Qualys Achieves FedRAMP® High ATO: Unlocking the Future of Trusted Cybersecurity for Government and Critical Infrastructure
Today, federal agencies and their technology partners are operating in the most scrutinized risk environment in history. The stakes are clear: a breach in high-impact systems – those holding national security, healthcare, or financial data – can result in loss of life, catastrophic economic damage, or disruption of essential services.
Against this backdrop, the federal government has doubled down on frameworks like FedRAMP, Zero Trust, and CISA Binding Operational Directives to reduce cyber risk. Further, the administration’s focus on delivering more efficient operations while addressing technical debt and tool sprawl requires agencies to take different approaches to cybersecurity and, more specifically, cyber risk management. This focus requires agencies to adopt platform-based cloud capabilities that can protect agency-wide networks while reducing the costs associated with deploying and managing multiple solutions from different vendors.
For federal agencies building or securing sensitive and highly regulated environments, meeting FedRAMP High is the highest bar for cloud security – signaling that a platform has passed rigorous, independent validation against 400+ NIST 800 – 53 High baseline controls.
Qualys Is Now FedRAMP High Authorized
The criticality of FedRAMP High authorization in 2025 stems from a confluence of accelerated federal modernization initiatives, heightened cybersecurity threats, and ambitious administration goals to rapidly deploy secure AI and cloud technologies across federal agencies.
Qualys has achieved FedRAMP High Authorization to Operate (ATO) for the Qualys Government Platform – a milestone that places the platform among a select group of solutions trusted for the nation’s most sensitive data and missions.
What does this mean in practice? It means the Qualys Government Platform has been independently validated to meet the highest level of security requirements. FedRAMP High is the most rigorous authorization level within the Federal Risk and Authorization Management Program (FedRAMP), aligning with NIST 800-53 High Impact controls. Reserved for cloud services that process the government’s most sensitive unclassified data, this level is designed to secure mission- and business-critical workloads.

With this authorization, Qualys becomes one of the few cybersecurity platforms continuously enforcing 400+ technical controls, spanning access control, audit, incident response, configuration management, and continuous monitoring. It delivers full-spectrum security – vulnerability management, compliance, EDR, asset inventory, policy enforcement, web application security, and more – at the FedRAMP High level.
Why FedRAMP High Matters Now
Cyber risk in federal and high-trust environments is not theoretical – it is measurable and compounding. Agencies struggle with asset sprawl across hybrid, multi-cloud, and on-premises systems. SaaS providers expanding into the federal market face long, complex ATO cycles that can delay revenue by 12-18 months. Critical infrastructure operators balance legacy OT systems with cloud workloads, creating blind spots in continuous monitoring.
Layered on top of this complexity are rising mandates: Zero Trust strategies, Executive Order 14028, and evolving FedRAMP and NIST frameworks. Each requires organizations to prove security maturity with data. Traditional siloed tools fail here. They generate alerts without prioritization, leaving teams with compliance reports that do little to reduce real risk exposure.
Fragmented stacks, limited capability platforms, and manual Plan of Actions and Milestones (POA&M)/patch workflows drive risk and audit fatigue. Solutions that unify discovery, assessment, prioritization, remediation and enable control inheritance at High are best positioned to efficiently reduce cyber risk across all environments.
This is where the FedRAMP High authorized Qualys Government Platform changes the game. It closes these gaps by delivering quantified, continuously validated cyber risk reduction at scale.
The Benefits of FedRAMP High Assurance
With Qualys Government Platform, agencies will experience:
- Mission‑ready cyber risk management – Qualys delivers continuous visibility across your entire risk surface (on‑premises, cloud, IoT, containers, AI) with automated discovery and continuous monitoring of vulnerabilities, misconfigurations, and threats—enriched by integrated threat intel. The result is real‑time, actionable risk insight that helps you prioritize and drive remediation, ensuring control, data integrity, and resilience in the most demanding environments.
- Proven scalability, built for resilience – Grounded in comprehensive risk insight, Qualys delivers end‑to‑end automation to prioritize, patch, and remediate not just vulnerabilities but also critical misconfigurations and compliance deviations across hybrid and multi‑cloud estates – minimizing the window of exposure and strengthening overall posture.
- Operational agility and integration – Engineered for massive scale and high performance, Qualys fits cleanly into existing IT and security workflows. Unified visibility, automated tasks, and actionable intelligence delivered directly into your processes improve efficiency and reduce complexity for centralized risk management.
Capabilities Enabled by FedRAMP High
The following solutions and capabilities are now available through the Qualys Government Platform:
- Unified Asset Inventory – Continuously discovers and classifies all assets (on-premises, cloud, containers, IoT, OT, AI workloads, web applications, APIs, and internet‑facing assets), eliminating blind spots that directly undermine CM-8 (Information System Component Inventory).
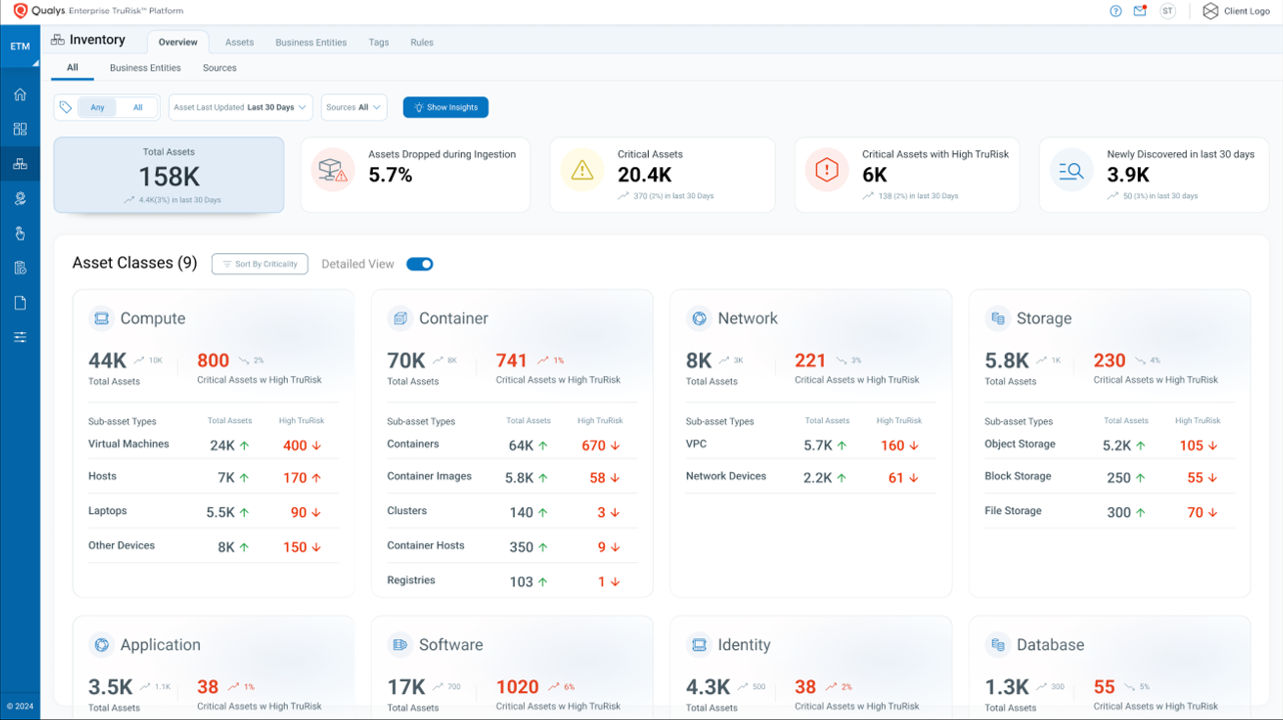

- Continuous Risk Assessment & Monitoring – Aggregates and analyzes risk factors, including vulnerabilities, misconfigurations, end‑of‑support software, and missing security controls. Enriches this telemetry with threat intelligence and asset criticality, aligning with RA-5 (Vulnerability Scanning) and CA-7 (Continuous Monitoring).


- Prioritization with TruRisk™ – Converts technical findings into business-aligned risk scores. This helps agencies comply with RA-3 (Risk Assessment) while enabling leaders to allocate resources based on quantified risk, not anecdotal severity.

- Automated Remediation Workflows – Integrates with patch management and ticketing systems to close gaps fast, supporting SI-2 (Flaw Remediation) and IR-4 (Incident Handling).
- Audit-Ready Compliance at scale – End‑to‑end coverage for vulnerabilities, configuration drift, and policy enforcement across servers, endpoints, cloud services, and containers. Automates alignment with NIST 800-53, DISA STIGs, CIS baselines, FISMA, CMMC, HIPAA, and CISA directives. Ties detection to closed‑loop remediation (patch validation and integrity monitoring) to operationalize CM‑2, CM‑6, CM‑8, and SI‑2—turning compliance into measurable risk reduction.

- Zero Trust & Critical Infrastructure Alignment – Supports CDM dashboards, CISA BODs, and Zero Trust programs by unifying internal and external attack surface visibility, risk‑based prioritization (TruRisk™), and automated enforcement. For high‑consequence environments, this translates to faster MTTR, fewer blind spots, and resilience at mission scale.

- Container Security: Continuously discovers and assesses images and containers across Kubernetes, Docker Hosts, Registries, and CI/CD Pipelines for vulnerabilities, malware, secrets, and SBOM. Prioritizes and auto-remediates real risk based on what’s running. Combines Attack Path Exposure with Business-Informed Scoring (TruRisk) to prioritize the most toxic combinations of risk.
Unlike point solutions that fragment visibility, Qualys delivers the industry’s only FedRAMP High-authorized full-spectrum security platform built for hybrid and multi-cloud environments. From public cloud workloads to on-premises data centers to remote endpoints, Qualys provides unified visibility and control across the entire attack surface.
While other FedRAMP High solutions stop at partial coverage, Qualys empowers teams to discover, assess, prioritize, remediate, monitor, and improve – without boundaries.
Who This Impacts
U.S. Federal Agencies
Agencies can’t afford “check-the-box” compliance. They need real-time visibility into vulnerabilities, misconfigurations, and exposures across hybrid environments. With FedRAMP High authorization, Qualys enables agencies to continuously monitor, prioritize with TruRisk™, and document compliance against NIST 800-53 and FISMA — reducing the burden of ongoing ATO maintenance.
SaaS Providers Expanding Federal Market Share
For SaaS companies seeking FedRAMP certification, every control inherited saves time and costs. By leveraging the Qualys FedRAMP High boundary, providers can inherit hundreds of High controls, accelerating their path to ATO while focusing on their core differentiators. SaaS providers and integrators leveraging Qualys inheritance can cut months off their certification journey, reducing both audit cost and engineering overhead by up to 40%.
Critical Infrastructure Operators
Critical infrastructure is now a national security concern. Operators in energy, transportation, healthcare, and finance face regulatory oversight that increasingly mirrors federal standards. By adopting a FedRAMP High-authorized platform, these organizations gain validated assurance of the resilience, scale, and continuous monitoring demanded in high-trust environments.
Conclusion
FedRAMP High authorization is the foundation to expand High boundary coverage across more Qualys services, ensuring customers gain even greater capabilities and assurance. Over the coming quarters, customers can expect parity with our FedRAMP Moderate offerings and targeted extensions into the Department of Defense (DoD) Cloud Computing Security Requirements Guide (SRG), supporting the nation’s most mission-critical environments. For agencies, SaaS providers, and critical infrastructure operators, the Qualys Government Platform transforms compliance from a cost center into a force multiplier for resilience and mission assurance. With Qualys now FedRAMP High Authorized, organizations inherit proven controls, gain efficiencies through a unified solution, and shift resources from paperwork to protection.
Whether you’re in the public or private sector, Qualys serves as a trusted risk operations platform that’s authorized to secure what matters most and maintain the resilience demanded by the federal mission.
Explore how Qualys can accelerate your FedRAMP journey and strengthen your security posture. Sign up for a demo today, or if you are an existing customer, reach out to your account team.
Resources:
- Qualys Government Platform listed on the FedRAMP marketplace