Patch Tuesday May 2015
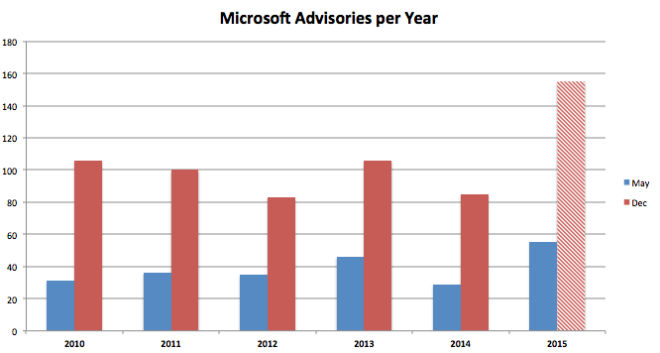
Today is Patch Tuesday May 2015, and it is coming on strong. Microsoft released 13 bulletins bringing the count for this year to 53. 53 is quite a bit higher than in any of the last five years, in fact I cannot remember a similar active year. Our internal tracking of vulnerability numbers now projects north of 140 advisories for this year, certainly also new record:
The main patch this month to address is MS15-043 for Internet Explorer (IE), which fixes 22 CVEs, of which 14 rated critical. Critical CVEs in IE allow the attacker to gain Remote Code Execution (RCE) on the machine of the target by luring the target go to a malicious webpage. Attackers have a variety of techniques in their arsenal to do so including:
- Attacking common blogging and forum software to gain control over the website and then include links to the malicious pages. A good example is the SoakSoak campaign. Recent vulnerabilities in this class have been in the Magento ecommerce engine and in WordPress CMS.
- Exploiting Online advertising providers and attach malicious links that get included automatically in unsuspecting websites that use the services of the provider, such as recently with MadAdsMedia.
- Using Search Engine Poisoning, a specialization of Search Engine Optimization (SEO) to attract traffic to special sites generated for that malicious content. Here every current subject is fair game: royal babies, accidents, recent sports events, free streaming, etc.
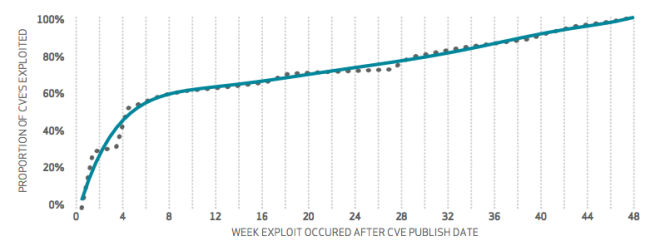
Attackers have at their disposal a number of exploits for a diverse set of vulnerabilities to adapt to the target’s machine. It is safe to say that their favorite attack vectors include Internet Explorer, native Windows vulnerabilities and Adobe Flash, which all receive monthly updates publishing upwards of 20 CVEs per month. You should be prepared to install these updates as quickly as possible. But how fast do you have to act? The latest Verizon Data Breach Investigation Report from April 2015 indicates that 50% of the newly exploited vulnerabilities they tracked get hit within two weeks:
But not all vulnerabilities get exploited. In fact in 2014 only 5% of all RCE type vulnerabilities in Microsoft software (see their RSA 2015 presentation) ended up having working exploits:
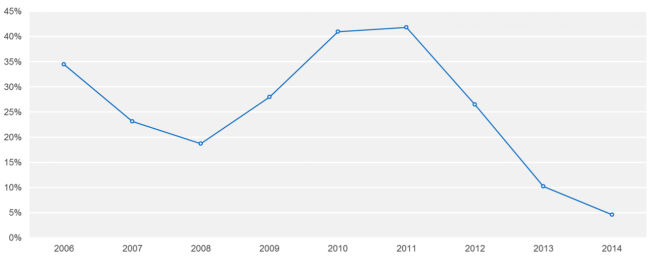
The difficulty is predicting which 5%. I think it makes sense to look at the past to see what got attacked and what vulnerabilities are covered in exploit packs and prepare accordingly. US-CERT just came out with a recommendation of 30 CVEs that they see attacked frequently and the German BSI has some strong views on what to look for as well. In a nutshell: Windows, Internet Explorer, Adobe Flash, Java, Office are on the top of their list.
Back to our Patch Tuesday: Next in our priority list is MS15-044, addressing two critical font vulnerabilities in the GDI+ library that affect many Microsoft products. Attackers can use webpages or documents that contain the malicious fonts to gain RCE. Fix MS15-044 with high priority.
MS15-046 is only ranked as important by Microsoft, but it addresses RCE file format vulnerabilities in both Word and Excel that attackers could use to gain control over your user’s machines. Both have as the attack vector e-mail attached documents that get sent to your user’s e-mail account in the expectation the documents get opened by their recipients. About 10% of the targets open them, according to data from the APWG (http://www.antiphishing.org) included in the VDBIR.
Speaking of file format vulnerabilities that yield RCE, Adobe also has a patch release this month. They are addressing critical problems in Adobe Flash and Adobe Reader/Acrobat in advisories APSB15-09 and APSB15-10. For Adobe Reader the attack vector is similar to the office scenario above an attacker needs to trick a user to open an attached PDF document that is formatted in a special way to execute the exploit. Once on the machine attackers would then use a second vulnerability to gain system administration privileges, for example any of the Kernel vulnerabilities that Microsoft is addressing in MS15-051 and MS15-052. Include both in your critical patch routine.
The remaining critical advisory covers Windows Journal with six vulnerabilities. Two of the vulnerabilities are publicly known, but are not being exploited. Patch quickly and evaluate disabling Windows Journal (a notebook application). I do not know anybody who uses Windows Journal, so I would recommend following the workaround described in the advisory and neutering the file description”.jnl” to counter this and future attacks on this software.
That’s it for May’s critical advisories. The remaining advisories deal with a number of other Microsoft products including the server software Sharepoint that gets a fix for a potential RCE type vulnerability in MS15-047.
Patch quickly, in less than two weeks if you can. I would enjoy hearing from you to see if you think this is realistic: wkandek@qualys.com. Thank you.
Hi Wolfgang.
The link to http://community.qualys.com/servlet/JiveServlet/downloadImage/38-2722-9668/bsi.png is broken.
It looks like a permissions issue.