Updated Qualys WAS Plugin for Jenkins Now Available
We are pleased to announce that version 2.0 of the Qualys WAS plugin for Jenkins is now available. This version of the plugin introduces a more user-friendly design and new features to facilitate automation.
What’s New?
Whereas the previous release of the plugin supported only Jenkins pipeline projects, the new version works with both pipeline projects as well as traditional freestyle projects. The main difference is that for a pipeline project the plugin outputs a snippet of script code that you insert into your overall pipeline build script. With a freestyle project, the plugin allows you to configure a post-build action. Either way the end result is having a WAS scan launch automatically as part of your build.
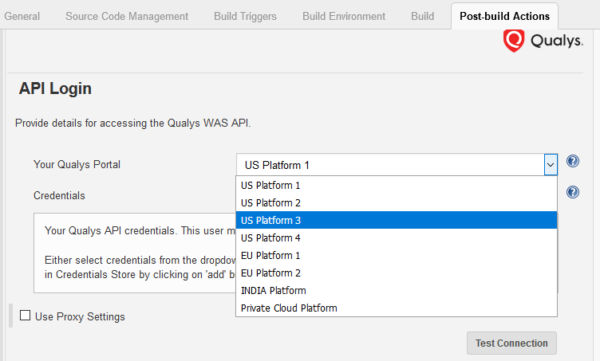
With version 2.0 of the plugin you no longer need to enter the Qualys API server URL. Simply choose which Qualys shared platform your organization is using and the correct URL will automatically be used. We currently have 8 shared platforms around the globe. Please note if your organization is using a Qualys PCP (private cloud platform), then you’ll still need to enter the API server URL.
The new version of the plugin leverages the WAS API to a greater extent. This means you no longer have to know the ID of the web application in WAS that you wish to scan. After entering valid Qualys credentials, the plugin automatically retrieves the list of available web applications from WAS and you can just select the correct one. The same is true if you wish to use a specific authentication record or a specific option profile for the scan. No need to enter the ID. Just select the desired one from the list.
Fail the Build Automatically
One of the best new features in v2 of the plugin is being able to specify pass/fail criteria for the build based on scan results. Let’s say you want the build to be marked as “fail” if any severity 5 vulnerability is found by the scanner OR if the application is vulnerable to cross-site request forgery (QID 150071 in WAS represents CSRF). This is easily configured as shown in the following screenshot:

Scan Results, in the Plugin
Once the scan has finished, the plugin now provides an option to view summary-level scan results. You’ll quickly be able to see the scan duration, the number of links crawled, whether or not the scanner successfully authenticated to the app, as well as vulnerability count for each severity level. If you had configured pass/fail criteria within the plugin, you’ll also see the specific criteria that was triggered (if any) which caused the build to fail.

To see all the Qualys QIDs found during the scan, click Vulnerabilities on the left side. This presents the data in tabular format. But for detailed scan results, including specifics about the vulnerabilities (request, response, how to fix, etc.), click the link on the Summary page to open the Scan Report (you will need to authenticate to the Qualys platform).
Using Bamboo or TeamCity Instead?
If you’re using Bamboo or TeamCity for your CI/CD tool instead of Jenkins, check out our WAS plugin for Bamboo and WAS plugin for TeamCity. These plugins have essentially the same feature set.
Security in DevOps
The rapid pace of software development and the transition to a DevOps model require innovative approaches to security. With our latest plugins, automating web app vulnerability scanning in your CI/CD process is easier than ever.
Any good reason not to push this into the central Jenkins plugin repo? No one installs hpi files locally.
Publishing it there has some specific requirements, such as releasing the code as open source on GitHub. It’s a possibility down the road.
Update: The plugin is now published, so you can do a direct install from within the Jenkins interface.
Any plans to bring a similar plugin to Azure Pipelines?
Yes. The Qualys WAS Connector for Azure DevOps is now available – see https://marketplace.visualstudio.com/items?itemName=Qualys-Inc.was-build-release-task