Handling the Vulnerability Surge in the Post-Mythos Era
How to Operationalize Hyper-Prioritization and Autonomous Remediation with Qualys
Executive Summary
The Mythos era, defined by a surge of AI-driven vulnerabilities from frontier models like Anthropic’s Claude Mythos, requires security teams to fundamentally move from manual to an autonomous remediation operational model for validated vulnerabilities. To handle the unprecedented vulnerability surge, organizations must operationalize hyper-prioritization to filter out 99% of noise, automate zero-day remediation while maintaining operational resilience, and leverage AI-speed detection for high-fidelity signals. The Qualys Enterprise TruRisk Management Platform, along with Qualys VMDR and TruRisk Eliminate, provides the risk management platform needed to execute this continuous loop, shifting operations from human-speed ticketing to machine-speed risk reduction.
Over the last four years, the volume of critical vulnerabilities has surged by 650%, while the mean-time-to-exploit has collapsed to -7 days. This negative window means attackers are weaponizing flaws before patches are even released. Security teams can no longer rely on ticket-driven workflows for the riskiest vulnerabilities. To survive exploitation in this frontier AI reality, organizations need three capabilities working as a single loop:
- Hyper-prioritization to cut 99% of the noise and focus on environmental exploitability.
- Zero-day remediation that acts at machine speed without breaking operations.
- AI-speed detection to feed the loop with high-fidelity signals.
Join us on May 6 at 9 am Pacific to learn how to manage risk in the post-Mythos era.
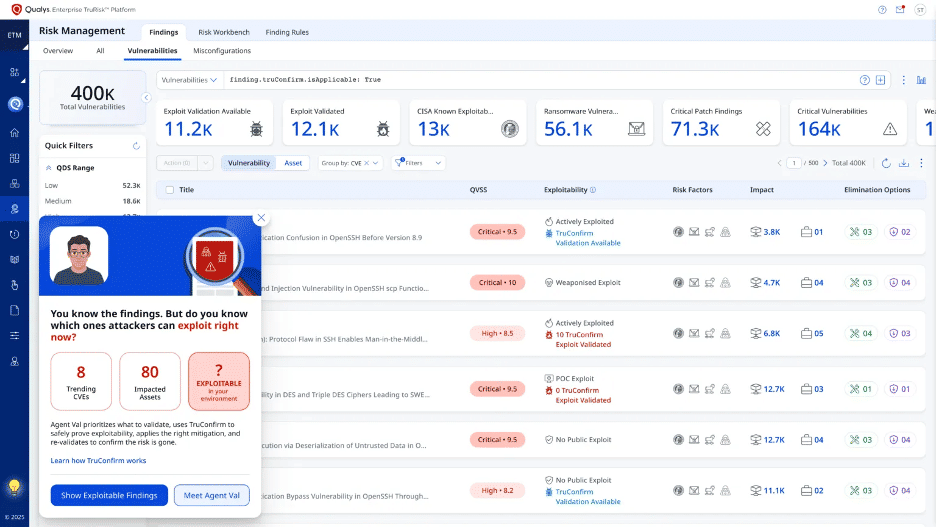
Hyper-Prioritization with Qualys ETM
Advanced AI models can now discover and help weaponize vulnerabilities far faster than organizations can manually triage them. The typical reaction to this avalanche is attempting to patch everything—a practical impossibility. In 2025 alone, 48,172 CVEs were published, yet only 0.74% were actively weaponized. Burning finite engineering cycles on theoretical risks creates a widening gap that attackers inevitably exploit.
The only scalable answer is ruthless hyper-prioritization. Historically, less than 1% of CVEs are weaponized, and many are not exploitable in specific environments due to compensating controls. Hyper-prioritization shrinks the problem set from “everything that looks scary” to “the specific exposures that can be exploited on your assets, right now.” This is where an AI-native ROC, powered by Qualys ETM, operationalizes remediation for validated vulnerabilities.
ETM aggregates findings into a unified inventory, linking technical assets to business criticality. Using TruRisk and TruLens, the platform layers three filters—threat context, business context, and environmental context to convert undifferentiated noise into ranked, business-relevant queues.
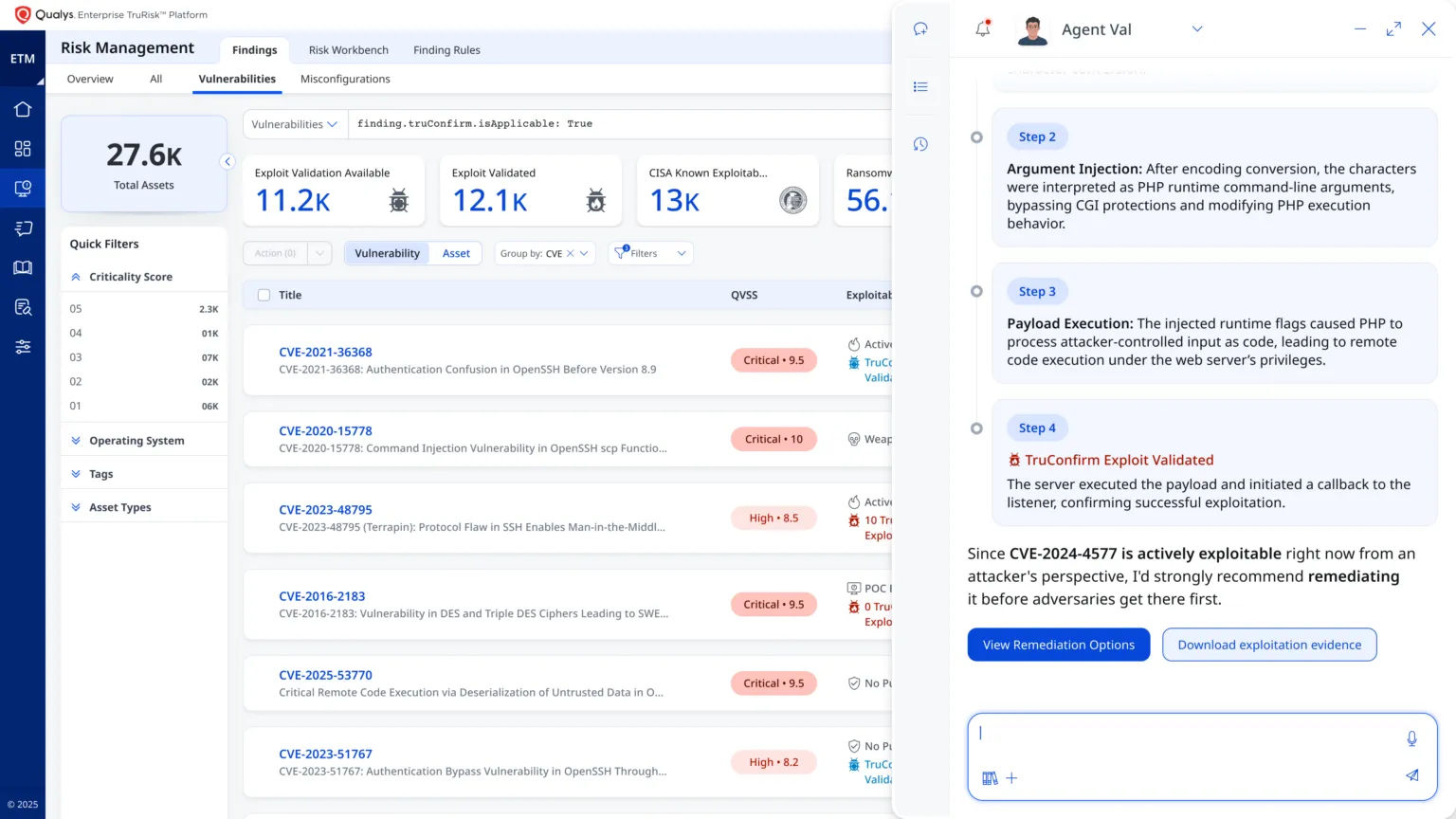
The final filter is exploitability validation via Qualys Agent Val and TruConfirm. By safely deploying modified network payloads against live production assets, these tools prove exploitability. In the last 12 months, TruConfirm has:
- Executed over 8 million production-safe validations with zero disruption.
- Achieved a 99.9% reduction in noise.
- Reduced theoretical remediation costs by order of magnitude.
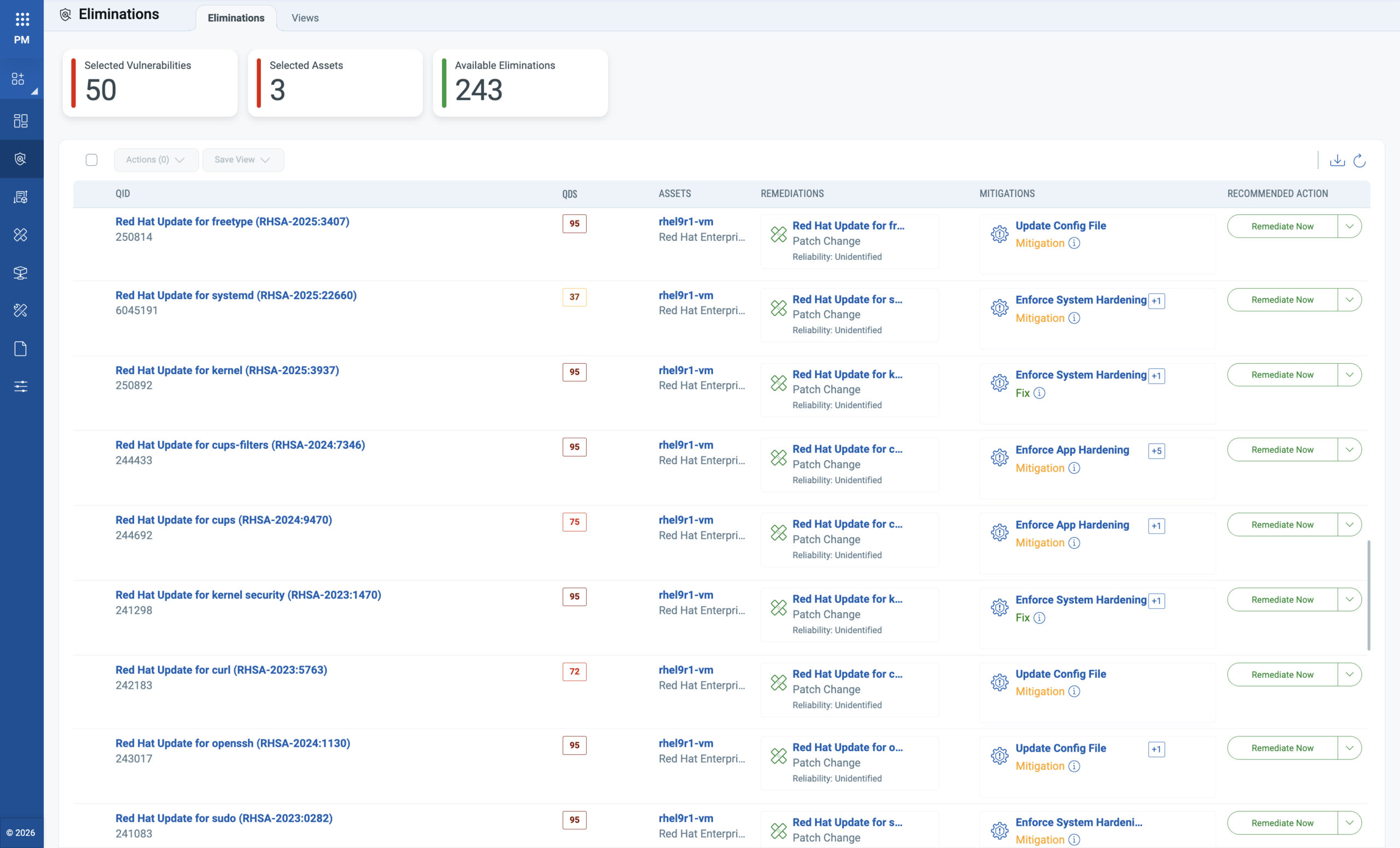
Zero-Day Remediation with TruRisk Eliminate
Once vulnerabilities are validated and prioritized, the primary challenge shifts to managing the remediation throughput. Remediation cannot remain a downstream process competing with manual patch approvals. It must transition into an automated workflow built on operational resilience.
Trust is the gating factor for automating remediation processes. TruRisk Eliminate is designed to earn that trust through four safeguards: AI-powered patch reliability scores, phased deployment waves, robust rollback, and patchless mitigation support. The platform is battle-tested, having deployed over 150 million patches in the last year, 40 million of which were applied completely autonomously with a rollback rate of less than 0.1%. When patches are unavailable, untested, or operationally risky, TruRisk Eliminate immediately pivots to patchless mitigations. At scale, this translates to massive risk reduction.
Post-remediation, Agent Val and TruConfirm continuously re-validate the environment to cryptographically prove attack paths are closed and deployed controls are working as intended. This loop shrinks the Average Window of Exposure (AWE) from 67 days to less than 18 days, thereby shifting the success metric from ticket closure to confirmed risk reduction.
Zero-day remediation is not “patch everything faster.” It is “remediate validated vulnerabilities at machine speed, to make autonomous action operationally safe.”
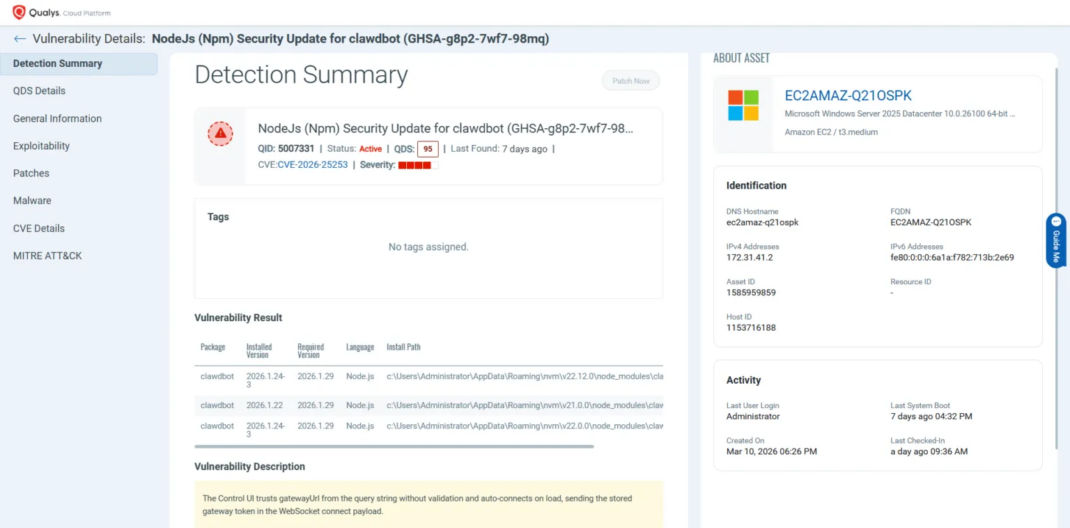
AI-Speed Detection with Qualys VMDR
Hyper-prioritization and autonomous zero-day remediation are only as effective as the detection signal feeding them. If your asset inventory is stale, your cloud workloads are invisible, or your AI-integrated services fall outside your sensor coverage, the loop breaks at the source, leaving you prioritizing and remediating against an incomplete picture of your actual exposure.
Qualys VMDR serves as the baseline engine, delivering Six Sigma–level accuracy in vulnerability detection and response. With a median response time for zero-day signatures measured in hours, VMDR ensures that when a vulnerability transitions to “actively exploited,” that state change is immediately visible.
Upcoming releases will reduce vulnerability signature generation from hours to minutes, leveraging multiple AI models with noise-filtering mechanisms to ensure that speed does not come at the cost of fidelity. TruConfirm coverage is also being expanded across cloud environments, container workloads, identity exposures, and misconfigurations, so that validated exploitability applies to every relevant asset type, not just traditional endpoints.
Conclusion
Human-speed security operations are not equipped for frontier AI-driven disclosure volumes. The window between disclosure and weaponization is now measured in hours for a growing share of high-severity vulnerabilities, and that window will continue to compress. Organizations that move to a continuous, evidence-driven, automated risk-reduction operating model now are building a structural advantage. Those that don’t accept the new reality are creating an ever-expanding gap between what attackers can exploit and what defenders can remediate.
By creating a closed operational loop — detection feeding prioritization, prioritization feeding validated exploitability, validated exploitability feeding autonomous remediation, and remediation feeding confirmed risk reduction.
That loop is what a Risk Operations Center powered by Qualys ETM delivers. VMDR for AI-speed detection. TruRisk and TruLens for context-aware prioritization. TruConfirm and Agent Val for production-safe exploit validation. TruRisk Eliminate for autonomous, operationally resilient remediation.
Read More
Ready to operationalize continuous risk reduction? Learn how Qualys can help you prepare for frontier AI-era disclosure waves.
Join us on May 6 at 9 AM Pacific to see this operating model in action.