QSC18 Virtual Edition: Global IT Asset Discovery, Inventory, and Management
 Maintaining an IT asset inventory is essential for a strong security posture, but digital transformation has further complicated this already challenging task.
Maintaining an IT asset inventory is essential for a strong security posture, but digital transformation has further complicated this already challenging task.
“The volume and variety of assets, including cloud, virtualization, mobility and IoT, is disrupting IT, and security takes center stage,” Pablo Quiroga, a Qualys Director of Product Management, said during QSC18 Virtual Edition.
Consequently, many security teams can’t definitively answer questions like: What are your IT assets? Where are they located? Who are their owners and users? How are assets related?
Having asset-inventory blind spots heightens security risks, which is why most regulations and standards highlight this practice. For instance, the Center for Internet Security’s Top 20 controls begin with inventory and control of hardware and software, because attackers constantly look to exploit vulnerable assets.
In his presentation, titled “Global IT Asset Discovery, Inventory, and Management,” Quiroga explained the importance of a complete and accurate inventory, and how Qualys can help. Read on to learn more.
Inventory challenges
Beyond digital transformation challenges, others include the growing volume and velocity of assets flowing into organizations, and the “noise” of collected asset data that’s irrelevant.
Organizations also struggle with data variations. Products get rebranded. New versions come out. Vendors are acquired. Products and vendors are listed with different names. “When an IT analyst wants to look at this data for this volume of assets, first thing they must do is clean up that data,” Quiroga said.
But doing this manually is time-consuming, and doesn’t scale. “By the time they’re done, the next round comes in. It’s never-ending work,” he said.
They must also gather relevant information beyond the basics. “You must collect other asset attributes that are external to the automated inventory,” he said. This includes lifecycle data, usage rights, ownership and cost. These data points help organizations build a full picture of each asset and make business decisions.
Asset inventory use cases
According to Quiroga, there are three key use cases for maintaining a global IT asset inventory. First, organizations must determine quickly which newly-discovered devices are not corporate-owned. “You must understand which assets you have on your inventory before determining which assets are non-corporate, and understand the difference,” he said.
Next is what he calls resource utilization, where knowing what software is installed but unused simplifies remediation. “Just remove the software,” he said. “No need to patch or manage it.”
Finally, there’s the vendor lifecycle use case: It’s crucial having clarity into end-of-life (EOL) and end-of-service (EOS) assets, which may no longer get updates and patches from manufacturers, he said.
Qualys Asset Inventory
The new Qualys Asset Inventory (AI) app, now in beta, addresses these challenges. It all starts with the scalable, self-updating and centrally-managed Qualys sensors:
- physical scanners for on-premises, legacy assets
- virtual scanners for private clouds and virtualized infrastructure
- pre-certified scanners for public cloud platforms
- a passive network sniffer
- APIs for integration with third-party tools
- lightweight, multi-platform Cloud Agents installed on assets
Specifically, the passive network sniffer, which enters beta in Q3, will help eliminate blind spots by identifying and profiling devices the moment they connect to the network. It will add details such as traffic data, while discovering systems unsuited for active probing or agents, like IoT, medical, and SCADA systems.
With this versatile set of sensors, “we’re well positioned to discover all asset types,” and collect deep, granular asset details, Quiroga said.
Normalization, classification and more
Qualys AI takes this comprehensive, multidimensional asset data, and normalizes and classifies it into meaningful, functional categories. “This gives you an out-of-the-box standard structure and taxonomy that empowers you with actionable data,” Quiroga said.
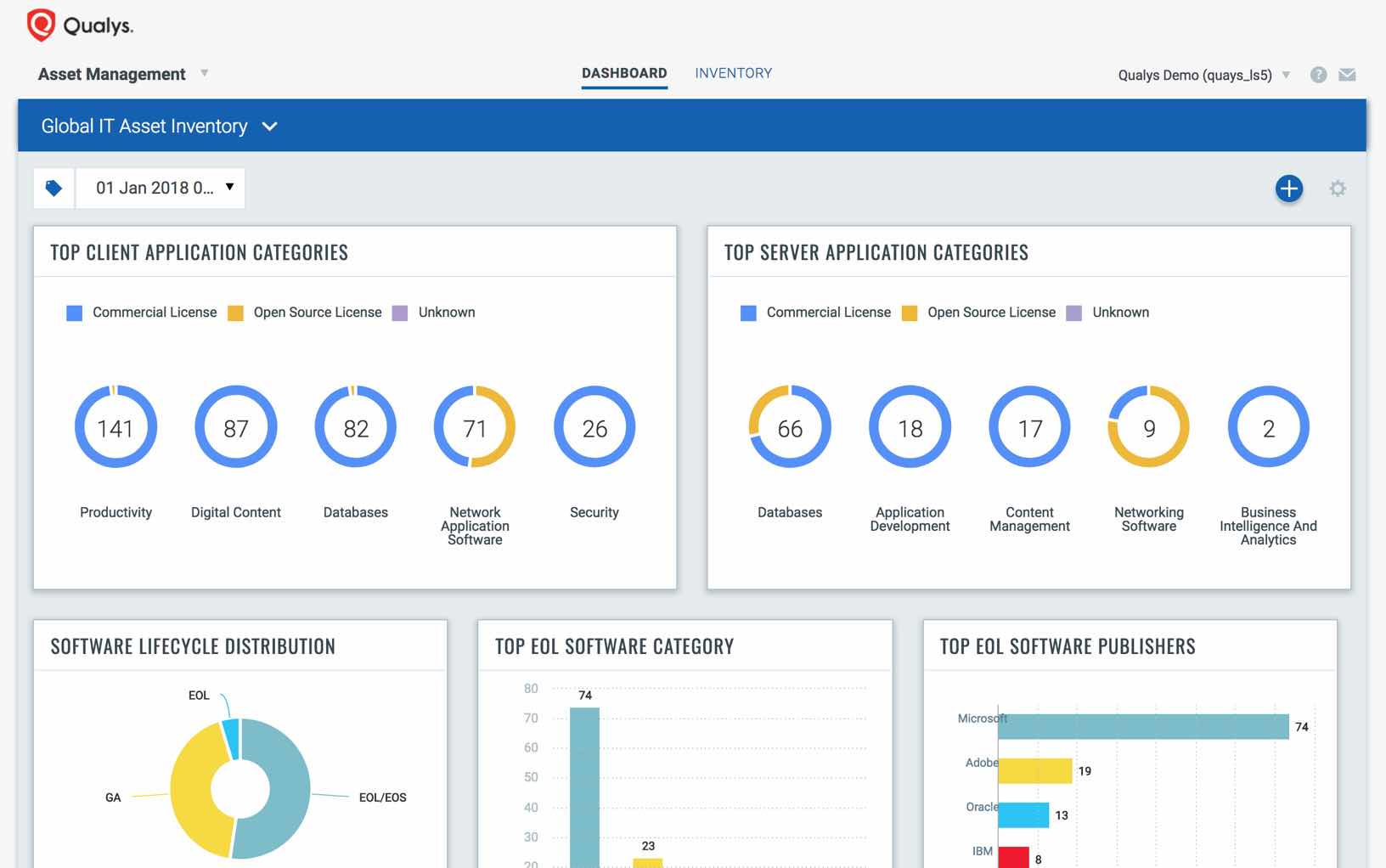
The Qualys technology catalog automatically extends asset information with non-discoverable metadata, such as product release dates, end of life dates, and license category. “The catalog is continuously curated, with a focus on completeness, relevance, and data quality, so that you can slice and dice, prioritize, and make informed decisions,” he said.
Qualys AI also has capabilities to sync with Configuration Management Databases (CMDBs) to keep asset data up-to-date.
In this way, Qualys AI gives security teams an invaluable “single source of truth” for IT asset data, as it discovers all assets across their global, hybrid infrastructure.
Watch the on-demand version of Quiroga’s presentation, which goes into a lot more detail on these and other topics, features a demo of Qualys AI, and includes a Q&A with the audience.