QualysGuard 8.1 New Features
QualysGuard 8.1 adds the following capabilities to the QualysGuard Cloud Platform and its suite of services:
- Vulnerability Management
- New Maps
- Certificate Fingerprint in Certificates Dashboard
- Lite OS Detection and Custom Header Settings
- Host Remediation Information
- Scan Report Template Improvements
- New Library Templates for Heartbleed and Continuous Monitoring
- Policy Compliance
- Directory Search UDCs
- Exception Expiring Notifications
- Policy Library Improvements
- API Enhancements
- User Defined HTTP Headers
- API Support for SCAP Scans
- Compliance Posture CSV Output
- QualysGuard Platform
- Help Tips
QualysGuard 8.1 will be released in production in the coming weeks and includes enhancements to QualysGuard Vulnerability Management (VM) and Policy Compliance (PC), QualysGuard Cloud Platform and the API.
For release notifications containing details about the release dates for specific platforms and to subscribe to release notifications by email, please see the following:
- US Platform 1
- US Platform 2
- EU Platform
- API Notifications (for all platforms)
QualysGuard Vulnerability Management (VM)
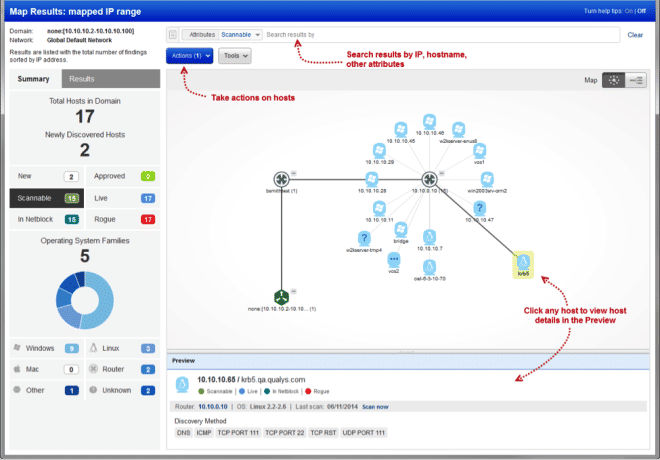
New Maps
QualysGuard VM Map Scans provide the ability to search the network for active assets, discover the relationships between interconnected networks, and ensure that newly discovered assets are authorized and regularly assessed. Network maps have a great new look and feel, and we’ve enhanced the functionality to allow for better filtering and searching. You’ll have all the functionality you had before – filtering by OS and discovery method, workflow actions, and the ability to drag and drop hosts, pan, zoom and expand/collapse nodes. Plus you get a new results summary, more layout options, filtering by host attributes (approved, scannable, etc) and you can search for hosts by IP and hostname.
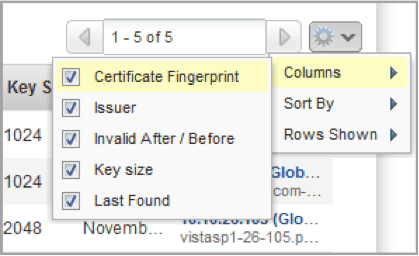
Certificate Fingerprint in Certificates Dashboard
QualysGuard provides an inventory of all SSL certificates detected via scans, and customers can use this report to manage the administration, renewal, and configuration of those certificates. With the emergence of issues such as Heartbleed it is critical to be able to uniquely identify a certificate, so we’ve added the Fingerprint of the certificate to both the Dashboard and the downloadable reports.
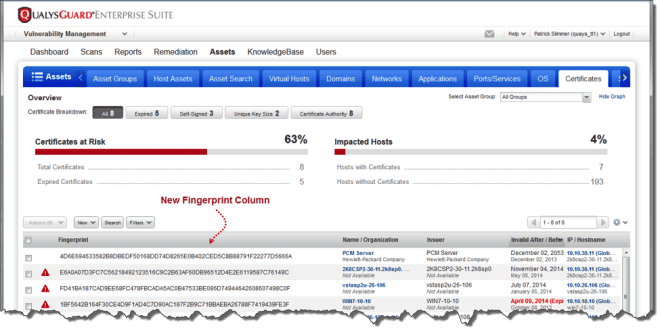 The Fingerprint is hidden by default, but can be enabled via column display settings:
The Fingerprint is hidden by default, but can be enabled via column display settings:
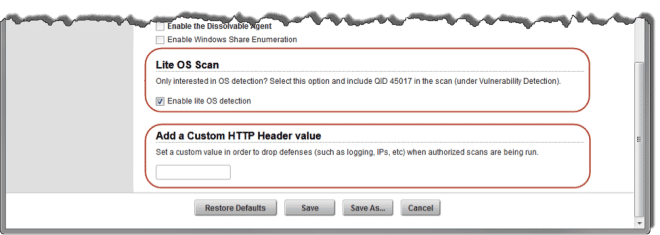
Lite OS Detection and Custom Header Settings
QualysGuard VM now supports the ability to tune Option Profiles to reduce the amount of “noise” created in logs when performing scans.
The Lite OS Scan option setting will reduce the number of checks we use – and consequently the number of potential log items and host alerts – when determining the Operating System for QID 45017. This allows customers to make the decision to trade off some detection accuracy in order to reduce NOC/SOC alerts and increase the speed of detection.
QualysGuard VM performs a number of tests on detected web servers, and these checks will often show up as activity in logs, IDS/IPS systems, and web application firewalls. In order to allow customers to filter out this authorized activity, QualysGuard now allows the configuration of a Custom HTTP Header that will be set for many CGI and Web Application checks. The header “Qualys-Scan: <your value>” can be set in the Option Profile.
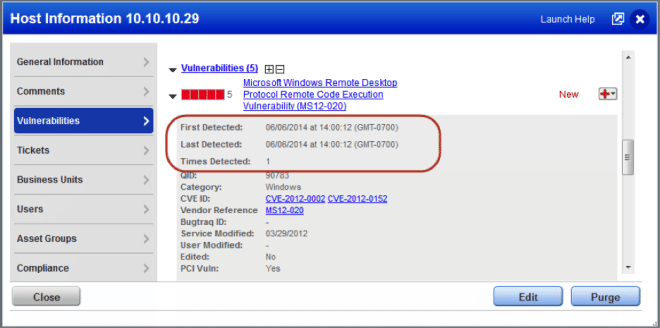
Host Remediation Information
QualysGuard VM provides a host information page that lists the state of an asset including ownership, detected vulnerabilities, ticketing and exceptions, etc., so that customers can drive remediation and risk reduction in their enterprise. We’ve added key metrics to allow you to see how quickly vulnerabilities are being detected and remediated, and provide a grade based on industry best practices so that you can benchmark the effectiveness of your vulnerability management program.
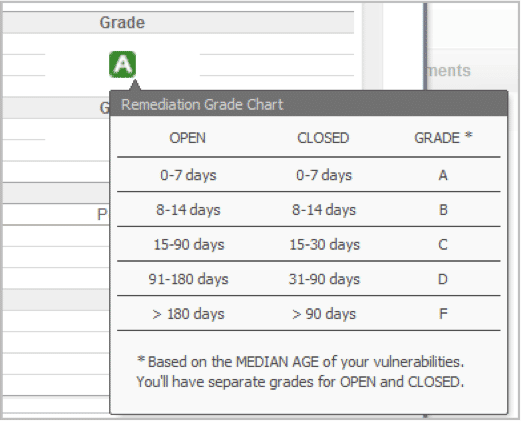
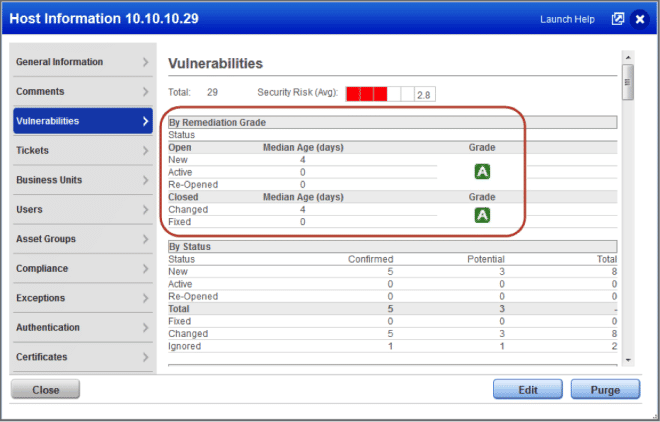 You can mouse-over the assigned grade to see the criteria used:
You can mouse-over the assigned grade to see the criteria used:
 Additionally, we’ve added information about detected vulnerabilities to allow you to track down longstanding issues or verify the remediation status and timeframes.
Additionally, we’ve added information about detected vulnerabilities to allow you to track down longstanding issues or verify the remediation status and timeframes.
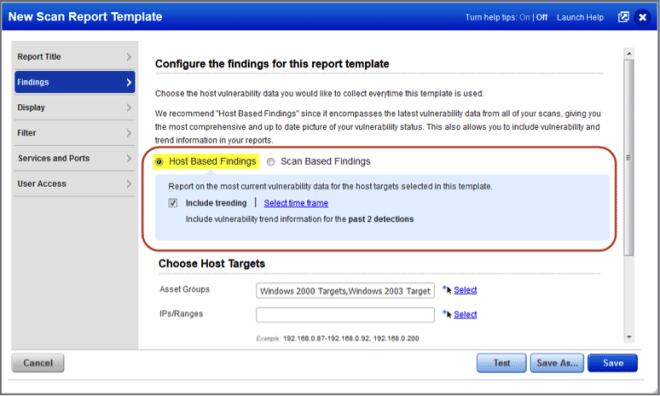
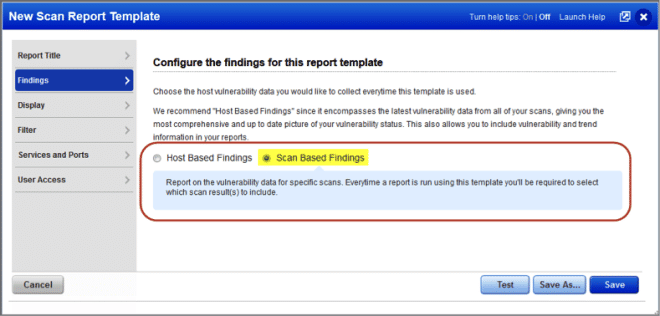
Scan Report Template Improvements
QualysGuard VM provides the ability to see the state of an asset at a single point in time as well as track the changes to an asset over time, so that customers can understand both their current risk and the effectiveness of their remediation efforts. In the past this has been called “automatic” and “manual” data, but we’ve clarified the names to more accurately reflect what these capabilities are.
Host Based Findings (formerly “automatic”) are recommended to give you the most comprehensive and up to date picture of your vulnerability status. Use this option to run a report on the latest vulnerability data from all of your scans. Each time you create a report with this setting, we’ll automatically collect vulnerability data that we’ve indexed per host in your account.
Scan Based Findings (formerly “manual”) are recommended when you need to see the results of a single scan at a single point in time. When choosing this option you must pick the saved scan results that will be used.
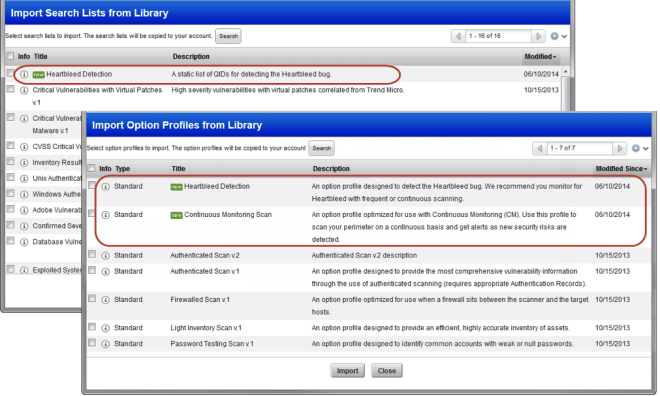
New Library Templates for Heartbleed and Continuous Monitoring
The Template Library provides several pre-configured options to allow you to quickly start using QualysGuard VM for common tasks such as reporting on critical vulnerabilities that have in-the-wild exploits, listing database vulnerabilities, etc. We’ve added two new templates that help you use our recently-released capabilities:
- Heartbleed Detection Option Profile and Search List: This allows you to quickly detecting and report on the Heartbleed bug. We recommend you monitor for the Heartbleed bug with frequent or continuous scanning.
- Continuous Monitoring Scan Option Profile: This profile is tailored to use with the Continuous Monitoring (CM) application to scan your perimeter on a continuous basis and get alerts in CM as new security risks are detected
QualysGuard Policy Compliance (PC)
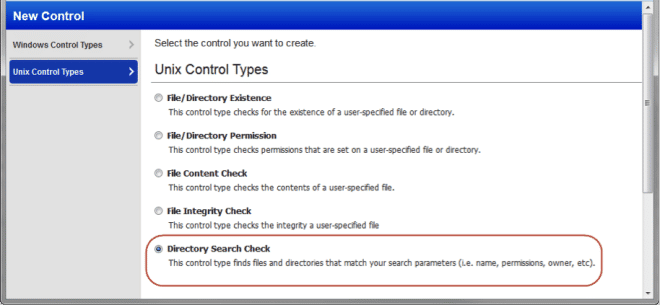
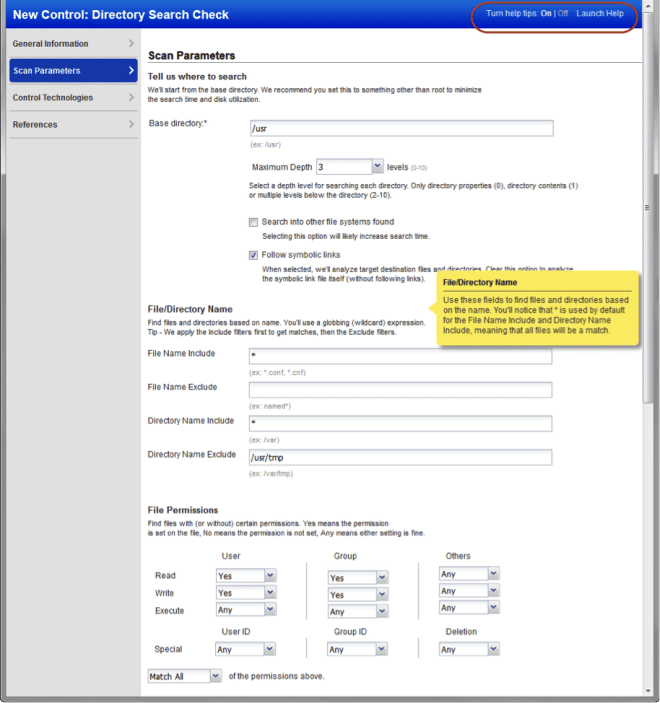
Directory Search UDCs
Many QualysGuard PC customers find that detecting specific types of files – spreadsheets with financial data, files with insufficiently restrictive permissions, etc. – is an important part of their compliance programs. We’ve added the new Directory Search User Defined Control (UDC) to allow customers to identify and list those files. Directory Search checks can be found under the Unix Control Types tab:
Once selected, you can configure all the criteria you want to select the matching files, including wildcard names, paths, and file permissions.
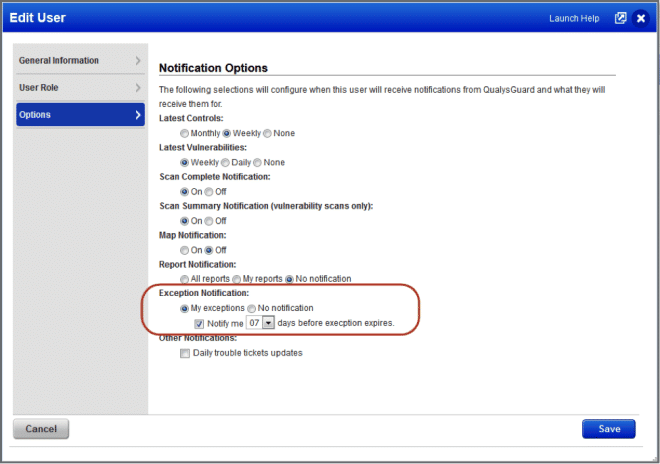
Exception Expiring Notifications
Exceptions can be granted in Policy Compliance to allow customers to combine technical results with business risk decisions, such as a willingness to provide an extra 30 days to remediate issues on critical production systems. We’ve added notifications to make stakeholders aware when an exception is nearing expiration so that they can address the issue or request an extension.
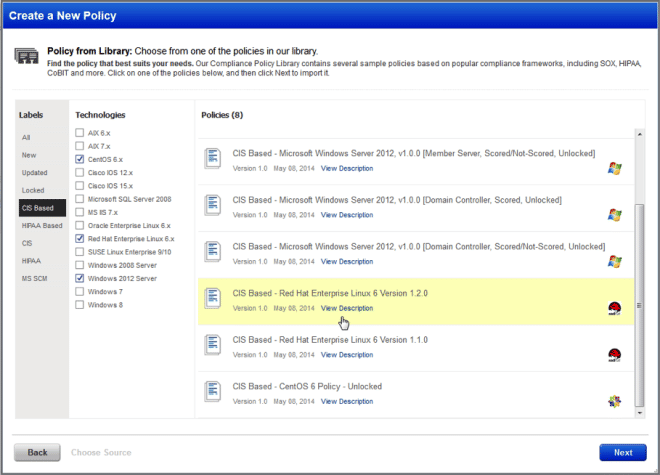
Policy Library Improvements
The Template Library provides several pre-configured options to allow you to quickly start using QualysGuard PC with common compliance standards such as CIS Benchmarks, HIPAA policies, etc. We’ve made it faster and easier to find and import policies into your subscription so that you can quickly start using these policies.
QualysGuard API
Additional details about the changes below can be found on the Qualys 8.1 API Notification.
User Defined HTTP Headers
As described above, a Custom HTTP Header that will be set for many CGI and Web Application checks QualysGuard VM so that customers can filter out logs from this authorized activity. This header can be configured via the runtime_http_header parameter for many scan APIs.
Support for SCAP Scans
The QualysGuard SCAP scan list capability available via the Qualys API, enabling customers to implement automation to scale and integrate your compliance program with the QualysGuard PC/SCAP application. A new API endpoint (/api/2.0/fo/scan/scap/?action=list) is available to view and download results.
Compliance Posture CSV Output
To increase automation capabilities and simplify integrations, we’ve added a CSV output option has been added to the Posture API (/api/2.0/fo/compliance/posture/info/?action=list).
QualysGuard Cloud Platform
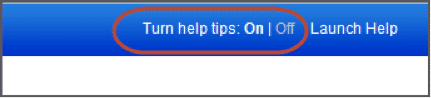
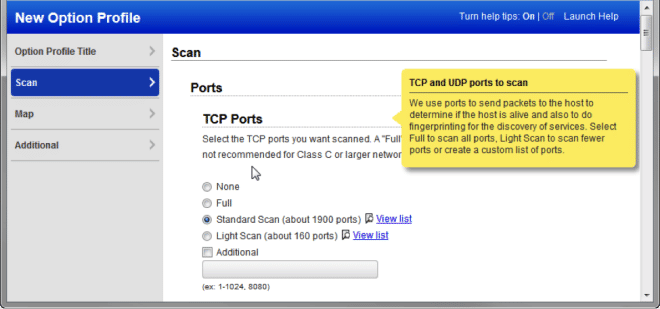
Help Tips
The QualysGuard Cloud platform continues to expand its capabilities, and many Qualys customers are making use of these capabilities. We’ve added mouse-over help tips to many places in the user interface so that you can get immediate help and context on new features and capabilities, allowing you to quickly get the benefits of these new capabilities. You can turn on help tips with a single click:
Tips provide quick content to supplement the online help, and look like this:
Thanks for this update Corey, I do have a question about the Heartbleed Bug Search List you guys created. Is there a reason this is a static list of QIDs? Is this list going to be maintained by Qualys? This list currently only has 3 QIDs in it but in your Knowledge base there are 15 QIDs that reference back to the Heartbleed Bug, are they duplicates?
Thanks again!
downinej,
the idea for the Heartbleed Bug Search List is to have the fastest way to check for active Heartbleed vulnerabilities and at the same time generate enough data to feed into the Certificate Manager (VM-Assets) where one can use the Filters for Heartbleed to manage the certificates that were emitted before the vulnerability was detected.
We have tested this Search List with some larger setups and found that one can scan a 100,000 IP perimeter with 5000 active hosts in under 8 hours. We then combined that scan with a Continuous Monitoring ruleset and profile and had a very workable Alerting system for new (found new vulnerabilities where IT staff installed systems based on older images) and existing Heartbleed instances.
Because of this focus (fast, non-authenticated) we do not forsee adding other QIDs to the Search List.
You are completely right that adding the remaining Heartbleed detections is a more comprehensive solution. If you are running authenticated scans I would recommend creating a new profile based for those scans.
Best,
–
Wolfgang