Monitoring AWS Golden AMI Pipelines with Slack
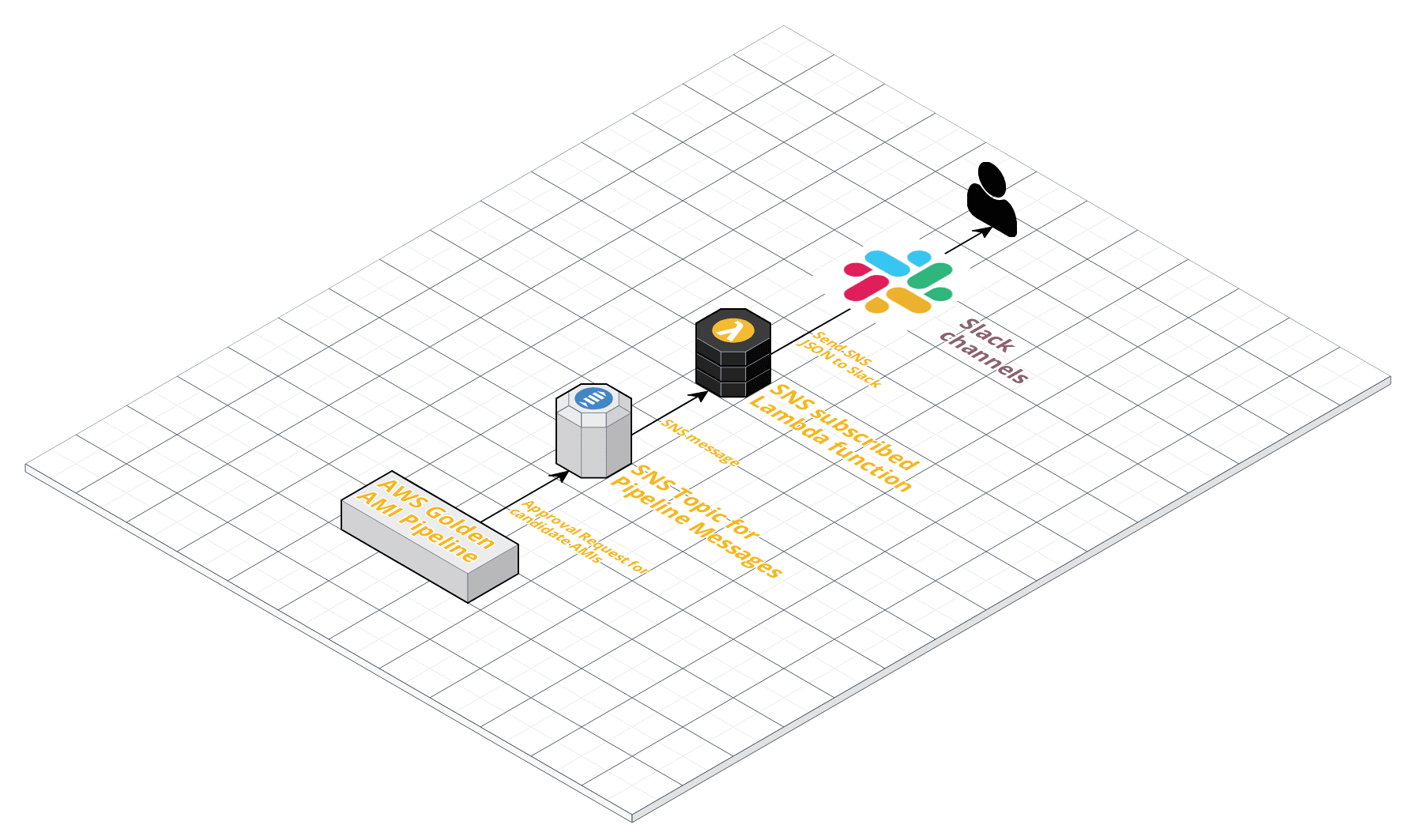
If your company uses Slack and is looking for ways to easily monitor activities in its AWS Golden AMI Pipeline, you can use AWS native services to send messages into a Slack channel. This can give your teams better visibility into the approval process for the candidate AMIs that they submit, as opposed to handling this via email. As we all know, email messages can get lost, overlooked or dumped in spam folders, which doesn’t happen with Slack messages. Moreover, Slack channels can have multiple subscribers so a single message can be seen by multiple people or other bots. Handling approval requests within a Slack channel also simplifies the management of the process.
Read on for a detailed, step-by-step explanation.
Getting Started
Slack configuration
You must first configure Slack to receive messages from the Golden AMI Pipeline. To do this you need to create a new channel – or choose an existing channel — to receive the notifications: For example “#aws-gap-updates”. Next you will configure a Slack app for “Incoming WebHooks”. This can be done by logging into your Slack account via a web browser and navigating to your account’s Slack App Directory and typing in “Incoming WebHooks” into the search bar.

Select “Incoming WebHooks” and then click “Add Configuration” on the next screen.

On the app configuration screen, choose a channel for the WebHook and click “Add Incoming WebHooks Integration.”

At this point, you will see the configuration information for your Slack App Incoming WebHooks. Scroll past the example data down to Webhook URL. This is the URL you will use to send messages to this Webhook. Copy this unique link so it is easy to retrieve, as you will need it later when setting up a Lambda function to send messages received from the Golden AMI Pipeline SNS topic.
AWS Lambda Function
Creation
There are many examples of Lambda functions for processing events and executing some code, so I will not cover that here. The basics of the function is that it needs to intake a message from the SNS topic and then send that message to the desired location. For this to happen, the Lambda function will need four pieces of required information and one optional configuration item.
Slack information for Lambda:
- Channel
- Username
- Text
- Icon Emoji (optional)
- Path
The Channel setting will direct the message to the channel configured in the Slack Webhook configuration and the Path will be the Slack Webhook URL from above. The Username is what will appear in the Slack channel as the sender of the message, and the text will either be the raw SNS notification or the specific data you extract from the message. The Icon Emoji can be used to specify the icon used for the sender of the Slack message. You can use any of the standard Slack emojis or a custom emoji of your choosing.
Configure
After creating your AWS Lambda function to process SNS notifications and send them to your designated Slack channel, you will need to subscribe the Lambda function to the SNS topic. Information on subscribing the Lambda function to a SNS topic can be found here.
Test
Make sure to test and validate both the Lambda function and the SNS subscription to send messages from the AWS Golden AMI Pipeline. You can test fire the Lambda function with an example SNS message to validate functionality and then trigger a test SNS message from the SNS topic to verify the subscription and desired functionality.
Final Thoughts
Once you have the candidate AMI approval messages being sent to the Slack Channel, you can look to expand what messages or SNS topics get sent. This can include the creation of other SNS topics for specific functions or triggered actions and reusing the configured Lambda function to send other messages. One example would be to expand the Golden AMI Pipeline’s steps to include additional logging via SNS messages sent to your Slack channel. You could also look at building out a Slack bot for submission of candidate AMIs to the Golden AMI Pipeline. There is a great GitHub example at https://github.com/esanchezm/amazon-cloudwatch-to-slack/ if you would like to explore these scenarios further.
(Sean Nicholson is a Security Solution Architect for Cloud Security at Qualys)