about any EU citizen. And there are some vague areas here. For example, if the EU citizen is traveling in the U.S. and you collect information about them, that may be subject to GDPR. However, if you have general statements of what you’re collecting data for and depending on the scope of the information they provide you, there may be limits to the impact.
Of course, for them to fine you, you have to be doing business in the EU. Ultimately there’ll be treaties and other ways of enforcing GDPR through national treaties. I’m not a lawyer. There are definitely legal implications that you need to talk to a law specialist about. But at a basic level, if you’re marketing services to EU citizens, even if you’re based in the U.S., you’re probably going to be under GDPR requirements. If your primary business is U.S. based for U.S. customers, and you have an occasional EU citizen using your services while traveling, it’s less likely you’ll have any significant problems with that. But from a legal perspective, I can’t say that those rules wouldn’t apply.
Does GDPR cover business contact information (name, business title, address, phone number) that has been available publicly and for a long time. I’ve heard that this basic business contact info is not part of the regulation.
Identifying information for individuals is definitely in scope, but I think we’re going to need more clarification from regulators on the extent that a name alone, or contact information shared as part of business interaction, is in scope or not. Given the low sensitivity of the information and that it’s generally available, it likely carries lower risk, if not out of scope. However, I don’t recall seeing an explicit exclusion of that data.
Returning to the front-end business workflow: Do you have to ask your end-customers for additional approval for various ways of collecting and using personal data (marketing, SMS/email/push notifications)?
Absolutely. You have to get consent, specify how you will use the data, and then only process data for reasons included in the consent. It’ll be interesting to see how this affects advertising and other services that mine large volumes of data about consumer purchases, searches, and related information.
Is GDPR mainly focused on customers, or on employees as well? If employees are within its scope, what type of information would be governed by GDPR (i.e., proxy logs, email, etc.)?
It is focused on protecting individuals’ data, which includes employees. Certainly, employee health, pay, identifying data, and other sensitive data are in scope. Most likely, acceptable-use policies related to use of technology would require that the devices are used for only business purposes, and your terms of employment should define how you use that data and what is and is not in scope for access and right-to-be-forgotten requests. Your legal and compliance teams should really look into your existing employment terms and contracts, and verify that appropriate consent is gathered for employees.
Should individual data about students and parents be accessible through an un-encrypted web server? Should the web server not be encrypted with SSL for GDPR?
In my opinion, that data is likely protected, and by allowing non-encrypted access to that data, it is being exposed to individuals that may not have the right to see or process that data. This is a general best practice and for many reasons that data shouldn’t be transmitted in the clear.
What are your thoughts on differences in “breach definition” under GDPR?
There is no difference in the definition of a breach. GDPR defines a “personal data breach” in Article 4(12) as: “A breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised. disclosure of, or access to, personal data transmitted, stored or otherwise processed.” What should be clear is that a breach is a type of security incident.
But there is a difference in the breach notification rules. So if you suffer a breach, the U.K. requires 72 hour notification and The Netherlands requires immediate notification. Those are the two extremes. Each EU member state has defined their own notification rules from immediate to 72 hours, which greatly complicates matters for your network and security operations teams. Incident management processes need to account for each of the member states’ requirements and ensure that the legal or compliance teams deal with the actual breach notification.
Is there a good way to erase all data to respond to a right to be forgotten request? That person could be anywhere in any data sets.
That is why GDPR is such a challenge. Applications need to be rebuilt with security and process features to track how data is being used, when it is collected, relate it back to consent collection data, and make it easy to find for inquiries or right-to-be-forgotten requests. Most applications will need to be redesigned to accommodate this, and process controls preventing exporting and off-purpose processing will need to be put in place.
Regarding the Middle East, if we take Kuwait for example, the Central Bank of Kuwait (CBK) is responsible for enforcing regulations and requirements, and all financial institutions are required to comply. So an argument we had with a client is that the EU can’t enforce GDPR unless the CBK review and adapt it in the Kuwaiti laws and regulations. Any comments regarding cases like these?
The extent that the law in EU is enforceable in other countries is a matter for lawyers and policymakers. My guess is that most organizations operating in the EU likely have subsidiaries, which would be required to comply. Most financial data protection requirements likely exceed the requirements of GDPR, but certainly industry verticals that are already highly-regulated will likely need to look at implications and additional control requirements.
How does the “right to be forgotten” work if there’s a law enforcement or national security request? Presumably ISIS suspects don’t get to disappear. How does this affect U.S. defense contractors or those working with NATO?
There are special provisions for that case that define different provisions for law enforcement and other government entities with a need for certain data. Tax collection and enforcement, financial records, and many other areas have special provisions as well. Otherwise, one could borrow some money and then ask to be forgotten.
I understand that there are some circumstances where you are not subject to GDPR, for instance if the only contact is because an EU resident ‘found’ your website without any effort on your part to market to them. For example, there was no effort to translate the site, no marketing campaigns directed at them, etc… Can you comment on that?
There is no issue with browsing to a site, but as soon as you start collecting the personal data you come into scope of GDPR. So a tracking cookie for example being placed on the end users’ browsers is technically collecting personal data.
What does GDPR say about genomic data (BAM, FASTQ or VCF files) ?
I’m not aware of any specific requirements for this case, but if the data is linked to an identity of a specific citizen, then it is likely classified as medical or sensitive information and would be protected.
Do you provide a “GDPR compliance report” type of template if we use the Qualys cloud services?
Yes, Qualys Policy Compliance (PC) provides reporting for Technical Controls and how they roll up to different regulatory requirements. Qualys Security Assessment Questionnaire (SAQ) provides specific content for preparedness data gathering and, in the future, data classification and review questionnaires. A number of reports on the results related to an assessment campaign can be generated.
Does GDPR apply to the U.K.?
Yes.

So if we aren’t marketing to EU citizens but they find our website on the internet, we have to prevent them from signing up or donating?
No, but you may want a general acceptable use policy. See the earlier related questions as well for more detail.
I have a system for companies, but if a user enter his personal email and phone number it’s my problem?
Your acceptable use and consent should indicate that they should not use personal information but rather business information. Your legal counsel should be able to assist you in formulating the right consent language to cover this case.
What is the best approach for tackling friction between vendors, software developers and risk assessors with regards to false positives?
False positives are not directly related to GDPR, but you should have general requirements for technical and procedural controls with your vendors along with SLAs, as mentioned above. For vulnerability requirements, an approach similar to that of PCI is a good methodology, where certain vulnerability classes have higher requirements for remediation than others.
How is the software licensed?
Qualys offers subscription licenses. License terms vary depending on which of our Cloud Apps are purchased. You can get more details by talking to one of our TAMs (Technical Account Managers) or starting a trial.
Can Qualys apps determine that any given data is personal data?
Qualys cannot directly identify personal data. Other tools and controls need to be put in place for that. Qualys can help you implement the proper security controls needed to protect against compromises of confidentiality, availability and integrity of data. It can help you with vendor risk assessments. It can help you automate data collection to gather required data for data owners, data classification, and process controls for any data you identify in your environment. Qualys can also help you track applications and assets that are used for gathering and processing protected data, allowing you to enforce security controls and best practices on those related systems.
I’ve read conflicting information about whether or not an IP address is considered personal data. Given that counter-intrusion software often uses IP address to mitigate attacks, how does the GDPR affect those security systems?
It can be considered identifying information, but alone it is less sensitive. An IP address can be personal data in some circumstances, such as when it’s linked to a login for a unique personal account. But the IP address of a corporate website or server, router or infrastructure on its own would not be personal data.
To read a summary of White’s webcast presentation, check out this recent blog post. To listen to a recording of the webcast, click here.