CVE-2022-42889: Detect Text4Shell via Qualys Container Security
A new critical vulnerability CVE-2022-42889 (Text4Shell) in Apache Commons Text library was reported by Alvaro Muñoz.
The vulnerability, when exploited could result in remote code execution (RCE) applied to untrusted input due to insecure interpolation defaults. As a result, this CVE is rated at CVSS v3 score of 9.8.
The affected Apache Commons Text versions are 1.5 to 1.9 and it has been patched in version 1.10. When this article is published, this CVE is not expected to be highly widespread as compared to the Log4Shell and Spring4Shell-related CVEs. The fact is that the Apache Common Text package and the use of the specific function StringSubstitutor interpolator are not widely used in production environments, causing critical concerns from the security and technology communities.
How to Detect Text4Shell Vulnerability via Qualys Container Security
Qualys Container Security provides sensors to detect image vulnerabilities from build time to runtime.
Use the Qualys Container Security sensors to detect CVE 2022-42889 with QID: 988179 in your container environments, so you can easily assess the vulnerability impacts of Text4Shell.
To see all the images impacted by these vulnerabilities, navigate to the Container Security application, go to Assets > Images, and search using the following QQL query:
vulnerabilities.qid: `988179`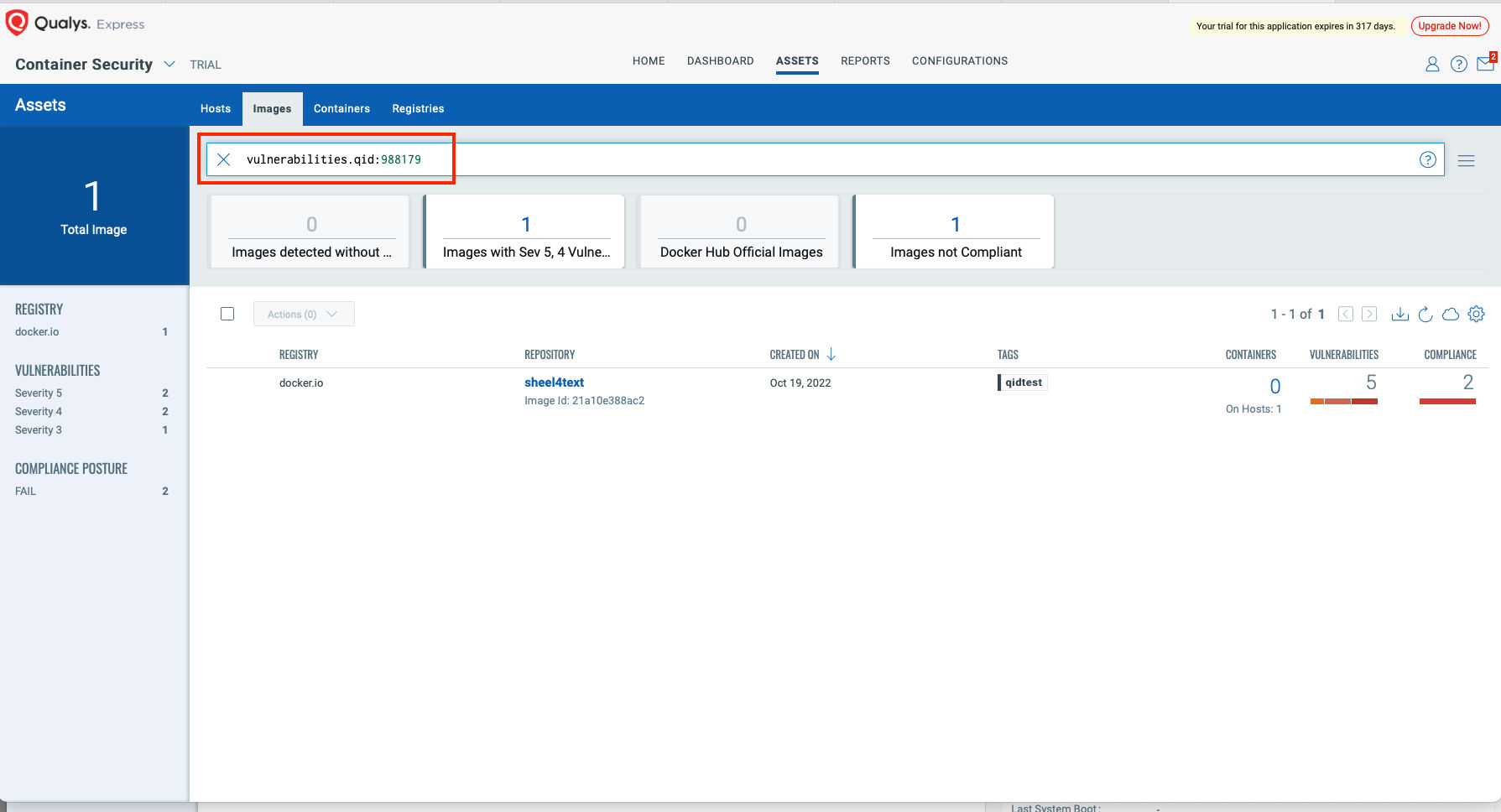
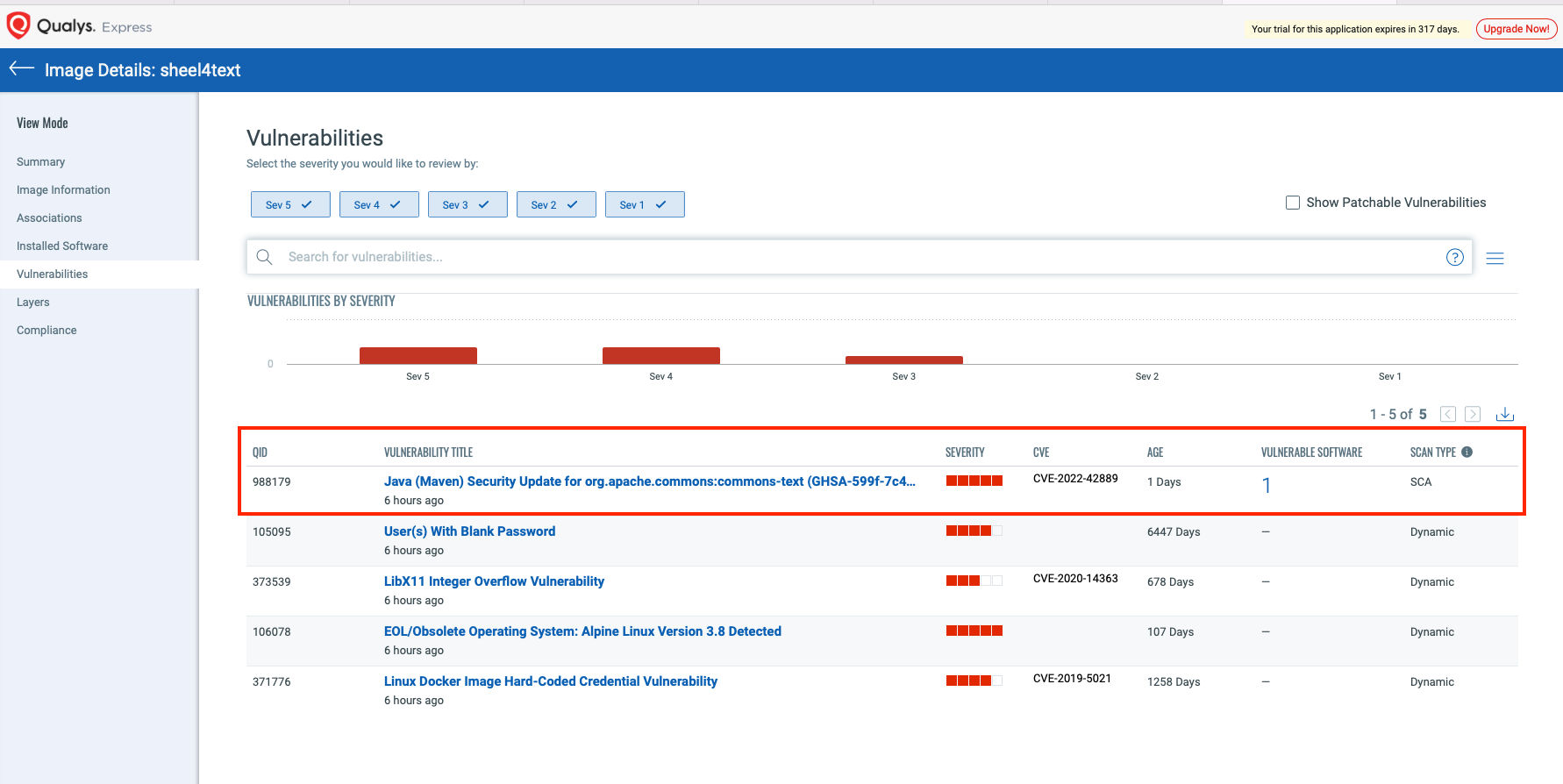
Select the image and navigate to the Vulnerabilities tab to view details of the vulnerability.
Patch the Images
Patch the detected vulnerable images as soon as possible, to mitigate potential attacks.
Qualys recommends using the latest Qualys Container Security sensors to scan for Text4Shell vulnerabilities.
Qualys Container Security offers a comprehensive solution for detecting vulnerabilities, including Text4Shell, across the entire lifecycle of the container from build time to runtime.