Patch Tuesday November 2015
Last updated on: October 27, 2022
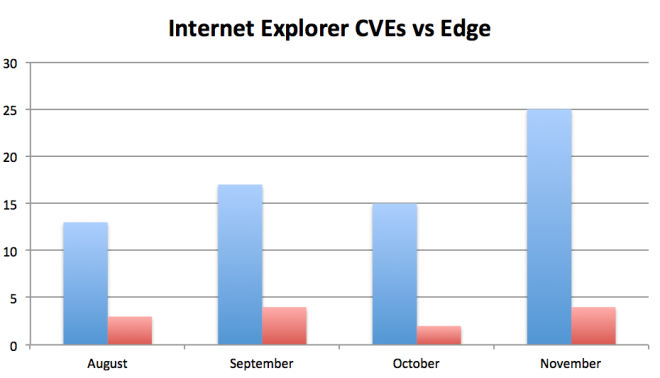
And we are back to normal for Patch Tuesday November 2015. Twelve bulletins that cover a wide mix of products from Internet Explorer (MS15-112) to Skype (MS15-123). Last month’s lower number of six bulletins was an anomaly caused by, maybe, the summer vacation? What is not an anomaly but the product of serious security engineering is the pronounced difference between Internet Explorer and Edge patches.
Edge is clearly more secure than Internet Explorer and a solid choice as your Internet Browser if your users can run all their business applications with it.
But back to our Patch Ranking. This month’s line-up has a fix for a known vulnerability in the critical MS15-115, which address seven vulnerabilities in Windows. Two of the vulnerabilities are in the font subsystem, which makes them remotely exploitable through web browsing and e-mail and affect all version of Windows, including Windows 10 and RT. MS15-115 is our top pick for this month.
Next is MS15-112 for Internet Explorer, which brings 25 fixes, 23 :!: critical that can be exploited for Remote Code Execution (RCE). The attack vector is through a malicious webpage, a very common one. Cybercriminals set these up by exploiting vulnerabilities in otherwise innocent webpages, gaining control over the content of the pages and then including invisible links to their attack pages that are driven by commercial exploit kits. The kits focus heavily on recent vulnerabilities in browsers and plug-ins (Flash is an 80% favorite according to recent research by Recorded Future) and often get new exploits just days after a vulnerability was published.
In fact browser (and e-mail) attacks are so common that the Center of Internet Security (CIS) has revamped their list of the 20 Critical Security Controls with a dedicated Browser/E-mail control as priority 7, ranked higher than normal Malware defenses in control 8.
Anyway, patch MS15-112 as quickly as you can.
Next on our list is MS15-116 which addresses seven flaws in Microsoft Office. Five of the vulnerabilities can be used to gain control over the account of the user that opens the malicious document, they provide RCE. This is enough control over the machine for a number of attacks, such as Ransomware for example. However the attacker can pair it with a local vulnerability in the Windows kernel to get a full compromise of the machine, allowing for complete control and the installation of multiple backdoors.
The other two critical bulletins are for Edge Browser (MS15-113) and Windows Journal (MS15-114) and you should apply them as quickly as possible, if just to maintain your machine on the latest level.
The remaining bulletins are all rated important and you should address them in your normal patch cycle:
- MS15-118 applies to .NET and fixes three vulnerabilities, one allowing to execute code as the user browsing the website (Cross Site Scripting). These vulnerabilities can often be used to steal the user’s session information and impersonate the user, depending on the application this can be quite significant: imagine somebody getting access to an admin level account on your web application this way.
- MS15-119 addresses an elevation of privilege vulnerability in the Windows socket system and is present on all versions of Windows, including 10.
- MS15-117 is a fix for a vulnerability in the network component NDIS and affects only older systems (Vista, Windows 7 and Server 2008).
- MS15-120, MS15-121, MS15-122 and MS15-123 fix single flaws in IPSEC, SChannel, Kerberos and Skype that can be used for DoS, MITM and encryption bypasses.
Last but not least Adobe also published an update for Adobe Flash. APSB15-28 addresses a number of critical vulnerabilities that would allow an attacker to execute code within the context of the user. Flash has been a favorite for attackers over the year, so be sure to keep it updated on your user’s machines.