Empower your Cloud Ops Teams – Publish Qualys CloudView Security Assessment Reports to their Slack Channel
In today’s constantly changing and evolving cloud environments, being able to quickly provide information on misconfigurations and security policy violations in your cloud accounts and assets has become a critical need to the success of your security operations. Many cloud platforms offer tools within their specific cloud environments to provide this type of visibility. However, security operations teams are quickly learning that in a multi-cloud environment, they need tools that provides this information across all three major cloud providers in a seamless and centralized way, with normalized data streams. They need a single source of truth for their account security regardless of the public cloud provider or the asset metadata.
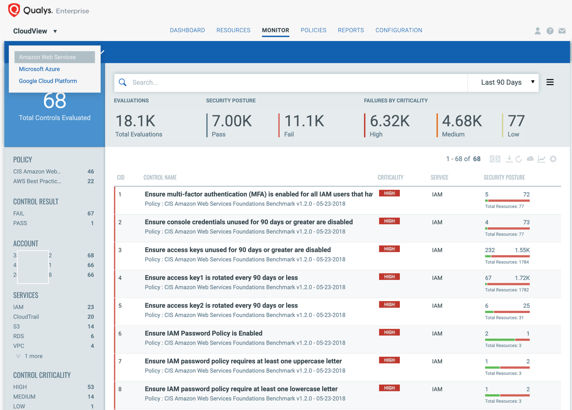
Qualys understands this problem and announced last year Qualys CloudView. CloudView today works across the largest public cloud platforms, providing Cloud Inventory (CI) and Cloud Security Assessment (CSA) on the cloud accounts and the associated assets security configurations. Providing this unified visibility regardless of cloud provider is quickly becoming a go to tool for security operations teams.
The next question has become: “How do we provide this information to our cloud operations teams within the toolsets they are already using?” As with any tool that is successful in the cloud space, the CloudView API can help.
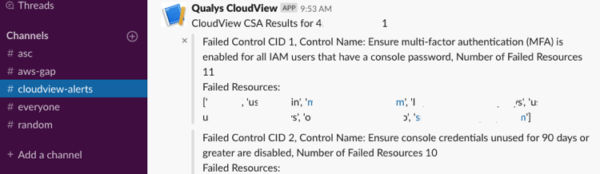
Qualys has published a script to create a CloudView CSA Report for a cloud account and publish this to an associated Slack Channel via a Slack incoming webhook.
Archiving and Audit
Additionally, the script can create a corresponding CSV report for archiving or saving in an audit record. These reports will highlight which controls have failed resources and the list of failed resources for each control per cloud account. Once the report has run, the script provides this report to the cloud operations teams within the tools they are already using, like Slack.
If you are not using Slack, you could still utilize the CSV reports functionality or take the provided framework to create your own integration with a messaging or automation tool in use in your environment.