Don’t forget about risk remediation of your macOS assets
Employees’ love for Macs has propelled tremendous growth for Apple. According to a recent study by Parallels, 55% of businesses use Mac devices themselves or explicitly approve of their use within the company.
It is hard to believe Macs have been around for almost 4 decades. Largely introduced to the world via a Super Bowl commercial in 1984, the Mac fundamentally changed the way most people interacted with computers.
While Macs were traditionally associated with creative industries like graphic design and marketing, over time more businesses have started to adopt Apple technology. We now see them in so many industries such as Healthcare, Finance, Insurance, Manufacturing, Retail, Education and Government to name a few.
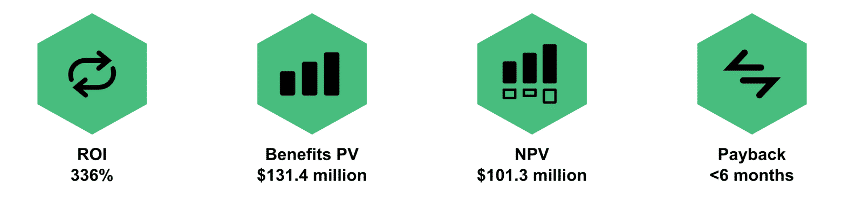
While the perception of the high cost may cause some concern from Finance and Procurement teams, Forrester published a Total Economic Impact Report that showed the average device lifecycle cost savings over a 3-year period is $843 per Mac. Additional financial benefits from the Forrester report can be found below.
While macs still make up a small percentage of end-user devices in the corporate environment, they can access most corporate resources including file sharing, cloud applications, VPN access and more. And due to these devices being connected to the corporate environment, they introduce risk and need to be secured. Necessary steps and functional areas to look to minimize these risks include:
1. Asset Management is the process of identifying, on a continuous, real-time basis, the IT assets that your organization owns, including how threat actors view your network plane (external attack surface management)
2. Vulnerability Management is the ongoing, regular process of identifying, assessing, reporting on, managing and remediating cyber vulnerabilities across endpoints, workloads, and systems.
3. Risk Prioritization is the process of analyzing identified risks and deciding the order in which their mitigation deserves your time and attention.
4. Remediation is the process of identifying and deploying software updates, or “patches,” to a variety of endpoints, including computers, mobile devices, and servers
5. Threat Detection and Response describes the ability of IT organizations to quickly and accurately identify threats to the network, applications, or other assets within the network.
To learn more about how Qualys helps manage risk effectively through asset management, risk mitigation, and threat detection and response, please visit www.qualys.com.
If you would like to start a trial of Qualys Patch Management, with unified support across Windows, Linux and macOS operating systems, please visit: https://www.qualys.com/forms/patch-management