Lasso In Employee Training, Vendor Regulatory Compliance with Automated Risk Assessments
We continue our series on assessing third-party risk, where we’re describing scenarios in which an automated, cloud-based system can help you identify security and compliance gaps among vendors, partners and employees.
In addition to protecting their organization’s IT environment, CISOs must also closely monitor the security and compliance policies and procedures of trusted third parties.
In this series’ first and second installments, we told you a tale of two CISOs — Jane and Emily — whose fortunes diverge as a result of this important but sometimes overlooked issue of third-party risk assessment.
At about the same time, their organizations’ hired a back-office services outsourcer, granting it access to their respective companies’ data and IT systems.
Years later, the outsourcer started faltering financially, technologically and operationally, becoming a risk to its customers.
Emily had put in place a formal, comprehensive, centralized and automated program for assessing third-party risk, so her organization promptly cut off ties with the outsourcer.
On the other hand, Jane’s organization lacked such a program. As a result, it belatedly realized how dangerous this business relationship had become when its customer data was compromised after hackers broke into the outsourcer’s network.
Assessing Business Process Risk Is an Inside-Outside Game
Conducted via surveys that people have to fill out, business process control assessments evaluate areas of an organization such as its business continuity plans, physical and environmental security tools and practices, operational risk safeguards, financial standing and human resources procedures.
Although their focus is usually on monitoring third parties, such as vendors, partners, suppliers, service providers and contractors, these risk assessments must also be conducted internally. That’s because organizations need to ensure employees, managers and business units are complying with their policies, industry best practices and with government regulations.
In this post, we describe two scenarios that illustrate the need for internal and external cloud-based, automated risk assessment. One — inefficient coordination of employee training — applies to the inside workings of an organization. The other — failure to monitor regulatory compliance within the organization as well as by its third parties — speaks to both internal and external risk assessment efforts.
Inefficient Coordination of Employee Training
Organizations must make sure their staff is aware of their policies and procedures, a task that is tricky for the obvious reason that employees are constantly joining and leaving.
This challenge is particularly acute in companies where turnover is high due to the nature of the business, such as the seasonality of retail stores.
Just like staff is in constant flux, internal guidelines and rules also get revised frequently due to a variety of reasons: technology changes, mergers and acquisitions, business scope modifications, geographic expansion and the like.
As a result, organizations need agility and speed to frequently perform these employee assessments as often as necessary, often via short, simple questionnaires.

They also need an automated system to ensure administration of these surveys to the right individuals or groups on staff, and at the right times.
Examples of important areas for assessment include IT security practices, such as best practices for managing email, and proper social media etiquette.
Email is a preferred vector for cyber criminals to attack organizations via malware-laden messages, phishing attempts and whaling schemes. Social media gaffes by employees can earn a company a lawsuit or bad press.
A cloud-based risk assessment app automates and accelerates this process of evaluating the effectiveness of employee training and process-awareness programs.
The app simplifies the distribution of surveys and management of campaigns, as individual employees are on-boarded, and as part of regular training sessions for groups or the entire staff.
Once these processes are moved into the cloud, the app can help you certify and document that all employees have been properly educated and trained about security policies, threats, compliance requirements and business risks.
Failure To Keep Up with the Ever-Changing Regulatory Burden
It’s common for organizations to struggle staying on top of new and changing regulations that apply to them, especially in industries under heavy government oversight, such as banking and healthcare.
Regulations are never simple, and they’re getting more complicated, while new ones come out every year, a situation that gets exponentially more difficult the more countries an organization does business in.
It’s challenging enough to understand regulations’ often convoluted rules, so it’s even more complicated to craft corresponding risk assessment surveys for your employees and vendors. Heightening the importance of this, governments are increasingly placing the onus on organizations for screening the regulatory compliance of the third parties they do business with.

In other words, an organization may be penalized for the regulatory non-compliance of its vendors and their business processes, products and services. Lack of awareness is not a valid excuse.
With a cloud-based risk assessment automation solution, this process is centrally managed and continuously updated by its developer as the regulator landscape changes, including its template library.
This means that you don’t need to worry about manually updating these pre-built questionnaires — it’s all done for you transparently in the background by experts on these rules and regulations.
Security Assessment Questionnaire
If your organization faces either or both of these scenarios, Qualys Security Assessment Questionnaire (SAQ) would be a good solution to consider. Qualys developed SAQ because the traditional way of conducting these risk assessment surveys — emailing questionnaires and tracking responses on a spreadsheet — no longer cuts it.
With SAQ, you can automate these polls — both externally and internally — to ensure the process is agile, accurate, comprehensive, centralized, scalable and uniform across your organization.
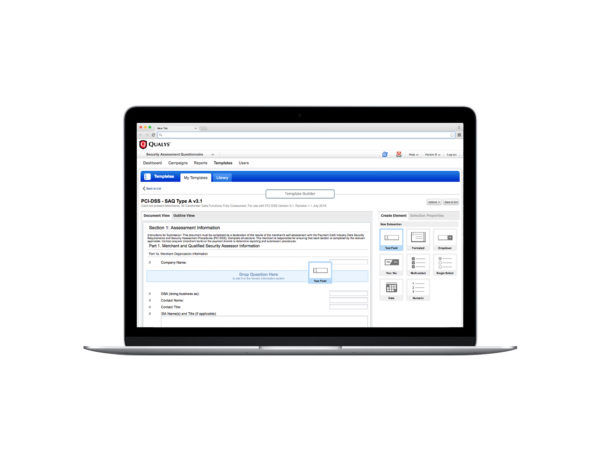
SAQ gives you a centralized, comprehensive view across your business process risk assessments. That way you can know if your staff or your third parties are putting your organization at risk of customer data theft, cyber crime, IP espionage, brand damage and government fines.
Try Security Assessment Questionnaire for free with nothing to install.
We’ll wrap up this blog series next week with one last scenario — a deficient method for tracking your fast-changing vendor landscape — and a deep dive on how SAQ works and all it can do for your organization’s efforts to assess third party risk.