TruConfirm: Autonomous, Agent-Led, Safe Exploit Validation for Real-World Risk Reduction

Table of Contents
- Key Takeaways
- The Question CISOs Cannot Answer Today
- The Certainty Problem in Modern Vulnerability Management
- Introducing TruConfirm: Agent-led, Safe Exploit Validation, PoweredByProof
- Agent Val: Operationalizing Continuous Validation
- The Operational Impact From Millions of Findings to the Few That Matter
- CTEM Needs Validation Qualys ETM Delivers It
- How TruConfirm Confirms Real-World Exploitability
- Coverage That Matches the Modern Attack Surface
- A Shift in Risk Operations: From We Think to We Know
- The End of Vulnerability Guesswork
Key Takeaways
- CISOs still can’t answer the only question that matters: Is this exposure exploitable on this asset, in our production environment, against our controls, right now?
- The vulnerability firehose broke the old model: With 48,177 CVEs published in 2025, “critical” lists are too large to fix, so the real job is separating actionable risk from noise.
- Most programs run on probability, not proof: Version-to-CVE mapping and CVSS-heavy prioritization produce “likely important” work, but don’t confirm reachability, exploitability, or control effectiveness in production.
- That mismatch wastes scarce engineering cycles: Teams patch issues that can’t be exploited, argue over scores, and still miss real, reachable attack paths that persist in the backlog.
- ETM closes the certainty gap with validation at scale: TruConfirm, embedded in Qualys ETM, provides agent-led, production-safe exploit validation, and Agent Val orchestrates what to validate next, then turns confirmed results into TruRisk-driven actions inside the Risk Operations Center.
The Question CISOs Cannot Answer Today
The scan is done. Dashboards are full. Change windows are tight. And one critical question dominates every vulnerability review: “Is this exposure actually exploitable on our asset, in our production environment,with our controls, right now?”
Volume is no longer an anomaly. In 2025, a staggering 48,177 CVEs were published. Most organizations now face thousands – often tens of thousands – of vulnerabilities labeled as “critical.” No security team has the resources to fix all of them. The real challenge is deciding which risks actually require action – and which are already mitigated by existing controls or simply not exploitable.
Most programs can inventory vulnerabilities and assign severity. Far fewer can answer the question CISOs actually care about: which of these will work against us – and which we can safely deprioritize.
Qualys TRU analysis shows that only 1% of reported CVEs are ever weaponized, yet remediation effort continues to be spread across the remaining 99%. High scores still dominate decision-making, even though severity does not equal exploitability, and theoretical risk continues to consume real engineering time and budget.
Attackers do not exploit CVEs. They exploit reachable code paths in live environments. They test whether a service is exposed, whether authentication can be bypassed, and whether deployed controls actually stop execution. Until exploitability is proven, teams debate, patch broadly, debate endlessly, and still miss the paths that matter most. This is not a visibility problem. It is a certainty problem.
The Certainty Problem in Modern Vulnerability Management
Most vulnerability programs still rely on a fragile chain of static signals rather than evidence – a software version maps to a CVE, a score implies likelihood, a ticket implies risk reduction. That logic collapses on an enterprise scale.
Even “risk-based prioritization” remains probabilistic. It helps narrow the focus, but it still produces a list of theoretically important risks, not proof that any exposures are actually exploitable or not already mitigated in production. At scale, no amount of prioritization can resolve risk on its own because prioritization ranks assumptions, while production environments demand proof.
- “Potentially vulnerable” becomes the unit of work. Version-based detection answers “is the component present?” It does not answer “can an attacker reach and exploit it in our environment?”Presence, reachability, exploitability, and control effectiveness are treated as the same problem, even though they are not.
- Scores flatten reality. CVSS and other scoring models summarize probabilities and emphasizetheoretical scores that may not be relevant to every organization. They cannot account for network routes, authentication state, runtime behavior, compensating controls, or deployment drift across clusters and clouds. A high score often triggers urgency, but still leaves teams guessing whether the exposure can succeed in their environment.
- Controls stay unverified. Scanners and scoring engines rarely validate whether WAF rules, firewall policies, segmentation, or EDR already block exploitation. Scanning alone can identify what exists, but it cannot determine which exposures will actually succeed against production assets and deployed controls. Scanning can identify what exists, but it cannot determine which risks are already mitigated versus which remain actionable.
- Breach and Attack Simulation (BAS) and attack path tools attempt to close this gap, but they often rely on simulated conditions, pre-determined paths, or non-production environments. In practice, they add tools, integrations, and operational overhead without delivering evidence-based validation of exploitability in live production systems.
The result is predictable. Teams waste scarce remediation resources fixing issues that cannot be exploited, while quieter but real exposures remain buried in the backlog. Engineering fatigue sets in. MTTR slows as teams debate what is “real.” Reprioritization becomes constant. And the risks that attackers can actually exploit persist.
When exploit speed outpaces decision speed, theoretical prioritization breaks down.
Introducing TruConfirm: Agent-led, Safe Exploit Validation, Powered By Proof
ETM introduces an agent-led risk operations model that shifts exposure management from theoretical risk to safe exploit validation with proof.
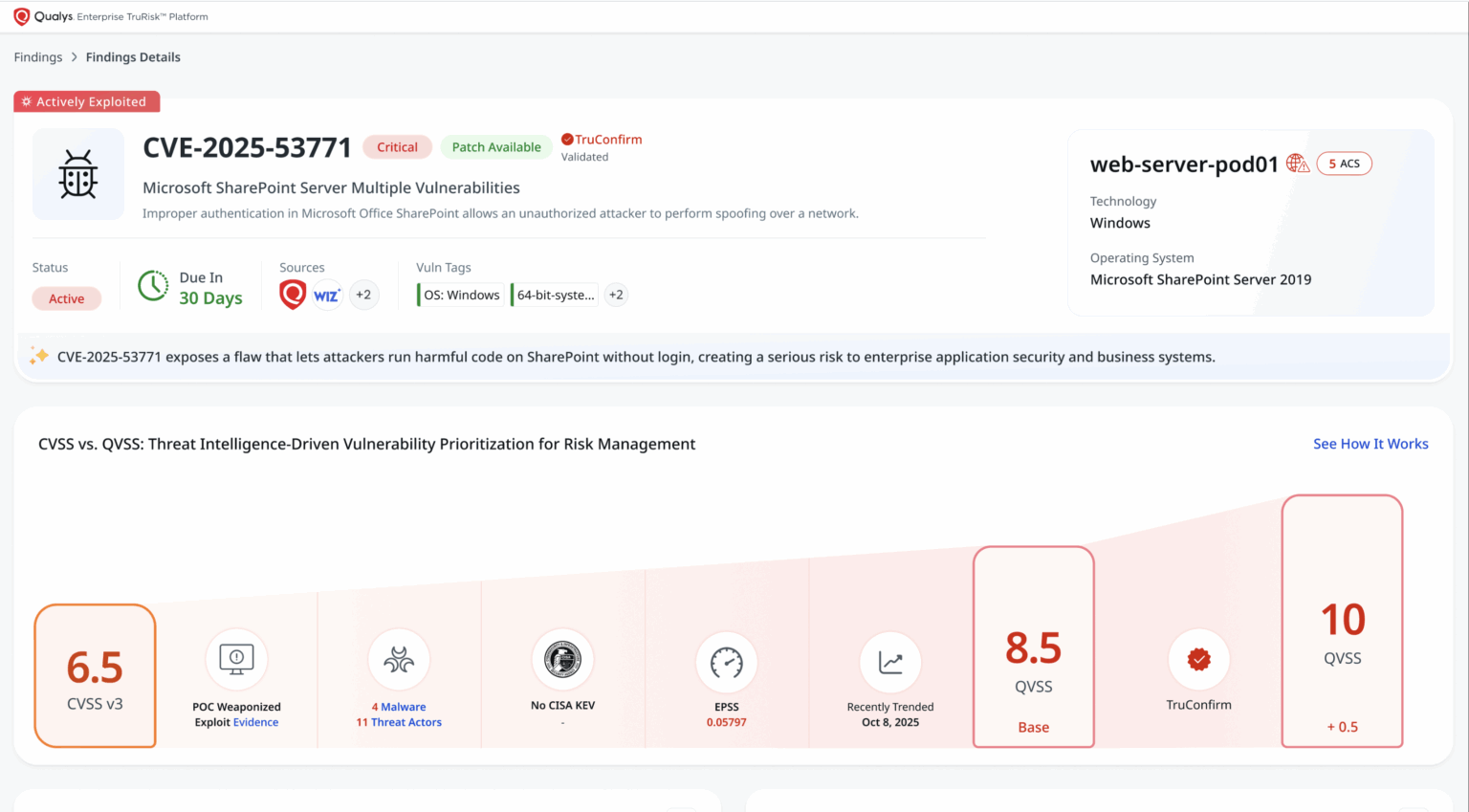
TruConfirm, an exposure validation service natively embedded in Qualys ETM, provides deterministic, production-safe evidence that shows whether an exposure can be exploited or is already blocked by existing controls. Agent Val continuously decides which high-risk exposures to validate next, safely orchestrates validation in production, and turns confirmed results into action inside the Risk Operations Center.
Agent Val becomes the central orchestration layer for exploit validation, continuously deciding what to validate, safely orchestrating TruConfirm execution, and driving confirmed results directly into risk operations. TruConfirm extends ETM with production-safe, evidence-based exploit validation.
Together, TruConfirm & Agent Val deliver “ground truth” by proving whether an exploit path executes – or is blocked – on real assets, against real security controls, in an organization’s live production environment. This proof is what enables ETM to move from theoretical prioritization to evidence-driven, continuously executed risk reduction, without adding tools, agents, or operational friction.
- Production-safe, deterministic validation – Teams relying on version-based scanners or traditional Breach and Attack Simulation (BAS) tools are often forced to work from assumptions. BAS tools typically run on golden images or simulated attack paths that rarely reflect the complexity of real production environments. Orchestrated by Agent Val, TruConfirm performs active validation directly on live assets. It uses a safety-first architecture with pre-tested, benign payloads including cryptographic proof-of-execution and silent out-of-band callbacks. This confirms exploitability without disrupting operations, installing agents, or exposing sensitive data. With validation tightly coupled to ETM’s risk model, results are immediately actionable.
- Validation that directly drives ETM risk decisions – TruConfirm is a core service within ETM’s risk engine. ETM aggregates asset and exposure data from Qualys and third-party sources. Using ETM’s risk context (threat intelligence, business context, and control awareness), Agent Val identifies high-risk exposures and orchestrates TruConfirm to validate whether they are truly exploitable.
Once exploitability is confirmed, ETM automatically amplifies the associated TruRisk™ score, generates risk-reduction recommendations tied to specific assets, business entities, and attacker activity, including ransomware-linked and CISA KEV exposures.
ETM then verifies outcomes and feeds results back into Agent Val, enabling continuous prioritization, faster mobilization, and verified TruRisk reduction within a single operating model. - Evidence-based validation of security control effectiveness – Many tools return a binary verdict: exploitable or not. TruConfirm goes further by capturing evidence that explains why an exploit attempt succeeded or failed. When validation is blocked, ETM records the exact defensive layer responsible, such as a WAF rule, firewall policy, network segmentation control, or EDR. When exploit paths are open, results flow directly into ETM workflows as prioritized tasks and mitigation plans. Teams can mobilize faster, reduce CAB friction with proof, and track projected TruRisk reduction tied to planned and completed actions.
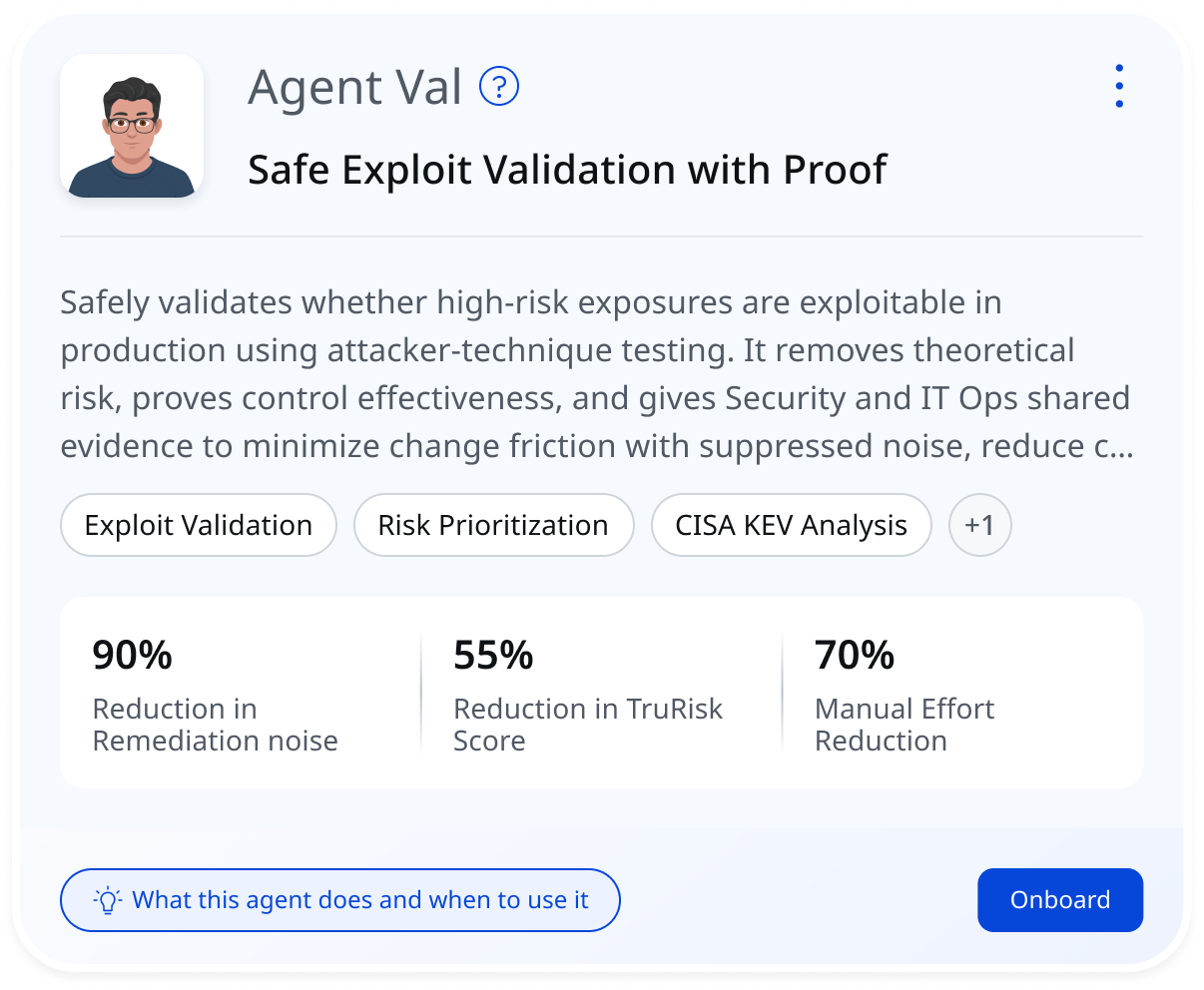
Agent Val: Operationalizing Continuous Validation
Exploit validation only becomes valuable when it runs continuously, safely, and in context. That is where most approaches break down. They either stop at prioritization or rely on point-in-time testing that cannot keep up with changing environments.
Agent Val closes that gap.
Agent Val is an agentic AI-led workflow inside Qualys Enterprise TruRisk Management (ETM) that operationalizes exploit validation as a continuous process. It sits on top of ETM’s risk graph and acts as a decision engine that determines what should be validated, when, and why.
Instead of treating validation as a manual step, Agent Val turns it into an always-on loop.
- It starts with risk-aware orchestration. Agent Val continuously evaluates exposures using business context, asset criticality, threat intelligence, and attacker relevance, including signals such as KEV and active ransomware campaigns. It selects which exposures deserve validation first based on real-world exploit likelihood and potential business impact.
- Once a target is selected, Agent Val orchestrates production-safe validation through TruConfirm. TruConfirm uses controlled, non-destructive techniques to prove whether a vulnerability is exploitable on the live asset.
- For internal assets, Agent Val incorporates runtime context using Cloud Agent telemetry. It distinguishes between a vulnerable component being present and an exploit path being reachable in that specific environment.
- When validation runs, Agent Val captures evidence of control effectiveness. If exploitation fails, ETM records the defensive layer responsible, turning validation into a form of continuous control verification tied to real attack paths.
- When exploitability is confirmed, Agent Val feeds the result back into ETM to amplify risk and drive decisions. TruRisk scores are updated, and targeted, asset-specific remediation recommendations are generated.
- Agent Val then moves into guided mitigation. It surfaces the most effective remediation options for each validated exposure, including patches, configuration changes, and compensating controls – tailored to the asset, operating system, and environment, reducing the need for manual interpretation and coordination across teams.
- Finally, Agent Val completes the loop with revalidation. After a fix is applied, it re-tests the same exploit path using TruConfirm to confirm the exposure is truly closed and ensures that validated risks do not re-enter the backlog due to incomplete fixes.
This end-to-end motion changes how validation operates. The result is a continuous, context-aware workflow that connects detection, proof, remediation, and verification inside a single system.
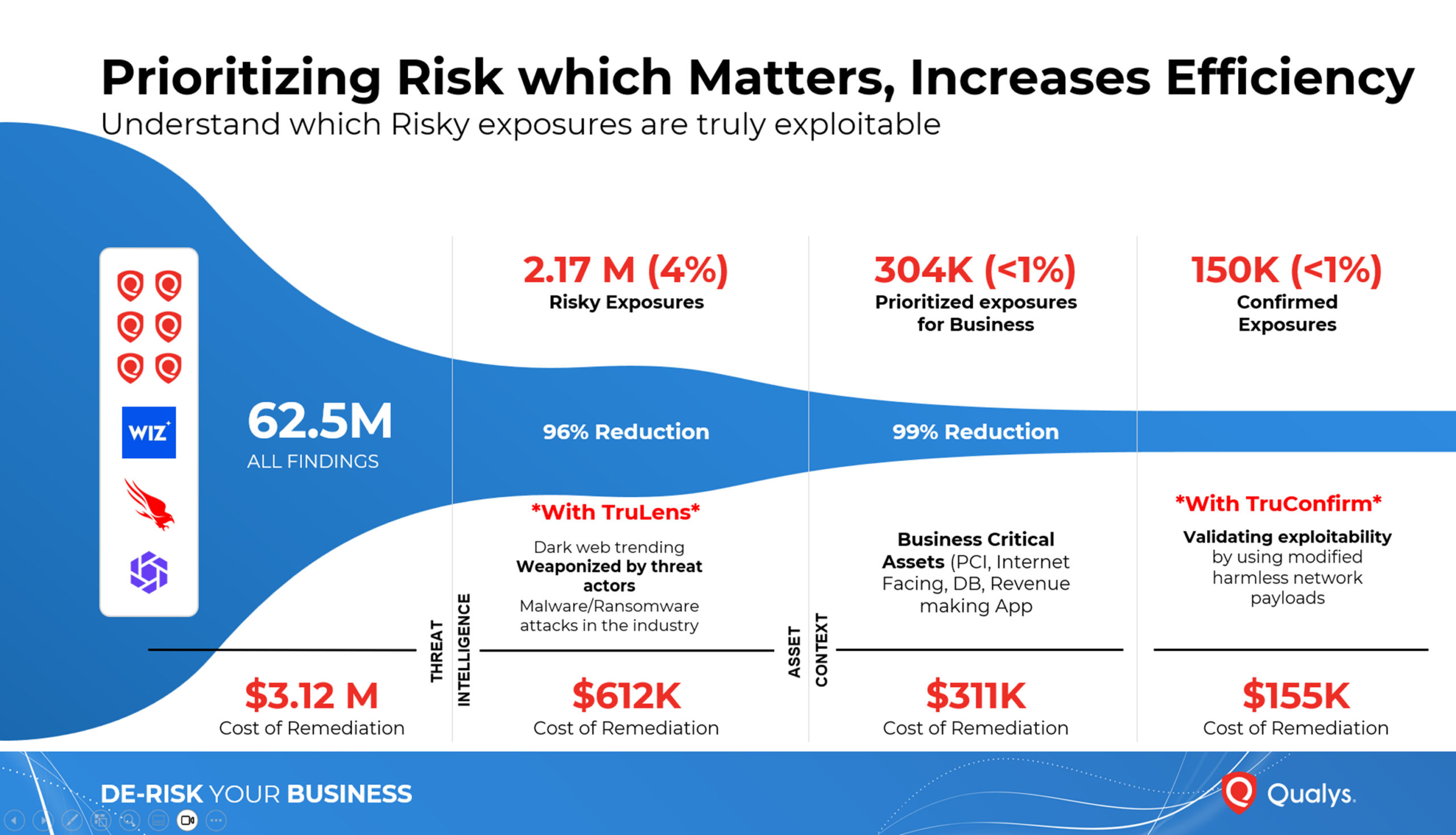
The Operational Impact – From Millions of Findings to the Few That Matter
ETM integrates TruConfirm into how vulnerability and risk teams already operate:
- Builds on the existing Qualys sensor footprint – No new sensors or architectural redesign
- Unified exposure backlog – ETM aggregates Qualys and third-party signals; TruConfirm validates within that backlog
- Focused validation – ETM targets weaponized, high-impact exposures that truly increase incident likelihood
- Evidence capture – Confirms exploitation or documents effective controls
- Risk elevation and mobilization – Validated risks flow into ETM workflows for prioritized action
- Closed-loop remediation – ETM orchestrates fixes and verifies outcomes
Download the whitepaper to learn how Qualys ETM uses validation to close real attack paths.
CTEM Needs Validation – Qualys ETM Delivers It
CTEM does not succeed on prioritization alone. Validation is a required phase.
With TruConfirm embedded inside Qualys Enterprise TruRisk Management, ETM operationalizes all five CTEM phases – discovery, scoping, prioritization, validation, and mobilization – within a single, unified Risk Operations Center. This is what turns exposure management from measuring risk into eliminating real attack paths with evidence.
How TruConfirm Confirms Real-World Exploitability
Attackers focus on execution. ETM uses TruConfirm’s multi-modal validation methods to substantiate exploit paths using the least risky interaction that still produces defensible proof. No single method fits every exploit pattern – some yield outputs while others are intentionally blind. TruConfirm uses the least risky interaction that still provides defensible evidence.
| Direct Response Validation | Sends a benign payload and evaluates execution for auditable proof. |
| Cryptographic Execution Proof | Uses unique hashes to mathematically confirm code execution, eliminating spoofing. |
| Out-of-Band Confirmation | Validates blind exploits via controlled callbacks— if a response is received, it’s exploitable; if absent, it’s not. |
Coverage That Matches the Modern Attack Surface
TruConfirm substantiates exploitability in areas where attackers are most active – web stacks, enterprise apps, network edge, cloud environments, and Internet of Things (IoT) devices. It focuses validation on 1,600+ weaponized CVEs, covering the threats that actually matter. Given that very few published CVEs are ever exploited in the wild, our coverage targets the attacks most likely to hit your environment, not the majority that never will.
A Shift in Risk Operations: From “We Think” to “We Know”
Most exposure programs tend to plateau at the reporting stage, often delivering basic counts, trends, and visual heatmaps without demonstrating tangible reductions in risk. This reflects a maturity curve that transitions from merely measuring exposure to actively eliminating paths that attackers could exploit.
TruConfirm advances this maturity curve by transforming exploitability assessments into concrete evidence. Instead of relying on probabilistic assessments like “What if,” it enables organizations to operate with confidence, using validated data that ties directly to their assets. This information is actionable for change control and incident prevention, thus enhancing operational certainty.
Such clarity serves as a powerful control mechanism, reducing unnecessary debate, streamlining prioritization cycles, and allowing ROC teams to work from a unified source of truth rather than competing viewpoints.
The End of Vulnerability Guesswork
The industry must move beyond assumptions. The volume of threats is increasing, exploit timelines are shortening, and the term “critical” has become little more than a label rather than a decision-making tool. It’s imperative that proof becomes the standard for managing exposure.
Proof enables three vital advantages probability cannot match: (1) a defensible answer to the question of “is this exploitable now?”, (2) faster action by removing the need for debate, and (3) evidence artifacts that withstand audit, change control reviews, and board reporting.
This is why TruConfirm is a game-changer. By incorporating automated exploit validation into Enterprise TruRisk Management, TruConfirm empowers risk operations to prioritize actions based on the actual threat landscape – focusing on execution and reachable paths rather than relying on conjecture.
Qualys ETM is available now. TruConfirm is delivered as a core capability within ETM and is planned to be generally available by H1 2026.
Himanshu, from a high level perspective, is this like using AI to execute metasploit framework in check mode across the estate and in volume terms how much does this reduce workload compared with using well structured QQL to find vulnerabilities in CISA KEV or where exploit is available?