End the Nightmare of Vulnerability Disclosure Overload: Keep Calm and Prioritize
Overwhelmed by the mounds of vulnerabilities in their IT environments, many organizations struggle to prioritize remediation, but you can overcome this challenge with the right approach

Steve, an information security manager, is again rattled awake at 3 a.m. by a recurring nightmare: He’s at work and his desk suddenly gets transformed into a mile-long Whack-A-Mole cabinet with thousands of holes. But instead of toy moles, what springs up from the cabinet holes are red square signs, each displaying a different CVE number.
Mallet in hand, a flustered Steve quickly realizes there’s no way he can hit every CVE sign before time runs out. Worse, he gets no points for hitting the ones that pose no threat to his IT assets: He only gets rewarded when he whacks one that could seriously compromise his IT environment.
But he can’t tell which vulnerabilities are trivial and which ones are devastating. Not at this speed and at this scale. Not with the changing IT security requirements of his company. After a while, a strident bell signals the end of the game. Frowning and agitated, Steve’s boss walks in. The company has been hit by a devastating ransomware attack. Steve lost.
In many organizations, dealing with security vulnerabilities has become such a nightmare. New vulnerabilities are disclosed every day, amounting to thousands per year, and organizations can’t patch all of them. They must identify which vulnerabilities are the most dangerous to their infrastructure at any given point in time, so they can fix those first.
In this three-part blog series, we’ll discuss key requirements for successfully prioritizing vulnerability remediation, so that Steve’s nightmare doesn’t become your reality.
To Prioritize Vulnerability Remediation, First Compile a Complete, Detailed Asset Inventory
To pinpoint the most dangerous vulnerabilities, organizations must first have a comprehensive, continuously updated view of all of their IT assets. This inventory must list all of the organization’s assets, whether they are on premises, in the cloud or at mobile endpoints, and whether they are permanently or intermittently attached to their network.
When prioritizing vulnerability remediation, it’s what you don’t know that derails your efforts. At the most basic level, this means being aware of all the hardware and software in your organization, from high-end systems to mobile apps.
Simply put, an invisible, “rogue” IT asset whose existence you ignore can’t be analyzed for vulnerabilities. If it contains critical vulnerabilities, it becomes your weakest link, a latent risk waiting to be exploited by an attacker at any moment.
There can be no “phantom” servers, PCs, smartphones, tablets, printers, applications, middleware and the like lurking in your network without your knowledge. You must have a complete, unobstructed view of your IT environment at all times, and be instantly aware of its changes.
You also need granular, detailed access to the components of each IT asset, and understand how extensively each asset is interconnected with and dependent on other systems. Finally, it’s critical to know what role each asset plays in your overall IT environment and how valuable and important it is to your organization.
This contextual knowledge and detailed data form the foundation upon which you can then begin the process of prioritizing vulnerability remediation. Absent this underlying information structure, your attempts to assess vulnerability risks will be ill-informed and ultimately erratic.
The Qualys Approach
Powered by Qualys AssetView (AV) and Vulnerability Management (VM) apps, the new Qualys ThreatPROTECT solves this common but thorny challenge.
Qualys VM and AV take care of vulnerability discovery and detection, and of IT asset inventories, respectively, while ThreatPROTECT analyzes that internal data and correlates it with external threat disclosures.
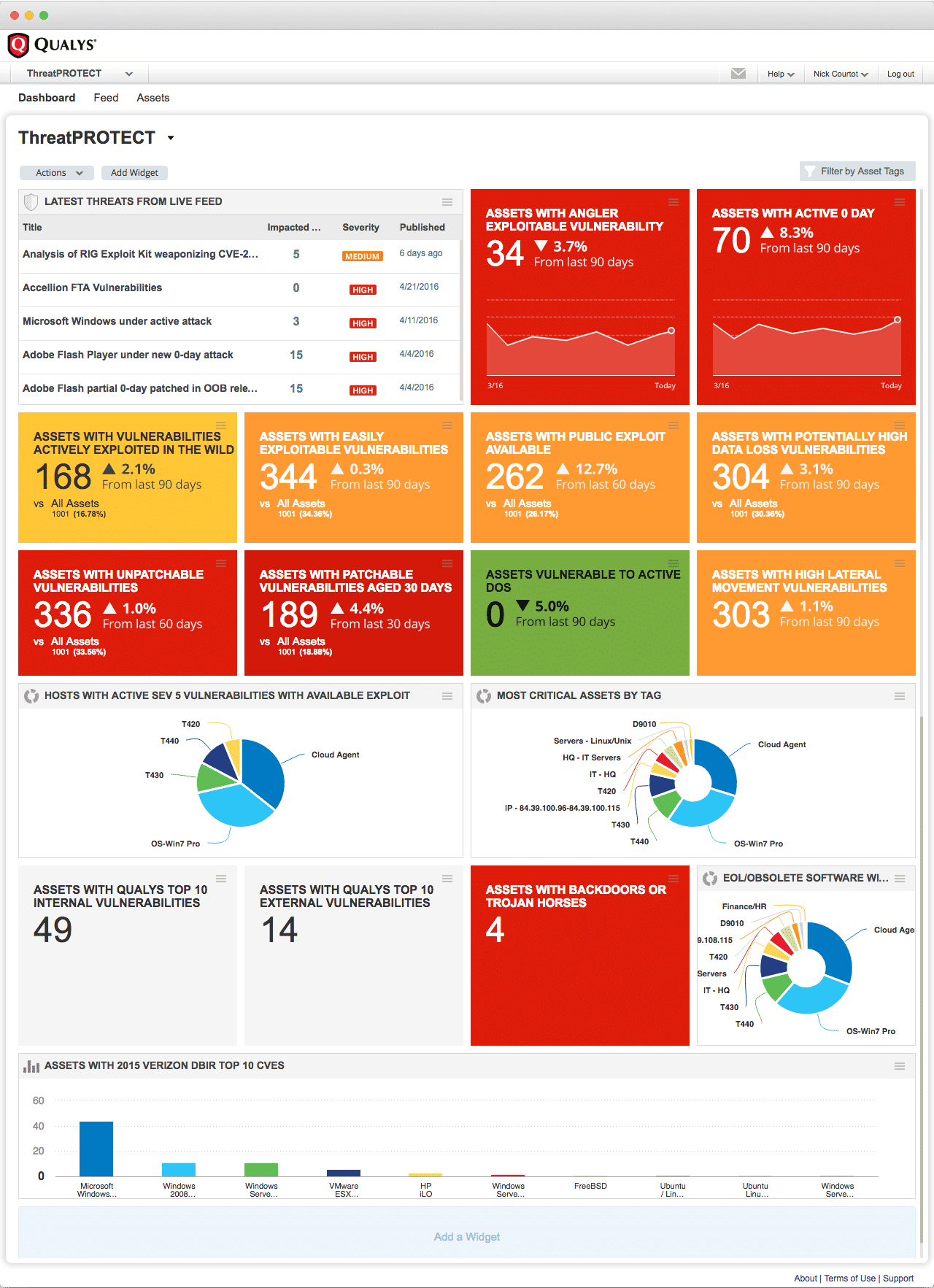
The result: Infosec teams get a comprehensive, holistic and continuously updated view of their IT asset vulnerabilities, presented in a central dashboard so that they can prioritize and actively decide which need to be fixed right away.
With Qualys, your IT assets are all either proactively scanned or continuously monitored by our agents, and they are always accounted for. You also get component and configuration details on all of your IT assets, and we help you understand their role and importance in your IT environment.
With this comprehensive and detailed IT asset inventory, you’ve fulfilled the first requirement for successfully prioritizing vulnerability remediation.
On our second installment next week, we’ll dive into the importance of always having a complete and updated knowledge of vulnerability disclosures and of correlating external threat information with the vulnerability gaps that exist in your IT environment.
For more best practices, download our whitepaper “Prioritizing Vulnerability Remediation in the Age of Threat Disclosure Overload.”