Expand Your Vulnerability & Patch Management Program to Mobile Devices with Qualys VMDR

As mobile devices have become ubiquitous in almost every business process, whether in bank branches, manufacturing sites or retail stores, they are now hosting business applications and data that is subject to regulatory compliance and security. With access to critical corporate resources inside the corporate network, these mobile devices have become critical assets for the organization.
Mobile Attack Surface Challenges
Alongside this trend, there has been a drastic rise in Android, iOS, and iPadOS vulnerabilities and an increased number of vulnerable apps distributed from authorized app stores. Through these vectors, mobile devices have become preferred targets for attackers to gain an entry point into corporate networks. Last year, for example, 900 million Apple iOS users were affected by iOS mail app vulnerability CVE-2020-9819 and CVE-2020-9818 exploit. Zecops demonstrated how to exploit these vulnerabilities (MailDemon) by sending oversized email to victims’ devices.
In another attack, Android mobile devices were targeted using the Google Chrome app vulnerability CVE-2020-6418, a type of bug that incorrectly implements relevant security checks. The attacker tricked victims into visiting a specially crafted web page that gave the attacker an initial foothold on the victim’s device via their browser. The attacker then deployed OS-level vulnerability CVE-2019-2215 to gain privileged control of the victim’s device including access to their data and the corporate network.
In both cases, the attacks were successful because the organizations were using a traditional vulnerability scanning approach for mobile devices. This approach fails to provide holistic security for mobile devices because it requires devices to connect to the VPN or the organization’s network in order to be scanned for vulnerabilities or patched. Mobile Device Management (MDM) also fails in this case because its ‘policy-based prevention’ does not assess devices or the apps running on them for the latest vulnerabilities, and it lacks knowledge of the security posture of the device and does not provide flexible patching.
Organizations are looking for a solution which provides continuous visibility into mobile devices across the enterprise, continuous visibility into the vulnerability and misconfiguration posture of the device and apps, and a workflow for prioritized updates and patching.
Introducing Qualys VMDR for Mobile Devices
Built on the FedRAMP-authorized Qualys Cloud Platform, Qualys VMDR for Mobile Devices extends vulnerability management, detection and response capabilities to mobile device platforms such as Android, iOS, and iPadOS. Qualys Cloud Agent for Android, iOS and iPadOS, available on Google Play Store and Apple App Store, provides continuous visibility, security and patch orchestration for your mobile platforms.
To learn more about this solution, watch the webinar on March 10: Seamlessly Expand Vulnerability & Patch Management to Enterprise Mobile Devices.
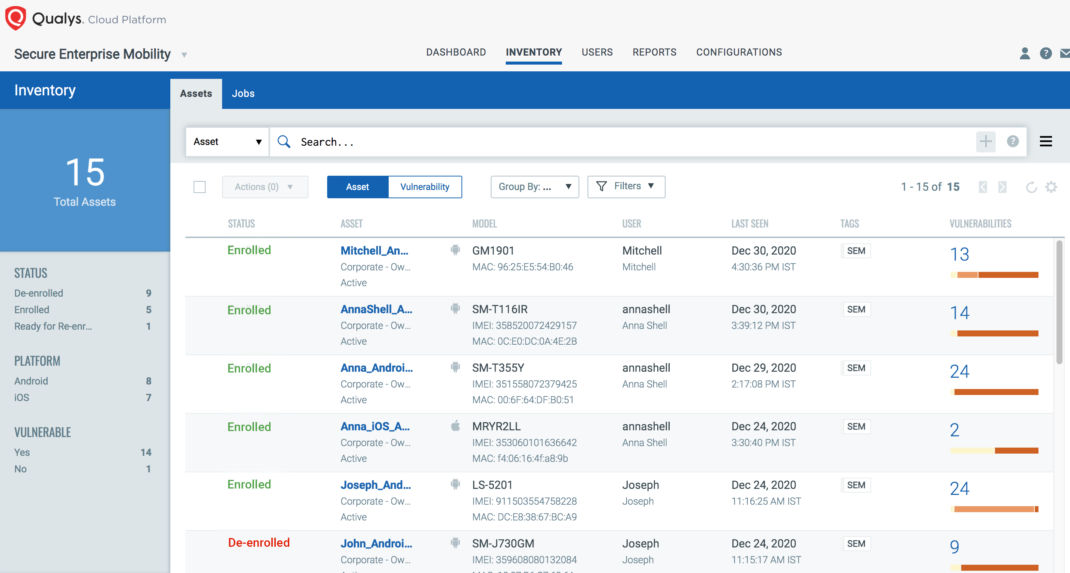
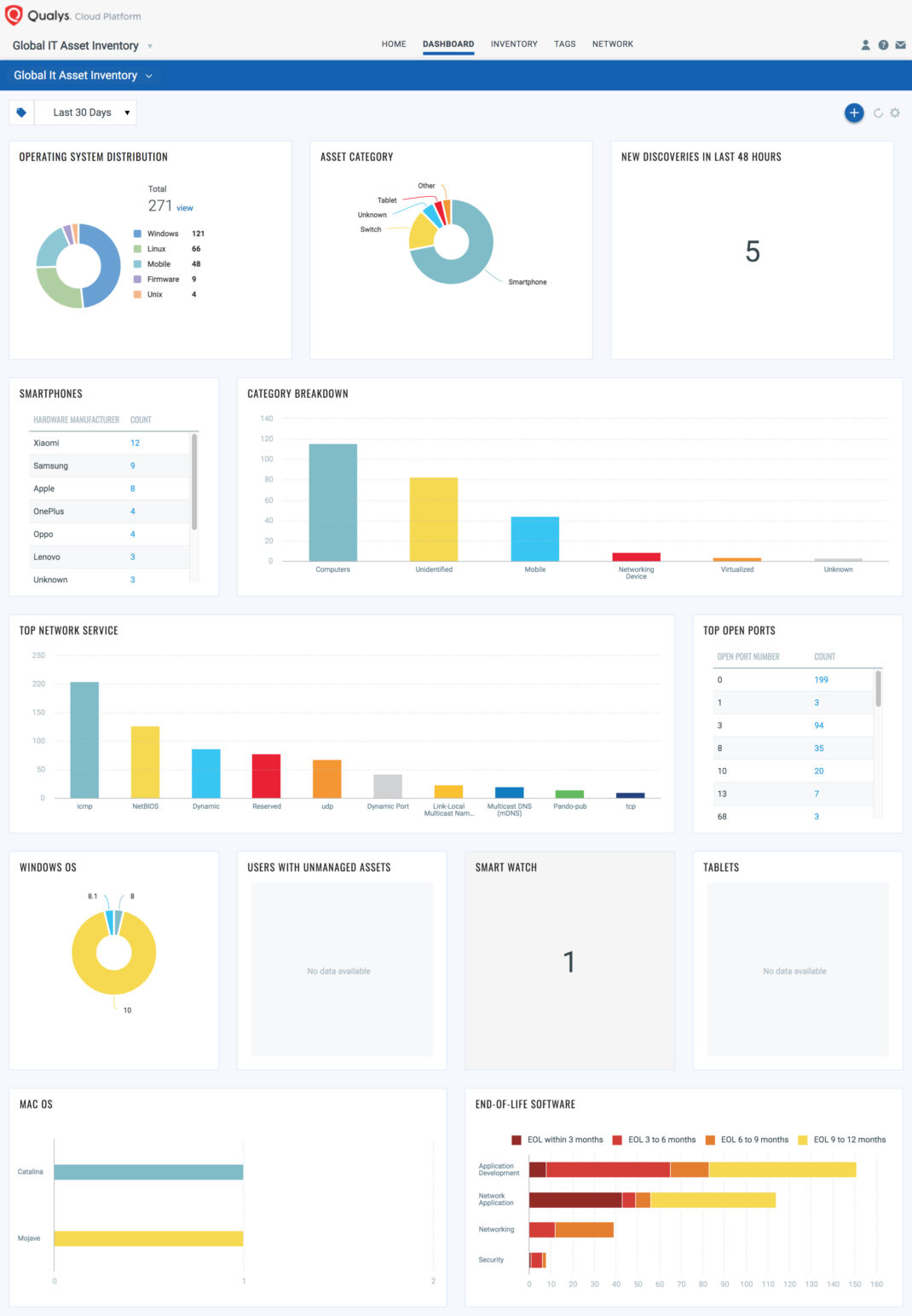
Continuous Visibility and Monitoring of Mobile Devices Connecting to Your Network
Knowing your mobile devices and monitoring their connections to your corporate network is fundamental to their security. With cloud agents deployed on your mobile devices, you get real-time visibility of all the mobile devices across your enterprise, including critical hardware and software details like firmware, OS, and installed applications details, along with location and the network information.
This mobile device inventory comes as a part of Qualys VMDR and Multi-Vector EDR.
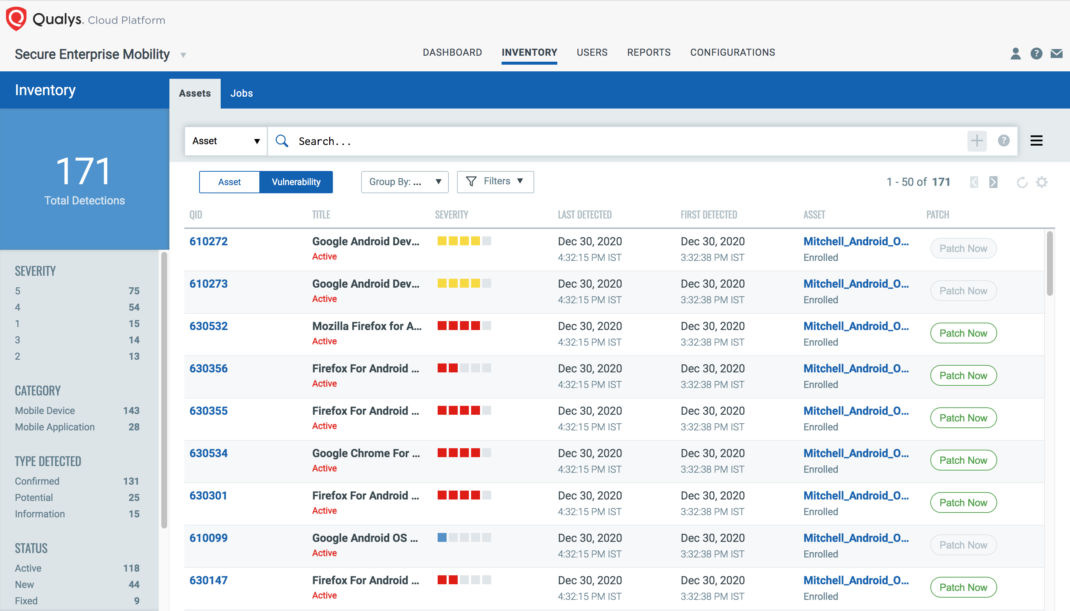
Real-Time Visibility into Vulnerabilities and Critical Device Settings
With best-in-class vulnerability assessment for Android, iOS and iPadOS devices, Qualys VMDR for Mobile Devices enables:
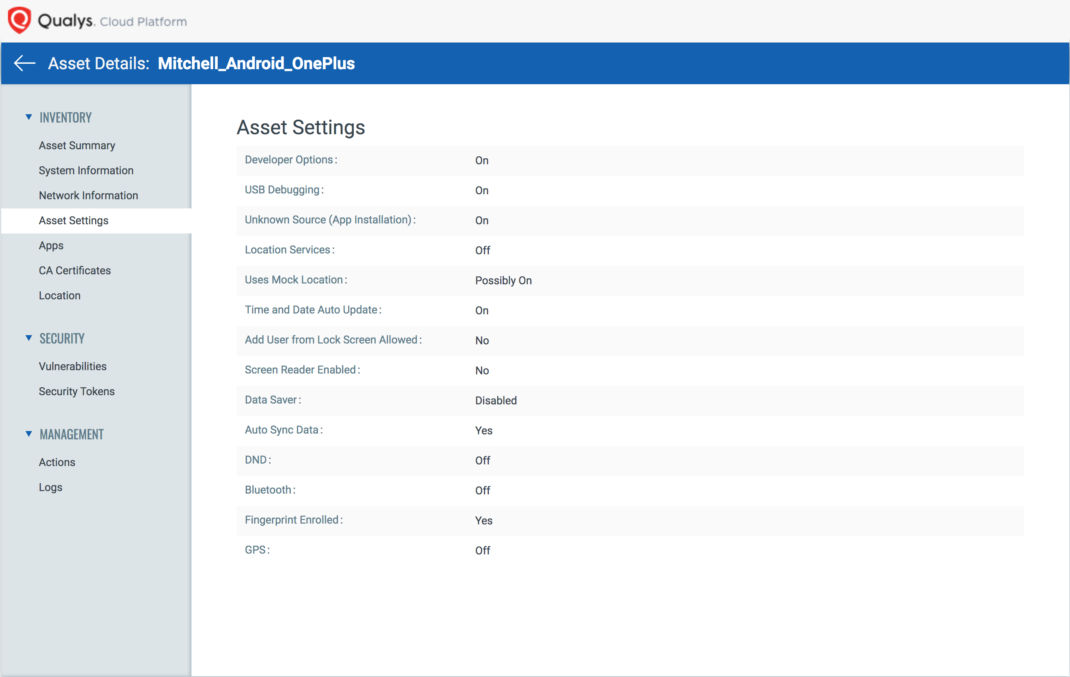
- Device vulnerability and exploit assessment covering vulnerabilities from 2016 to the latest for Android, iOS, and iPadOS providing insights into vulnerable OS versions with CVE details and detection of jailbroken/rooted devices,
- Detection of critical device settings such as encryption disabled, password removed/disabled, Bluetooth settings, etc.,
- Assessment of app vulnerability detections covering vulnerabilities from 2016 to the latest such as Google Chrome browser vulnerabilities, along with the detection of potentially harmful apps, and
- Insights into network vulnerabilities and detection of devices connected to insecure or open Wi-Fi networks.
Qualys VMDR helps expand your vulnerability management program with configuration assessment by continuously monitoring the critical mobile device configurations as recommended by National Security Agency (NSA) best practices, such as Bluetooth status, location services, app trusted status, and more.
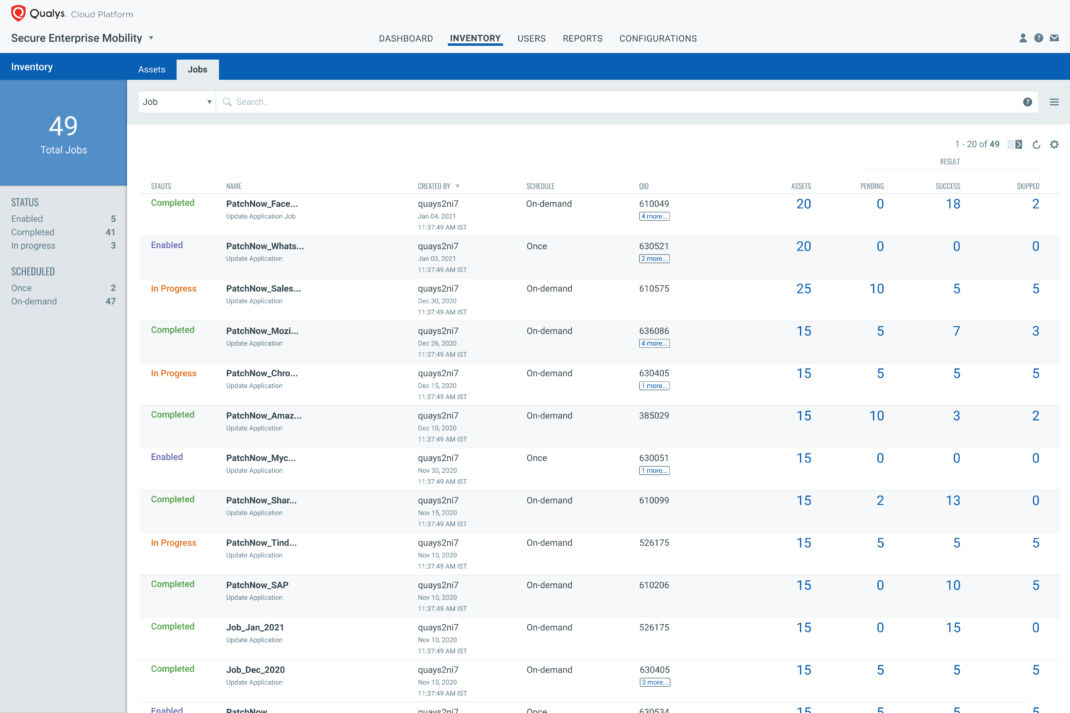
Remote Response and Seamless Patch Orchestration
Two of the biggest response challenges in the mobile world are:
- Performing remote actions when the mobile device is not on the VPN or network, i.e. when traditional vulnerability management approaches are not possible, and
- Determining the appropriate mitigation action, which requires time-consuming research to map application updates to vulnerabilities and then either deploy those updates or uninstall the risky apps.
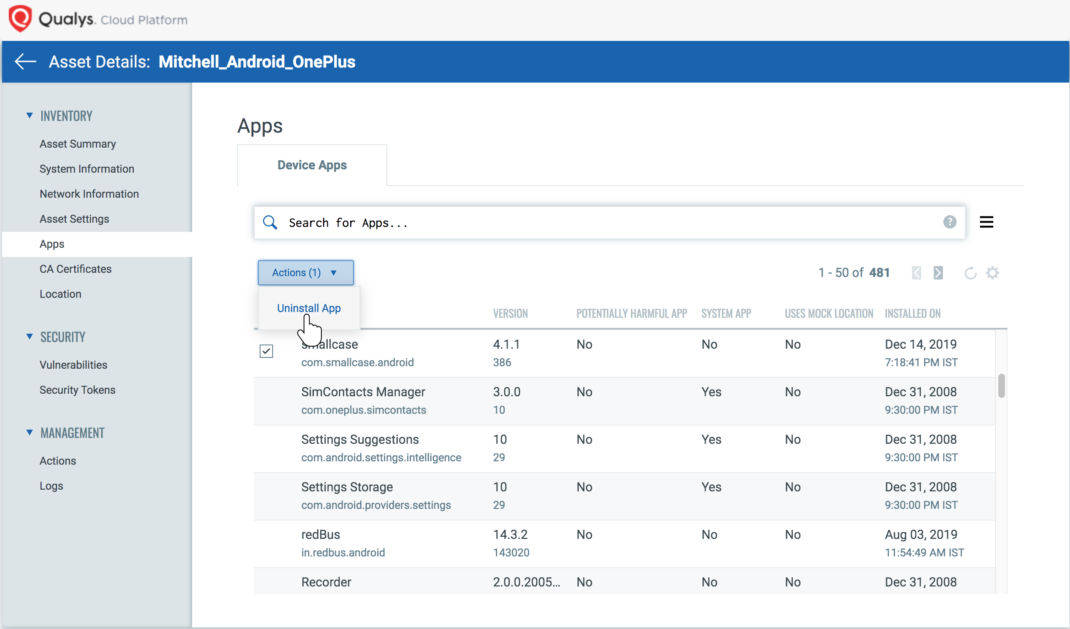
Qualys VMDR for Mobile Devices automatically and continuously correlates the vulnerabilities of Android apps available on Google Play Store with appropriate application updates, significantly decreasing your remediation response time. IT and remediation teams can schedule and deploy those patches from Google Play Store via seamless orchestration provided by VMDR or they can uninstall vulnerable apps.
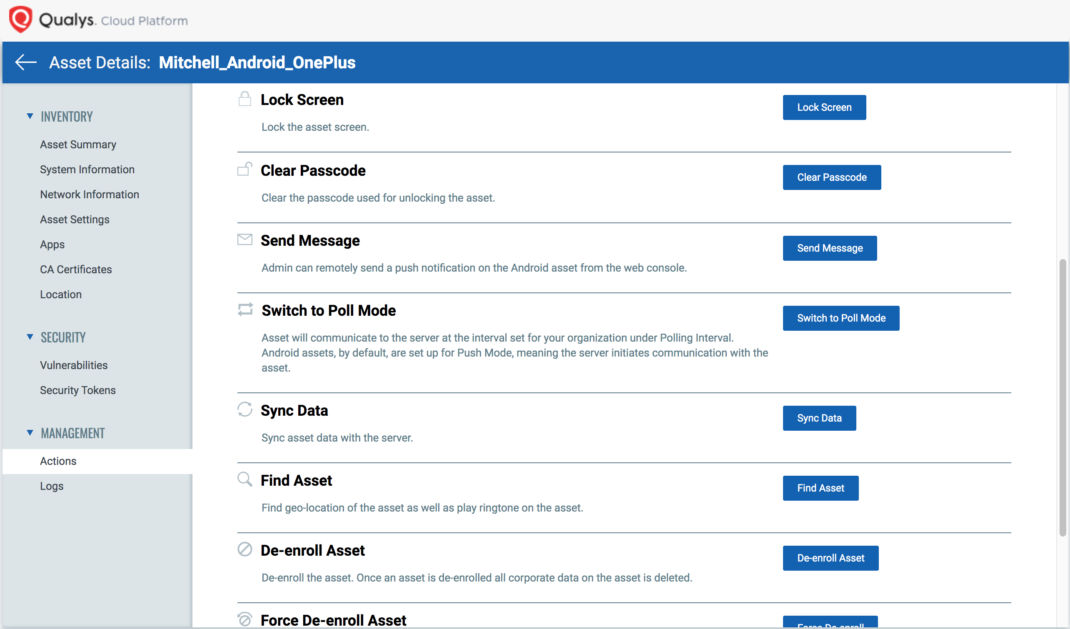
Based on the security posture of the device, security teams can take actions on all at-risk mobile devices simultaneously, even if the devices are not connected to the VPN or corporate network, leveraging over-the-air, out-of-the-box controls to reset in critical cases or lock devices, change passcodes, or even de-enroll the device.
Vulnerability Posture of Mobile Devices AND Servers in a Single Pane of Glass
One of the key metrics for vulnerability risk management teams and management is visualization of vulnerability and security posture across hybrid environments, from datacenter servers to endpoints to mobile devices. With mobile data flowing to the Qualys Cloud Platform via VMDR for Mobile Devices, your vulnerability and security teams can continuously inventory all your assets, including mobile devices, in a consolidated manner and gain insights into the vulnerability and misconfiguration posture of your servers and mobile devices in a single pane of glass.
Visibility, Assessment, Correlation and Orchestration
With the growth of mobile devices, increasing attack surface and data exposure risks, security teams are looking for a solution which goes beyond traditional mobile vulnerability scanning tools. Qualys VMDR for Mobile Devices extends the power of vulnerability & patch management to Android, iOS and iPadOS devices for:
- Compressive visibility into mobile devices, installed apps, and configurations, even if they are not on VPN or network,
- Continuous vulnerability and end-of-life assessment of devices, OSs, and applications along with monitoring for potential harmful applications,
- Automatic correlation of vulnerabilities with apps and Android patches, and
- Orchestration of appropriate response actions such as deploying patches from Google Play Store or uninstalling vulnerable apps.