Qualys Cloud Suite 8.6 New Features
This new release of the Qualys Cloud Suite, version 8.6, includes updates for usability and functionality across the platform as well as Vulnerability Management and Policy Compliance.
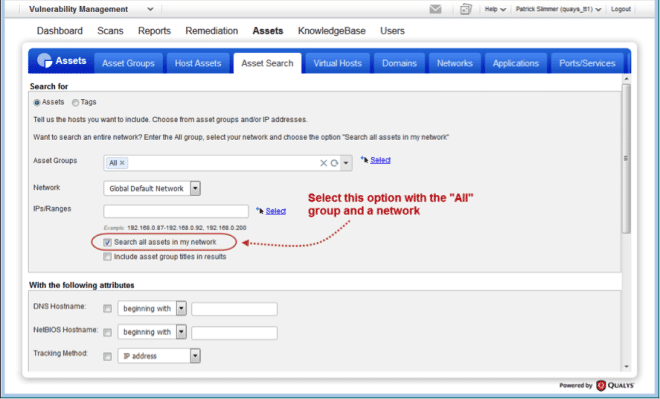
Cloud Platform: Several new core improvements have been implemented in this release to make scanning and searching for information easier across PC and VM. We added the ability to scan by tags by selecting your scanner appliance based on tags and added a new search widget to simplify finding asset tags wherever they are used. We made improvements to the authentication dashboard to simplify analysis of Scan Status, and enabled searching across all assets without having to specify network ranges. New platform support for NetApp was added to support VM and PC scanning of certain NetApp device share information.
Vulnerability Management: You now have the ability to download KnowledgeBase data via CSV/XML, and a number of new reporting improvements (Most Vulnerable Hosts, Patch) were added providing more detail and search options to those reports. We have added new report template options for handling agent data for assets with multiple IP addresses, so that relevant data can be selectively included in the Scan Report, and the Library was updated with new items to support SSL Certificate reporting. You can now also view multiple Oracle instances on a port.
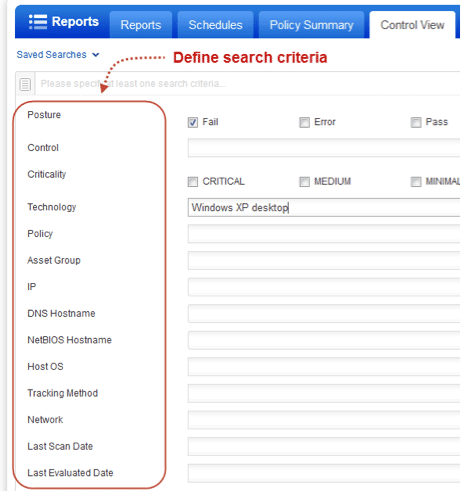
Policy Compliance: You can now use Control View to dynamically query information about compliance posture across controls and policies. This will allow you to easily and quickly find specific control results, enabling you to perform a variety of ad-hoc queries that previously would require exporting of data for analysis outside of Policy Compliance. You can quickly find what policies are associated with assets, filter by a variety of compliance posture values such as criticality, pass/fail state, and much more! When you are done searching for information, you can save your queries and share them with other users in your subscription.
Feature Highlights
- Qualys Cloud Platform
- Select Scanner Appliances using Asset Tags
- NetApp Technologies Supported
- Better Understand Authentication Status for Scanned Hosts
- Search All Assets in a Network
- Now it’s Easier to Find Asset Tags
- Qualys Vulnerability Management (VM)
- View multiple Oracle instances on a port
- Download the KnowledgeBase to CSV, XML
- MVH Report – Shows Severity Levels based on Search Lists
- Patch Report – Include Patches from Unspecified Vendors
- Display Host Identification Information in Reports
- New Library Items for SSL Certificates
- Qualys Policy Compliance (PC/SCAP)
- Display reference information in reports
- View and search controls at single location
Qualys Cloud Suite 8.6 will be released according to the schedule below. For release notifications containing details specific to each platform and to subscribe to release notifications for your platform, please see the following:
Qualys Cloud Platform
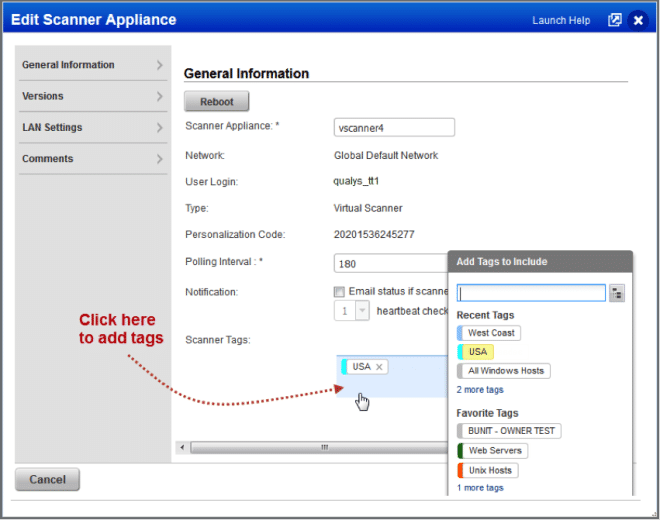
Select Scanner Appliances using Asset Tags
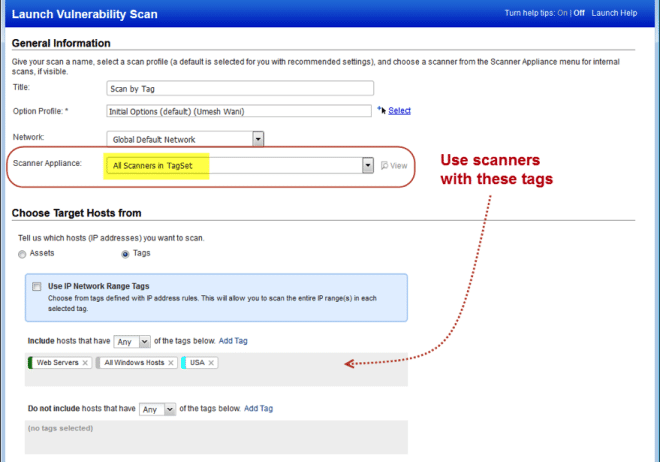
With this release you can use asset tags to select scanner appliances for your scans which will make it easier to dynamically select scanners for your scan jobs. For example, scan hosts with the asset tag USA using scanner appliances with the tag USA. You’ll need to first assign tags to your scanner appliances. Then be sure to specify the scan target using tags and choose the scanner option “All Scanners in TagSet”. This option is available for vulnerability scans and compliance scans.
Launch a scan using All Scanners in TagSet
Select the scanner appliance option “All Scanners in TagSet” and choose one or more tags for your scan target. This option is also available when scheduling scans.
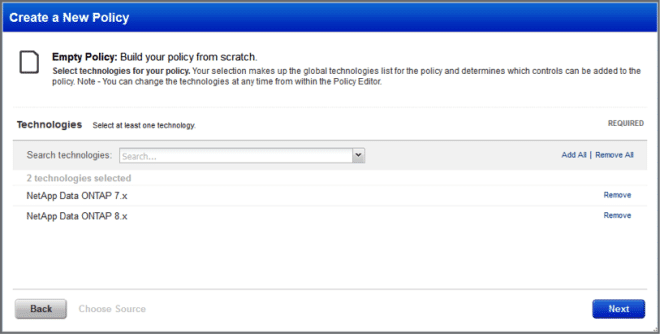
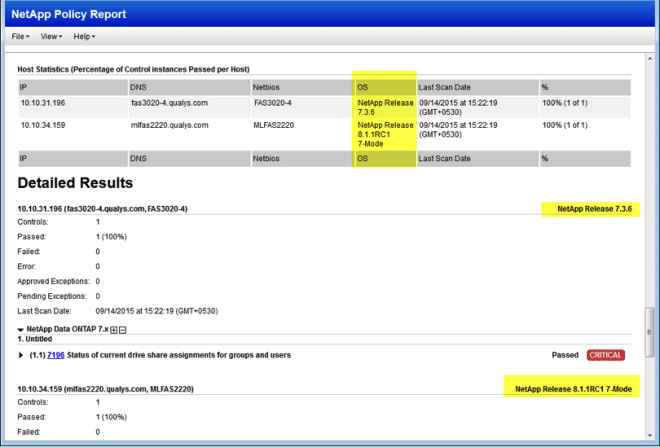
NetApp Technologies Supported
With this release we can accurately detect NetApp Data ONTAP operating system versions on your NetApp filer devices and map them to a technology. When you scan your NetApp devices, we will enumerate shares and report the following QIDs (VM) and CIDs (PC).
QIDs: 90635* 90797 90798 90831 90978
CIDs: 4528* 7196 7197 7198
* Requires that you select the “Windows Share Enumeration” option in your scan option profile. This allows us to count files in a share directory that is available to Everyone on Windows. (Note – We will always enumerate shares. This option is only needed to count files)
We currently support NetApp Data ONTAP 7.x and NetApp Data ONTAP 8.x 7-Mode platforms. The NetApp Clustered Data ONTAP 8.x platform is not supported.
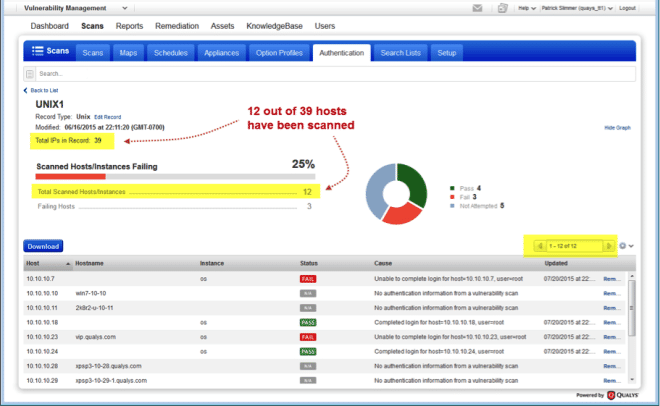
Better Understand Authentication Status for Scanned Hosts
The authentication summary now tells you the number of IPs in your record and the total number of scanned hosts/instances. When you view record details, the list will only include scanned hosts with the status of Pass, Fail or N/A (Not Attempted, meaning not scanned using authentication). We will no longer list hosts in the record that have not been scanned.
Search All Assets in a Network
You can now easily perform an asset search across all assets in a network without entering the IPs/ranges, making it much easier to find assets in VM.
Now it’s Easier to Find Asset Tags
We’ve updated our asset tag selector for scans and reports. Now when you search for tags, we’ll show the first 10 results and a “Show more” link. Just click the link to see all matching tags and select the ones you want to include in your scan or report.
 <insert image of Add Tags widget>
<insert image of Add Tags widget>
Qualys Vulnerability Management (VM)
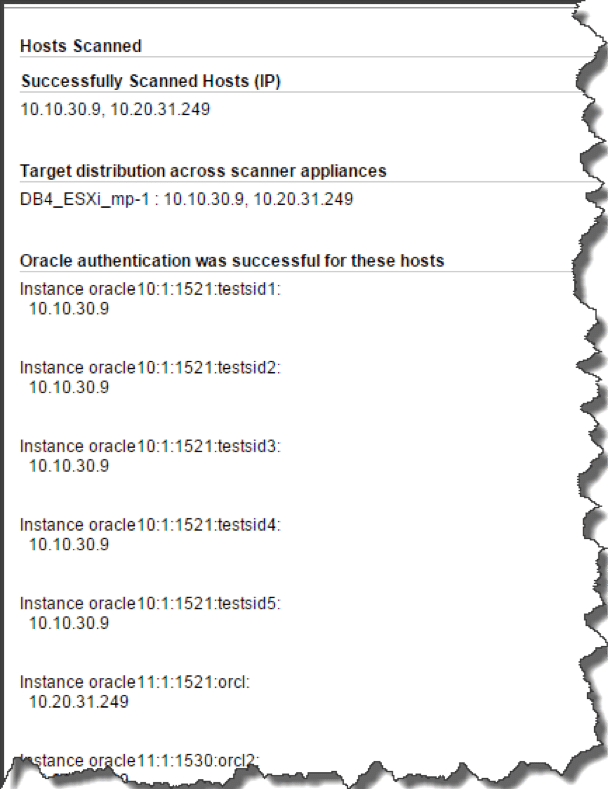
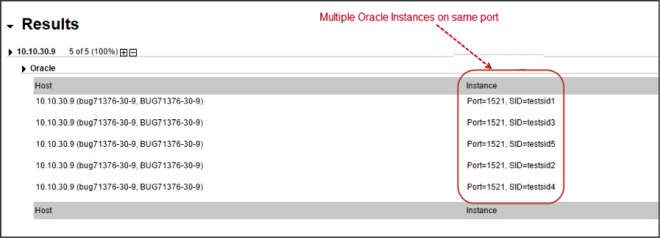
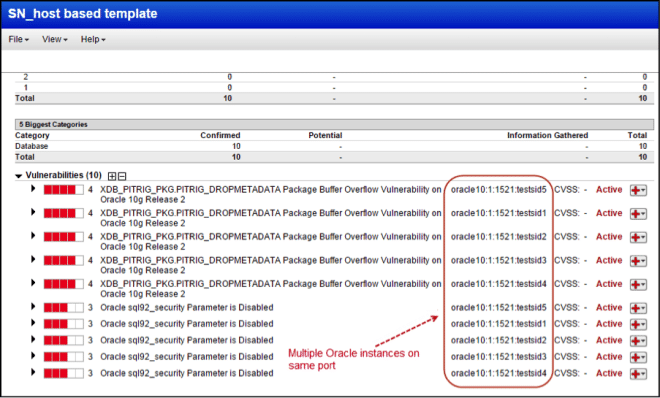
View multiple Oracle instances on a port
Now you’ll see scanned Oracle database instances listed separately in your scan results, in reports and asset views. Note you’ll need to create a separate Oracle authentication record for each of the instances you want to scan.
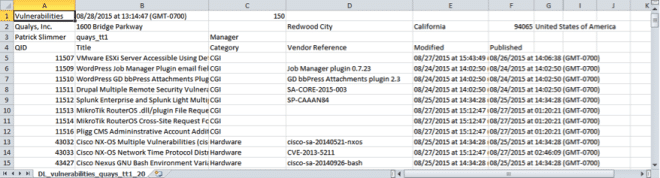
Download the KnowledgeBase to CSV, XML
You can download the KnowledgeBase in the same way you download other data lists. Simply choose Download from the New menu when you’re on the KnowledgeBase tab. Then select a file format (CSV or XML). Only the records and columns shown in the UI will be included in the downloaded report.
Sample CSV Report:
Sample XML Report:
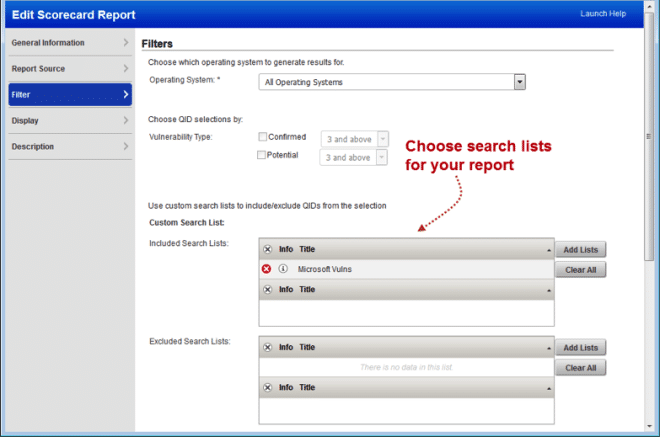
MVH Report – Shows Severity Levels based on Search Lists
When you customize your Most Vulnerable Hosts Report using search lists, we’ll now display the severity levels that match your search lists. We’ll show the lowest severity level in your search list plus higher severity levels. For example, if the lowest severity in the search list is 2 then your report will show severity levels 2, 3, 4 and 5. If the lowest severity is 5 then your report will only show severity 5.
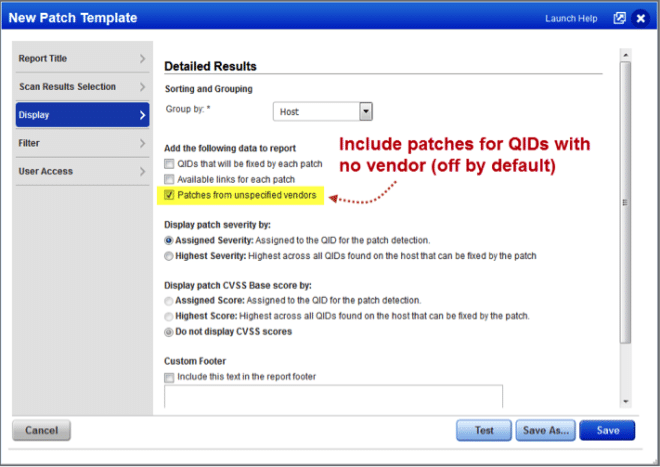
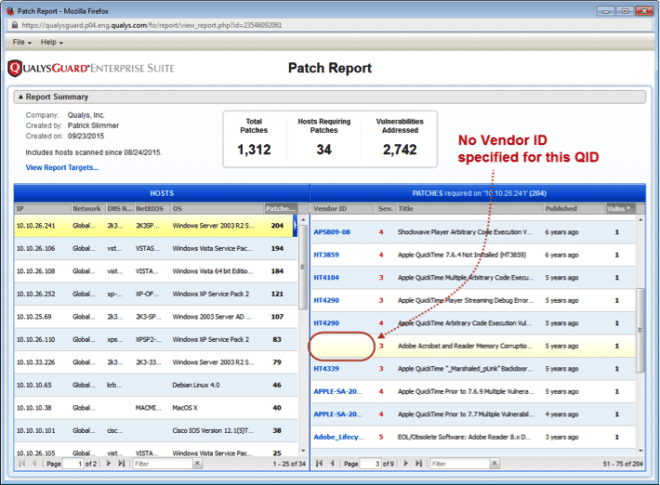
Patch Report – Include Patches from Unspecified Vendors
We’ve added a new option to the Patch Report template that allows you to include patches in your report for vulnerabilities for which we do not currently have vendor information. You will not see a Vendor ID for these QIDs in your report.
Here’s a sample report showing a QID that does not have a Vendor ID. This QID is included in the report because “Patches from unspecified vendors” is selected in the template.
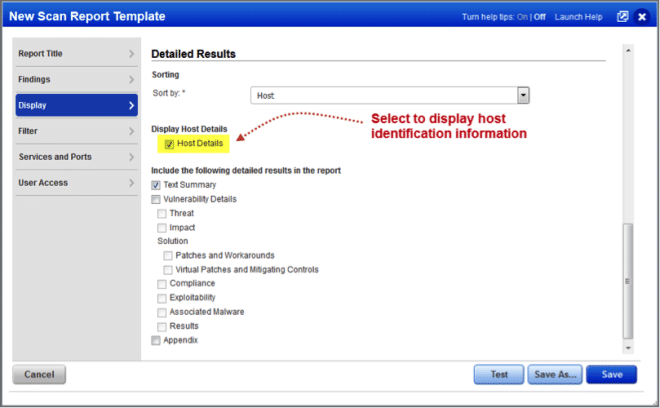
Display Host Identification Information in Reports
When you have cloud agents they’re collecting additional host information. Now you can include identifying information in your scan reports like the asset ID and related IPs (IPv4, IPv6 and MAC addresses) for each host agent. (This option is only available when VM agents are licensed in your account.)
Here’s a sample report showing host identification information for host 10.10.196.180. Host identification information may be included in all report formats (HTML, PDF, XML, etc).
New Library Items for SSL Certificates
Our Library provides several pre-configured options that you can import into your account. We’ve added a new SSL Certificates option profile and search list to the Library for use in detecting SSL certificates and calculating SSL grades. Import is supported from Option Profiles, Search Lists, and from Assets. See the release notes for more details on each option.
Tell me about SSL Grades – Available only when the SSL Labs Grade feature is enabled for your subscription. SSL Labs has been integrated with Qualys VM to provide grades for your certificates. When enabled, you’ll see a letter grade (A+, A, A-, B, C, D, E, F, T, M, NA) for each certificate on your certificates list. This grade is intended to help you identify and prioritize certificates with SSL configuration issues.
Qualys Policy Compliance (PC)
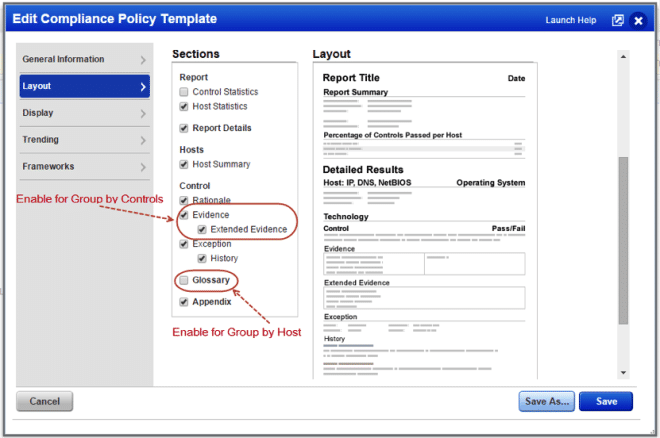
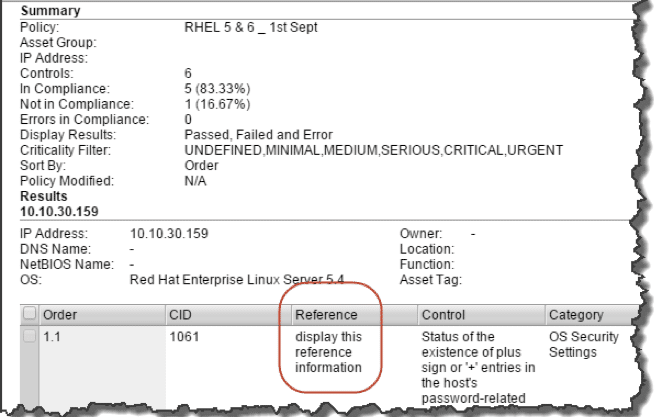
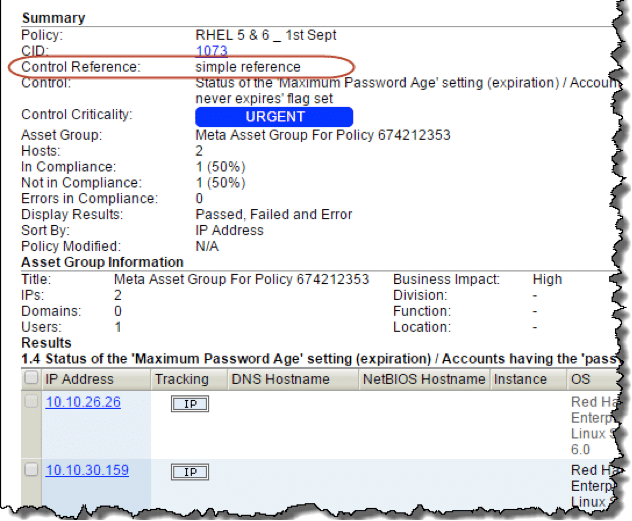
Display reference information in reports
User-defined control references can now be displayed in Policy Compliance reports and Interactive reports.
Policy Compliance report
Compliance Interactive reports
Individual Host Compliance Report
View and search controls at single location
You now have the ability to view and search for information, across all controls and policies in your subscription. This makes it easier for you to navigate your compliance data. You can save and share the queries with other users. Information is displayed as per user permissions.
Define search criteria
Save search
Release Schedule
For release notifications containing details specific to each platform, including the release date, and to subscribe to release notifications for your platform, please see the following: