Qualys Integrates with Shodan to Help Map the External Attack Surface
Qualys CyberSecurity Asset Management (CSAM) now natively integrates with Shodan to enable cybersecurity teams to identify all assets visible on the internet, including previously unknown and potential security issues… before attackers find them.
Your attack surface is dynamic. Assets come and go, and your infrastructure configuration changes to adapt to your business needs. Cybersecurity teams need to continuously monitor their external attack surface, track changes, and receive notifications when new, unknown assets or critical issues are found.
“Shadow IT”—unsanctioned technologies and applications deployed without IT oversight—has accelerated its sprawl across corporate networks as more teams adopt new cloud services and development processes without proper authorization.
Believe it or not, many IT and Security professionals still depend on spreadsheets to maintain an inventory of their externally facing assets. Typically, different teams within the same organization will have their own spreadsheet of such assets and rarely share this information. This approach is just not scalable, not only because the assets and their configurations are ever-changing, but also spreadsheets are not automatically updated with new assets. Many assets become visible on the Internet unintentionally, giving you no visibility into the “unknown unknowns”. Often these are assets managed by subsidiaries, acquisitions, or other partners.
Shodan is the search engine for every asset visible on the internet
Shodan.io is a popular tool that continuously scans the internet and indexes information about assets exposed to the internet, including basic information such as public IP addresses, open ports, listing vulnerabilities, and outdated app stacks.
Often tools like Shodan are leveraged by attackers to find low-hanging opportunities and entry points to organizations. These opportunities are not just limited to baby monitors, smart utility meters, and security cameras. Devices such as printers, cloud instances, and private database servers initially intended to be disconnected from the internet or otherwise protected by perimeter security are often found visible to the internet.
Security teams also use Shodan as a search engine to discover all their assets visible to the internet. However, it becomes yet another data source disconnected from their asset inventory, just like the spreadsheets or other free/commercial tools that maintain such information.
Security teams want to reduce the threat from unknown unknowns as much as possible. This includes assets on partner or third-party sites, workloads running on public clouds, IoT devices, abandoned IP addresses, and services enabled by Shadow IT.
They also want to automatically associate and add context to assets related to their organization, no matter where the asset is hosted or by whom.
And most of all, security teams want to know what an attacker’s reconnaissance will find, before they find it. They want to know their exposed vulnerabilities and risks from exploits, attack vectors, the ease/difficulty of exploitation, and the remediation complexities to correct their exposure.
Qualys CSAM lets you see what assets attackers see on the internet
Qualys CyberSecurity Asset Management (CSAM) now natively integrates with Shodan to enable you to correlate assets, tag existing inventory within Qualys to rank criticality, and highlight your unknown unknowns. Now you can quickly expand your visibility and security assessment of these blind spots.
CSAM queries Shodan and finds all assets related to your organization. CSAM then automatically tags these assets and compares them with the existing asset inventory already present in Qualys. It then identifies assets that Qualys does not currently manage. This allows you to quickly bring them under management through network scans or the Qualys Cloud Agent.
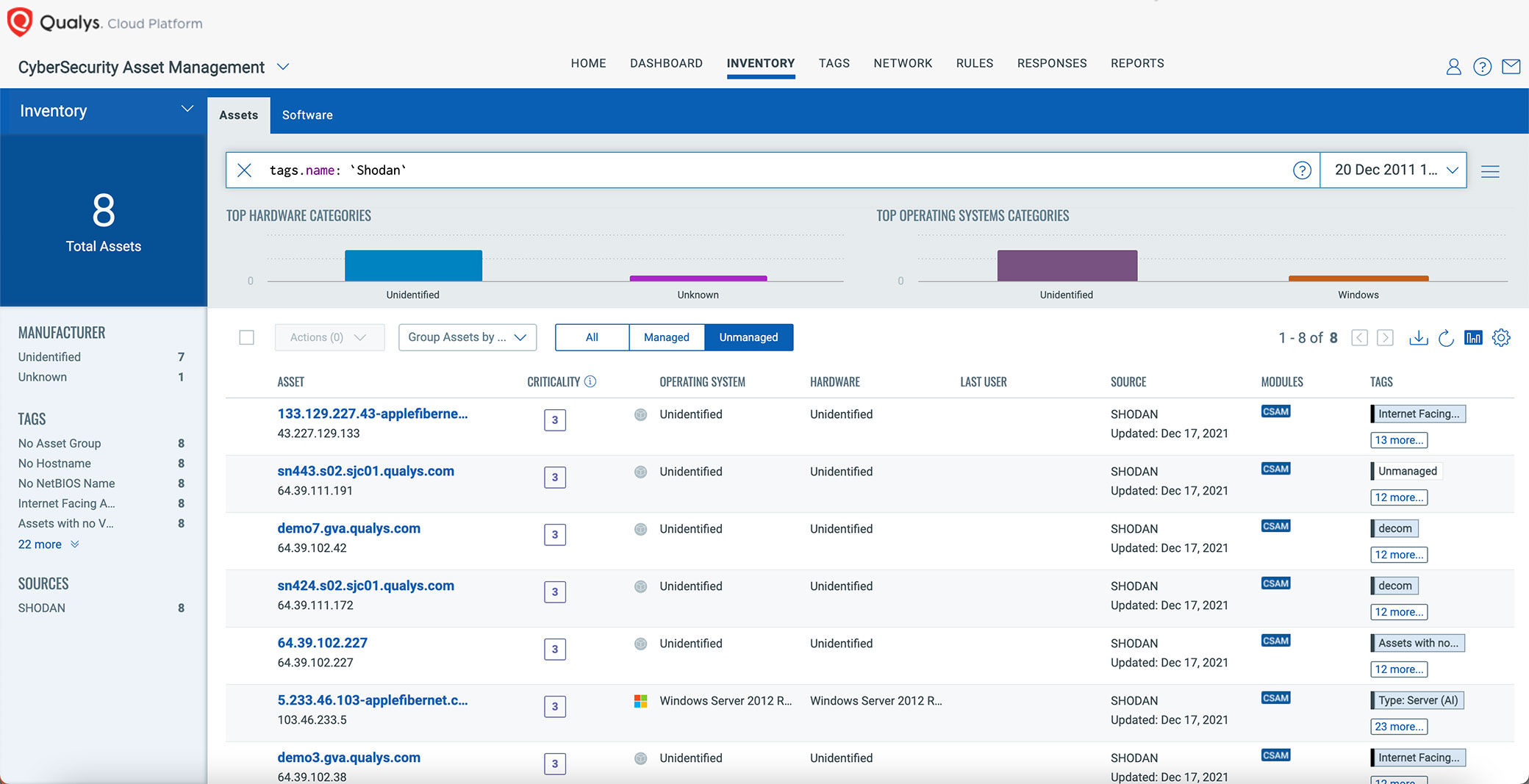
It’s easy to get this valuable insight in CSAM. All you need to do is provide a few basic filter criteria such as organization name, domain, or certificate name. Qualys will pull all assets matching those criteria from Shodan and update your CSAM inventory automatically with the information from Shodan.

Once the asset is scanned and managed with Qualys sensors, organizations can continuously gather comprehensive asset inventory data, apply business criticality and risk context, detect security gaps like unauthorized or end-of-life software, and respond with appropriate actions to mitigate risk.
Since this is all integrated within Qualys Cloud Platform, security teams can easily transition from discovering unknowns to fully inventorying these assets. Qualys then puts them into a proper security context, assessing them for vulnerabilities and misconfigurations, prioritizing and remediating risks, all from a single unified platform.
This integration with Shodan is the first step in getting full visibility of your external attack surface in CSAM. CSAM will continue to add more insights to evaluate your external attack surfaces better over the coming releases, such as horizontal and vertical domain and subdomain enumeration, WHOIS and DNS record correlation, certificate grades from SSL Labs, and data from data other feeds and sources.
The Shodan integration is now available to all Qualys customers having the CSAM subscription. Contact your Technical Account Manager (TAM) or Support to get this functionality enabled for your subscription today!
Learn more about CSAM and sign up for your own trial.
Not enough content to convince me. This appears to be another false Marketing claim.
Could not make any connection with Shodan work, the Print Screens does not show how to make it work.
This is coming of the top of massive false negatives with Log4j.