Using Dynamic Search Lists to Align Vulnerability Reporting with Patching Cycles
For Operations teams that have a patching cycle in place, it makes sense to align their vulnerability reporting with their patching cycle, so that they can show which vulnerabilities were remediated by each patching cycle. Since scanning and reporting can’t always be timed with the patching cycle, one solution is to create a report that excludes vulnerabilities that were published within a given patching cycle.
With the recent release of QualysGuard 7.4, it’s possible to create a dynamic search list based on publish date, i.e. a report that aligns with the patching cycle:
Advanced Search Capabilities for Dates in the Vulnerability Knowledge Base and Search Lists: Now users can create search queries such as “past 60 days” or “past month” for the Published Date, Service Modified Date and User Modified Date, so it becomes easy to generate reports that only focus on a specific time frame such as the past month, without the need to manually edit the filters.
With this capability, we can also create a report to exclude the vulnerabilities published after a specific date, basically the inverse. So let’s do an example together. We will create a technical report that excludes vulnerabilties older than 30 days.
Creating Reports Based on Dynamic Search Lists
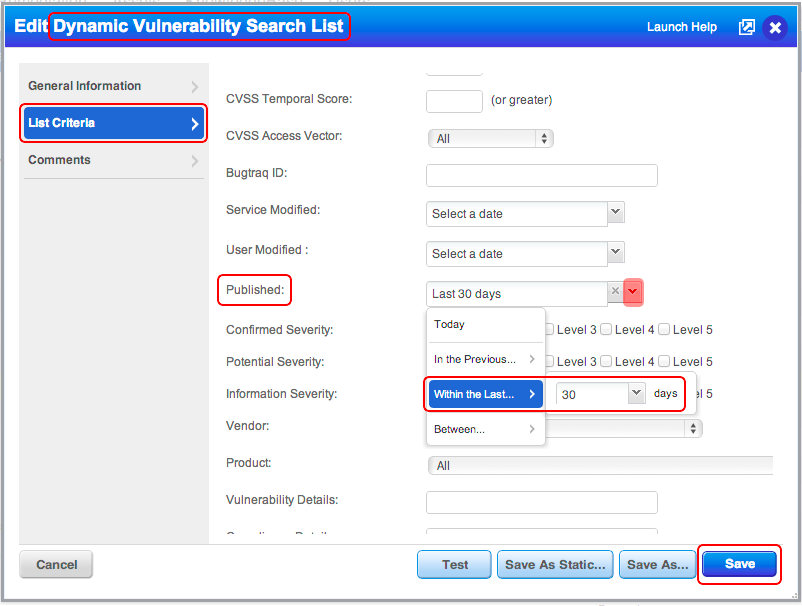
First create the dynamic search list, and within the List Criteria, modify the Publish attribute to the number of days you wish to exclude from your report. Below is an example search list to find vulnerabilities published in the last thirty days:
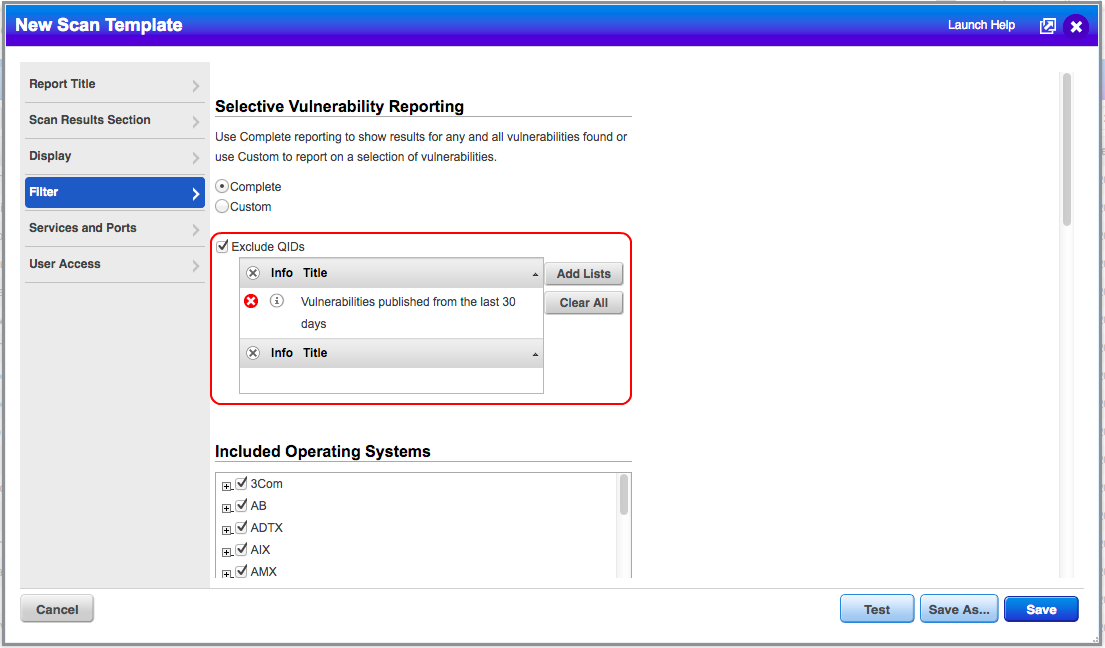
Now we create a report template to exclude vulnerabilities found from this search list.
Note that bullet for Complete is enabled. This sets the base scope of vulnerabilities. From this set of vulnerabilities, we remove "Vulnerabilities published from the last 30 days". One can tweak this report (Save As… is great for this) to cater to the report audience. For example, create a report template for just MSFT vulnerabilities, and exclude any vulnerabilities that were published in the last thirty days–you do not need to create a separate search list for the Exclude QIDs.