Managing CISA Known Exploited Vulnerabilities with Qualys VMDR
CISA released a directive in November 2021, recommending urgent and prioritized remediation of actively exploited vulnerabilities. Both government agencies and corporations should heed this advice. This blog outlines how Qualys Vulnerability Management, Detection & Response can be used by any organization to respond to this directive efficiently and effectively.
Situation
Last November 2021, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) released a Binding Operational Directive 22-01 called “Reducing the Significant Risk of Known Exploited Vulnerabilities.” This directive recommends urgent and prioritized remediation of the vulnerabilities that adversaries are actively exploiting. It establishes a CISA-managed catalog of Known Exploited Vulnerabilities that carry significant risk to the federal government and sets requirements for agencies to remediate these vulnerabilities.
This directive requires federal agencies to review and update internal vulnerability management procedures to remediate each vulnerability according to the timelines outlined in CISA’s vulnerability catalog.
Directive Scope
This CISA directive applies to all software and hardware found on federal information systems managed on agency premises or hosted by third parties on an agency’s behalf.
However, CISA strongly recommends that public and private businesses as well as state, local, tribal, and territorial (SLTT) governments prioritize the mitigation of vulnerabilities listed in CISA’s public catalog. This is truly vulnerability management guidance for all organizations to heed.
CISA Catalog of Known Exploited Vulnerabilities
CISA has overall released 654 Common Vulnerabilities and Exposures (CVEs) that pose the highest risk to federal agencies. CISA’s most recent update was issued on April 25, 2022.
The Qualys Research team is continuously updating CVEs to available QIDs (Qualys vulnerability identifiers) in the Qualys Knowledgebase, with the RTI field “CISA Exploited” and this is going to be a continuous approach, as CISA frequently amends with the latest CVE as part of their regular feeds.
Out of these vulnerabilities, Directive 22-01 urges all organizations to reduce their exposure to cyberattacks by effectively prioritizing the remediation of the identified Vulnerabilities.
CISA has ordered U.S. federal agencies to apply patches as soon as possible. The remediation guidance is grouped into multiple categories by CISA based on attack surface severity and time-to-remediate. The timelines are available in the Catalog for each of the CVEs.
Detect CISA Vulnerabilities Using Qualys VMDR
Qualys helps customers to identify and assess the risk to their organizations’ digital infrastructure, and then to automate remediation. Qualys’ guidance for rapid response to Directive 22-01 follows.
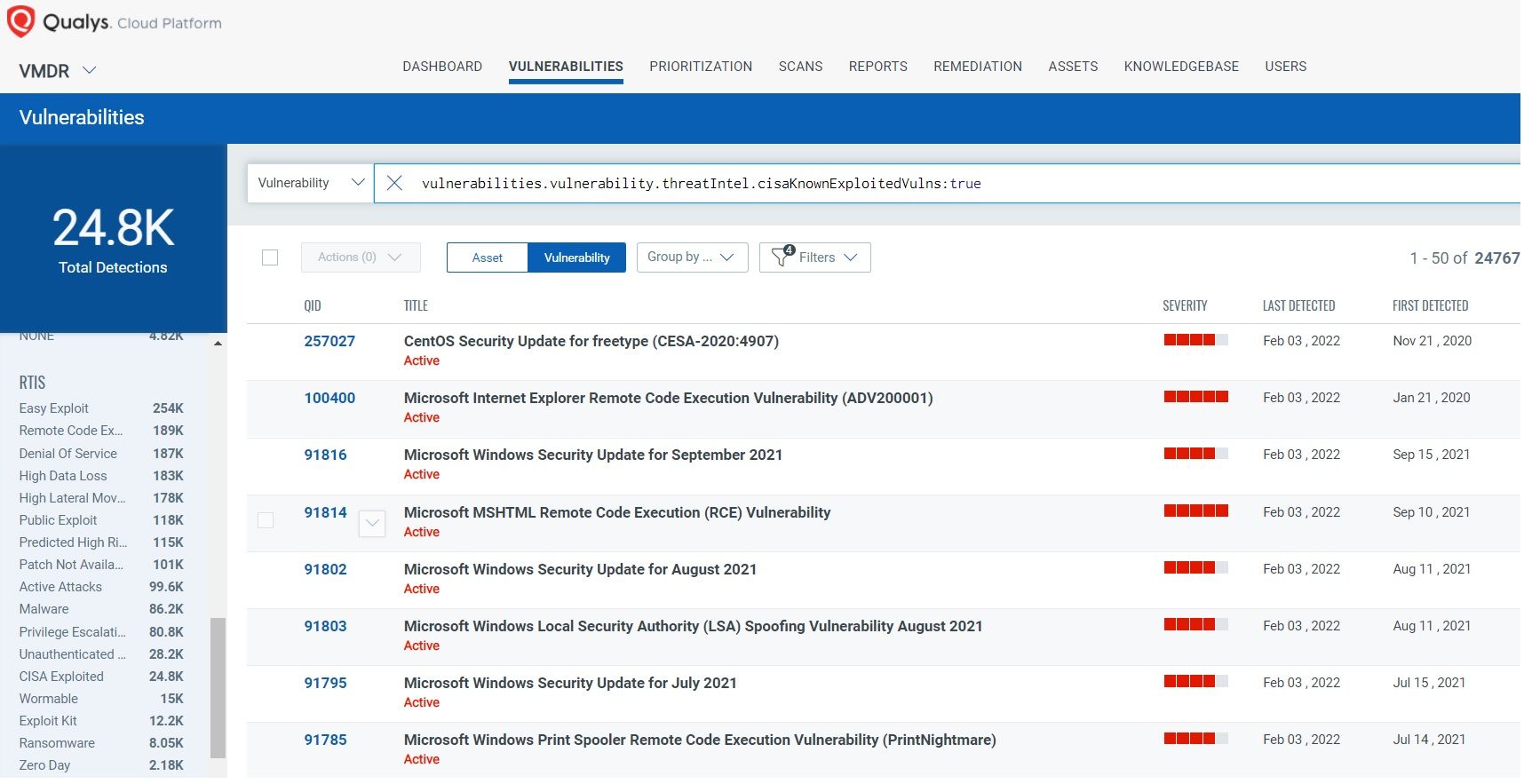
The Qualys Research team has released multiple remote and authenticated detections (QIDs) for these vulnerabilities. Since the directive includes 379 CVEs (as of February 22, 2022) we recommend executing your search based on QQL (Qualys Query Language), as shown here for released QIDs by Qualys vulnerabilities.vulnerability.threatIntel.cisaKnownExploitedVulns:”true”
CISA Exploited RTI
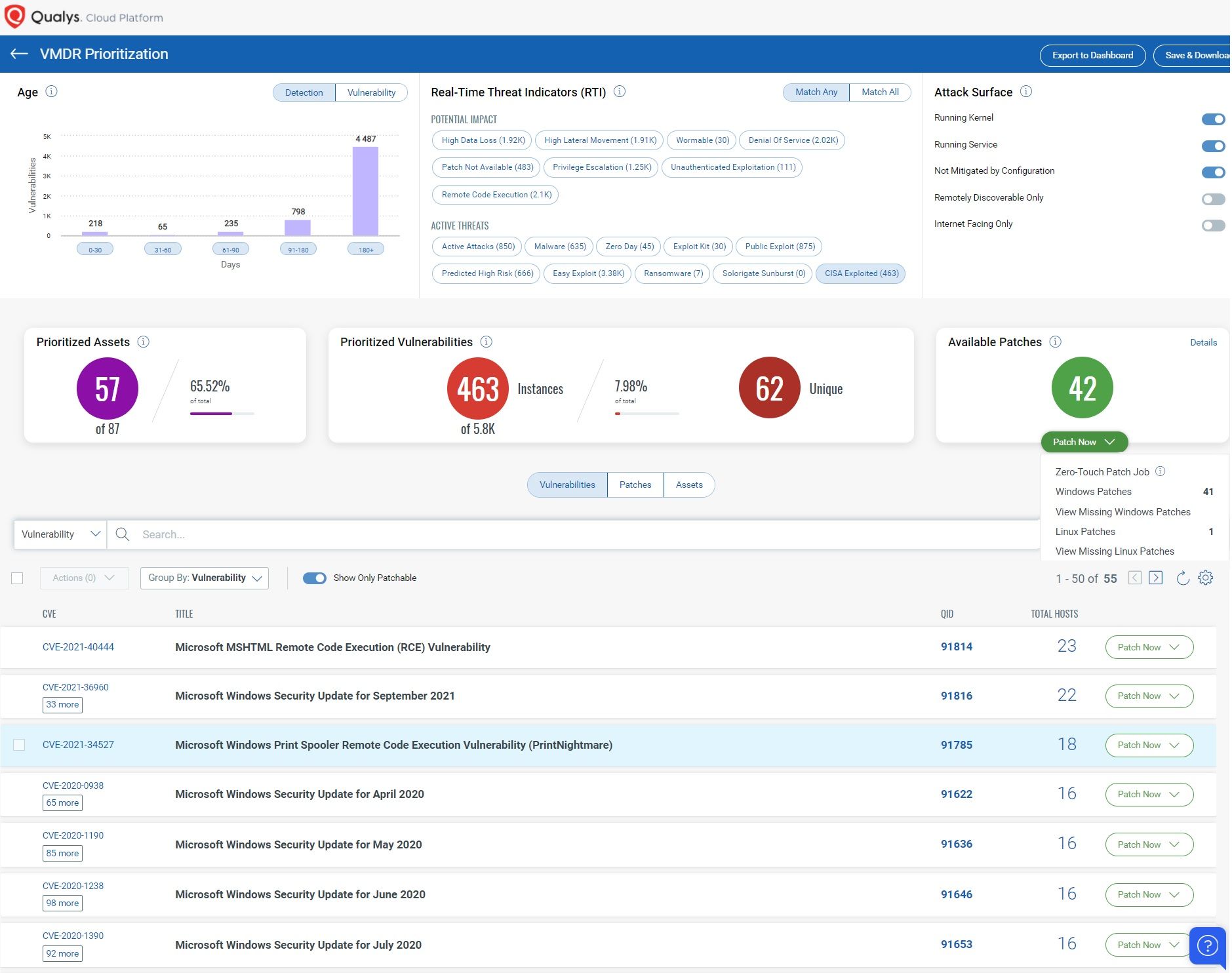
Using Qualys VMDR, you can effectively prioritize those vulnerabilities using VMDR Prioritization. Qualys has introduced an RTI Category, CISA Known Exploited Vulnerabilities.
This RTI indicates that the vulnerabilities are associated with the CISA catalog.
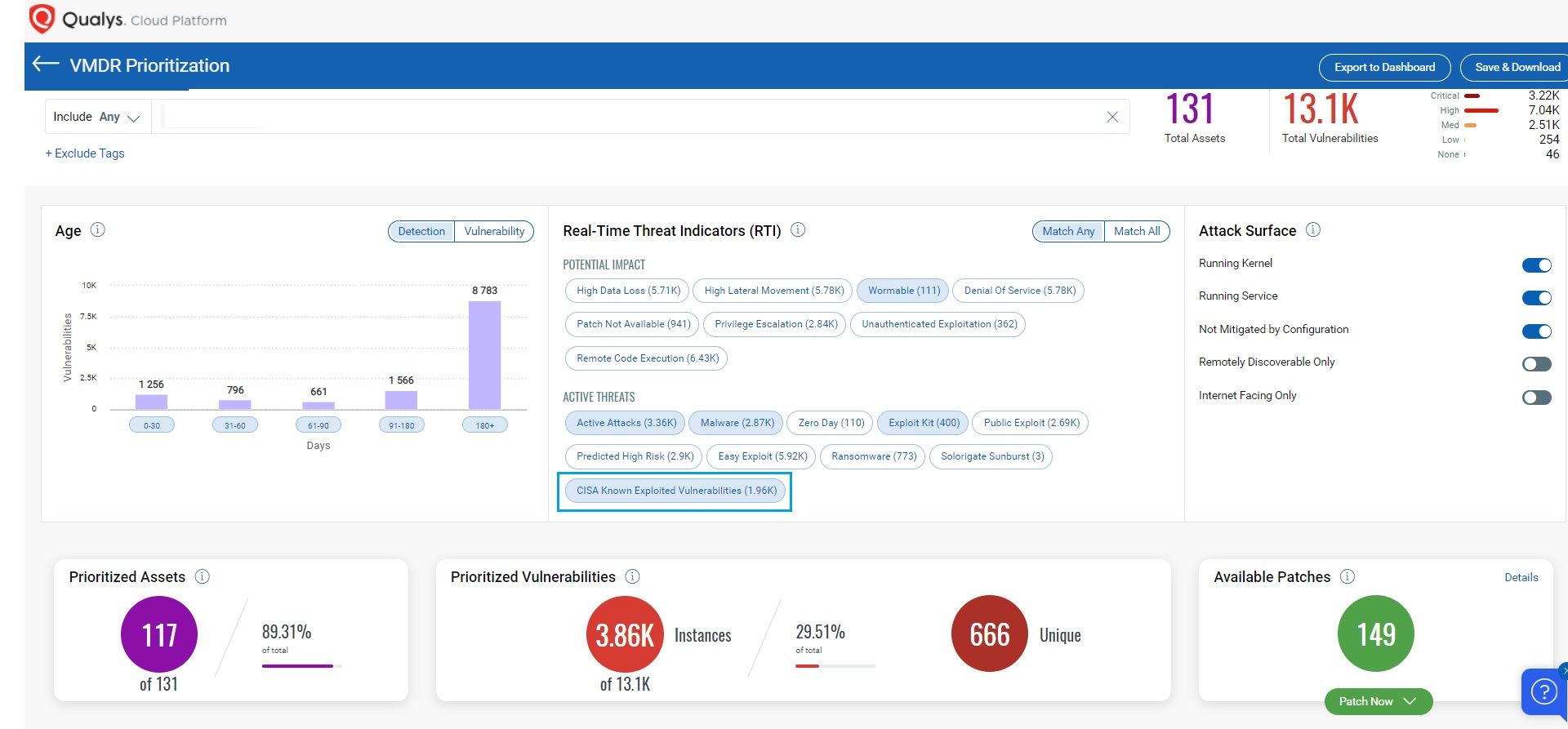
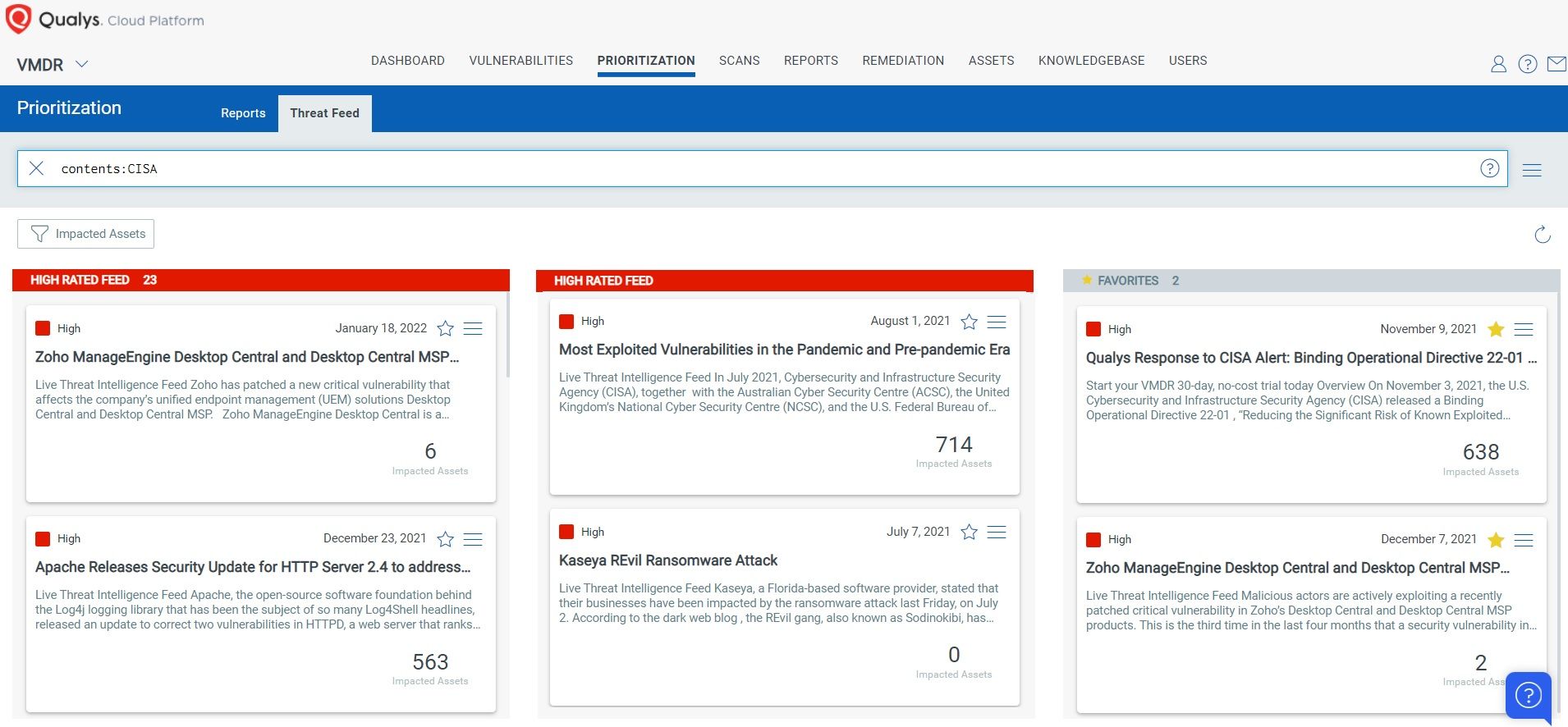
In addition, you can locate a vulnerable host through Qualys Threat Protection by simply clicking on the impacted hosts to effectively identify and track this vulnerability.
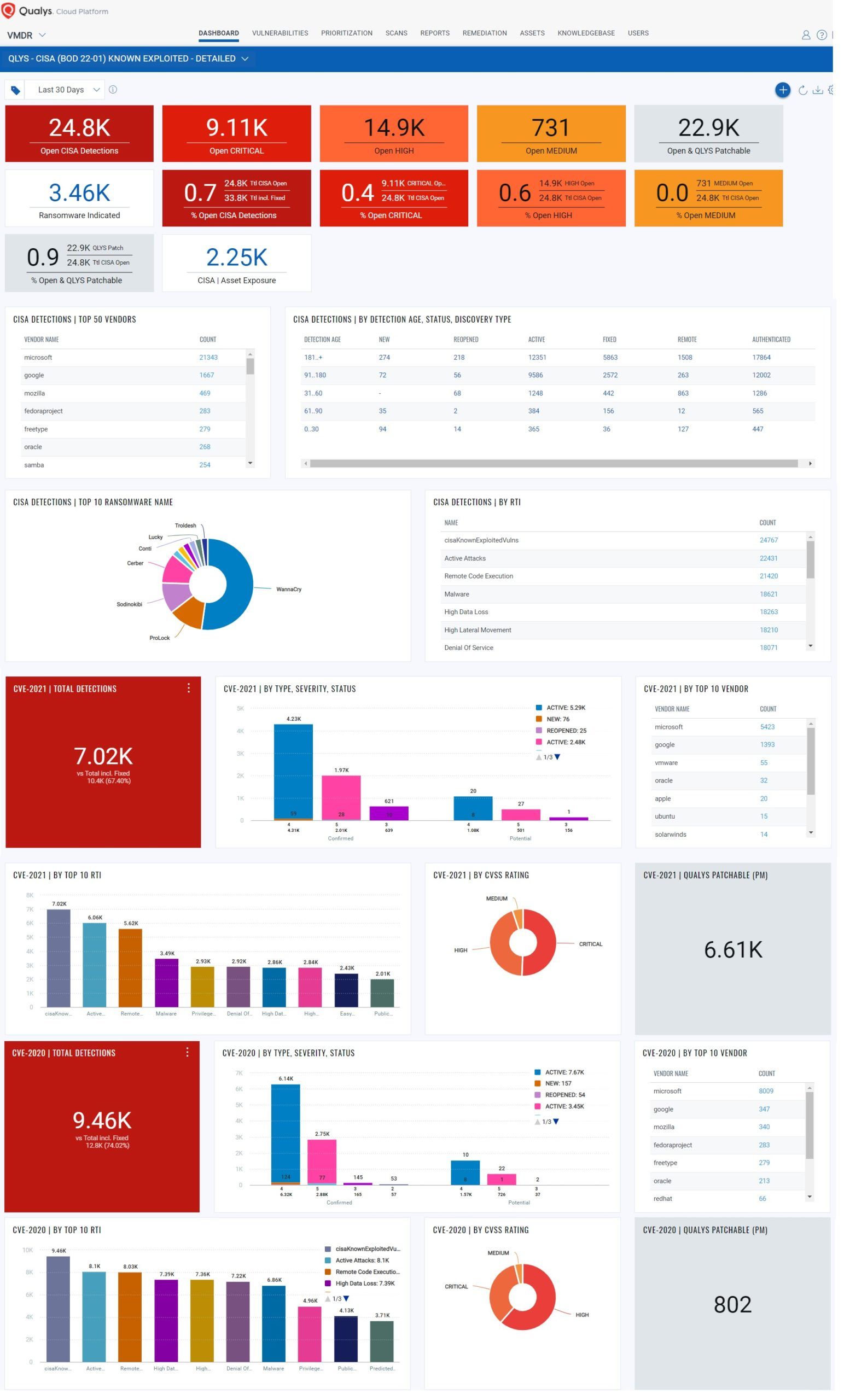
With Qualys Unified Dashboard, you can track your exposure to CISA Known Exploited Vulnerabilities and track your status and overall management in real-time. With dashboard widgets, you can keep track of the status of vulnerabilities in your environment using the “CISA 2010-21| KNOWN EXPLOITED VULNERABILITIES” Dashboard.
Detailed Operational Dashboard
Remediation
To comply with this directive, federal agencies need to remediate all vulnerabilities as per the remediation timelines suggested in CISA Catalog.
Qualys patch content covers many Microsoft, Linux, and third-party applications. However, some of the vulnerabilities introduced by CISA are not currently supported out-of-the-box by Qualys. To remediate those vulnerabilities, Qualys provides the ability to deploy custom patches. The flexibility to customize patch deployment allows customers to patch all the remaining CVEs in their list.
Customers can copy the following query into the Patch Management app to help customers comply with the directive’s aggressive remediation timelines set by CISA. Running this query for specific CVEs will find required patches and allow quick and efficient deployment of those missing patches to all assets directly from within Qualys Cloud Platform.
cve:[`CVE-2010-5326`,`CVE-2012-0158`,`CVE-2012-0391`,`CVE-2012-3152`,`CVE-2013-3900`,`CVE-2013-3906`,`CVE-2014-1761`,`CVE-2014-1776`,`CVE-2014-1812`,`CVE-2015-1635`,`CVE-2015-1641`,`CVE-2015-4852`,`CVE-2016-0167`,`CVE-2016-0185`,`CVE-2016-3088`,`CVE-2016-3235`,`CVE-2016-3643`,`CVE-2016-3976`,`CVE-2016-7255`,`CVE-2016-9563`,`CVE-2017-0143`,`CVE-2017-0144`,`CVE-2017-0145`,`CVE-2017-0199`,`CVE-2017-0262`,`CVE-2017-0263`,`CVE-2017-10271`,`CVE-2017-11774`,`CVE-2017-11882`,`CVE-2017-5638`,`CVE-2017-5689`,`CVE-2017-6327`,`CVE-2017-7269`,`CVE-2017-8464`,`CVE-2017-8759`,`CVE-2017-9791`,`CVE-2017-9805`,`CVE-2017-9841`,`CVE-2018-0798`,`CVE-2018-0802`,`CVE-2018-1000861`,`CVE-2018-11776`,`CVE-2018-15961`,`CVE-2018-15982`,`CVE-2018-2380`,`CVE-2018-4878`,`CVE-2018-4939`,`CVE-2018-6789`,`CVE-2018-7600`,`CVE-2018-8174`,`CVE-2018-8453`,`CVE-2018-8653`,`CVE-2019-0193`,`CVE-2019-0211`,`CVE-2019-0541`,`CVE-2019-0604`,`CVE-2019-0708`,`CVE-2019-0752`,`CVE-2019-0797`,`CVE-2019-0803`,`CVE-2019-0808`,`CVE-2019-0859`,`CVE-2019-0863`,`CVE-2019-10149`,`CVE-2019-10758`,`CVE-2019-11510`,`CVE-2019-11539`,`CVE-2019-1214`,`CVE-2019-1215`,`CVE-2019-1367`,`CVE-2019-1429`,`CVE-2019-1458`,`CVE-2019-16759`,`CVE-2019-17026`,`CVE-2019-17558`,`CVE-2019-18187`,`CVE-2019-18988`,`CVE-2019-2725`,`CVE-2019-8394`,`CVE-2019-9978`,`CVE-2020-0601`,`CVE-2020-0646`,`CVE-2020-0674`,`CVE-2020-0683`,`CVE-2020-0688`,`CVE-2020-0787`,`CVE-2020-0796`,`CVE-2020-0878`,`CVE-2020-0938`,`CVE-2020-0968`,`CVE-2020-0986`,`CVE-2020-10148`,`CVE-2020-10189`,`CVE-2020-1020`,`CVE-2020-1040`,`CVE-2020-1054`,`CVE-2020-1147`,`CVE-2020-11738`,`CVE-2020-11978`,`CVE-2020-1350`,`CVE-2020-13671`,`CVE-2020-1380`,`CVE-2020-13927`,`CVE-2020-1464`,`CVE-2020-1472`,`CVE-2020-14750`,`CVE-2020-14871`,`CVE-2020-14882`,`CVE-2020-14883`,`CVE-2020-15505`,`CVE-2020-15999`,`CVE-2020-16009`,`CVE-2020-16010`,`CVE-2020-16013`,`CVE-2020-16017`,`CVE-2020-17087`,`CVE-2020-17144`,`CVE-2020-17496`,`CVE-2020-17530`,`CVE-2020-24557`,`CVE-2020-25213`,`CVE-2020-2555`,`CVE-2020-6207`,`CVE-2020-6287`,`CVE-2020-6418`,`CVE-2020-6572`,`CVE-2020-6819`,`CVE-2020-6820`,`CVE-2020-8243`,`CVE-2020-8260`,`CVE-2020-8467`,`CVE-2020-8468`,`CVE-2020-8599`,`CVE-2021-1647`,`CVE-2021-1675`,`CVE-2021-1732`,`CVE-2021-21017`,`CVE-2021-21148`,`CVE-2021-21166`,`CVE-2021-21193`,`CVE-2021-21206`,`CVE-2021-21220`,`CVE-2021-21224`,`CVE-2021-22204`,`CVE-2021-22893`,`CVE-2021-22894`,`CVE-2021-22899`,`CVE-2021-22900`,`CVE-2021-26411`,`CVE-2021-26855`,`CVE-2021-26857`,`CVE-2021-26858`,`CVE-2021-27059`,`CVE-2021-27065`,`CVE-2021-27085`,`CVE-2021-28310`,`CVE-2021-28550`,`CVE-2021-30116`,`CVE-2021-30551`,`CVE-2021-30554`,`CVE-2021-30563`,`CVE-2021-30632`,`CVE-2021-30633`,`CVE-2021-31199`,`CVE-2021-31201`,`CVE-2021-31207`,`CVE-2021-31955`,`CVE-2021-31956`,`CVE-2021-31979`,`CVE-2021-33739`,`CVE-2021-33742`,`CVE-2021-33766`,`CVE-2021-33771`,`CVE-2021-34448`,`CVE-2021-34473`,`CVE-2021-34523`,`CVE-2021-34527`,`CVE-2021-35211`,`CVE-2021-35247`,`CVE-2021-36741`,`CVE-2021-36742`,`CVE-2021-36934`,`CVE-2021-36942`,`CVE-2021-36948`,`CVE-2021-36955`,`CVE-2021-37415`,`CVE-2021-37973`,`CVE-2021-37975`,`CVE-2021-37976`,`CVE-2021-38000`,`CVE-2021-38003`,`CVE-2021-38645`,`CVE-2021-38647`,`CVE-2021-38648`,`CVE-2021-38649`,`CVE-2021-40438`,`CVE-2021-40444`,`CVE-2021-40449`,`CVE-2021-40539`,`CVE-2021-4102`,`CVE-2021-41773`,`CVE-2021-42013`,`CVE-2021-42292`,`CVE-2021-42321`,`CVE-2021-43890`,`CVE-2021-44077`,`CVE-2021-44228`,`CVE-2021-44515`,`CVE-2022-0609`,`CVE-2022-21882`,`CVE-2022-24086`,`CVE-2010-1871`,`CVE-2017-12149`,`CVE-2019-13272` ]
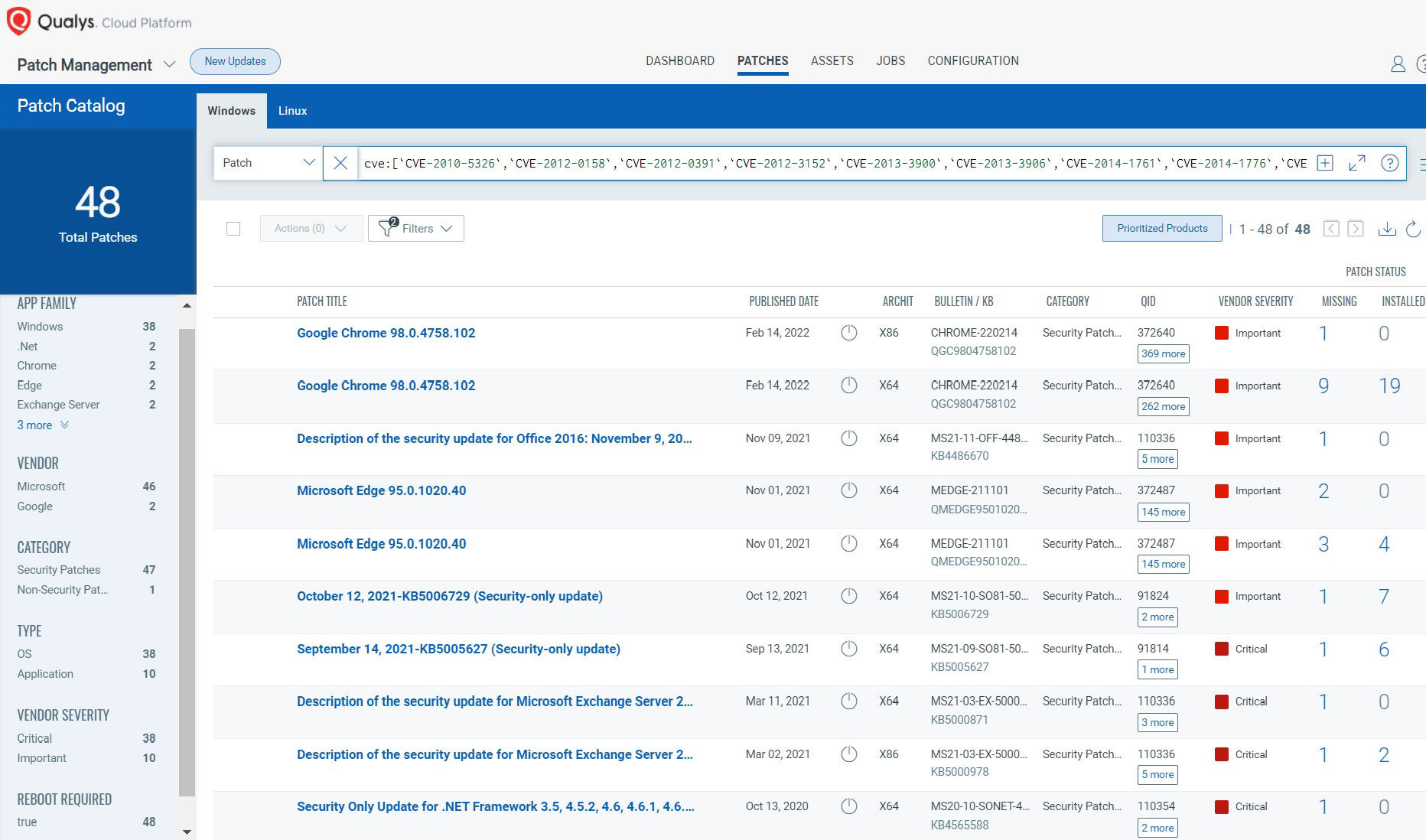
Vulnerabilities can be validated through VMDR and a Patch Job can be configured for vulnerable assets.
Federal Enterprises and Agencies Can Act Now
For federal agencies and enterprises, it’s a race against time to remediate these vulnerabilities across their respective environments and achieve compliance with this binding directive. Qualys solutions can help your organization to achieve compliance with this binding directive. Qualys Cloud Platform is FedRAMP authorized, with 107 FedRAMP authorizations to our credit.
Here are a few steps Federal entities can take immediately:
- Run vulnerability assessments against all of your assets by leveraging our various sensors such as Qualys agent, scanners, and more
- Prioritize remediation by due dates
- Identify all vulnerable assets automatically mapped into the threat feed
- Use Qualys Patch Management to apply patches and other configuration changes
- Track remediation progress through our Unified Dashboards
Summary
Understanding just which vulnerabilities exist in your environment is a critical but small part of threat mitigation. Qualys VMDR helps customers discover their exposure, assess threats, assign risk, and remediate threats – all in a single unified solution. Qualys customers rely on the accuracy of Qualys’ threat intelligence to protect their digital environments and stay current with patch guidance. Using Qualys VMDR can help any size organization efficiently respond to CISA Binding Operational Directive 22-01.
Getting Started
Learn how Qualys VMDR provides actionable vulnerability guidance and automates remediation in one solution. Ready to get started? Sign up for a 30-day, no-cost VMDR trial.
I find it odd that another SKU is needed to easily track CISA vulns. This should be something that is relatively easy to do without the need for VMDR – but it appears that it is not.