What is the Apex Predator Doing to Get Your Information?
This week at the USENIX Enigma 2016 Security conference the final talk was given by Rob Joyce, Chief of the NSA’s Tailored Access Operations (TAO). TAO is the offensive unit of the NSA that got much coverage following the public disclosure of internal NSA documents by Edward Snowden, with some of their arsenal of exploitation tools documented.
In his talk “Disrupting Nation State Hackers” Joyce inverts his typical role and this time gives defensive advice. His point of view as the Apex Predator of APT units in the world gives him unique insight into what works in defense, i.e. what are the measures that make the work of the professionals under his command harder.
His fundamental recommendation is clear: know what devices and applications run on your network, then find the vulnerabilities in this setup. This is similar to what his attack team is doing when they get a new target, they invest time and effort on mapping the target’s infrastructure until they know it well enough to have found the open vulnerabilities. More often than not they find known vulnerabilities in the devices on the network. These known vulnerabilities have documentation and proof-of-concepts exploit code available that make the initial exploitation easier, making them far more attractive than relying on 0-days. Quick patching is one of the best measures that makes his team’s work harder and he calls slow patching an “inexcusable practice”.
He gives further advice on starting with secure baseline configurations, adding anti-exploitation software (such as Microsoft EMET) and reputation based whitelisting to your endpoints to gain further robustness. On the network side, strong segmentation is your ally and helps with anomaly detection that will be enable to find the intruders that still made it into your networks.
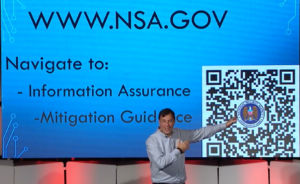
I recommend watching the whole presentation and sharing it with your friends and colleagues. Further detail on some of the defensive techniques mentioned can be found at the link referenced the the QR code in the above picture. If you rather not scan in a QR code made by the NSA you can go directly to their website to access the documents.