Meet FedRAMP Compliance with Qualys Cloud Platform
Table of Contents
- What is FedRAMP?
- How Qualys Can Help Meet FedRAMP Compliance
- NIST 800-53 Family: Configuration ManagementID: CM-8 Information System Component Inventory
- NIST 800-53 Family: Risk AssessmentID: RA-5 VULNERABILITY SCANNING
- NIST 800-53 Family: System and Information IntegrityID: SI-7 SYSTEM AND INFORMATION INTEGRITY
- NIST 800-53 Family: Configuration ManagementID:CM-6 CONFIGURATION SETTINGS
- NIST 800-53 Family: Policy & Procedures, Awareness & Training, Physical Access ControlControl IDs: AC1, AT-1, PE-1, PE2: Non-technical control requirements
- Summary
FedRAMP compliance is not without its challenges. Learn about some of the major security controls and how the Qualys Cloud Platform can help achieve FedRAMP authorization.
What is FedRAMP?
The Federal Risk and Authorization Management Program (FedRAMP) is a U.S. government program that promotes the adoption of secure cloud services across the Federal Government by providing a standardized approach to security and risk assessment for cloud technologies and federal agencies. FedRAMP reduces duplicative efforts to comply with multiple federal agency requirements by putting everything under a common security framework. Once FedRAMP authorizes a cloud service offering, any federal agency can then use the security package following the FedRAMP guiding principle, which says, “Do once, use many.”
FedRAMP provides four types of security baseline, defined as Low, Moderate, High, and Tailored (LI-SaaS). Each baseline refers to applicable NIST Special Publication 800-53 security controls. Similar to NIST 800-53, these controls are divided into 17 control families. Each family contains security controls related to the general security topic of that family.
FedRAMP Compliance Implementation Challenges
Three major challenges faced by any organization seeking FedRAMP authorization include:
- Setting proper system boundaries. Defining FedRAMP’s scope is most important for any organization with a cloud-based environment, which is only becoming more challenging.
- Updating asset inventory. Defining FedRAMP’s scope is further complicated unless you have completed an asset inventory. Until you know all assets across your environment, it is difficult to verify that the correct scope has been defined.
- Establishing a vulnerability management process. Vulnerability identification, assessment, and mitigation are the most important requirements in the FedRAMP authorization process. The challenge is identifying a solution that can provide the correct information as well as reporting capabilities. The latter is especially important to meet the FedRAMP RA-5 control requirement and Plan of Actions and Milestones (POA&M) monthly report.
Apart from these main challenges, there are other obstacles that an organization needs to face while pursuing FedRAMP authorization. These include:
- Implementation of multiple security solutions to meet FedRAMP’s control requirements
- Deployment of multiple security solutions adds more steps such as agent deployments, data deduplication, and more system overloads.
- Additional efforts for data collaboration & integration challenges
How Qualys Can Help Meet FedRAMP Compliance
Qualys Cloud Platform is an all-in-one solution to address all your FedRAMP compliance needs. With its comprehensive app portfolio and platform-wide capabilities, enterprises can easily speed up the journey to FedRAMP authorization and continuous compliance. Let’s examine a few major FedRAMP requirements and understand how Qualys helps you address them.
Free Trial
Get Full Access to the Qualys Cloud Platform for Free
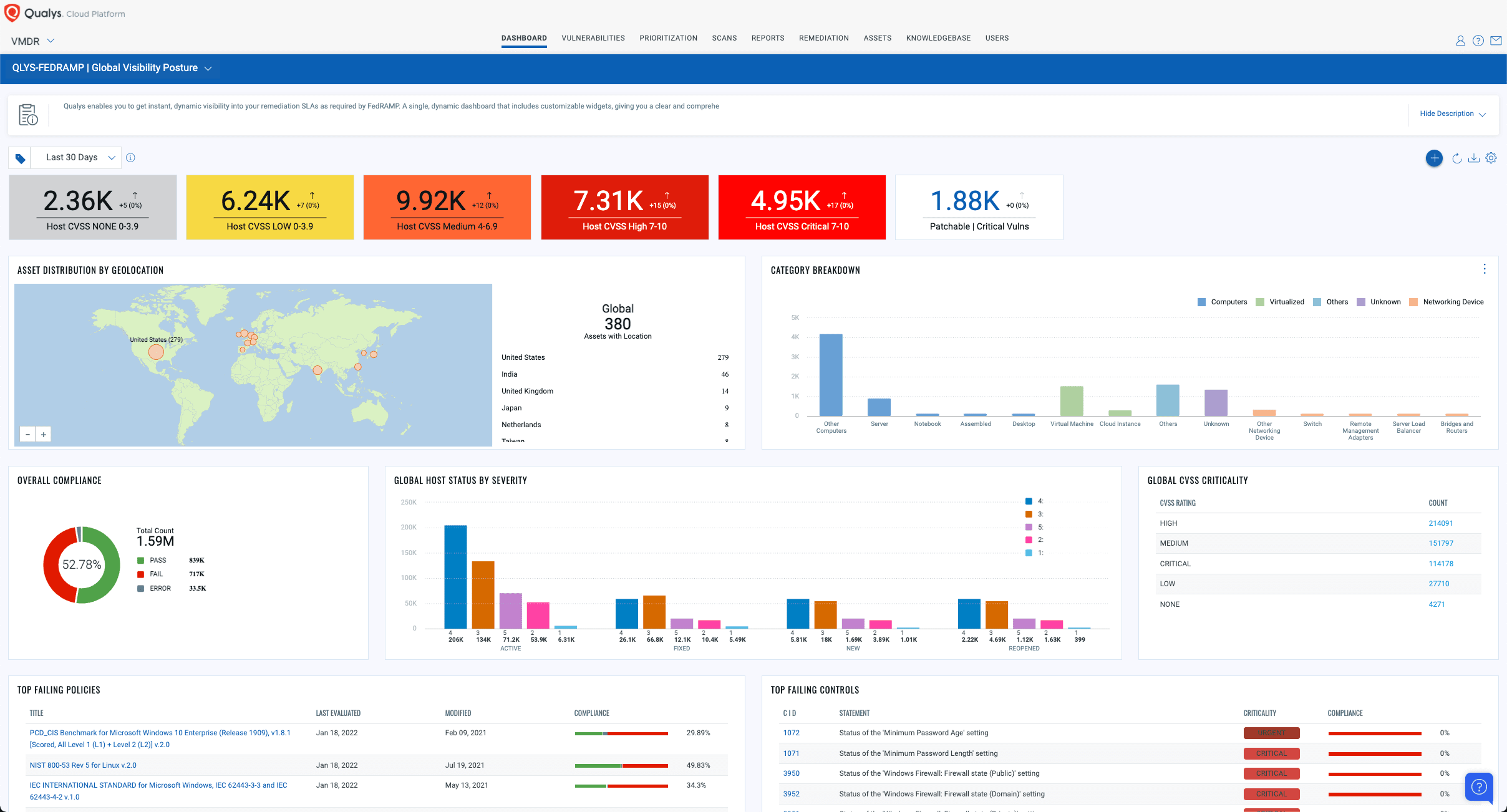
Qualys Unified Dashboard (UD): FedRAMP Compliance Dashboard
Qualys Unified Dashboard unifies compliance data from all Qualys capabilities in one place. It delivers a holistic view of your FedRAMP compliance posture. This is true single-pane-of-glass visibility across your organization. Unified Dashboard provides greater agility and insight, allowing users to visualize data from all applications together, gain a deeper understanding of your data, reach new insights, and better answer pertinent questions.
NIST 800-53 Family: Configuration Management
ID: CM-8 Information System Component Inventory
Qualys CyberSecurity Asset Management (CSAM)
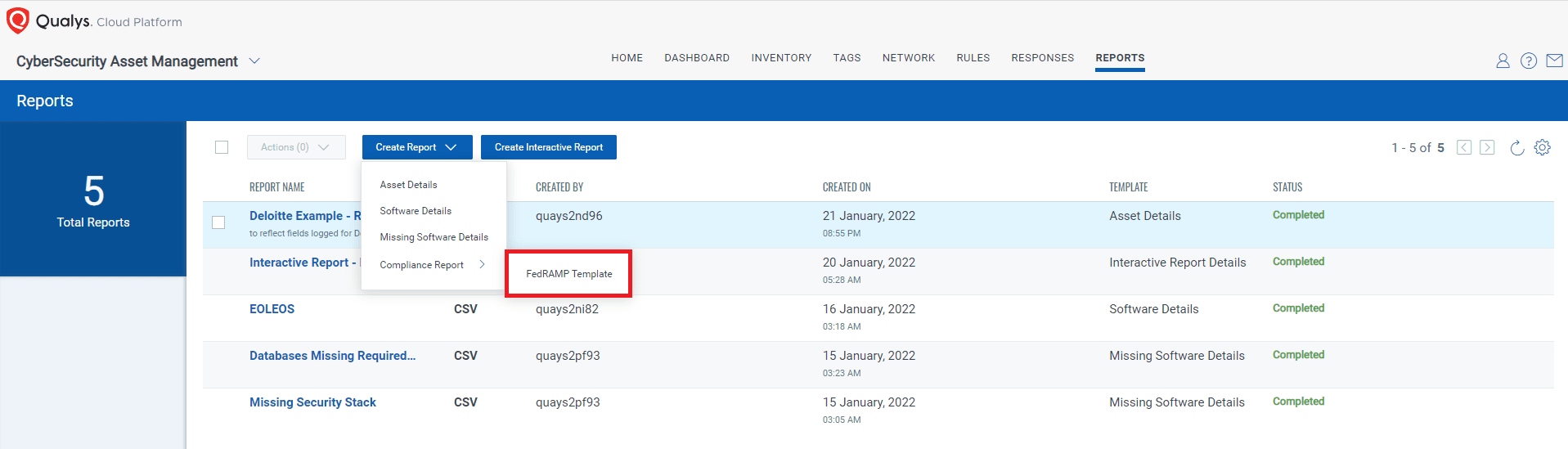
Cybersecurity teams can’t protect what they don’t see. Visibility into your up-to-date inventory is one of the most important and fundamental compliance requirements. Not just for FedRAMP, but for any regulatory requirement. Qualys Cyber Security Asset Management (CSAM) helps you meet the CM-8 requirement. With CSAM, you can continuously inventory assets, apply business criticality and risk context, detect security gaps like unauthorized or EOL software, and respond with appropriate actions to mitigate risk. Because Qualys features a unified console, all this happens all in one place, thus reducing your organization’s ‘threat debt’.
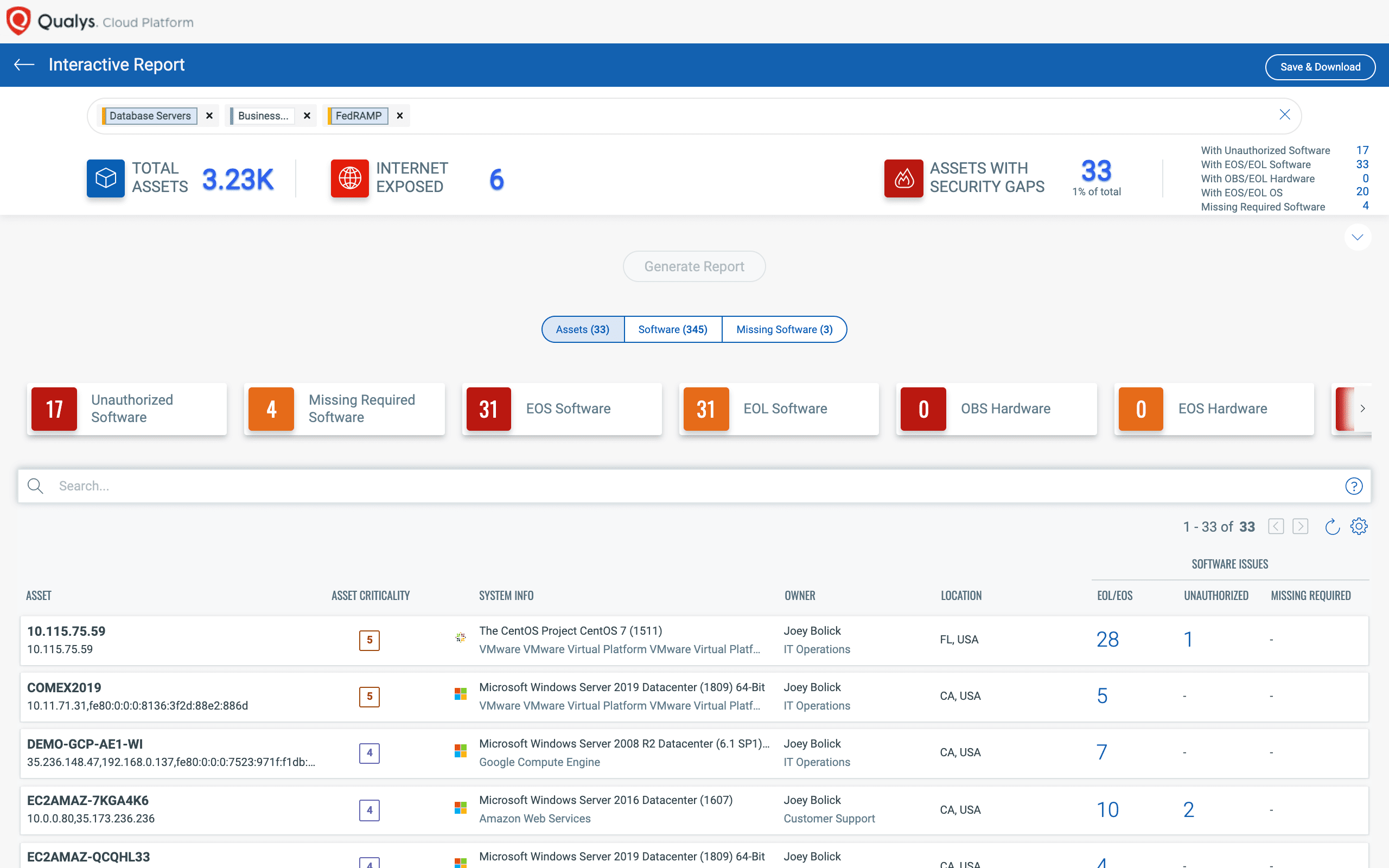
Qualys CSAM offers an out-of-the-box FedRAMP inventory report that helps you generate an Asset Inventory Report aligned with FedRAMP requirements.
NIST 800-53 Family: Risk Assessment
ID: RA-5 VULNERABILITY SCANNING
Qualys Vulnerability Management Detection and Response (VMDR)
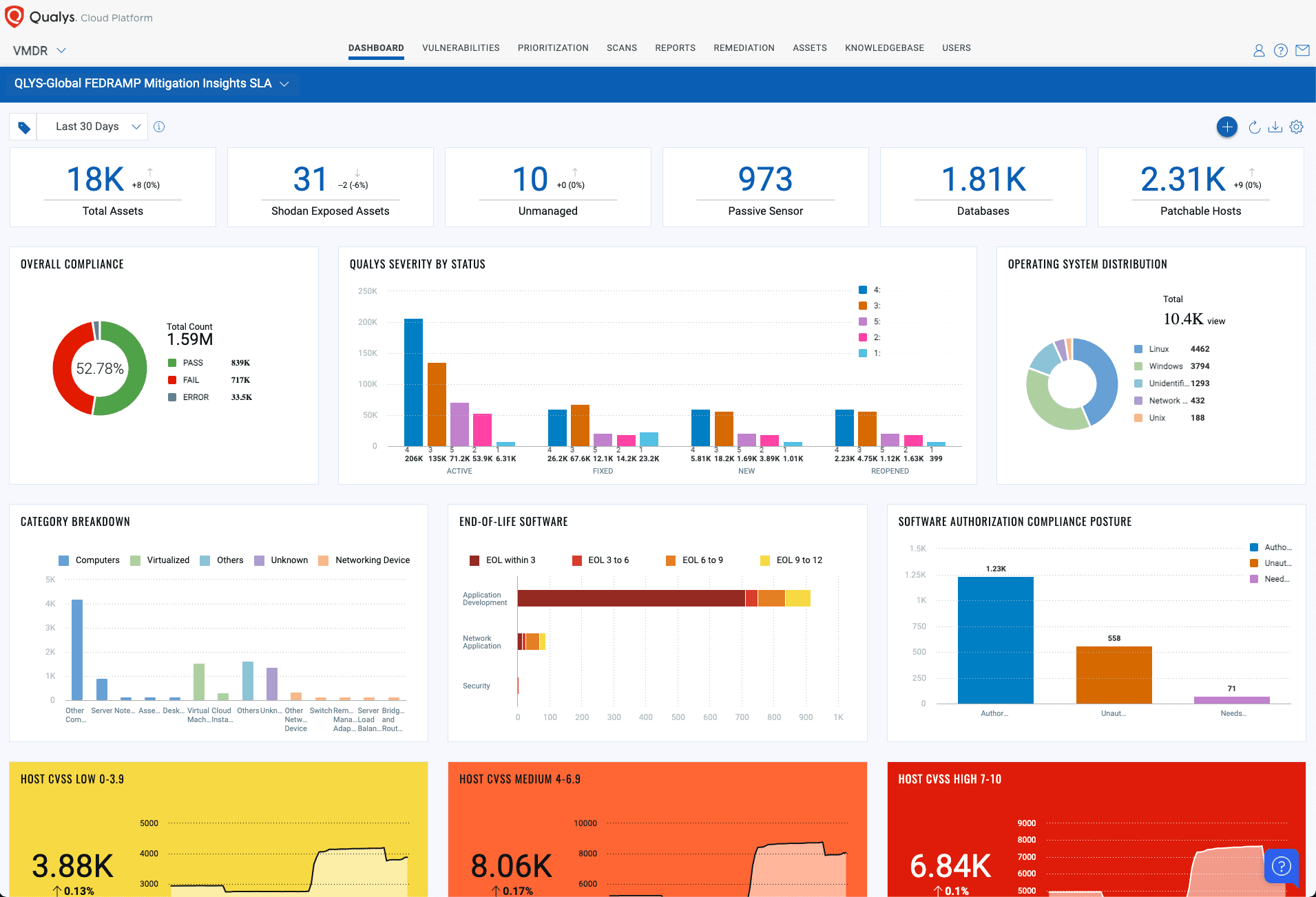
FedRAMP’s RA-5 requirement addresses the vulnerability management process. It requires you to scan your IT environment on a regular basis to check for vulnerabilities, and then to patch them in a timely manner. Qualys VMDR is the solution best suited to meet the RA-5 control requirement to submit a monthly POA&M report. It discovers, assesses, prioritizes, and patches critical vulnerabilities in real-time, across your global hybrid-IT landscape, using a single solution.
Qualys VMDR uses real-time threat intelligence, advanced correlation, and powerful machine learning to automatically prioritize the riskiest vulnerabilities on your most critical assets. Prioritization by criticality reduces potentially thousands of discovered vulnerabilities to only the few hundred that matter. Qualys VMDR further prioritizes remediation by assigning a business impact to each asset, such as devices that contain sensitive data, mission-critical applications, public-facing assets accessible over the Internet, and more.
NIST 800-53 Family: System and Information Integrity
ID: SI-7 SYSTEM AND INFORMATION INTEGRITY
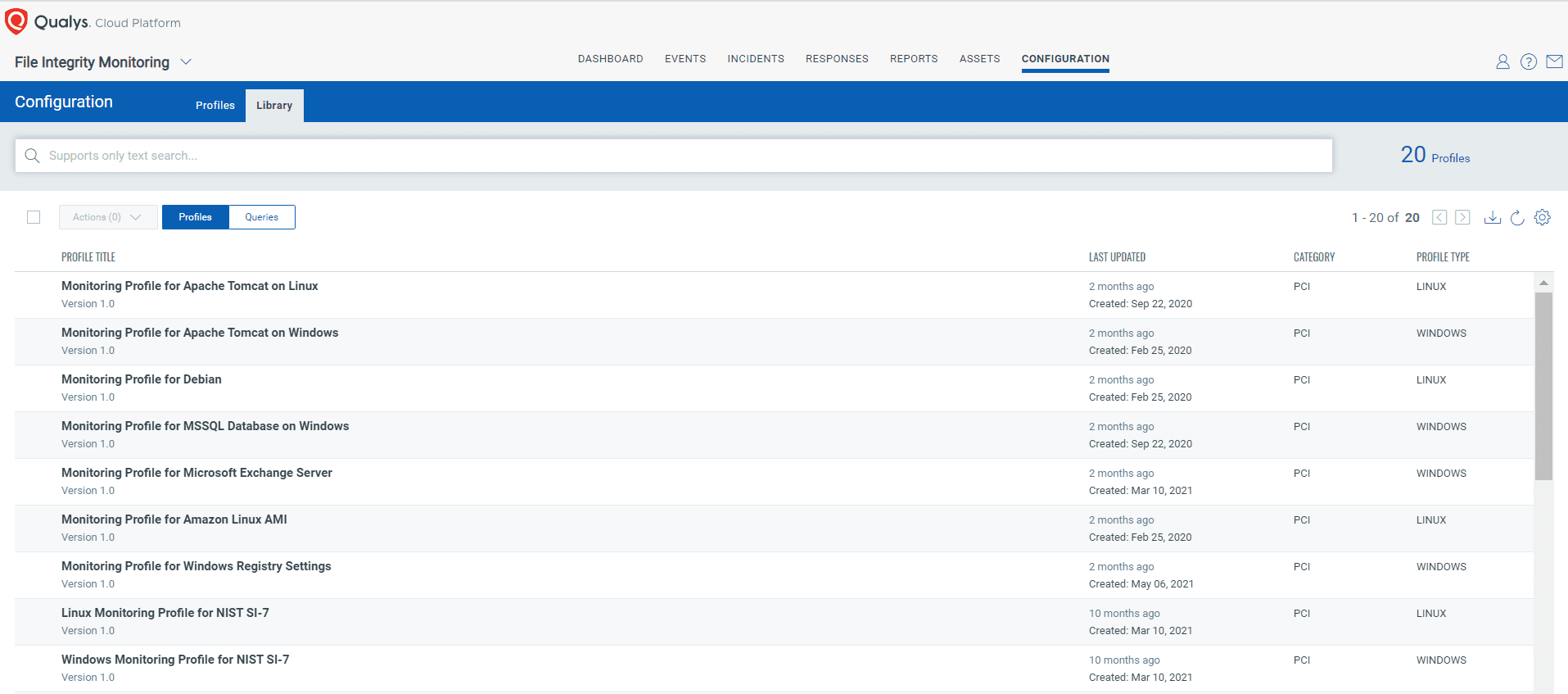
Qualys File Integrity Monitoring (FIM)
FedRAMP’s SI-7 requirement states that, “The information system must employ cryptographic mechanisms to detect unauthorized changes to software, firmware, and information.” Qualys File Integrity Monitoring provides out-of-the-box profiles to monitor highly critical files, registry objects, and actions in support of SI-7. This helps you to kick-start your monitoring efforts and also to comply with various compliance standards in addition to FedRAMP.
NIST 800-53 Family: Configuration Management
ID:CM-6 CONFIGURATION SETTINGS
Qualys Policy Compliance (PC) | Qualys Cloud Security Assessment (CSA) | Qualys Container Security (CS)
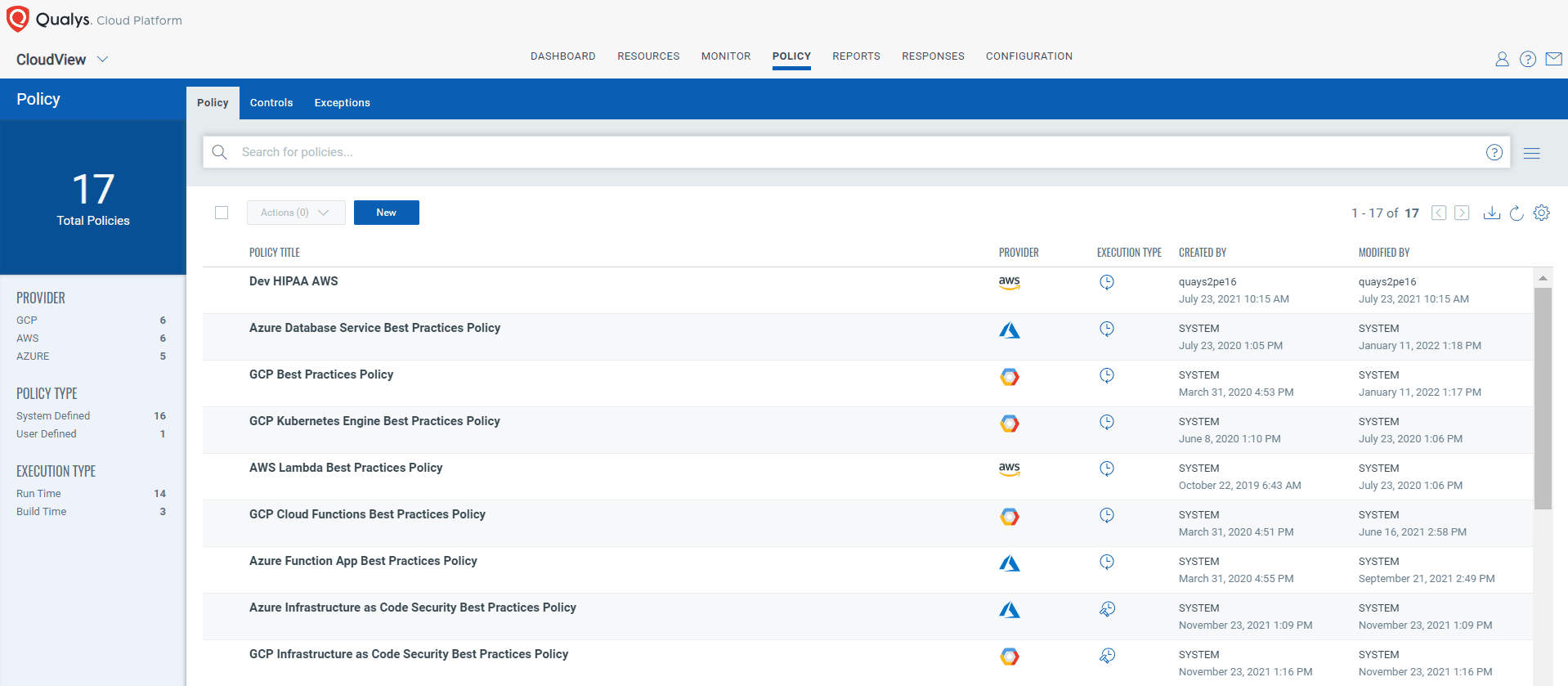
FedRAMP requires that you define stringent baseline policies for your IT environment that include your critical server, hardware, and software. However, just defining a baseline is not sufficient. You need to ensure that policies are properly implemented across your IT environment. Qualys Policy Compliance (PC) and Qualys Cloud Security Assessment (CSA) apps help you fulfill this important FedRAMP mandate. With Qualys PC/CSA you can create your own policies with configuration control settings then assess your environment against them, identify misconfigurations, and fix them before attackers can exploit them.

While Qualys Policy Compliance (PC) helps you with your physical assets, Qualys Security Cloud Assessment (aka CloudView) can check the control compliance of your cloud-based assets.
Container Security (CS): Qualys Container Security capability helps you address all FedRAMP related container requirements such as container infrastructure security, security across DevOps pipeline, image hardening, registry scanning, container-native vulnerability analysis as well as container asset management and tracking.
Read our detailed blog on Container Infrastructure and FedRAMP compliance
NIST 800-53 Family: Policy & Procedures, Awareness & Training, Physical Access Control
Control ID’s: AC1, AT-1, PE-1, PE2: Non-technical control requirements
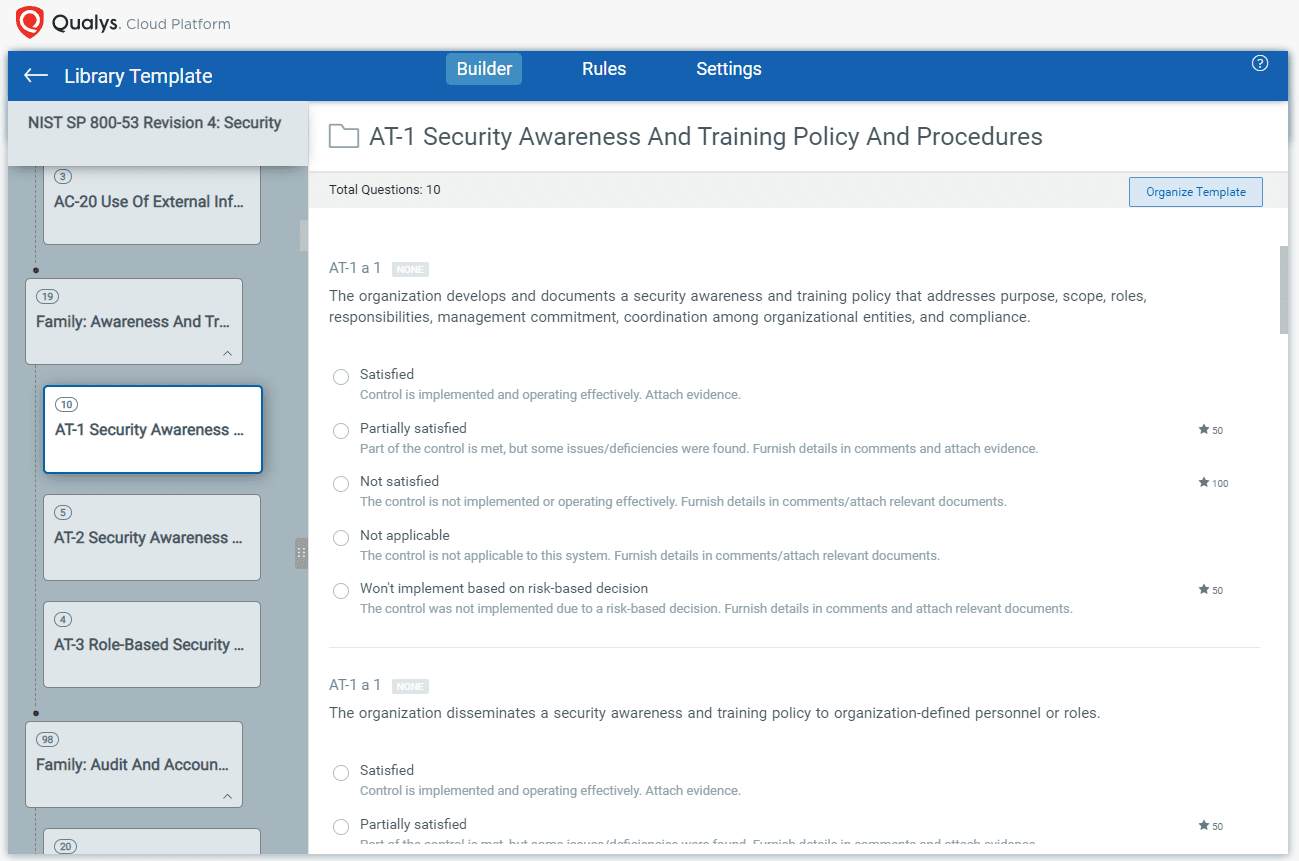
Qualys Security Assessment Questionnaire (SAQ)
Another FedRAMP requirement is to have policies and procedures in place and reviewed on a regular basis. In fact, this is highlighted in every FedRAMP family. Qualys Security Assessment Questionnaire (SAQ) can help you create a questionnaire and assign it to each respective stakeholder to confirm availability of their policies & procedures as well as compliance controls. Qualys SAQ also provides out-of-the box templates that can be used directly for these internal assessments.
Apart from the specific capabilities outlined above, Qualys offers multiple other functions to assist you in fulfilling FedRAMP requirements. The following table details how Qualys capabilities can help your organization to address all FedRAMP control families.
Qualys Capabilities as Mapped to the ‘FedRAMP High’ Control Baseline
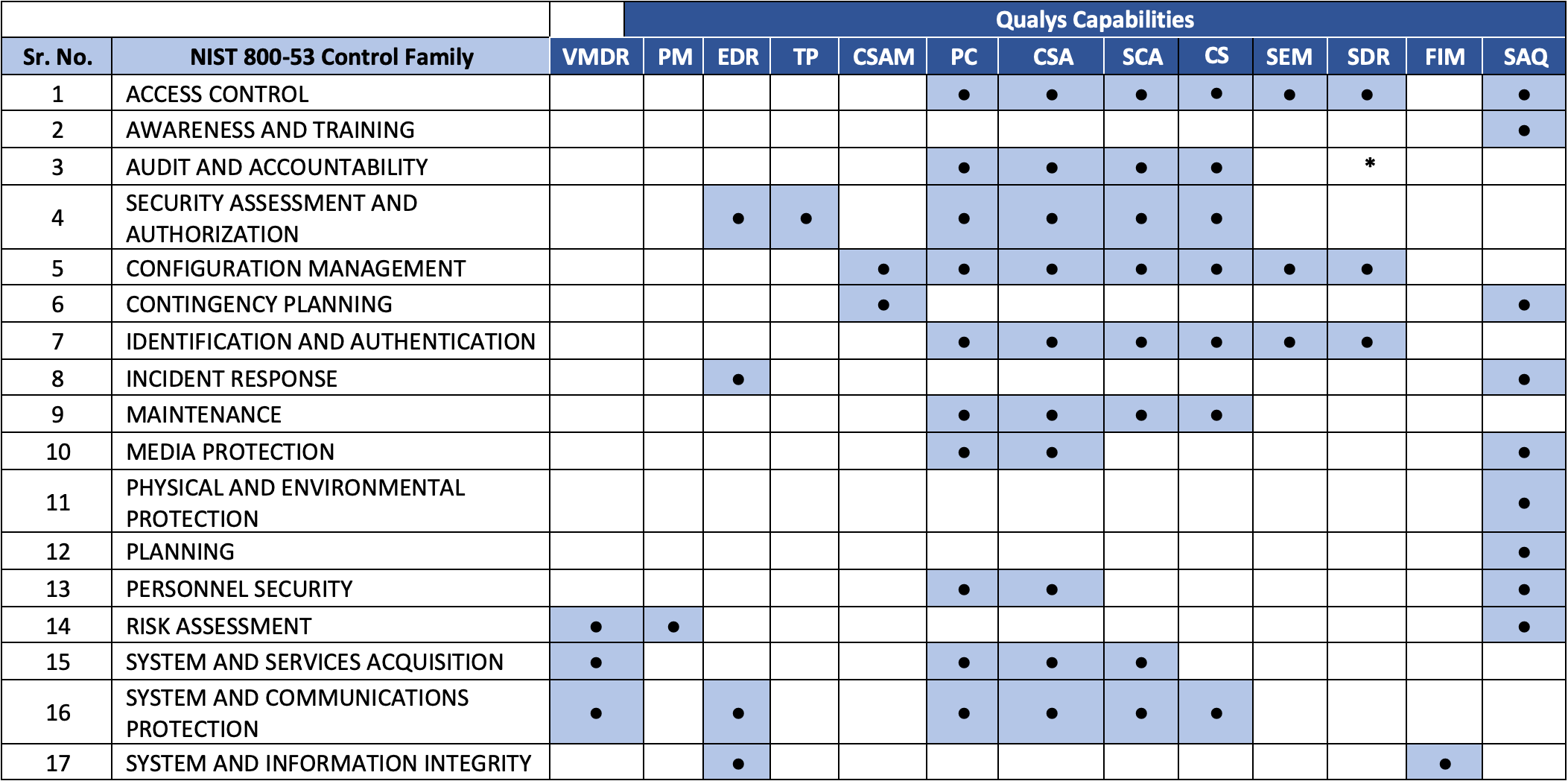
This table describes all Qualys apps and their distinct capabilities in brief. For more information, please visit https://www.qualys.com/apps/
| Qualys Capabilities | Description |
|---|---|
| Qualys CyberSecurity Asset Management (CSAM) is asset management reimagined for security teams. With Qualys CSAM, organizations can continuously inventory assets, apply business criticality and risk context, detect security gaps like unauthorized or EOL software, and respond with appropriate actions to mitigate risk, thus reducing the ‘threat debt’. | |
| Qualys Vulnerability Management, Detection and Response (VMDR) automatically discover every asset in your environment, including unmanaged assets appearing on the network, inventory all hardware and software, and classify and tag critical assets. | |
| Qualys CloudView continuously monitor and assess your cloud assets and resources for misconfigurations and non-standard deployments. Qualys CSA is a next-generation cloud app for unparalleled visibility and continuous security of public cloud infrastructure. | |
| Qualys Endpoint Detection and Response (EDR) unifies different context vectors like asset discovery, rich normalized software inventory, end-of-life visibility, vulnerabilities and exploits, misconfigurations, in-depth endpoint telemetry, and network reachability with a powerful backend to correlate it all for accurate assessment, detection and response. | |
| Qualys File Integrity Monitoring (FIM) log and track file changes across global IT systems. It helps you in detecting and identifying critical file changes, incidents, and risks resulting from malicious activity. | |
| Qualys Patch Management (PM) streamline and accelerate vulnerability remediation for all your IT assets. Qualys PM automatically correlates vulnerabilities to patch deployments so you can remediate vulnerability quickly, proactively, and consistently. | |
| Qualys Policy Compliance (PC) assess security configurations of IT systems throughout your network. Qualys PC is a next-gen solution for continuous risk reduction and compliance with internal policies and external regulations. | |
| Qualys Container Security (CS) gives you complete visibility of container hosts wherever they are in your global IT environment. With Qualys CS, security teams can enforce policies to block the use of images that have specific vulnerabilities, or that have vulnerabilities above a certain severity threshold. | |
| Qualys SaaS Detection and Response (SaaSDR) streamlines and automates the entire process of managing your SaaS apps, including global settings, user privileges, licenses, files, and their security and compliance posture. | |
| Qualys Security Assessment Questionnaire (SAQ) minimize the risk of doing business with vendors and other third parties by helping you assessing them. Qualys SAQ is a transformative solution for automating and streamlining an organization’s vendor risk management process as well as helps you in procedural control compliance check. |
Summary
FedRAMP compliance is a must for any organization that seeks to provide services to U.S. federal agencies. But getting FedRAMP authorization is no easy task unless you have the correct tools to help ease the process. Qualys Cloud Platform offers an integrated family of capabilities that make it easy for any organization to achieve FedRAMP compliance. Indeed, as Qualys Cloud Platform itself is FedRAMP compliant we can guide you best in your compliance journey!
If your organization is planning to pursue or is already pursuing FedRAMP authorization, then you can count on Qualys Cloud Platform as your on-ramp to FedRAMP.