Cybersecurity Threat Landscape 2024 Midyear Review
Table of Contents
- Key Takeaways from the Threat Landscape Report 2024
- Vulnerability and Threat Analysis in the Cybersecurity Landscape 2024
- Cyber Threat Landscape 2024 A Detailed Review
- Key Statistics and Their Impact on the 2024 Cybersecurity Landscape
- Mid-2024s Most Exploited Vulnerabilities in the Cybersecurity Landscape
- Conclusion
As we navigate the complexities of 2024, it’s crucial to pause and reflect on the evolving threat landscape that surrounds us. This moment offers a unique opportunity to scrutinize our triumphs and missteps, understand the events that have decisively shaped our environment, and consider those that have subtly influenced it. By extracting key lessons from our recent experiences, we can fortify our strategies and prepare more effectively for the emerging risks that lie ahead.
This review delves into understanding vulnerabilities by identifying their evolution and primary concerns. This knowledge enables us to preemptively address risks. Armed with these insights, we’re better positioned to tackle upcoming challenges and leverage opportunities with greater confidence.
Key Takeaways from the Threat Landscape Report 2024
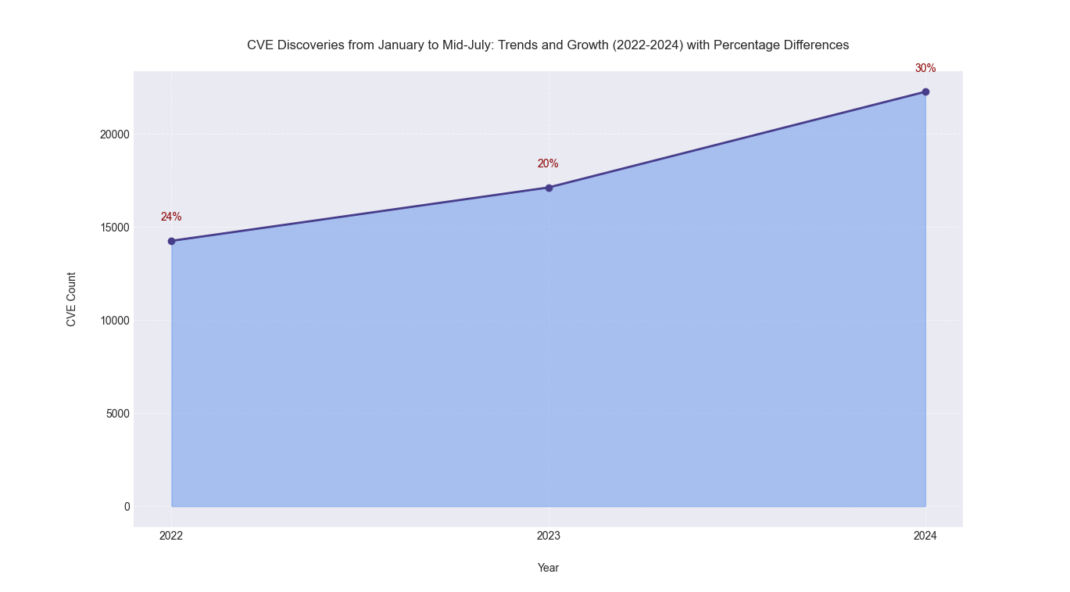
- From January to mid-July 2023-2024, the annual count of reported Common Vulnerabilities and Exposures (CVEs) rose by about 30%, from 17,114 in 2023 to 22,254 in 2024. This trend highlights a growing security challenge and the need for enhanced cybersecurity measures.
- In 2024, 0.91% of vulnerabilities (204 vulnerabilities) have been weaponized; they present a substantial threat, necessitating focused security measures.
- The primary security concerns of these weaponized vulnerabilities include exploiting public-facing applications for initial access and using remote services for lateral movement within networks.
- Our research reveals a 10% increase in the weaponization of old CVEs in 2024 (discovered prior to 2024), highlighting the need to address previously identified vulnerabilities.
Vulnerability and Threat Analysis in the Cybersecurity Landscape 2024
From January to mid-July 2022-2024, there has been an annual increase in the number of CVEs reported. The CVE count escalated from 14,249 in 2022 to 17,114 in 2023 and surged to 22,254 in 2024. Significant increases of 24%, 20%, and 30%, respectively, have been seen each year, underscoring a persistent and substantial escalation in vulnerability discoveries. The increase in CVEs reflects rising software complexity and the broader use of technology, necessitating advanced and dynamic vulnerability management strategies to mitigate evolving cybersecurity threats.
A thorough analysis of the 22,254 reported vulnerabilities during the initial seven and a half months of 2024 (up until our research cut-off date of July 21, 2024) reveals that a precise subset of 0.91% (almost 1%) has been weaponized. This very small fraction of vulnerabilities accounts for the most severe threats. This subset represents the highest risk, characterized by weaponized exploits, active exploitation through ransomware, use by threat actors, malware, or confirmed wild exploitation instances.
To effectively mitigate such threats, it’s crucial to prioritize actively exploited vulnerabilities, leverage threat intelligence, and regularly schedule scans to detect new vulnerabilities. A vulnerability management tool that integrates threat intelligence could be pivotal for an enterprise.
Our recent analysis also indicates an increase in the weaponization of old CVEs since the onset of 2024. Although old CVEs often resurface and get weaponized well after discovery, over the last 7.5 months, there has been a notable increase, slightly over 10%, in the weaponization of older CVEs identified before 2024, which is a stark reminder that cybersecurity is not just about staying ahead but also about not falling behind. Some of these vulnerabilities have been trending on the dark web for months. An example is CVE-2023-43208 NextGen Mirth Connect Java XStream (Qualys Vulnerability Score 95/100), which heavily involves systems used by healthcare organizations. This resurgence of previously identified vulnerabilities, which mainly impact remote services and public-facing applications, highlights a significant oversight in updating and enforcing cybersecurity protocols. This re-emergence emphasizes the need to shift from a purely reactive security posture to a more proactive, predictive, and preventative approach.
By adopting a holistic view that incorporates continuous monitoring, rapid patch management, and a deep understanding of the evolving threat landscape, businesses can significantly reduce their vulnerability to cyberattacks. This strategic foresight will protect critical assets and foster trust and resilience in our increasingly interconnected world.
Cyber Threat Landscape 2024 A Detailed Review
In the rapidly changing field of cybersecurity, keeping up with emerging threats is crucial. The first seven and a half months of 2024 have already presented a complex picture characterized by 22,313 reported vulnerabilities. A meticulous examination of these vulnerabilities reveals that only a tiny fraction, precisely 0.91% or 204 vulnerabilities, have been actively weaponized. Despite this seemingly low percentage, the impact and severity of these weaponized vulnerabilities are disproportionately high.

Key Statistics and Their Impact on the 2024 Cybersecurity Landscape
Several of these weaponized vulnerabilities are associated with multiple threat actors, highlighting their strategic value and effectiveness for various malicious purposes. Additionally, six are linked to ransomware campaigns, emphasizing ransomware’s continued prominence as a method for cyber extortion and posing a substantial risk to cybersecurity.
62.6% of vulnerabilities rank 95/100 or above on the Qualys Vulnerability Score (QVS), signaling them as critically important. QVS integrates multiple dimensions of risk assessment, including active exploitation, exploit maturity, and visibility on both the dark web and social media. Nearly half of these vulnerabilities (49.4%) are considered CVSS critical, emphasizing the severity but not necessarily the breadth of risk factors QVS considers. Moreover, the Exploit Prediction Scoring System (EPSS) indicates a high likelihood of exploitation (scores above 0.9) for only 18.6% of cases.
To enhance our understanding of these vulnerabilities, we are utilizing the MITRE ATT&CK Framework to analyze the frequency and distribution of tactics across these CVEs. Here are key areas that require focused security measures:
- Initial Access via Public-Facing Applications: Exploiting public-facing applications (T1190) is a primary vector for initial access, with nearly half of the CVEs involving vulnerabilities in these applications. This highlights the critical need for assessing and securing external-facing components to mitigate risks.
- Lateral Movement through Remote Services: There is a notable trend of lateral movement utilizing remote services (T1210). This prevalent attack methodology indicates that attackers often exploit vulnerabilities to navigate through the network once entry is secured.
The data reveals a significant focus on vulnerabilities in public-facing applications, stressing the urgent requirement for robust external defenses. The frequent exploitation of remote services for lateral movement highlights the importance of enhancing internal network security and implementing active monitoring systems.
These insights underscore the necessity for comprehensive security strategies that safeguard against both external and internal threats.
To stay ahead in our dynamic cybersecurity landscape, the adoption of advanced threat intelligence and robust measures like QVS is essential. These tools enable proactive prioritization and response, ensuring we remain one step ahead of emerging threats.
While only a small fraction (less than a percent) of reported vulnerabilities are weaponized, their impact is disproportionately large and potentially catastrophic. This highlights the critical need for security strategies that prioritize these high-risk vulnerabilities. Moreover, the association of these vulnerabilities with multiple threat actors and ransomware campaigns calls for heightened attention and the implementation of robust incident response strategies. Such proactive measures are essential to defend against the most severe threats.
Note that vulnerabilities added to the CISA KEV catalog adhere to the criteria established in BOD 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities.
Mid-2024’s Most Exploited Vulnerabilities in the Cybersecurity Landscape
In 2024, a select group of vulnerabilities have emerged as particularly prevalent targets for cyberattacks. These vulnerabilities highlight trending attack vectors and underline the urgent need for robust defensive strategies.
It is crucial to consider several key aspects. Firstly, the data analyzed in this report, compiled by Qualys Threat Research Unit (TRU), is rigorously anonymized to ensure that our insights cannot be traced back to specific organizations or assets, maintaining strict confidentiality and integrity. Secondly, Qualys ranks vulnerabilities based on their prevalence and impact, integrating multiple factors such as CVSS base scores, exploit code maturity, real-time threat indicators, and evidence of active exploitation, among others, for a comprehensive assessment. This Top 10 ranking reflects their current significance in the cyber threat landscape. This designation is derived from an analysis incorporating data from over 25 distinct threat intelligence sources utilized by Qualys.
| Rank | CVE | Product | Vulnerability | QVS | CVSS | CISA KEV |
| 1 | CVE-2024-21887 | Ivanti Connect and Policy Secure Web | Command Injection | 95 | 9.1 | Yes |
| 2 | CVE-2023-46805 | Ivanti Connect and Policy Secure Web | Remote Authentication Bypass | 95 | 8.2 | Yes |
| 3 | CVE-2024-21412 | Microsoft Windows | Security Feature Bypass | 95 | 8.1 | Yes |
| 4 | CVE-2024-21893 | Ivanti Connect and Policy Secure Web | Privilege Escalation | 95 | 8.2 | Yes |
| 5 | CVE-2024-3400 | Palo Alto Networks (PAN-OS) | Command Injection | 95 | 10 | Yes |
| 6 | CVE-2024-1709 | ConnectWise ScreenConnect | Authentication Bypass | 95 | 10 | Yes |
| 7 | CVE-2024-20399 | Cisco NX-OS Software | CLI Command Injection | 95 | 6.7 | Yes |
| 8 | CVE-2024-23897 | Jenkins Core | Remote Code Execution | 94 | 9.8 | No |
| 9 | CVE-2024-21762 | Fortinet FortiOS | Out-of-Bound Write | 95 | 9.8 | Yes |
| 10 | CVE-2024-38112 | Microsoft Windows | MSHTML Platform Spoofing | 95 | 7.5 | Yes |
Critical Contenders: Just Missed the Cut
While the top 10 list captures the most crucial vulnerabilities of mid-2024, a few just missed the cut but demanded attention due to their high severity and potential impact. These vulnerabilities are critical for organizations to address immediately.
- CVE-2023-22527 (Atlassian Confluence): This severe remote code execution vulnerability, with a QVS of 95 and a CVSS score of 9.8, allows attackers to run arbitrary code on affected installations.
- CVE-2023-48788 (FortiClient EMS): This SQL injection flaw, which scores a QVS of 95 and a CVSS of 9.8, poses a high risk by allowing attackers to manipulate databases and access sensitive information.
- CVE-2024-24919 (Check Point Security Gateways): This information disclosure vulnerability, although it has a slightly lower CVSS score of 8.6, and a QVS of 95, can leak sensitive data.
All of the above vulnerabilities are listed on the CISA KEV, highlighting their recognized significance, exploitation in the wild, and potential impact. While not included in the top 10, each presents a clear and present danger to network security and requires prompt attention from cybersecurity teams to mitigate risks effectively and protect sensitive systems.
Have you ever wondered why, even though it’s 2024, we still see CVE identifiers from 2023, like CVE-2023-22527? Contrary to what you might expect, the year in a CVE identifier doesn’t necessarily mark when the vulnerability was discovered or made public. Instead, it pinpoints when the CVE ID was initially requested or assigned. This timing can sometimes extend beyond the calendar year.
Conclusion
In today’s complex cybersecurity landscape, stakeholders must deploy comprehensive vulnerability management programs that effectively prioritize threats.
Qualys exemplifies leadership in this domain, having recently surpassed the significant milestone of covering over 100,000 CVEs. Notably, Qualys leads the industry with a detection coverage of 98.7% for CISA’s KEV catalog—the highest in the industry—which is indispensable for effective risk prioritization, resource allocation, and compliance. Adopting a hybrid vulnerability management strategy that combines agent-based and agent-less methods, including network, external, and passive scans, is crucial. This approach is particularly pertinent given that 21.74% of CVEs in the CISA KEV catalog are actively exploited on network and perimeter devices, underscoring the need for a comprehensive security posture to effectively identify and mitigate vulnerabilities.
Organizations must ensure regular updates, diligent patch management, and advanced threat detection systems are in place to mitigate the risks associated with high-critical vulnerabilities.
We strongly recommend that organizations conduct risk assessments and adopt a comprehensive approach to vulnerability management. Prioritize addressing vulnerabilities actively exploited in the wild (such as CISA KEV), those with a high likelihood of exploitation, and those for which weaponized exploit code is available. To explore our comprehensive scanning solutions and prioritize handling high-risk vulnerabilities, sign up for a no-cost VMDR trial to explore our comprehensive scanning solutions.
Our study identifies public-facing applications and remote services as key risk areas. To ensure their safety, it is crucial to inventory and secure these against high-risk vulnerabilities. Join our CSAM trial today to enhance your public interfaces’ security.
Come meet us at Qualys booth #1320 at Black Hat USA next week.