Discover Gentoo Linux Vulnerabilities using Qualys VMDR

The Qualys vulnerability signatures team has released a new series of signatures (detections) for Gentoo Linux, allowing security teams to identify Gentoo Linux hosts and detect their vulnerabilities.
Gentoo Linux is a Linux distribution built using the Portage package management system. It is a free operating system based on Linux, and its source code is compiled locally according to the user’s preferences and can be automatically optimized and customized for various applications.
The newly released set of 20 signatures (QIDs) covers the most recent 2020 Gentoo Linux advisories. Qualys plans to release more QIDs covering the rest of the 2020 advisories later this quarter, followed by QIDs for previous years’ advisories in the coming months.
Security teams should use Qualys Vulnerability Management, Detection and Response (VMDR) to discover, assess, prioritize, and patch critical vulnerabilities in real time, including for Gentoo Linux, as part of your security and compliance programs.
Identify Gentoo Linux Assets & Vulnerabilities
Qualys VMDR enables easy identification of Gentoo Linux systems:
operatingSystem: "Gentoo Linux"
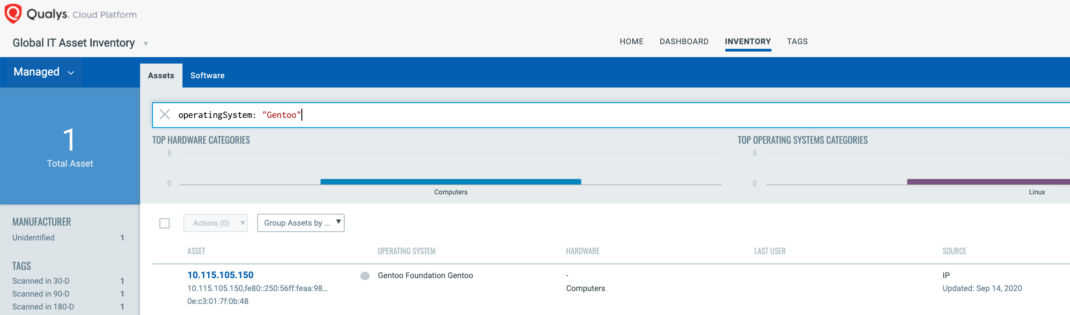
Once the hosts are identified, they can be grouped together with a ‘dynamic tag’, let’s say – “Gentoo Linux”. This helps in automatically grouping existing Gentoo Linux hosts as well as any new host that spins up in your environment. Tagging makes these grouped assets available for querying, reporting and management throughout the Qualys Cloud Platform.
In order to identify Gentoo Linux hosts and detect their vulnerabilities, Qualys recommends running an authenticated scan using a Qualys scanner.
Gentoo Linux QIDs are included in signature version VULNSIGS-2.4.976-2 and above.
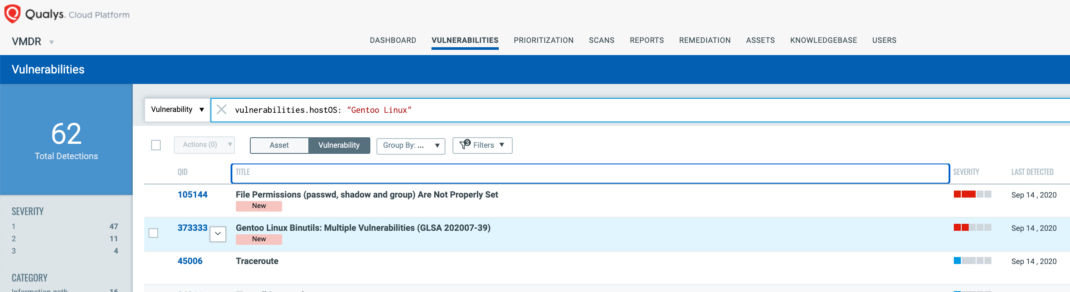
Customers can search for all Gentoo Linux vulnerabilities using the following QQL query :
vulnerabilities.hostOS:”Gentoo Linux”
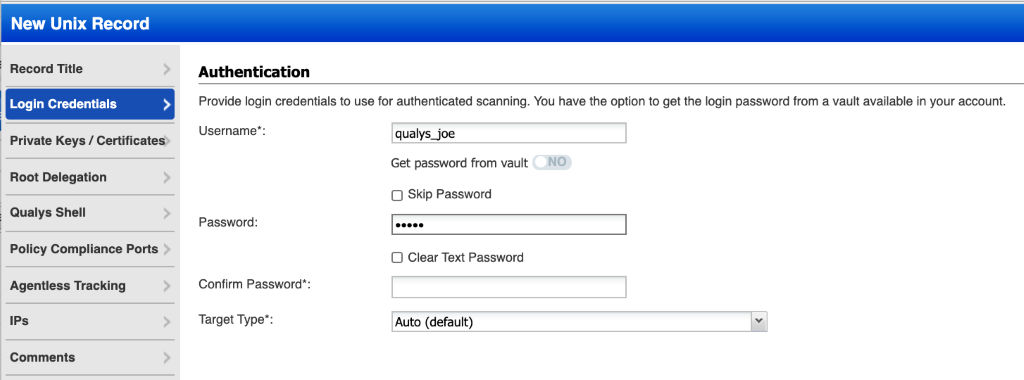
Configure Unix Authentication Record
Authenticated scanning should be configured via a standard Unix auth record, which is similar to auth records for other Linux OSes, like Redhat, Ubuntu, and others.
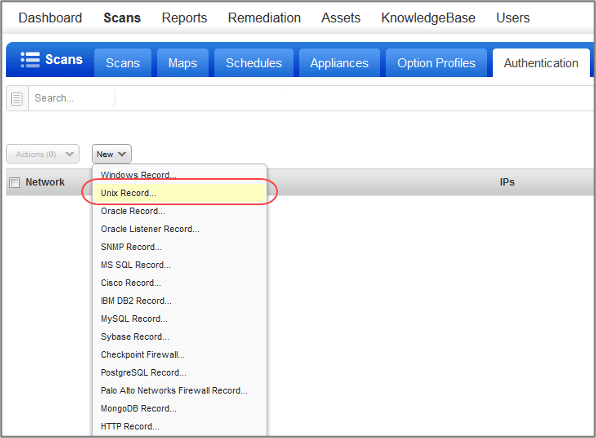
As seen below, simply go to :
Scans -> Authentication -> New > Unix Record.
Enter the Unix login credentials (user name, password) that the Qualys service should use to log in to Unix hosts at scan time. Target Type is “Auto” for Linux OS distributions. Online help is always available to assist you.
Scan Gentoo Linux Hosts
Scanning for Gentoo Linux vulnerabilities does not require root privileges; however, the account must be able to perform following commands:
1) execute “uname” to detect the platform for packages,
2) read “/etc/os-release” and “/etc/system-release-cpe”, and execute “qlist -IvC” commands
Scan reports identify Gentoo Linux as:
Qualys VMDR automatically detects new Gentoo Linux vulnerabilities as their associated detections (QIDs) are added to the KnowledgeBase. As with all detections, Gentoo Linux QIDs contain recommended steps to address the vulnerability.