Top 4 Controls for a Secure PC – Part 1
At the RSA conference a few weeks ago, we introduced a new free service – the Top 4 Control audit. This service focuses on how to help computer end users and small- to medium-sized companies implement the top 4 security measures first suggested by the Australian government’s ASD division. In their internal forensics, using the four measures were able to prevent over 85% of the incidents that had occurred in the government agencies that they were responsible for. In the last year, the Top 4 controls have been starting to gain acceptance, with both the SANS Institute and the Council on CyberSecurity supporting their implementation. CSIS’s Jim Lewis gave them a very favorable mention in his 2013 paper “Raising the Bar for Cybersecurity”.
I have used our new Top 4 service on a new machine that I received recently. It was a new laptop, a Lenovo T430. It came with Windows 8.1 installed, an ideal and updated target to work with.
In essence, the Top 4 consists of:
- Whitelisting, which prevents the execution of downloaded malware, as it is not contained in the approved list of software
- Patching applications, which shrinks the attack surface in the installed applications focusing directly on the software most abused in recent months: Java, Adobe Flash, Adobe Reader , Microsoft Office and Apple Quicktime
- Patching the operating system, which fixes known vulnerabilities in Windows and further shrinks the available attack surface
- Running as a standard user, which makes it harder for malware to install itself permanently on the system, as this usually requires administrator privileges
Overall, it is a small, but pretty promising set of controls to try out. Nothing better than a brand new machine to test a quick setup to see how practical the whole suggestion of running the Top 4 audit really is.
When I first booted up my new machine, I was prompted to use my Hotmail account at Microsoft, but I opted to use a local account because I felt I would rather maintain a clear separation between my online and local machine accounts. (Hint, click on "Create a new account," then "Sign in without a Microsoft account.")
I proceeded to install the Top4 service plugin through the URL retrieved through my account on Qualys BrowserCheck Business Edition (http://tinyurl.com/qgbe4 or https://browsercheck.qualys.com/?uid=de39b22f468a147906fd65041b56719e). If you want to use the Top 4 service, you should really create an account in the Business Edition backend tool and get your personalized URL to get better reporting and trending on your results, but feel free to use the above URL if that is too much effort for you at the moment.
Then, after logging into Windows with the newly created user “wkandek”, I clicked on the Desktop tile and started Internet Explorer on the familiar desktop interface and went to the URL tinyurl.com/qgbe4, clicked on “install plugin” and accepted the Terms of Service. Then, I answered “Yes”, and “Yes” to the prompts by Windows. You also need to add the “https://browsercheck.qualys.com” site into your trusted sites in Internet Explorer by clicking on “Tools” (the little gear icon in the top right corner), “Internet Options,” “Security,” “Trusted Sites,” “Sites” and then “Add.” Then select “Advanced Scan” in the drop-down menu in the top right corner and hit the “Scan” (or “Re-Scan”) button.
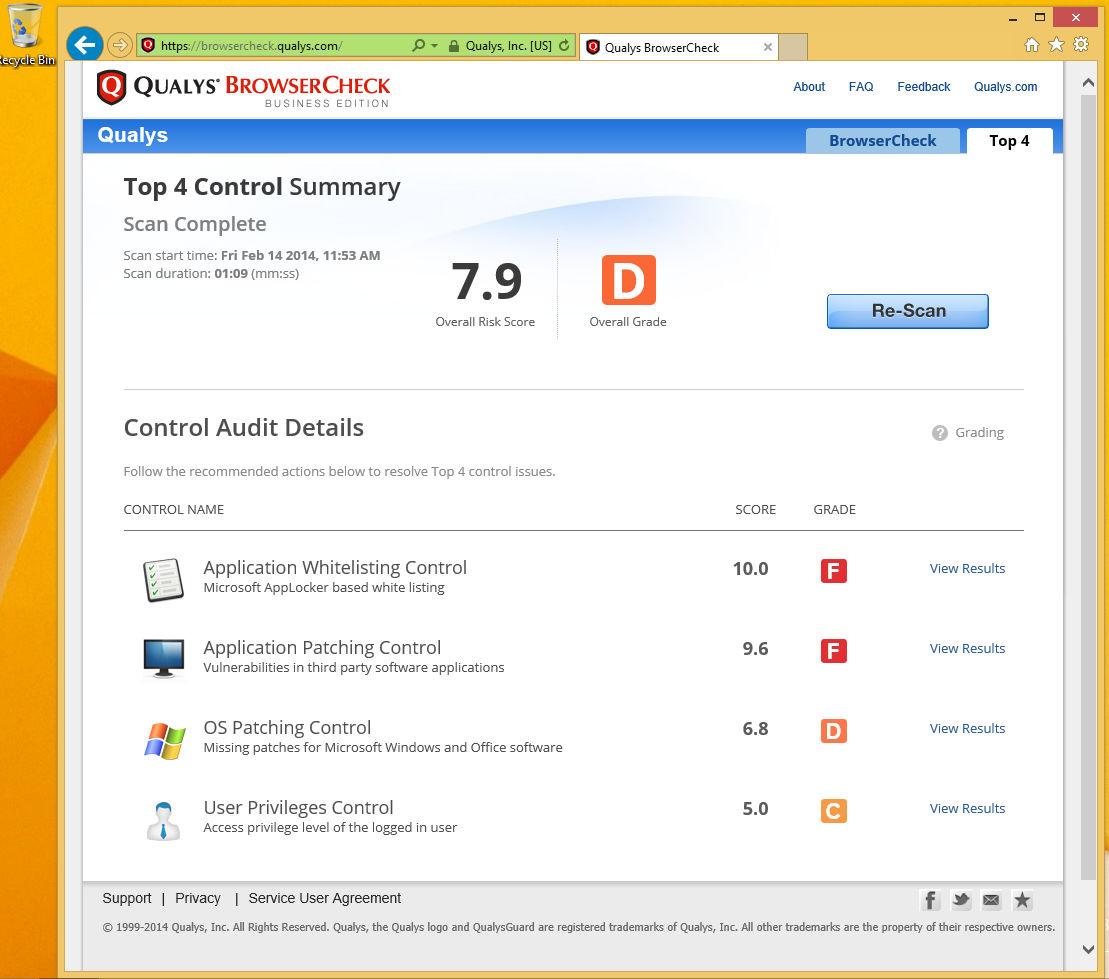
The first scan gave me a pretty bad grade: overall “D”, composed of 2 * “F” grades, and a “D” and a “B”.
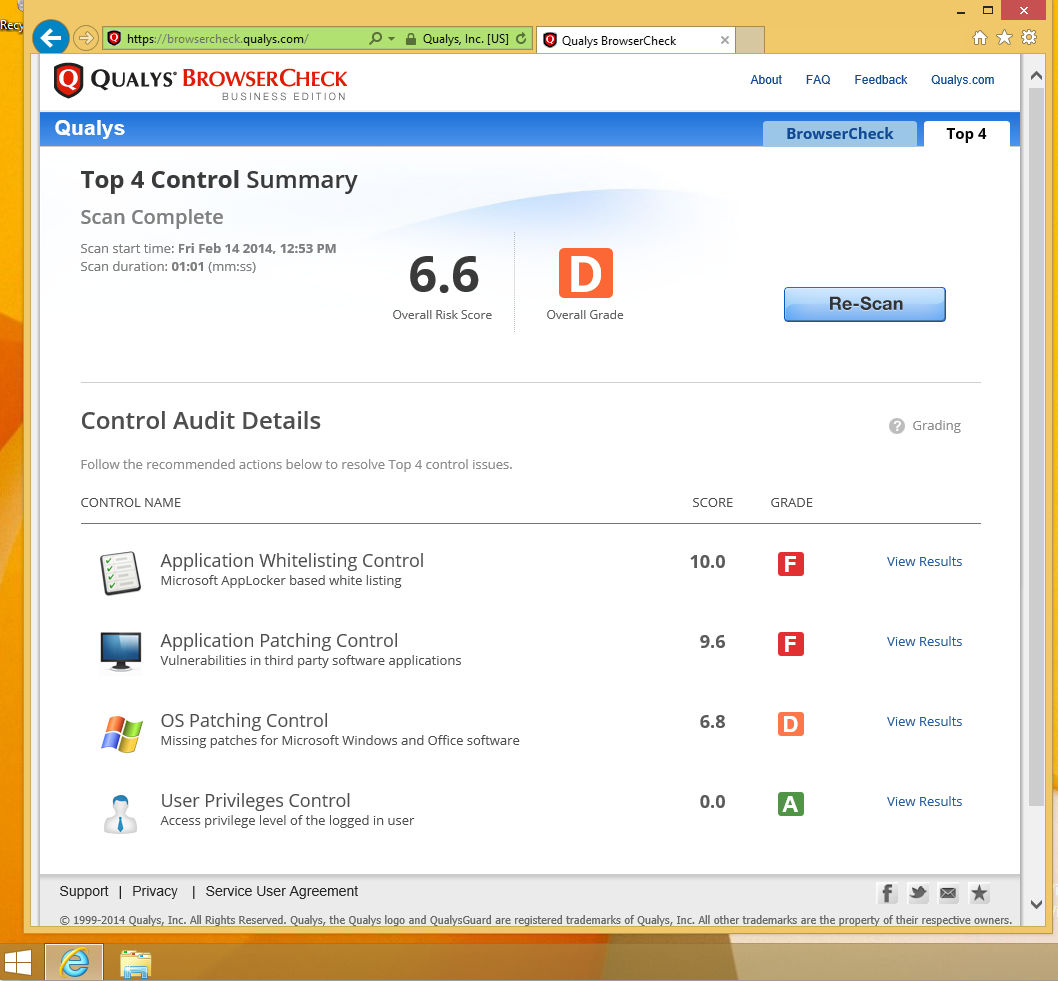
I decided to attack "control 4" from the Top 4 list first, because it should be simple to address. I started the control panel, clicked on ‘Users and Accounts” and created a second local user “wolfgang” that would serve as my day to day account. Logging out of my admin account “wkandek” and into the account “wolfgang”, I reran the scan by going to http://tinyurl.com/qgbe4 (I had to add http://browsercheck.qualys.com to my trusted sites again) and got a better score, an “A” in item 4: “User Privileges”, but still a “D” for overall security, mainly caused by the two “F” grades in controls 1 and 2.
OK, that was straightforward; so far under 30 minutes spent on getting better. Moving on to the next controls. Let’s do Windows Operating System Patching next.