What are my most prevalent “worst of the worst” vulnerabilities?
Table of Contents
Showing management progress in your vulnerability management program is a sure fire way to help remove the stigma of being the "bad news bearers" team. Progress, of course, can be a daunting task when the number of new vulnerabilities per year reached thousands years ago. One way to attack this problem by getting the most bang for your buck is by remediating the most prevalent vulnerabilities — this can also reduce the average time per host for vetting the vulnerability.
QualysGuard’s Scorecard Report
QualysGuard offers a report, what we call a scorecard report, to filter out exactly this information. The scorecard report’s default setup is to display the most prevalent confirmed vulnerabilities from severity 3 on up. What may make the most sense to your organization is to reveal the most prevalent confirmed severity 5 vulnerability, as these are the most dangerous — not to mention severity 5 vulnerabilities include kiddie scripts, what a way to get owned!
| Severity | Level | Description |
|---|---|---|
 |
Serious | Intruders may be able to gain access to specific information stored on the host, including security settings. This could result in potential misuse of the host by intruders. For example, vulnerabilities at this level may include partial disclosure of file contents, access to certain files on the host, directory browsing, disclosure of filtering rules and security mechanisms, denial of service attacks, and unauthorized use of services, such as mail-relaying. |
 |
Critical | Intruders can possibly gain control of the host, or there may be potential leakage of highly sensitive information. For example, vulnerabilities at this level may include full read access to files, potential backdoors, or a listing of all the users on the host. |
 |
Urgent | Intruders can easily gain control of the host, which can lead to the compromise of your entire network security. For example, vulnerabilities at this level may include full read and write access to files, remote execution of commands, and the presence of backdoors. |
Figure – Definition of Vulnerability Severity Levels, QualysGuard Vulnerability Management and Remediation FAQ
Tailoring the Scorecard Report
Let’s step through how to edit the scorecard report to make it more useful to you. In this example, we will edit the scorecard report to only show the most prevalent severity 5 vulnerabilities.
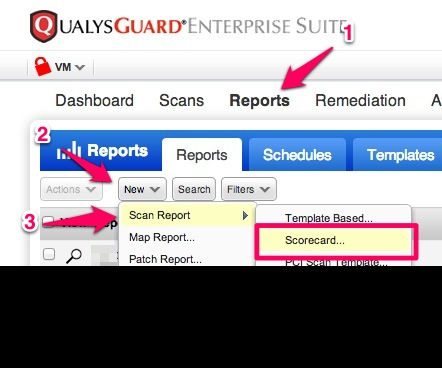
First open up the Scorecard Report wizard.
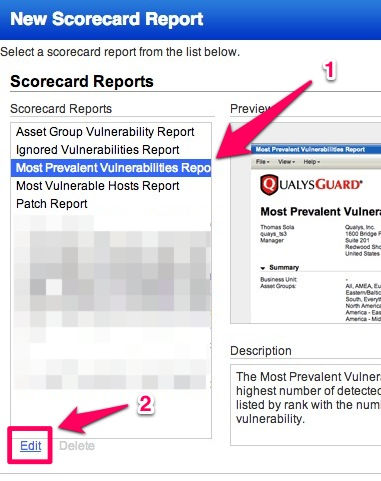
Now select the included "Most Prevalent Vulnerabilities Report", then click the "Edit" button in bottom left.
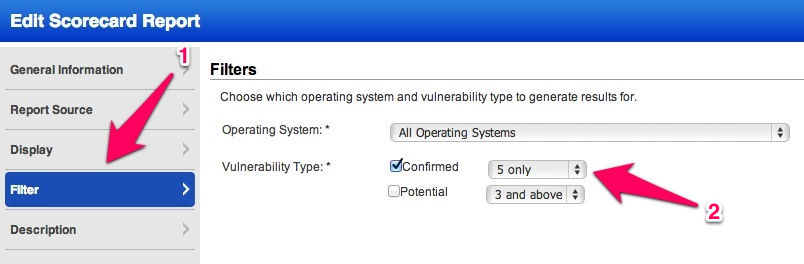
In the Filters section, change the Confirmed Vulnerability Type.
Click Save As…
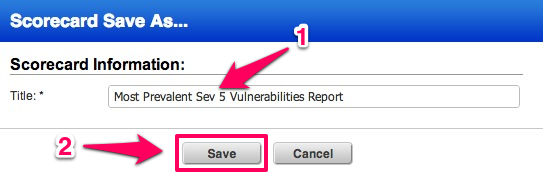
Name the scorecard something more useful now that we’re only showing confirmed severity level 5 vulnerabilities.
Now run your new report by clicking on the run button instead of the edit button.
After the fix, show it off!
Post remediation, give your operations team credit by focusing on the number of vulnerabilities remediated, rather than the number of types of vulnerabilities. What this means is, communicate the total number of hosts for each vulnerability, rather than "we eradicated these ten vulnerabilities" from the top ten report.
Not only is the total a more accurate metric of your security posture, but it is also a much higher number, too! Gains communicated like this will foster a more positive relationship between you and Operations, as well as with management.

Amazing…
This is a great feature.
See that this is also available on the Score card report for Asset Group Vulnerability Report. When you edit the filter on this report, it only allows you to select confirmed or potential. Will you be adding the option like you have on the most prevalent report you describe here to have next to the confirmed or potential, level 4 and above or level 5, etc?
We commonly use the confirmed 4 and above so I need to download this as a csv file and remove the level 3 and then we lose the percentages.
This is a solid request with practical implications. Please send your Technical Account Manager a note of this feature request, or use the Help –> Contact Support –> Feature Request option to formalize this.
When you say 'baddest of the bad', I’d want to see those that have a correlated Malware and/or Exploit associated to them, Authenticated vs Unauthenticated, and Internal vs Externally facing affected hosts.
An unauthenticated vulnerability actively being exploited in the wild detected on a non-private IP would probably be worth calling out.
Excellent point. One can build reports against these types of vulnerabilites by using dynamic search lists in report templates. For example, you could select vulnerabilities that are only found remotely, unauthenticated and can be exploited by the exploit toolkit of your choice in the List Criteria section.
is it possible to include a summary per asset group like an executive summary?