QualysGuard Adds Malware Correlation and Virtual Patch Solutions
The forecast is "More snow."
Hundreds of people abandoned their cars on Chicago’s Lake Shore Drive after a storm left them stuck in more than a foot of snow. Atlanta roads were nearly shut down and a Hawks game was canceled when snow overwhelmed the city’s eight snow plows. Municipalities across the nation are finding their already thin finances stretched to the limit by snow removal costs.
A nearly endless blizzard overwhelming resources with no end in sight…does this remind anybody else of vulnerabilities on a corporate network? I can envision you nodding your head in agreement, thinking of the last report with quadruple-digit vulnerability counts (even when filtered to just Severity 4 and 5). It’s not that you’re not interested in get comprehensive scanning; it would just be nicer if you could easily focus on the most important issues.
At Qualys we’ve been looking for ways to help you filter and prioritize the vulnerabilities reported by QualysGuard into more actionable – and more concise – reporting. Last year we introduced Exploitability Correlation to help focus on high-risk vulnerabilties, and over the past month we’ve worked closely with Trend Micro to introduce two new enhancements: Malware Correlation and Virtual Patch Solutions.
QualysGuard 6.16 introduced Malware Correlation with the Trend Micro Threat Encyclopedia, allowing you to determine which vulnerabilities have associated Malware. For example, the screenshot below shows that QualysGuard QID #90636 (MS10-061: Microsoft Windows Print Spooler Remote Code Execution Vulnerability) is used by STUXNET:
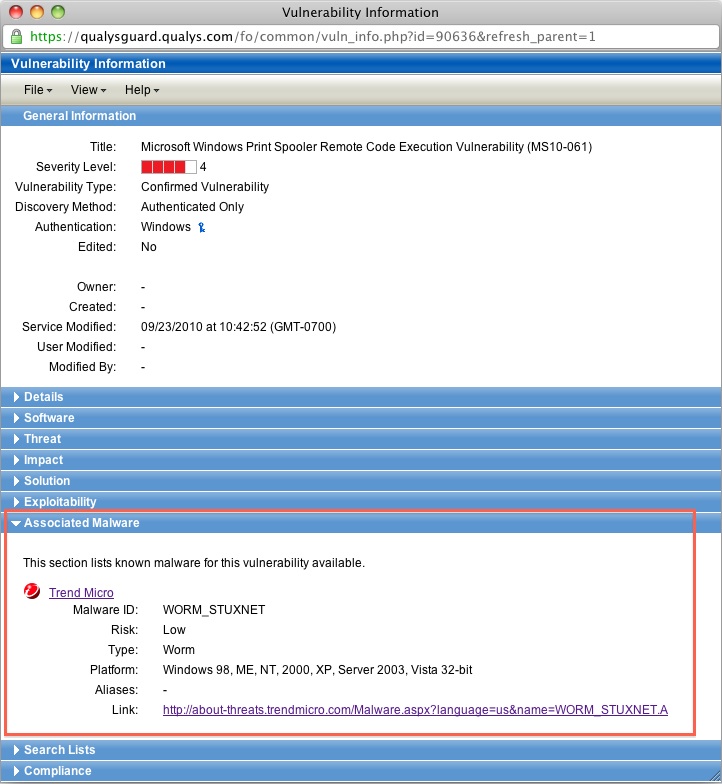
Using Search Lists that filter on QIDs with associated Malware will allow you really target the big risk items in your environment that could lead to something like a Conficker outbreak, while still having all the information on other vulnerabilities that need to be tracked and patched.
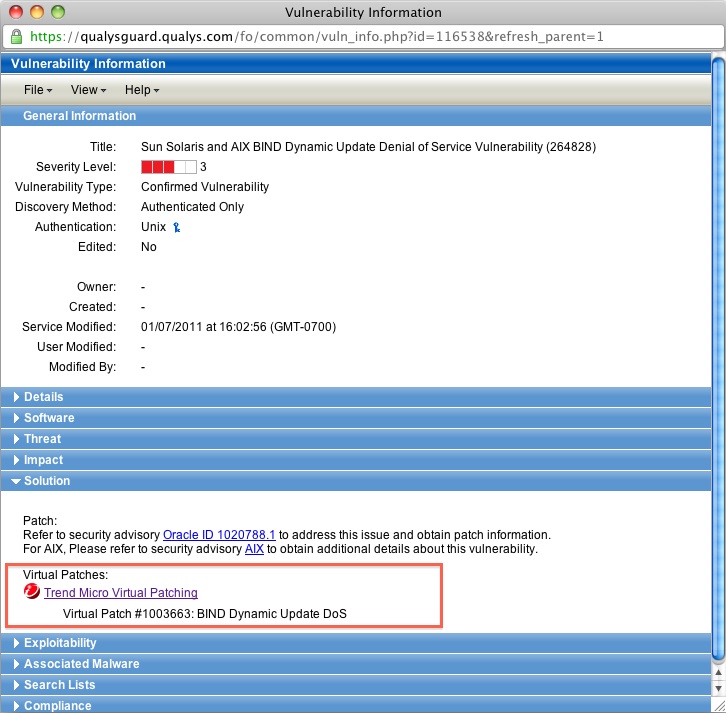
After you’ve determined the vulnerabilities that need to be fixed you now need to…well, do the fixing. QualysGuard provides comprehensive information on patches available and workarounds that can be used, and in QualysGuard 6.17 we’ve added information on the availability of virtual patches that can also help mitigate risks in your environment. A virtual patch is not a software patch per se, but is actually a mechanism – such as a HIPS firewall rule – that doesn’t actually patch the affected software but does still provide a mitigating control that reduces or eliminates the ability of an attacker to exploit the weakness. We’ve leveraged the Trend Micro Threat Encyclopedia to determine which QIDs have virtual patching solutions provided by Trend Micro Deep Security and OfficeScan + IDF as shown in this screenshot:
We’ve also expanded our Search Lists to support filtering on both vendor-provided patches and virtual patches:
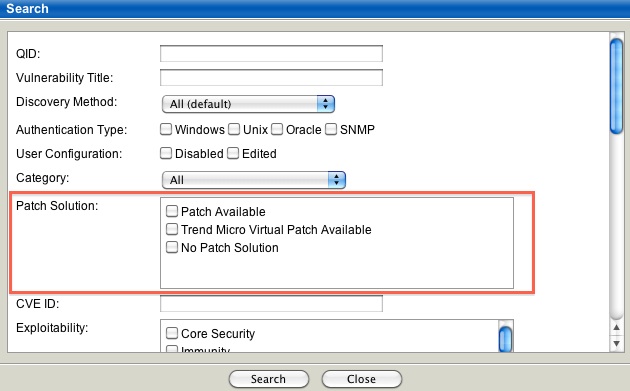
This allows you to find alternatives to applying vendor patches, especially in cases where a software patch can’t be applied (due to change control or software version dependencies) or isn’t available yet.
We’ve also tried to make it easy for you to use these new capabilities by including a few new items in our Template Library:
- Virtually Patchable Assets v.1: A report template listing high-priority vulnerabilities that can be remediated only via a Trend Micro virtual patch.
- Assets at risk of Malware v.1: A report template listing assets that have vulnerabilities with associated Malware as described by Trend Micro.
- Critical Vulnerabilities with Virtual Patches v.1: A Search List of high severity vulnerabilities with virtual patches correlated from Trend Micro.
- Critical Vulnerabilities with Associated Malware v.1: A Search List of High severity remotely-accessible vulnerabilities with associated Malware correlated from Trend Micro.
Please let us know how we can improve these capabilities to make them even more useful. In the interim, we hope you find these new features helpful in weathering the blizzard of vulnerabilities you face every day!

Are you working with any other anti-malware vendors such as Symantec, McAfee, etc.?
Also, I’d like to be able to seach on a particular Malware ID/Name and show the Hosts possibly vulnerable whereas today, you can only seach on Vulnerabilites and see if Malware is associated. If we notice a particular malware threat, it would be nice to be able to quickly do an Asset Search for all Hosts potentialy vulnerable. Today, I would need to know the Vulnerabilities (QID) associated with the Malware before I run my search. To use your own analogy, browsing through the KB for a particular Malware is a bit like trying to find a particular snowflake in a blizzard.
We will be working with other Malware vendors in the future.
Searching for Malware IDs and Names is good idea that has been suggested previously, and we are looking at enhancing our search mechansims to allow that. Stay tuned!
Is there any concrete plan for the EU release? Right now we have the Malware correlation, but not the Virtual Patching?
Hi,
If an organization is using both tools how would they analyse the coverage of virtual patching?
Do we have any common parameter or an identifier, which both Qualys+Trendmicro understand?
QID will not be identified by Trendmicro and Virtual Patch ID will not be understood by Qualys.