Meltdown/Spectre: Intel Nixes Patches, Tech CEOs Questioned on Information Blackout
IT departments and tech vendors continued grappling with Spectre and Meltdown this week, as Intel pulled its glitchy patches and the U.S. Congress questioned the vulnerability disclosures’ timing and scope.
Spectre and Meltdown aren’t typical vulnerabilities for a number of reasons, and as a result, they’ve proven problematic to deal with. Intel, whose products are the most impacted, has had a particularly rocky time crafting its firmware updates for mitigating the bugs.
After receiving multiple complaints from customers, in particular data center operators, that the firmware updates for Broadwell and Haswell CPUs were causing systems to unexpectedly reboot, Intel on Monday finally deep-sixed them.
“We recommend that OEMs, cloud service providers, system manufacturers, software vendors and end users stop deployment of current versions, as they may introduce higher than expected reboots and other unpredictable system behavior,” Navin Shenoy, executive vice president and general manager of Intel’s Data Center Group, wrote in a blog post.
The silver lining is that, according to Shenoy, Intel has discovered the “root cause” for the firmware’s problems, and is actively developing new updates that it’s already testing.
Meanwhile, the U.S. Congress’ House Energy and Commerce Committee said on Wednesday it wants to know why a small group of tech vendors kept the information about Spectre and Meltdown secret for months — between the vulnerabilities’ discovery in June and their public disclosure on Jan. 3rd.
The committee sent letters to the CEOs of Apple, Amazon, AMD, ARM, Google, Intel and Microsoft, stating that “this situation has shown the need for additional scrutiny regarding multi-party coordinated vulnerability disclosures.”
The letter goes on to say that “cybersecurity is a collective responsibility,” and that it’s no longer limited to the IT industry, given that now there are Internet-connected products in many other sectors, including utilities, healthcare and manufacturing.
Signed by U.S. Rep. Greg Walden, a Republican from Oregon and committee chairman, and by three other members, the letter asks, among other things, why the information was kept confidential, which company or companies proposed this information embargo, and when was the US-CERT (United States Computer Emergency Readiness Team) notified.
The CEOs, which have until Feb. 7 to respond, also must say whether they took into account the potential negative impacts of the information embargo on critical infrastructure sectors and on individual companies that were kept in the dark.
The Lowdown on Meltdown and Spectre
The main reasons that set Meltdown and Spectre apart from most vulnerabilities are that they’re hardware flaws, and that their scope is massive, affecting most Intel CPUs released in the past 20 years, as well as a smaller quantity of ARM and AMD CPUs.
Meltdown (CVE-2017-5754) provides access to all physical memory, including kernel memory, via a user mode, ring 3 process, so that “any process running in the system can access all the contents of physical memory,” as Qualys Product Management Director Jimmy Graham said recently during a webcast.
Attackers could steal passwords, grab private keys and do whatever necessary to escalate their system privileges to administrator levels. “Anything that can be stored in memory can be accessed through Meltdown,” Graham said.
Meanwhile, Spectre (CVE-2017-5753, CVE-2017-5715) impacts Intel, AMD, and ARM CPUs by abusing branch prediction and speculative execution, resulting in data leakage from compromised processes. “An attacker process on a system can access the memory contents of other process, and can include kernel memory in some circumstances,” Graham said.
Tips, Best Practices and Resources
Graham offered the following recommendations for managing the Spectre and Meltdown mitigation process.
- Detect vulnerable assets using Qualys Vulnerability Management authenticated scans or with Qualys Cloud Agents. It’s crucial to have a clear idea of how many impacted systems are in your environment, which vulnerabilities you have, and which patches have been applied.
- Prioritize patching efforts based on asset risk and exposure. If you can’t install the microcode patches because they’re problematic or non-existent at this point, focus on the OS and browser patches. “For workstation type devices, I’d focus on patching the underlying OS, because performance concerns are not as great, compared to servers, and patch the browsers as well to start enabling some of these mitigations,” Graham said.
- Test and test again. “Everything needs to be tested. These patches are not simple software patches that we’ve seen previously. These are fundamental changes to how the kernel is treated in Linux and in Windows,” he said.
- Tests should go beyond simply verifying that updates and patches they’ve been successfully installed. You must test workloads on servers. “You don’t want to be blindly installing these patches on very critical database systems without testing them with some kind of load,” Graham said.
- Make sure third-party antivirus software is up to date.
- Install browser patches for workstation type-devices.
- Patch virtual systems such as Xen and VMWare.
- Patch Windows workstations and servers with the most recent January patches.
- Install microcode packages for Linux and BIOS updates for Windows
Qualys now has more than 75 QIDs to determine the patch state for Spectre and Meltdown. Qualys provides both agentless scanning and agent-based detections, so you can use the most appropriate method for any given IT asset.
In addition, Qualys recently rolled out a pre-built Spectre/Meltdown Dashboard to give you visibility into the remediation progress. It can be downloaded from the Qualys Community site.
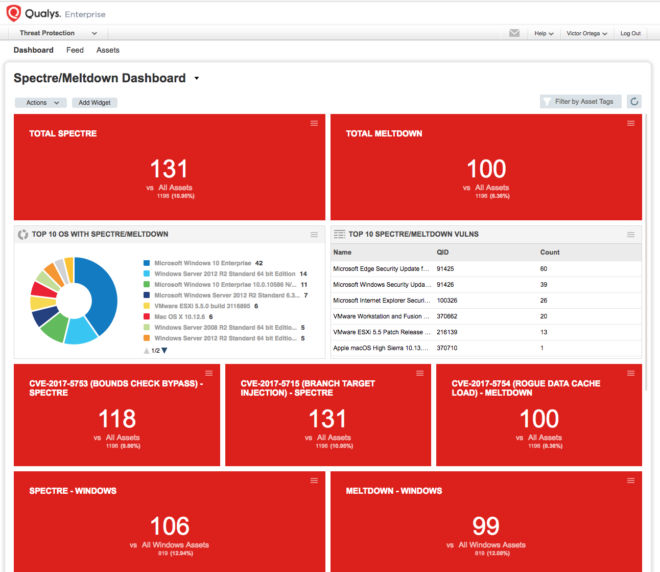
You can also find detailed and illustrated instructions on how to create Qualys Search Lists, Scan Option Profiles, Remediation Tracking and Patch Reports for Spectre and Meltdown in this article published to our community site by Debra M. Fezza Reed, Qualys’ Product Manager for Reporting.
Graham’s webcast also includes a demo of the new Spectre/Meltdown dashboard, and his answers to questions from the audience.