Qualys Study Reveals How Enterprises Responded to Log4Shell
On December 9, 2021, a critical zero-day vulnerability affecting Apache’s Log4j2 library, a Java-based logging utility, was disclosed to the world. This was no small announcement. As the third most used computer language, Java is practically ubiquitous. Its Log4j2 library is extremely popular. Billions of devices around the globe currently run Java. Most enterprises likely have multiple versions of it running throughout their computing systems.
This new weakness discovered in Java was soon given a name: Log4Shell. In the cybersecurity hall of fame – one that includes nasty past exploits like HeartBleed, WannaCry, and ShellShock – Log4Shell was found to be in a league all its own. Difficult to locate but easy to exploit, it was clear that this vulnerability would have a massive impact across nearly every industry… hitting only two weeks before the holidays.
The Cybersecurity Industry Springs into Action
It didn’t take very long for this critical Java vulnerability to be exploited in the wild. Nearly 1 million attack attempts were launched in just 72 hours following the Log4Shell vulnerability’s disclosure.
There was no time to waste. The bad guys didn’t care that it was the holiday season. With many companies preparing to operate with skeleton IT staffing during the final two weeks of 2021, hackers and attackers saw an opportunity. The race was on.
Qualys was among the first industry players to analyze the threat and develop effective countermeasures to mitigate this dangerous new vulnerability. Our Qualys Cloud Platform is a unified cybersecurity and compliance solution comprised of a suite of specialized cloud apps that help global enterprises manage their vulnerabilities, threats, and exploits.
We’ve indexed more than 10 trillion datapoints across our installed enterprise customer base and completed 6 billion IP scans per year with 75 million cloud agents deployed in hybrid IT environments globally. With that kind of scale, Qualys occupies a unique vantage point capable of ferreting out Log4Shell wherever it hides.
Quickly identify Log4Shell vulnerabilities using our cloud platform
Enterprise IT Response to Log4Shell, by the Numbers
Qualys Research Team analyzed anonymized security data across the networks of global enterprises using Qualys Cloud Platform. By examining how and where the Log4j2 library was implemented across organizations worldwide, we were able to provide the following insights on Log4Shell’s impact within a month of its disclosure.
Here’s a window into how the world’s enterprises responded.
Log4Shell Exposure
- Qualys Cloud Platform scanned more than 150 million IT assets, across all geographies, flagging 22 million vulnerable app installations. Of these, more than 80% were open source applications.
- Log4Shell was detected in more than 3 million vulnerable instances.
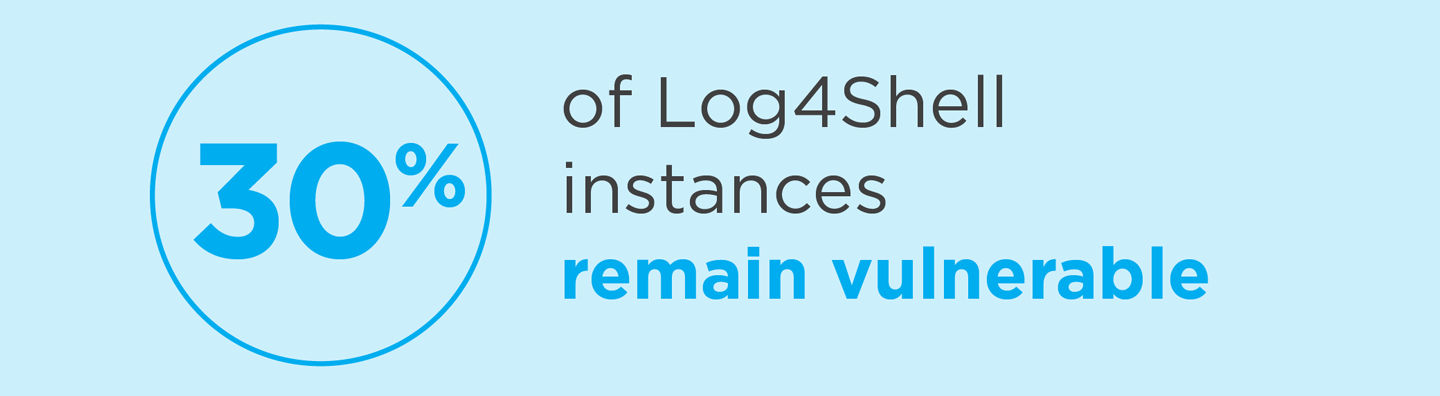
- More than two months later, 30% of Log4j instances remain vulnerable for exploit.[1]
Log4Shell Threat Landscape
- Nearly 68,000 vulnerabilities were found in cloud workloads and containers across the US and EMEA, reinforcing the recommendation that enterprises need to monitor running containers for flaws like Log4Shell.
- CISA and NCSC reported 1,495 products vulnerable to Log4Shell, and of those we observed 1,065 products across 52 publishers currently in use. This indexing proved very valuable to Qualys customers as this SBOM mapping is provided out of the box, providing immediate insights into their vulnerable software inventory.
- Surprisingly, more than 50% of application installations with Log4j were flagged as “end-of-support”. This means that these publishers will likely NOT be providing Log4Shell security patches for these apps.
- The vulnerability was detected in more than 2,800 web applications. Since web apps are publicly facing, this was the first line of defense for many enterprises looking to fend off early attacks. In the U.S., most detections occurred before/during the holiday period, while in the E.U. these spiked after the holidays.

Vulnerability Trends
- The vast majority of the vulnerable assets (over 80%) were on Linux.
- A total of 98 distinct log4j versions were observed in use, 55% of which were vulnerable versions.
- There was a 20% spike in detections as the New Year arrived and employees returned to work.
- Within the first month after Log4Shell’s disclosure, we observed that 12% of total log4j installations were vulnerable, while only 5% were not.

Remediation Trends
- Average time to remediation after detection was 17 days. Systems which could be exploited remotely were patched faster (12 days) while internal systems were slower.
- After the first month, remediation efforts plateaued and began trending down, quite likely because security teams are finding it easier to mitigate Log4Shell rather than permanently fixing it.

Attack Patterns
- Our threat intelligence research team observed attempted ransomware attacks by Conti, Khonsari, and nation state-backed adversaries based on Log4Shell, as reported by VentureBeat.
- Our Multi-Vector EDR solution detected 22,000 potential attacks per week at the height of the crisis. Many of these were scattershot “spray & pray” attacks trying to infect as many systems as possible quickly. Our data indicates that threat actors were trying to take advantage of the holiday season window of opportunity.
- Attacks also trended down into January, as mitigating controls and patches were rolled out by enterprise IT teams.
Within 24 hours, the Qualys Research Team had published its findings and launched a Log4Shell resource center to keep the industry updated. We released over 70 vulnerability detections and continued to release more as vendors released patches for their vulnerabilities. We hosted a series of webcasts for customers and non-customers alike on the steps we recommended for remediation.
Given the ubiquity of Log4Shell, we realized that having more enterprises detect it quicker would benefit the entire cybersecurity community. With this in mind, Qualys developed a new open source Log4j scanning utility to save security teams valuable time. To help enterprises quickly detect and remediate these vulnerabilities we offered complimentary access to our unified security and compliance platform for 30 days.
Quickly identify Log4Shell vulnerabilities using our cloud platform
Conclusion
Thankfully, critical vulnerabilities as severe as Log4Shell are a rare occurrence. However, the future discovery of another weakness just as bad (or worse) is inevitable. That’s why all enterprises, large and small, are well advised to invest in a best-in-class platform solution that can aid security operations, IT asset management, vulnerability detection and response, cloud security, EDR, and web app protection. CxOs should make sure that their security and IT Ops teams have a unified view of the organization’s risk posture. Real-time threat intelligence like that from the Qualys knowledgebase helps enterprises to continuously assess, monitor and report on the latest and greatest security threats so that, when “next time” inevitably arrives, we’ll be ready.
Footnotes
- does not account for any mitigations applied