Patch Tuesday January 2015, 2nd Edition
Every three months Patch Tuesday has a 2nd edition when Oracle publishes their security updates in their considerable software portfolio.
But before we get to the Oracle updates, there is news on the 0-day front. Google has auto published two more Windows bug reports (https://code.google.com/p/google-security-research/issues/detail?id=127 and https://code.google.com/p/google-security-research/issues/detail?id=128) after both had reached their self-imposed 90 day embargo limit time. Both are for Windows and will probably be classified as important once we get a Microsoft bulletin for them, meaning that by themselves they are not powerful enough to get control over a Windows target machine. However, if paired with another vulnerability both give the attacker access to the machine that could be used to escalate privileges. So there are two new 0-days out there that Microsoft most likely will address in February’s Patch Tuesday.
There is only so much you can do about the issue at this point, you could inquire with your AV vendor whether they have protection for the issue built-in as they are privy to some pre-release information from Microsoft within their MAPP program. What do you think about this current situation? Are you more on Microsoft’s side of the debate or Google’s? Interestingly, in a recent webinar in the UK, the audience was split in the middle – 25% blaming Google, 25% Microsoft and 50% blaming both equally. Let me know here in the comments section or by e-mail: wkandek@qualys.com.
But back to Oracle’s release. There are apparently 0-days here as well, because Oracle advises that some of the vulnerabilities are being used in the wild already. Their January 2015 list has 169 entries, a new record (see graph below) in terms of vulnerabilities for 48 different products types. 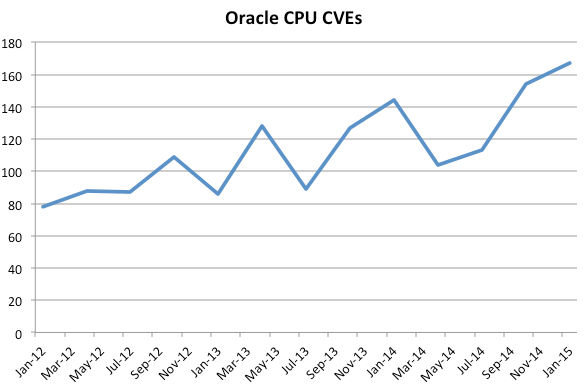
A number of the vulnerabilities reach the high score of the maximum 10 on the CVSS scale, meaning they can be used to take control over the targeted machine, working remotely through a network and without requiring credentials.
Let start with the most popular products first:
- Java: 19 vulnerabilities addressed in Java 8 and Java 7, 13 are remotely exploitable with highest score CVSS 10. This should be high on your list for your patching efforts, at least on the desktop where most of the vulnerabilities are aimed at. Only four vulnerabilities also apply to servers.
- Oracle RDBMS: nine vulnerabilities addressed with the highest score at CVSS 9. All of them require an authenticated user, so they cannot be used by simply having network access. Be advised though that database security researcher David Litchfield has recently talked about a serious vulnerability in an Oracle database that he found in a security assessment and that seems quite exploitable, see: https://twitter.com/dlitchfield/status/557209648504135681
- MySQL: also nine vulnerabilities, with three being remotely exploitable. Highest CVSS value is 7.5.
- Sun Solaris: 29 fixes for the operating system, 10 remotely exploitable with the highest score being CVSS 10. If you run Solaris and have it exposed to the Internet, this might well be your most important section of this quarters Patch release.
Beyond these four product groups there is a large number of patches for many of the Oracle systems available: application servers and middleware (Glassfish and Weblogic among others), CRM, Peoplesoft and supply chain and virtualization products as well.
With such a large patch surface it is extremely important to have a good asset map, knowing what products in what version are running in what part of your company. Most crucially, a technical owner for each such system needs to be available to talk about the security impact of these patches. I hope you have such a map in place to help in your work this month.