Enhanced Native DNS based Scanning with Qualys VMDR

Network based scanning of modern infrastructure is getting very complex, especially when the assets are behind CDNs, load balancers, firewalls, and more recently, ephemeral assets that spin up/down as required. This blog describes recent enhancements to Qualys Cloud Platform that allow native scanning of assets based on DNS to accurately assess vulnerabilities on those systems.
Scanning assets based on DNS hostname has been a key capability of the Qualys Cloud Platform for many years. In recent years we have seen a significant uptick in assets hosted behind CDN networks, load balancers, and firewalls which pose a unique set of challenges when performing network-based scans against them.
In our recent release (QWEB 10.17.0.0), Qualys VMDR introduced new capabilities that will allow customers to scan these types of assets, especially those behind CDNs, and accurately report vulnerabilities against them. CDNs, and accurately report vulnerabilities against them.
A Content Delivery Network (CDN) is a group of distributed servers able to provide high availability and performance by geographically distributing services based on the location of website visitors or app users. Due to globalization, almost every organization is adopting CDNs. CDNs are typically used to deliver static content such as images, style sheets, documents, client-side scripts, and HTML pages. The significant advantages of using a CDN are lower latency and faster content delivery to users, regardless of their geographical location relative to the data center where the website or application is hosted. CDNs also help reduce the load on a web application because the application does not have to service requests for content hosted on the CDN.
Limitations of DNS Scanning in Modern Infrastructure
Modern IT infrastructure is getting more complex over time. It now includes CDNs, load balancers, firewalls, and ephemeral assets that only live for a short period of time. Scanning them for vulnerabilities has become a challenge. Often during a single scan, multiple DNS hostnames could resolve to the same IP. This is especially true when the assets are behind a CDN network. This poses a unique challenge for scanning tools that are dependent on IP addresses to uniquely identify an asset within a scan. Previously, if multiple DNS hostnames were resolved to the same IP, Qualys VMDR would consider them duplicates and then discard the results for these assets.
For example, here’s the old method:
- User launched a scan on three separate targets by DNS name: site1.test.com, site2.test.com, and site3.test.com.
- Qualys VMDR would scan site1.test.com first.
- All three DNS names were resolved to the same IP address (10.10.10.1).
- Qualys Cloud Platform would retain results for site1.test.com, and discard results for site2.test.com, and site3.test.com as they were considered duplicates.
Enhanced Native DNS Based Scanning with Qualys VMDR
To address these DNS-based scanning challenges, Qualys is introducing enhanced Native DNS-based Scanning in Qualys VMDR. With the recent release (QWEB 10.17.0.0), customers can launch scans on multiple targets by DNS name and receive individual scan results for each target – even if they resolve to the same IP address.
For example, here’s the new method:
- User launches a scan on three separate targets by DNS name: site1.test.com, site2.test.com, and site3.test.com.
- All three DNS names resolve to the same IP address (10.10.10.1).
- Now, if you launch a scan on all three sites, VMDR will launch the scan on all three targets separately, and you will get different scan results for all three targets.
- It will also save separate asset records for the different scan targets. The asset records will have the same IP address but different DNS names.
- Only the appropriate asset record is updated with the new scan results when a new scan is launched by DNS name.
These Native DNS based Scanning enhancements are now available to all Qualys VMDR customers. If you are not yet a customer, we invite you to Learn more about VMDR and sign up for your own trial.
How to Setup Native DNS based Scanning
Here’s how you set up enhanced Native DNS based Scanning in Qualys VMDR.
- Enable Native DNS scanning from the Scan tab > Setup menu.
- If you scan DNS, then the scan will be done based on DNS.
- DNS will be resolved to its IP address, and the resolved IP will be DNS tracked irrespective of the earlier tracking defined.
- For example: If the resolved IP was configured as IP tracked, the resolved IP will be DNS tracked after the DNS-based scanning.
- For DNS-based Scanning, Scanner Appliance of version v12.9 is required.
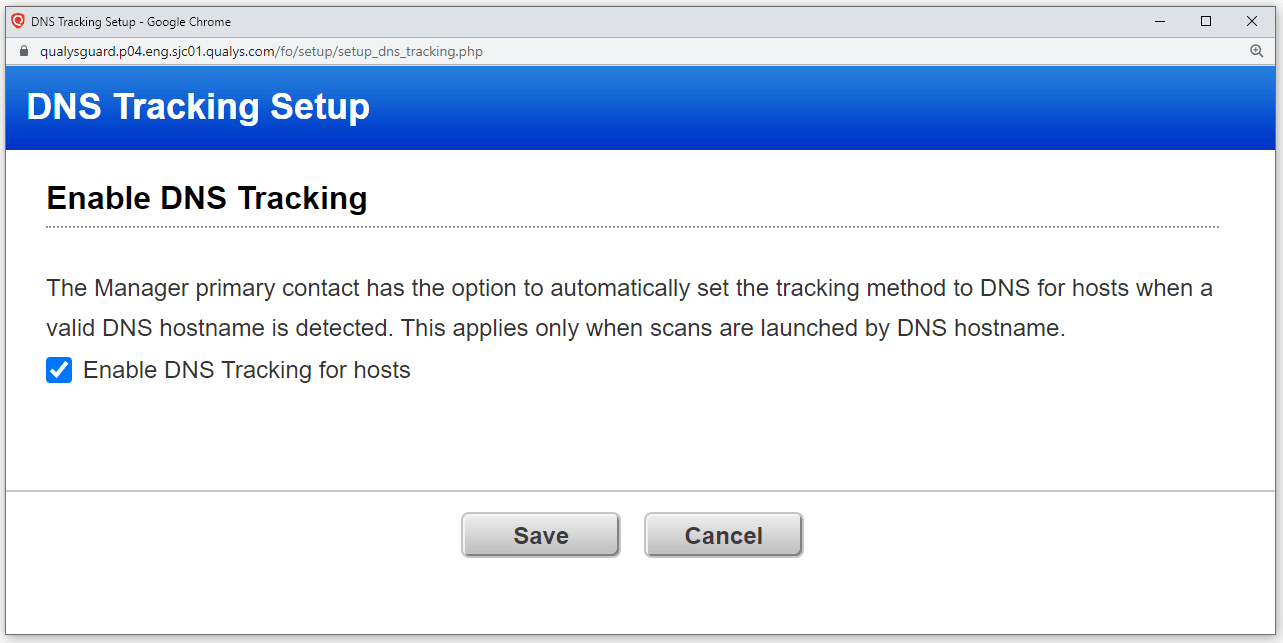
You can also automatically track all hosts by DNS where a valid DNS hostname is detected through the additional configuration done on the backend.
Frequently Asked Questions (FAQ)
What is the timeline for this functionality to be available?
This functionality is released in QWEB 10.17.0.0. There is a dependency on Scanner Appliance version v12.9.
Do I need to reach out to my Technical Account Manager to enable this feature?
No, you can enable it through the Scan tab > Setup tab. If you cannot see the “DNS Tracking” tab in the Setup tab, reach out to your Technical Account Manager.
What impact does this have on Agentless Tracking?
None. There is no impact on the Agentless Tracking feature.
I am not able to confirm that hosts are getting tracked by DNS. What should I do?
Please ensure that you have configured the “Enable DNS Tracking for hosts” checkbox in the Scan tab > Setup tab. All hosts should have a valid HDS hostname.
How do I scan DNS targets that are behind a Load Balancer?
Launch the scan on the IP address instead of the DNS name for targets behind a load balancer. Ensure that you have authentication records for those IPs in your account to get proper scan results. Authentication is always used for compliance scans and is used for vulnerability scans when authentication is enabled in your option profile.
What will happen if a domain resolves to multiple IPs is scanned by FQDN and enabled DNS tracking?
VMDR will launch the scan on the targeted domain, and you will get one scan result for the targeted domain.