Tenacity – An Adversary Emulation Tool for Persistence
Persistence is one of the more sought-after techniques of an attacker or adversary. Persistence is achieved through a set of tactics or techniques that adversaries use to maintain their foothold on compromised systems across restarts, changed credentials, and other interruptions that could cut off their access. According to cyber threat intelligence reports, three out of the top ten techniques used by attackers are persistence techniques. Because adversaries typically employ persistence techniques early in the attack lifecycle, it is important to detect them before adversaries cause any significant damage to the organization.
Working on the Qualys Threat Research team, we developed Tenacity, a lightweight adversary emulation tool that supports 30+ persistence techniques and 100+ procedures used by real-world attackers in the wild. We leveraged data from MITRE ATT&CK and open-source cyber threat intelligence to understand how adversaries achieve persistence on compromised systems. Using our tool, the organizations and individuals can quickly validate the risk posture and exposure of their business as well as the performance of existing security solutions.
Tenacity Components

The tool is developed entirely in python. It consists of 4 main components, namely, a command-line interface (CLI), database, set of modules and utility functions. The user interacts with the CLI by entering a sequence of commands. The data is derived from the MITRE ATT&CK knowledge base. It contains a list of techniques along with meta information about each technique such as the platform on which the given technique is applicable, attack groups that employ the given technique and data sources that can be used to detect the given technique. Tenacity has a module for each technique which makes use of the helper functions to run the emulation. Each module is a collection of different procedures, where each procedure is a specific set of commands that attackers execute to achieve persistence on the compromised system.
Demonstration
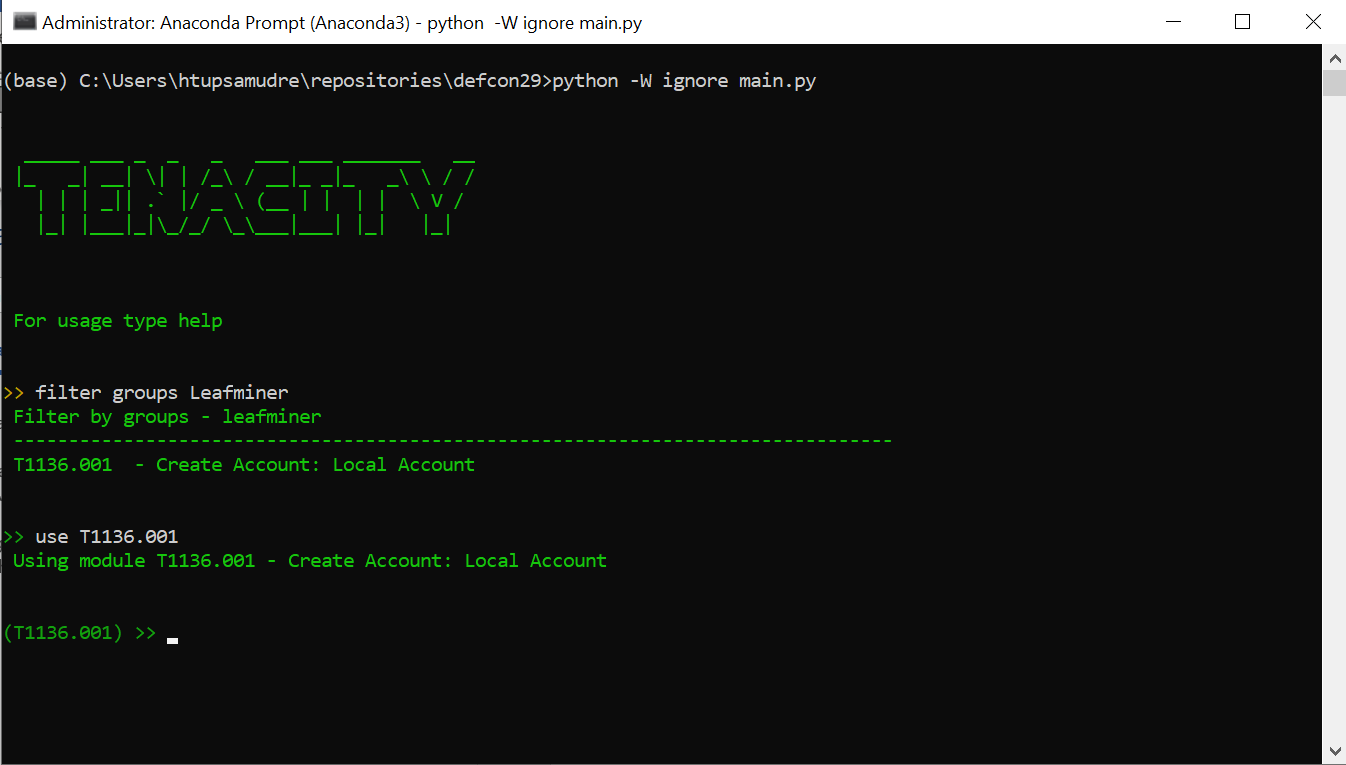
We demonstrate the usage of our tool through an example. Note that Tenacity requires admin privileges for performing emulations. Suppose that we want to emulate a persistence technique employed by a specific attack group, for instance, Leafminer (G0077). To list the persistence techniques employed by the Leafminer group, we need to use the filter command. The syntax of the command is filter groups Leafminer.

According to the MITRE ATT&CK knowledge base, the Leafminer attack group achieves persistence on a compromised system by creating a local user account (T1136.001). To select the technique T1136.001 for emulation, we need to employ the use command. The syntax of the command is use T1136.001.
After executing the use command, the prompt has been changed to reflect our selection of the T1136.001 technique. To list the different procedures available within the T1136.001 module, we can use the show procedures command.
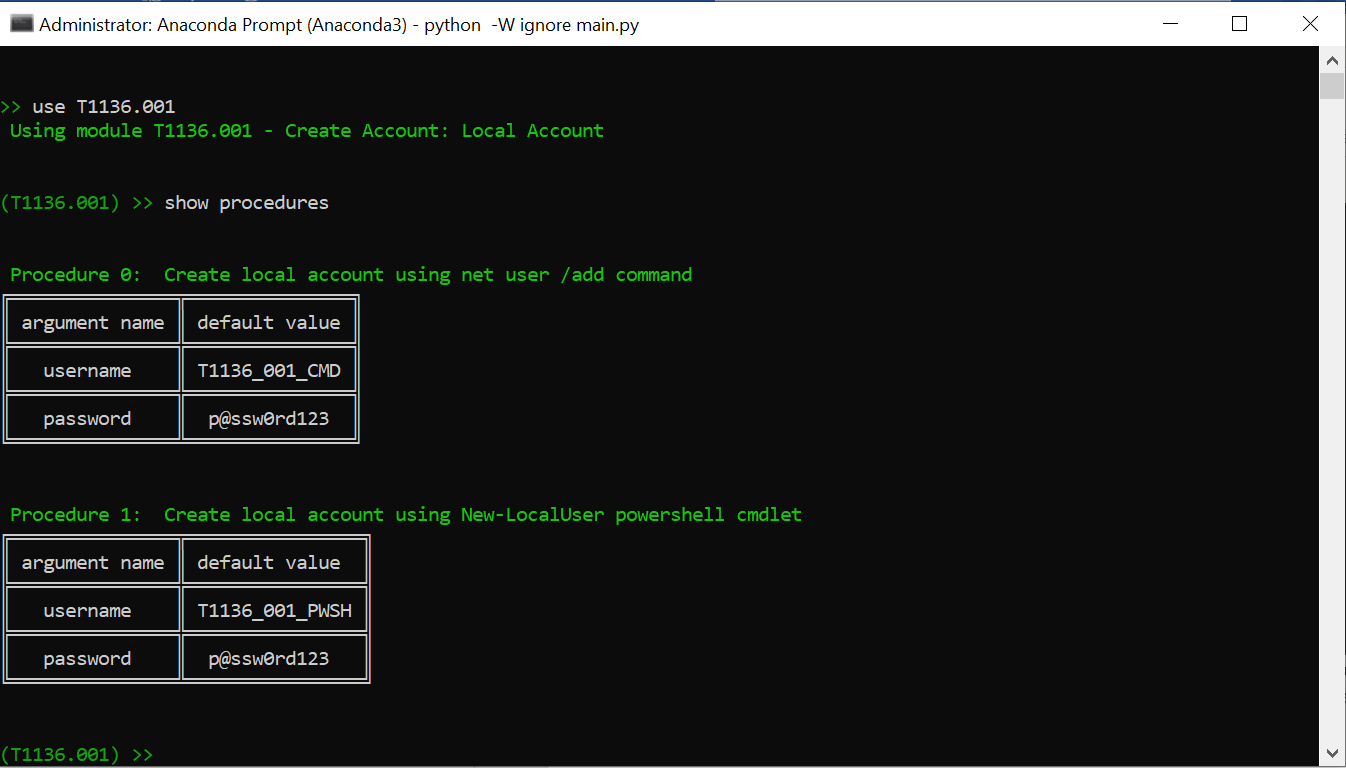
Currently there are two procedures available for emulation. The first procedure uses net user command, and it uses default username T1136_001_CMD and password value p@ssw0rd123 as shown in the first table. The second procedure uses powershell New-LocalUser cmdlet to create a new user, and it uses default username T1136_001_PWSH and password value p@ssw0rd123 as shown in the second table.
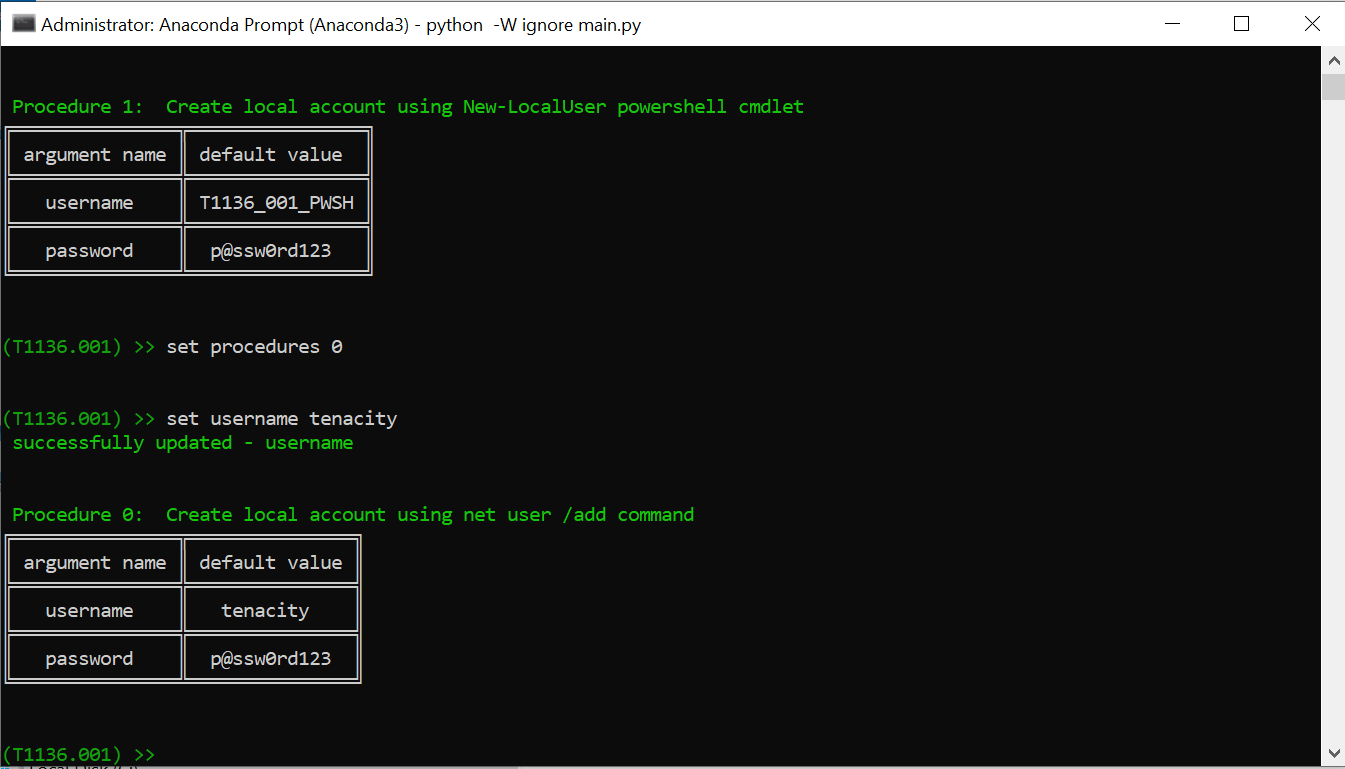
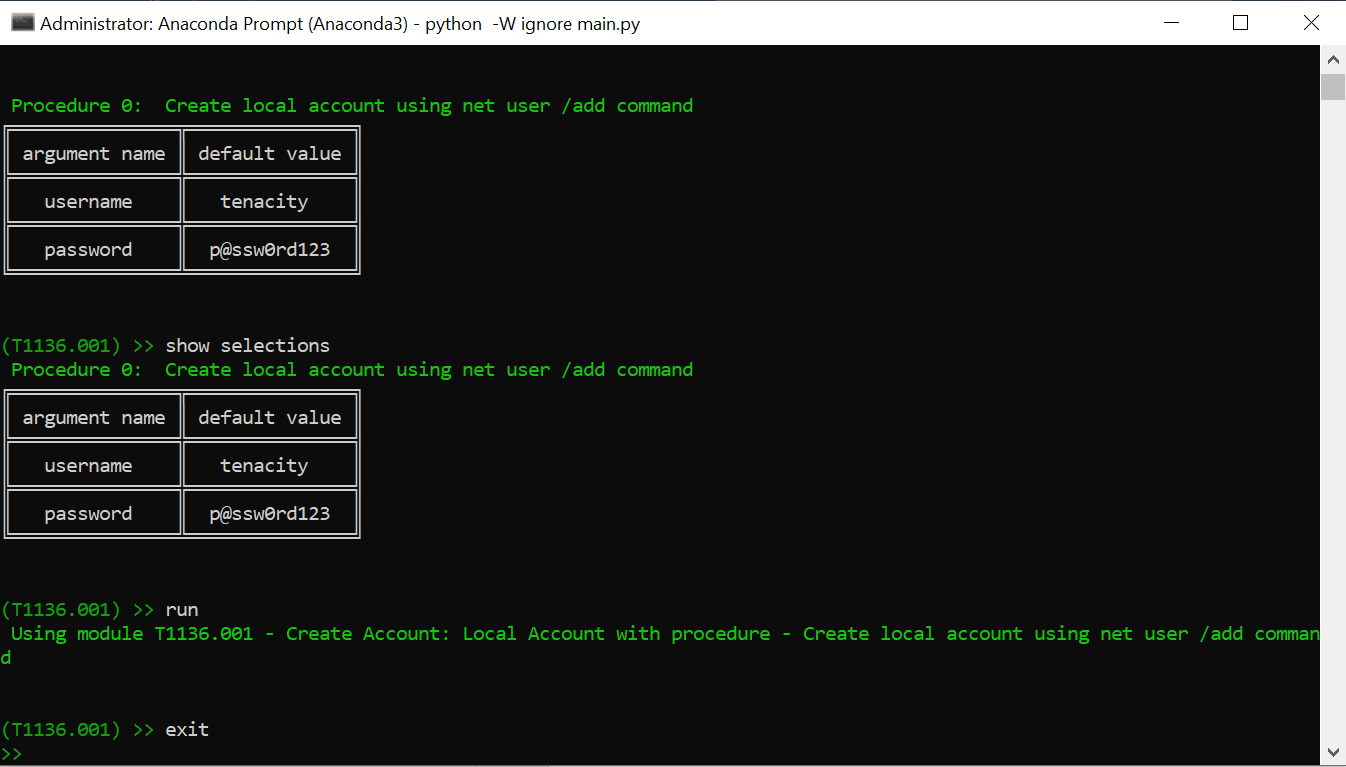
To select a procedure for emulation, we need to use the set procedures command. Let us select the first procedure for emulation. Since the procedures are numbered starting from 0, emulate the first procedure, we need to use the set procedures 0 command. After selecting the procedure, we can change the default arguments used within the procedure using the set command. For example, to change the username used in the selected procedure from T1136_001_CMD to tenacity, we can use the set username tenacity command.
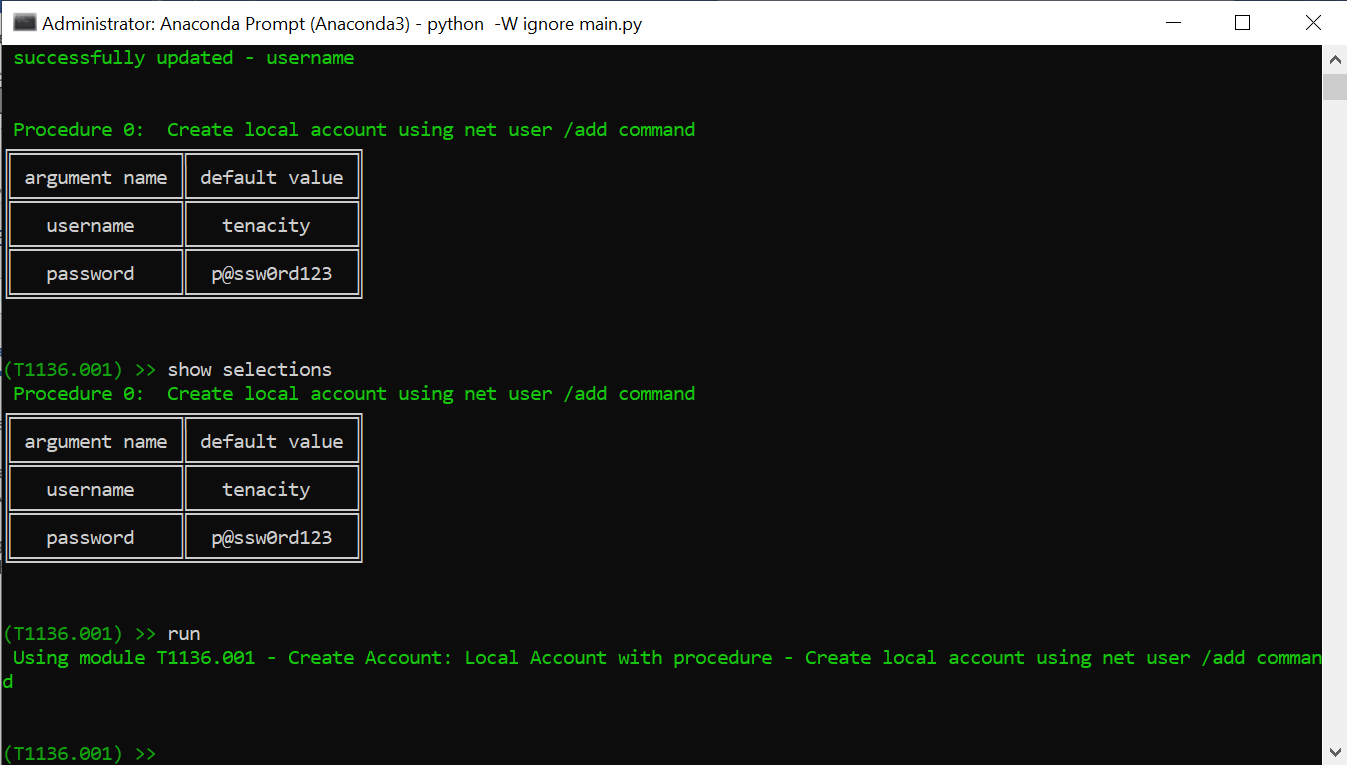
We can check the selected procedure using the show selections command.

Finally, we execute the selected procedure using the run command.
Once the procedure is executed, we can look at the log file for more details.
The run command not only executes the net user command, but it also performs other activities such as logging, auditing, and cleanup.
We have integrated our tool with the Windows event log. After the command is executed, our tool processes the Windows Security log and looks for relevant events. For instance, if a new user is created then event with id 4720 is generated. However, for this event to get logged into Windows security log on the system, we need to turn on the auditing for user account management if it is not already enabled. The tool uses the auditpol command to enable the auditing. Then, the tool executes the net user command. Once the command is executed, the tool uses the powershell Get-EventLog cmdlet to search the windows security log for event with id 4720. The tool filters the windows security log by event id and time and looks only for the most recent event that occurred after executing the net user command.

After executing the procedure, the tool performs cleanup activity. It turns off the auditing and deletes the created user account to restore the system in its original state.

Once a procedure from the technique T1136.001 is emulated, one can verify if the relevant telemetry is generated and the technique is detected by the deployed security solutions.
To exit from the selected T1136.001 module, we need to use the exit command. The interface prompts user to select another persistence technique for emulation.
Future Work
The development of Tenacity is in progress. We are working on some features to make the tool more usable. The tool has been integrated with Windows event logs; we are working to add support for Sysmon & other popular logs. We are also adding more export options (e.g., pdf) so that the result of the emulations can be consumed by other applications. We started with persistence techniques as they are the most sought-after techniques by attackers. However, we plan to release the tool and extend it to other techniques with the help of the security community.
We are demonstrating Tenacity in Adversary Village at DEF CON 29.
Contributors
Atul Nair, Malware Researcher, Qualys
Harshal Tupsamudre, Senior Threat Research Engineer, Qualys