Unpacking the CVEs in the FireEye Breach – Start Here First
In a blog post on Dec. 22, 2020, Qualys revealed it has identified 7.5 million instances of vulnerability to the stolen FireEye Red Team assessment tools across an anonymized set of its 15,700-member customer base.
Of the 7.5 million instances of vulnerability, 99.84% were caused by only 8 CVEs, and over 99% were caused by these five CVEs: CVE-2020-1472, CVE-2019-0604, CVE-2017-11774, CVE-2016-0167 and CVE-2019-0708.
In this article, we examine the five CVEs in detail to:
- Help SOC and operational security teams understand the behavioral aspects of these CVEs and plan defensive strategies;
- Help threat hunting teams understand their threat attributes and associated attack vectors and take defensive actions against adversaries actively exploiting these CVEs.
From a threat perspective, we explore threat attributes like IoCs, signatures, observables, and malware associated (like ransomware, cryptomining, etc.) with the CVEs. Since these CVEs are related to red teaming exercises, we also provide the list of threat actors known to have widely exploited these CVEs. Finally, we explore the adversary Tactics, Techniques and Procedures (TTPs) applicable for each CVE.
While Qualys VMDR is well equipped to detect and patch the respective CVEs, we also present the Indicators of Compromise (IoCs) and signature details associated with the CVEs that can be detected using Qualys Multi-Vector EDR. The mitigation details are provided with related vendor-released patch details.
For a detailed walkthrough of this research and how Qualys VMDR and EDR can help security teams address the threat, please sign up for the webinar on Thursday, February 4 at 10am Pacific: Unpacking the CVEs in the FireEye Breach.
CVE-2020-1472 (QID: 91668)
A privilege escalation vulnerability exists when an adversary establishes a vulnerable Netlogon secure channel connection to a domain controller using the Netlogon Remote Protocol. An adversary who successfully exploits the vulnerability could run a specially crafted application on a device on the network. See CVE-2020-1472 security update.
This vulnerability will further allow an adversary on the same network as the domain controller to forge an authentication token and reset the domain controller password to a value known only by the adversary.
The following mapping diagram shows the threat mappings to CVE-2020-1472.
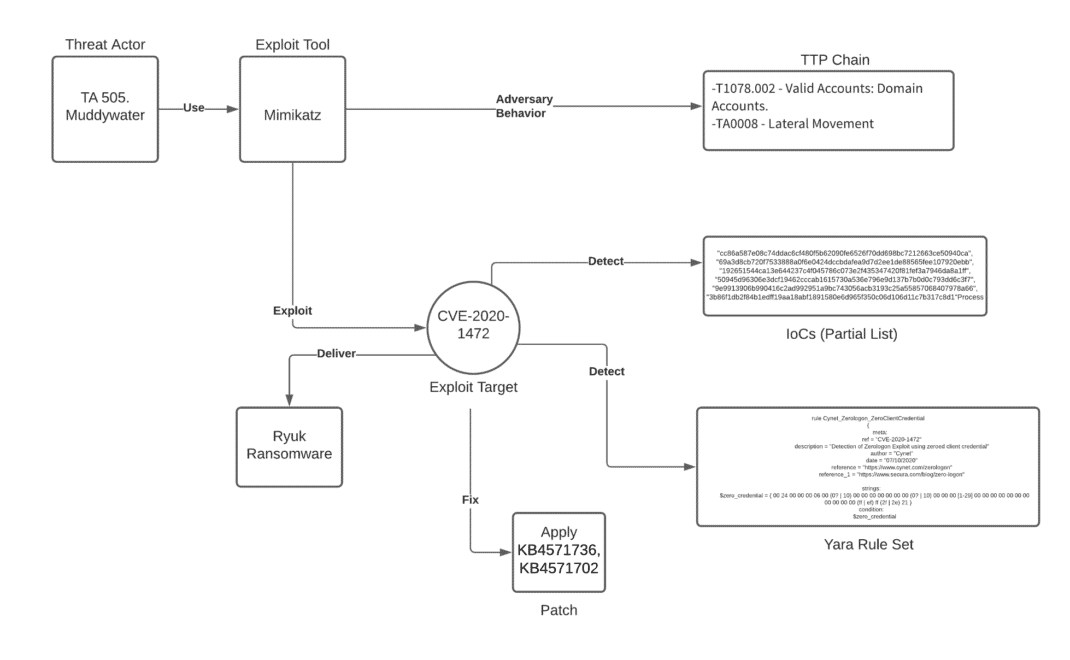
Threat Attribution
Following the release of the PoC code for this vulnerability on Sept. 11, 2020, a fully functional exploit was included in the “Mimikatz” tool. According to Microsoft Security Intelligence, threat actors quickly launched campaigns that took advantage of the vulnerability’s critical impact and the available exploit. Notable among the threat actors are: TA 505 (aka Chimborazo), Muddywater (aka Mercury), and Ryuk ransomware gang. The threat actors applied the following distinct attack vectors:
- TA 505 (aka Chimborazo) leveraged the legit tool “Mimikatz” to exploit the Zerologon vulnerability and further deployed a campaign with fake updates to connect to the threat actor’s C2 infrastructure to perform escalation of privileges.
- The Ryuk ransomware group exploited the Zerologon vulnerability to escalate privileges on target machines. The actor group was further able to reset passwords on the primary domain controller after which they moved laterally to the second domain controller. Researchers further revealed that the Ryuk group pivoted from the primary domain controller, using RDP to connect to the backup servers. See the Ryuk in 5 Hours from the DFIR Report.
Prevention and Detection
Adversary attempts to exploit CVE-2020-1472 can be identified by running QID 91668 from Qualys scanner and prevented by applying KB4571736, KB4571702 patches from Microsoft.
In cases of post-exploitation detection, the following detection methods can be applied.
- Yara rule set can be used to scan memory dumps of lsass.exe and will alert upon detection of Mimikatz or other Zerologon exploits.
- Scan target infrastructure for existence of the set of IoCs provided by Qualys.
Adversarial TTP
Following are the TTP steps sequence that represent adversarial actions:
- Valid Accounts: Domain Accounts [T1078.002]. Allow unauthenticated adversary to gain escalated privilege to domain controller.
- Lateral Movement [TA0008]. Malicious adversaries can leverage this vulnerability to compromise other devices on the same network
CVE-2019-0604 (QID: 110330)
A remote code execution vulnerability exists in Microsoft SharePoint when the software fails to check the source markup of an application package. An adversary successfully exploiting the vulnerability could run arbitrary code in the context of the SharePoint application pool and the SharePoint server farm account. See CVE-2019-0604 security update.
The following mapping diagram shows the threat mappings to CVE-2019-0604.
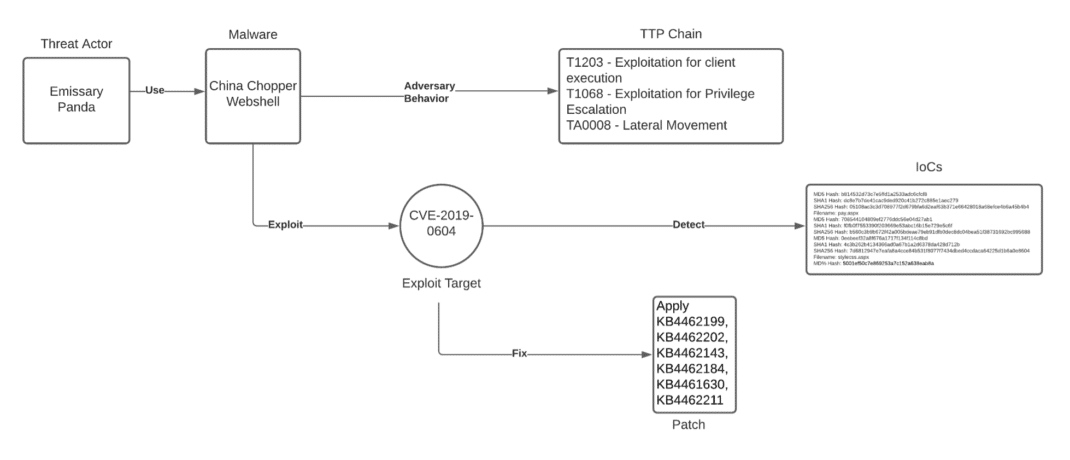
Threat Attribution:
CVE-2019-0604 has been primarily used to install webshells on target SharePoint servers.
Emissary Panda (aka APT27, TG-3390, Bronze Union, Lucky Mouse) threat actor has been identified back in April 2019 to have extensively exploited CVE-2019-0604 to install webshells (primarily China Chopper) on SharePoint servers targeting Government Organizations. The threat actor group further performed lateral movement by dumping credentials using Mimikatz in the post-exploitation phase.
Prevention and Detection
Adversary attempts to exploit CVE-2019-0604 can be identified by running QID 110330 from Qualys vulnerability scanner and prevented by then applying KB4462199, KB4462202, KB4462143, KB4462184, KB4461630, KB4462211(for applicable product versions) patches from Microsoft.
In cases of post exploitation detection, organizations can look up for the following CVE-2019-0604 IoCs within their environment.
MD5 Hash: b814532d73c7e5ffd1a2533adc6cfcf8
SHA1 Hash: dc8e7b7de41cac9ded920c41b272c885e1aec279
SHA256 Hash: 05108ac3c3d708977f2d679bfa6d2eaf63b371e66428018a68efce4b6a45b4b4
MD5 Hash: 708544104809ef2776ddc56e04d27ab1
SHA1 Hash: f0fb0f7553390f203669e53abc16b15e729e5c6f
SHA256 Hash: b560c3b9b672f42a005bdeae79eb91dfb0dec8dc04bea51f38731692bc995688
MD5 Hash: 0eebeef32a8f676a1717f134f114c8bd
SHA1 Hash: 4c3b262b4134366ad0a67b1a2d6378da428d712b
SHA256 Hash: 7d6812947e7eafa8a4cce84b531f8077f7434dbed4ccdaca64225d1b6a0e8604
MD5 Hash: 5001ef50c7e869253a7c152a638eab8aAdversarial TTP
Following are the TTP steps sequence that represent adversarial actions:
- Exploitation for client execution [T1203]. Adversaries exploit a deserialization technique without input validation in the DecodeEntityInstanceId method within the Microsoft.SharePoint.dll library. The method is ultimately exposed to authenticated end-users through a picker.aspx page, where a specially crafted web request could lead to execution of arbitrary code.
- Exploitation for Privilege Escalation [T1068]. Adversaries execute a webshell to elevate their privileges on target SharePoint server.
- Lateral Movement [TA0008]: Adversaries use post exploitation tools like Mimikatz to perform credential dumping and perform lateral movement on the target network.
CVE-2019-0708 (QID: 91541, 91534)
A remote code execution vulnerability exists in Remote Desktop Services – formerly known as Terminal Services – when an unauthenticated attacker connects to the target system using RDP and sends specially crafted requests. This vulnerability is pre-authentication and requires no user interaction. An adversary who successfully exploits this vulnerability could execute arbitrary code on the target system. The adversary could then install programs; view, change, or delete data; or create new accounts with full user rights. See CVE-2019-0708 security update.
The following mapping diagram shows the threat mappings to CVE-2019-0708.
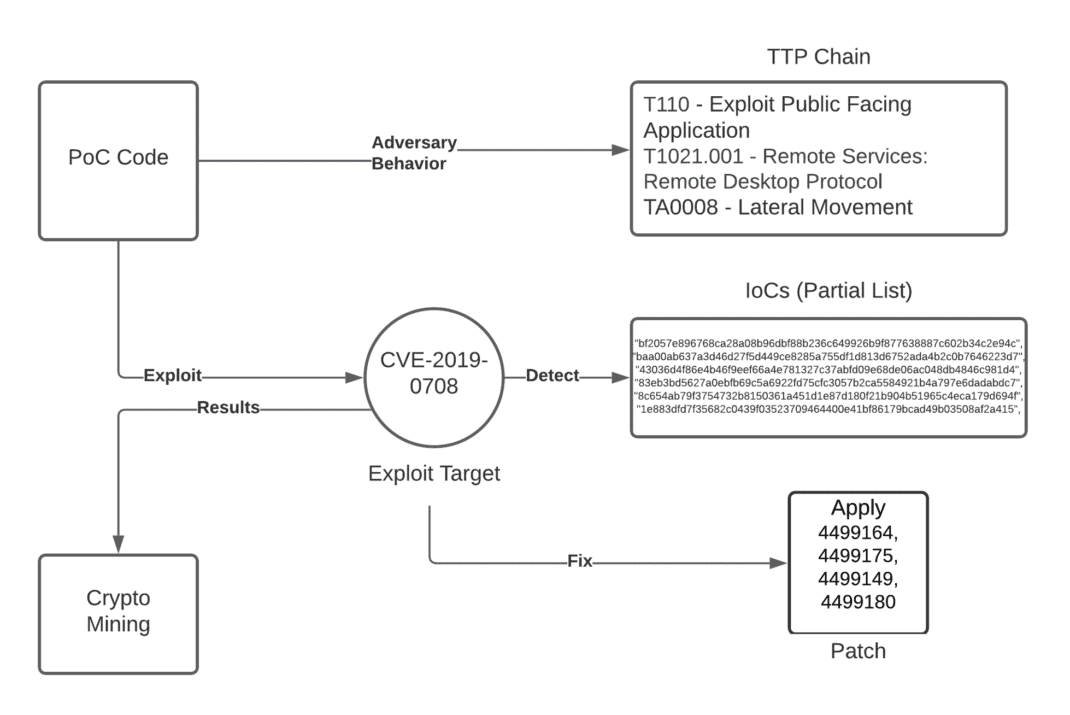
Threat Attribution
Since CVE-2019-0708 can be exploited remotely by sending a specially crafted RDP request and given its wormable nature, a working PoC exploit code was available 24 hours after the vulnerability was disclosed.
Due to the critical impact this vulnerability has on the target network, it’s heavily targeted by various threat actors. Primarily for cryptomining.
Prevention and Detection
Adversary attempts to exploit CVE-2019-0708 can be identified by running QIDs 91541, 91534 from Qualys vulnerability scanner and prevented by then applying KB4499164, KB4499175, KB4499149, KB4499180 (for applicable product versions) patches from Microsoft.
In cases of post exploitation detection, scan target infrastructure for existence of the set of IoCs provided by Qualys.
Adversarial TTP
Following are the TTP steps sequence that represent adversarial actions
- Exploit Public Facing Application [T1190]. Adversaries scan for internet facing systems running a required RDP version.
- Remote Services: Remote Desktop Protocol [T1021.001]: Adversaries send a specially crafted request to target RDP service.
- Lateral Movement [TA0008]. Using to the wormable nature of the vulnerability, adversaries perform a rapid lateral movement over the target network.
CVE-2017-11774 (QID: 110306)
A security feature bypass vulnerability exists when Microsoft Outlook improperly handles objects in memory. An adversary who successfully exploits the vulnerability could execute arbitrary commands. An adversary could provide a specially crafted document file designed to exploit the vulnerability, and then convince users to open the document file and interact with the document. See CVE-2017-11774 security update.
The following mapping diagram shows the threat mappings to CVE-2017-11774.
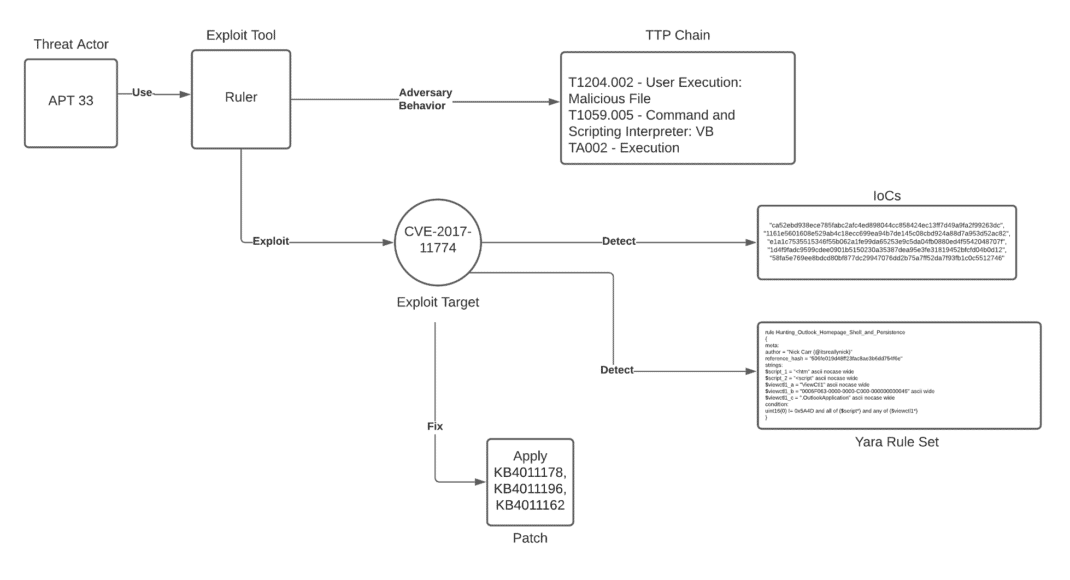
Threat Attribution
The US cyber command has issued an alert about threat actors’ active malicious use of CVE-2017-11774. While the alert did not mention the threat actor, further research revealed the threat actor to be APT 33. The threat actor is known for using the exploitation technique published by SensePost and combining it with password spraying techniques for lateral movement on the target network.
Prevention and Detection
Adversary attempts to exploit CVE-2017-11774 can be identified by running QID 110306 from Qualys vulnerability scanner and prevented by then applying KB4011178, KB4011196, KB4011162 (for applicable product versions) patches from Microsoft.
In cases of post-exploitation detection, the following detection methods can be applied:
- Yara rule set can be used to detect Outlook home page shell and persistence.
- Scan target infrastructure for existence of the set of IoCs provided by Qualys.
In cases of post-exploitation detection, can be used to detect Outlook home page shell and persistence.
Adversarial TTP
Following are the TTP steps sequence that represent adversarial actions:
- User Execution: Malicious File [T1204.002]. The adversary sends a malicious URL or file for the user in a phishing attempt to click.
- Office Application Startup – Outlook Home Page [T1137.004]. When the remote URL is clicked, it will render the contents using the Windows DLL ieframe.dll. This will persist through system restarts. allowing the adversary an attacker to achieve remote code execution that persists through system restarts.
- Execution [TA002]. Since the rendered code is persistent, the adversary performs remote code execution.
- Lateral Movement [TA0008]. Adversaries use password spraying techniques to perform lateral movement over the target network.
CVE-2016-0167 (QID: 91204)
A privilege escalation vulnerability exists when the Windows Graphics Component improperly handles objects in memory. An adversary who successfully exploited this vulnerability could run processes in an elevated context. In a local attack scenario, the adversary could exploit this vulnerability by running a specially crafted application to take control over the affected system. See CVE-2016-0167 security update.
The following mapping diagram shows the TTP chain and observables related to CVE-2016-0167.
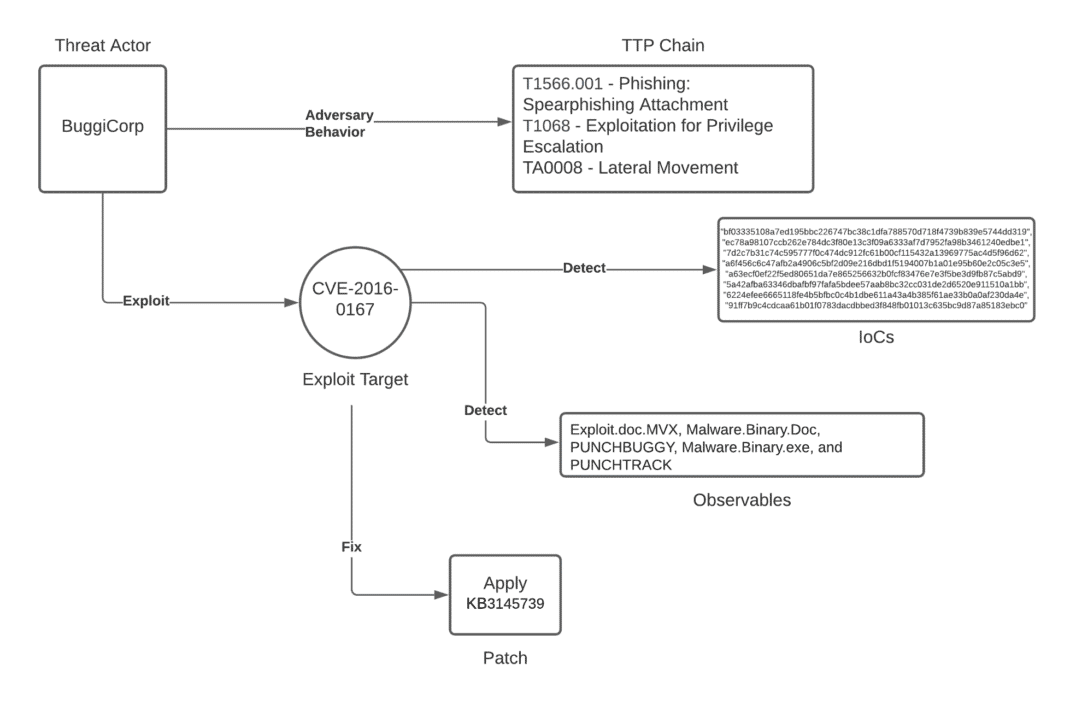
Threat Attribution
This local privilege escalation was targeted by “BuggiCorp” threat actor. The threat actor created the exploit for the zero-day version of CVE-2016-0167 and put it on sale for $90,000 in cybercrime forum exploit[dot]in.
In another instance, a financially motivated threat actor launched spear phishing email campaigns targeting CVE-2016-0167. This was primarily targeted towards retail, restaurant and hospitality industries8.
Prevention and Detection
Adversary attempts to exploit CVE-2016-0167 can be identified by running QID 91204 from Qualys vulnerability scanner and prevented by then applying KB3145739 patch from Microsoft.
Existence of the following observables will allow responders to identify the successful exploitation of CVE-2016-0167:
Exploit.doc.MVX, Malware.Binary.Doc, PUNCHBUGGY, Malware.Binary.exe, and PUNCHTRACK.
Finally, scan the target: Scan target infrastructure for existence of the set of IoCs provided by Qualys to detect the post-exploitation proof for CVE-2016-0167.
Adversarial TTP
- Phishing: Spear phishing Attachment [T1566.001]: Adversaries send documents with malicious links to end users
- Execution [TA002]. Perform remote code execution from the malicious link
- Exploitation for Privilege Escalation [T1068]: Adversary performs a local privilege escalation attack through the remotely executed code to gain escalated privilege
Remediate with Qualys Patch Management
This table shows the applicable patch details for each CVE.
| CVE | Patch KB |
| CVE-2020-1472 | KB4571736, KB4571702 |
| CVE-2019-0604 | KB4462199, KB4462202, KB4462143, KB4462184, KB4461630, KB4462211 |
| CVE-2019-0708 | KB4499164, KB4499175, KB4499149, KB4499180 |
| CVE-2017-11774 | KB4011178, KB4011196, KB4011162 |
| CVE-2016-0167 | KB3145739 |
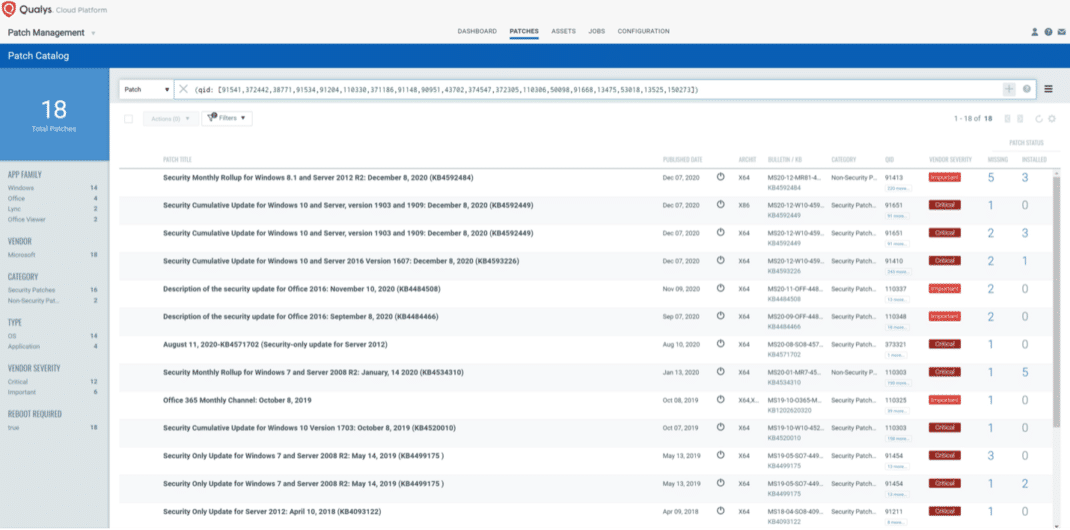
To view the relevant missing patches in your environment that are required to remediate the vulnerabilities leveraged by the FireEye tools you may run the following QQL in the Patches tab of Qualys Patch Management:
(qid: [91541,372442,38771,91534,91204,110330,371186,91148,90951,43702,374547,372305,110306,50098,91668,13475,53018,13525,150273]) The same QQL can be used in the patch assets tab in order to see all the assets that miss at least one of the FireEye-related patches. Refer to the image below.
Qualys has created two dashboard widgets that you can import into the patch management dashboard. These widgets show the number of missing FireEye-related patches in your environment and the number of assets in your environment missing one of those patches. You can download these two dashboard widgets from the PatchMGMT-Fireeye-Widgets attachment at the bottom of the FireEye Theft dashboards article.
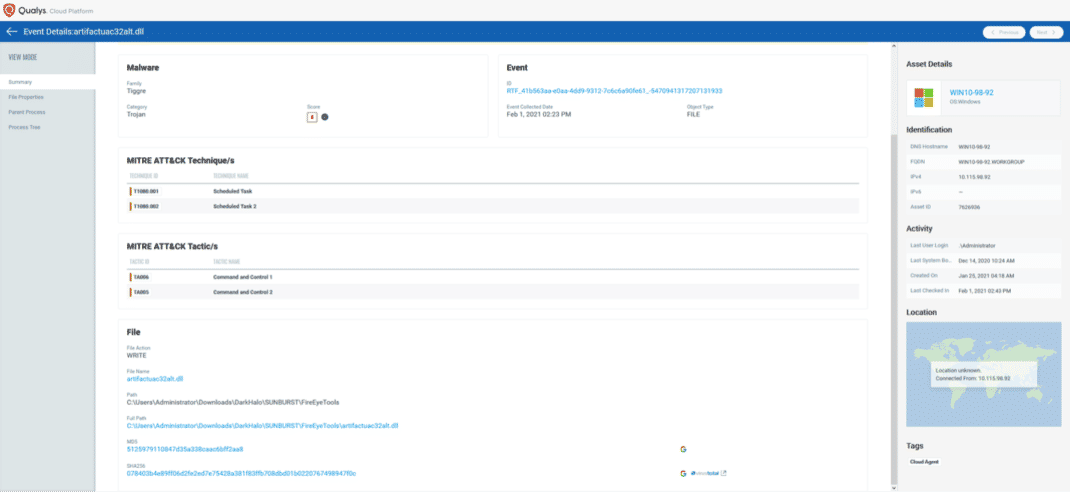
Hunting for Indicators of Compromise with Endpoint Detection and Response (EDR)
Qualys Multi-Vector EDR helps security teams hunt for evidence of these CVEs by looking for evidence of the files from the provided IoCs. End users can search for the above-mentioned IoCs and observables using the Qualys Query Language (QQL). For example, the MD5 hashes for CVE-2019-0604 can be searched using the following QQL:
file.hash.md5:["708544104809ef2776ddc56e04d27ab1","b814532d73c7e5ffd1a2533adc6cfcf8","0eebeef32a8f676a1717f134f114c8bd","5001ef50c7e869253a7c152a638eab8a"]
Further, Qualys EDR users can search their susceptibility to any of the applicable attack vectors by searching for the respective technique and tactic ids.
Resources
See the comprehensive list of all IoCs for each CVE referenced in this article. Right-click to download.
Assess and Act
The threat exposure details (like threat actor and adversarial TTP chain) for the CVEs presented above proves their high prevalence among cyber attackers, and especially, among state-sponsored threat actors who have been applying complex attack vectors to gain access to target networks by exploiting the above-mentioned CVEs.
While the Qualys Cloud Platform already prioritizes these CVEs (and associated QIDs) for remediation, we envision the comprehensive threat exposure details presented above will allow both cyber-attack detection and response teams to include an actionable plan to evaluate their exposure to impending attack vectors.
Learn More
For a detailed walkthrough of this research and how Qualys VMDR and EDR can help security teams address the threat, please sign up for the webinar:
Unpacking the CVEs in the FireEye Breach
Thursday, February 4 at 10am Pacific