Oracle January 2017 CPU Fixes 270 Vulnerabilities
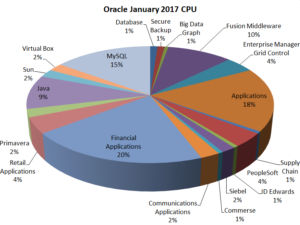
Oracle kicked off the New Year with its first installment of the quarterly CPU (critical patch update) for 2017. The update contains fix for 270 security issues across wide range of products. The graph below shows distribution of the update. More than 100 vulnerabilities that were fixed could be compromised by a remote attacker without requiring any credentials. Most remote vulnerabilities could be exploited over the HTTP protocol.
Java
This Critical Patch Update contains 17 new security fixes for Oracle Java SE. Sixteen (16) of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials. We recommend that organizations patch as soon as possible.
MySQL and Oracle Database
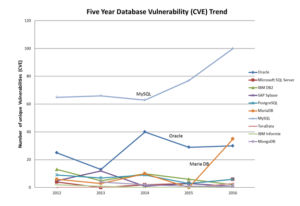
Twenty-seven (27) vulnerabilities were fixed in MySQL as compared to only 2 for the Oracle database. Five MySQL vulnerabilities were remotely exploitable while none were remotely exploitable in the Oracle database. The graph below shows the number of unique vulnerabilities found in various database over the course of 5 years. The highest number of vulnerabilities by CVE count in the last 5 years were found in MySQL. In addition MySQL had the highest rate of increase in vulnerabilities. In 2016 there was a 30% increase in the number of vulnerabilities in MySQL.
Sun, Solaris and Oracle Virtual Box
Both Sun Solaris and Virtual Box had 4 vulnerabilities fixed out of which 1 was remotely exploitable in both. The Solaris remotely exploitability vulnerability was in the kernel while remotely exploitable vulnerability in Virtual Box was in the GUI using HTTP protocol.
Applications and Fusion Middleware
Most of the vulnerabilities that were fixed in Oracle Applications, Fusion Middleware, Financial application and Retail applications could be exploited over HTTP. An attacker could send a specially crafted HTTP request without authentication to trigger the issue. More than 90 vulnerabilities were fixed in total in these applications.
To conclude, Oracle updates are huge and touch a wide range of products. As compared to older CPUs this was a regular-sized update but is bound to keep administrators busy due to the sheer number of vulnerabilities and products it touches.