NSO Pegasus iPhone Spyware Vulnerabilities Fixed by Apple – Detect & Prioritize Using VMDR for Mobile Devices

Table of Contents
- CoreGraphics Arbitrary Code Execution Vulnerability
- WebKit Arbitrary Code Execution Vulnerability
- XNU Arbitrary Code Execution with Kernel Privileges Vulnerability
- Multiple ImageIO Arbitrary Code Execution Vulnerabilities
- Discover Vulnerabilities and Take Remote Response Action Using VMDR for Mobile Devices
Apple recently released iOS and iPadOS 12.5.5, 15.0, which includes a security update that addresses almost 25 vulnerabilities, including several critical RCE and privilege escalation vulnerabilities. In 12.5.5, Apple fixed 3 critical zero-day vulnerabilities, which are used to deploy NSO Pegasus iPhone spyware to secure old iPhones. Earlier in 14.8 these 2 critical zero-day vulnerabilities exploited by NSO Pegasus were fixed and on 20th September Apple updated the security advisory and added 11 new vulnerabilities in the 14.8 security update.
“Apple is aware of a report that this issue may have been actively exploited,” the company said in security advisory. Apple has released a fifth time an immediate security update release to fix critical zero-day vulnerabilities which are actively exploited. Qualys recommends that security teams should immediately update all devices running iOS and iPadOS to the latest version.
CoreGraphics Arbitrary Code Execution Vulnerability
Apple released a patch in 12.5.5, to fix arbitrary code execution critical vulnerability (CVE-2021-30860). This vulnerability has a CVSSv3.1 base score of 8.8 and should be prioritized for patching as successful exploitation of the vulnerability allows a remote attacker to execute arbitrary code on the target system by opening a specially crafted PDF file. It affects the iPhone 5s, iPhone 6, iPhone 6 Plus, iPad Air, iPad mini 2, iPad mini 3, and iPod touch (6th generation).
WebKit Arbitrary Code Execution Vulnerability
Apple released a patch in 12.5.5, to fix arbitrary code execution critical vulnerability (CVE-2021-30858). This vulnerability has a CVSSv3.1 base score of 8.8 and should be prioritized for patching as successful exploitation of the vulnerability allows a remote attacker to execute arbitrary code on the target system by opening a specially crafted web page. It affects the iPhone 5s, iPhone 6, iPhone 6 Plus, iPad Air, iPad mini 2, iPad mini 3, and iPod touch (6th generation).
XNU Arbitrary Code Execution with Kernel Privileges Vulnerability
Apple released a patch in 12.5.5, to fix arbitrary code execution critical vulnerability (CVE-2021-30869). This vulnerability has a CVSSv3.1 base score of 8.8 and should be prioritized for patching as successful exploitation of the vulnerability may allow a malicious application to execute arbitrary code with kernel privileges on the target system. It affects the iPhone 5s, iPhone 6, iPhone 6 Plus, iPad Air, iPad mini 2, iPad mini 3, and iPod touch (6th generation).
Multiple ImageIO Arbitrary Code Execution Vulnerabilities
Apple released a patch in 15.0, to fix multiple arbitrary code execution critical vulnerabilities (CVE-2021-30835 and CVE-2021-30847). These vulnerabilities have a CVSSv3 base score of 8.8 and should be prioritized for patching as successful exploitation of the vulnerability allows a remote attacker to execute arbitrary code on the target system by opening a specially crafted image. It affects the iPhone 6s and later, iPad Pro (all models), iPad Air 2 and later, iPad 5th generation and later, iPad mini 4 and later, and iPod touch (7th generation).
Discover Vulnerabilities and Take Remote Response Action Using VMDR for Mobile Devices
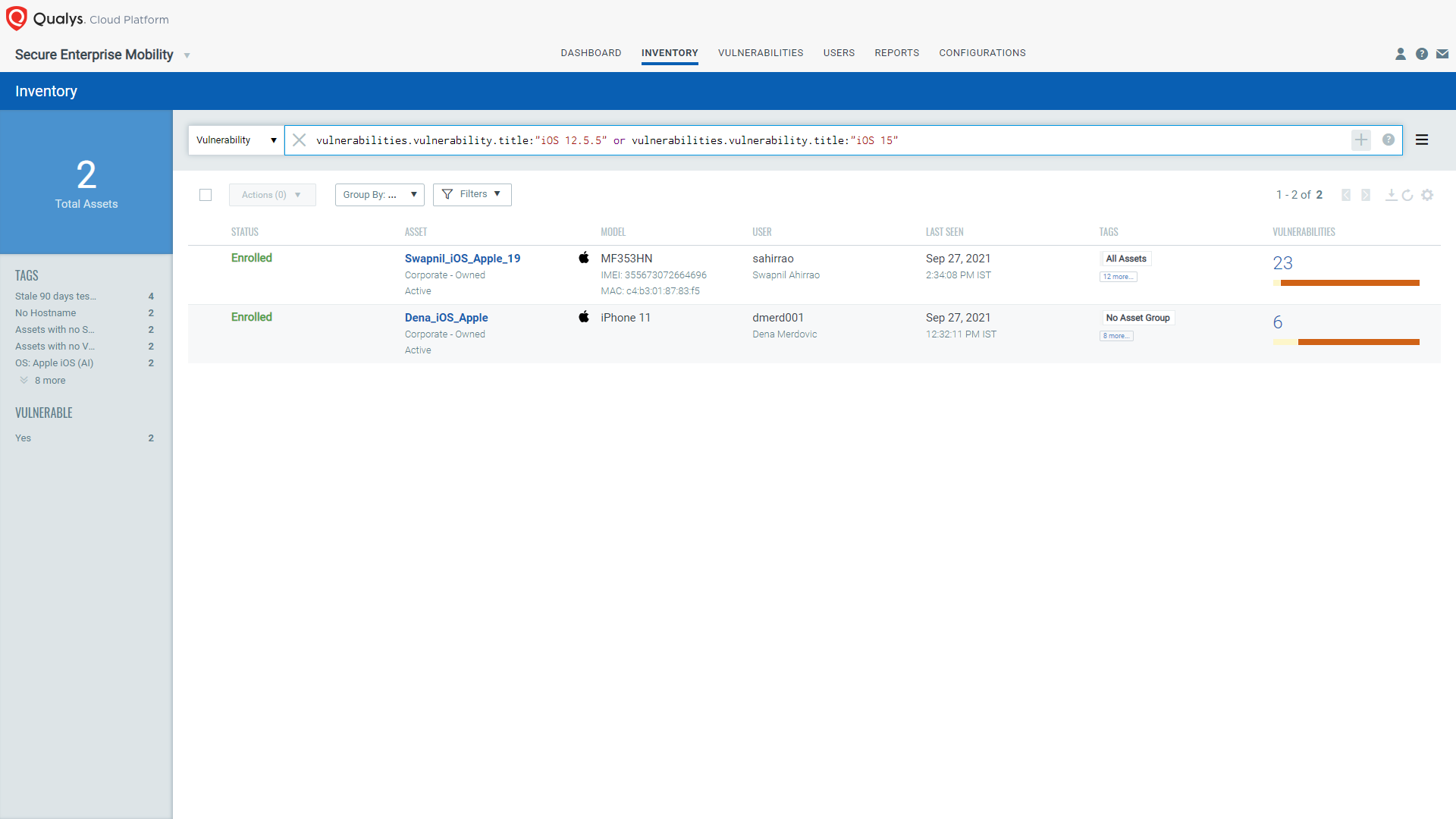
Discover Assets Missing the Latest iOS Security Updates
The first step in managing these critical vulnerabilities and reducing risk is to identify the assets. Qualys VMDR for Mobile Devices makes it easy to identify the iOS and iPadOS assets not updated to the latest version 15.0 or 12.5.5. To get the comprehensive visibility of the mobile devices, you need to install Qualys Cloud Agent for Android or iOS/iPadOS on all devices. The device onboarding process is easy, and the inventory of mobile devices is free.
Query: vulnerabilities.vulnerability.title:"iOS 12.5.5" or vulnerabilities.vulnerability.title:"iOS 15"
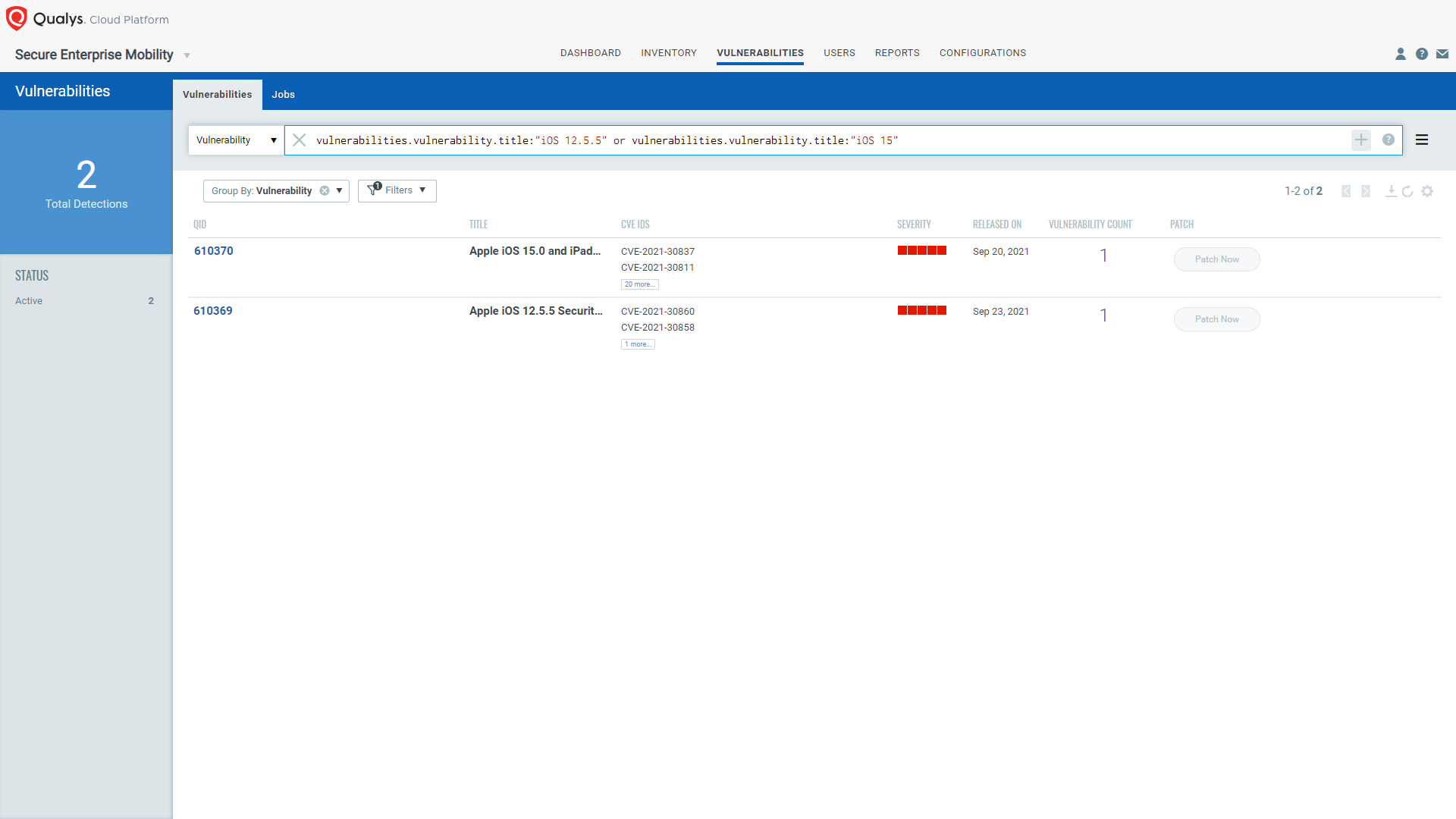
Once you get the list of assets missing the latest security patch, navigate to the Vulnerability tab. Enter the QQL: vulnerabilities.vulnerability.title:”iOS 12.5.5″ or vulnerabilities.vulnerability.title:”iOS 15″ and apply the Group By “Vulnerabilities” to get the list of the CVEs that Apple fixes in iOS and iPadOS 12.5.5, 15.0 releases. Qualys VMDR helps you understand what kind of risk you are taking by allowing the unpatched device to hold corporate data and connect to your corporate network.
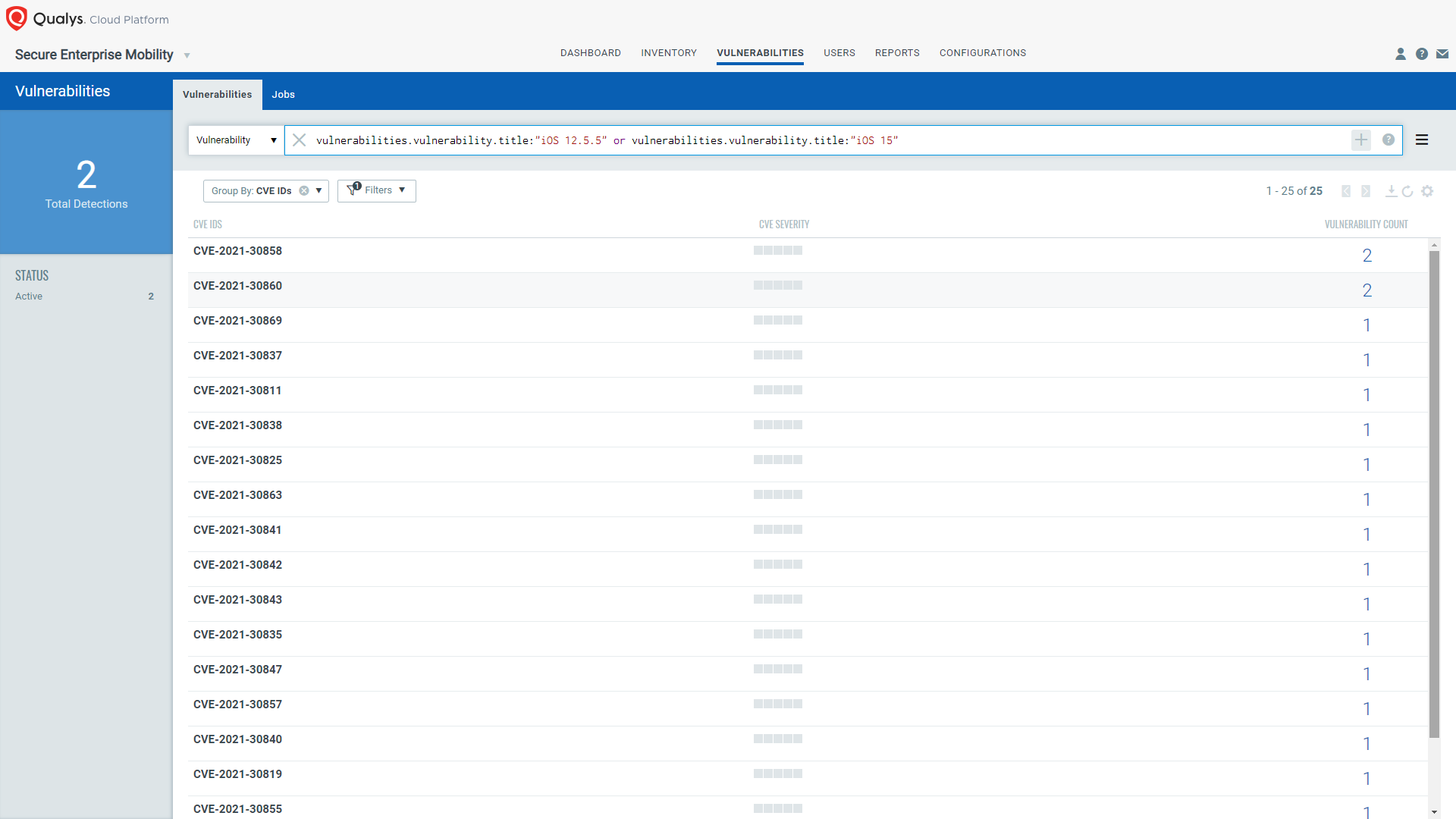
Also, you can apply the Group By “CVE Ids” to get only the list of CVEs fixed by Apple in iOS and iPadOS 12.5.5, 15.0 releases.
QID 610369 and 610370 are available in signature version SEM VULNSIGS-1.0.0.47, and there is no dependency on any specific Qualys Cloud Agent version.
With the VMDR for Mobile Devices dashboard, you can track the status of the assets on which the latest security update is missing. The dashboard will be updated with the latest data collected by Qualys Cloud Agent for iOS/iPadOS devices.
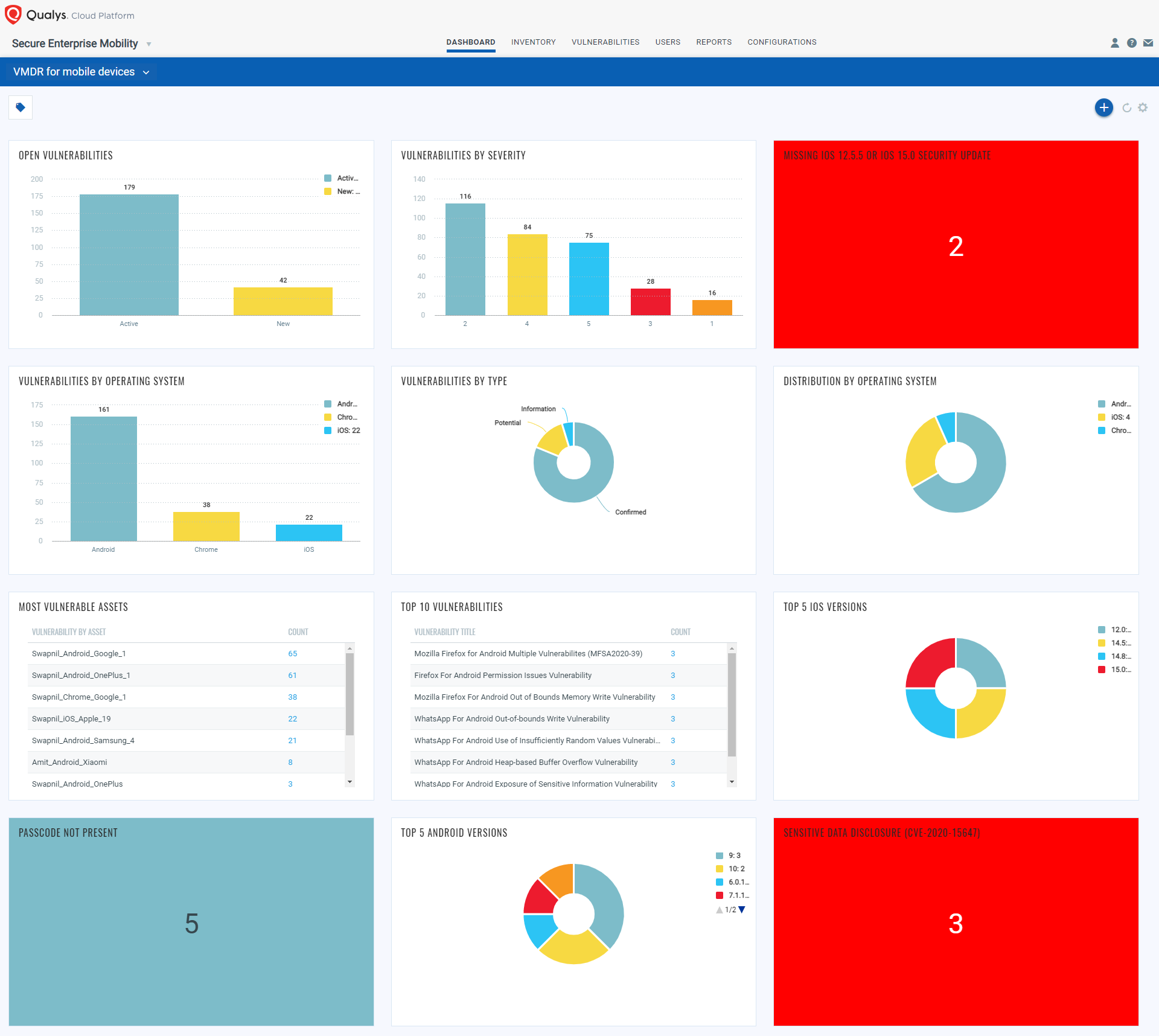
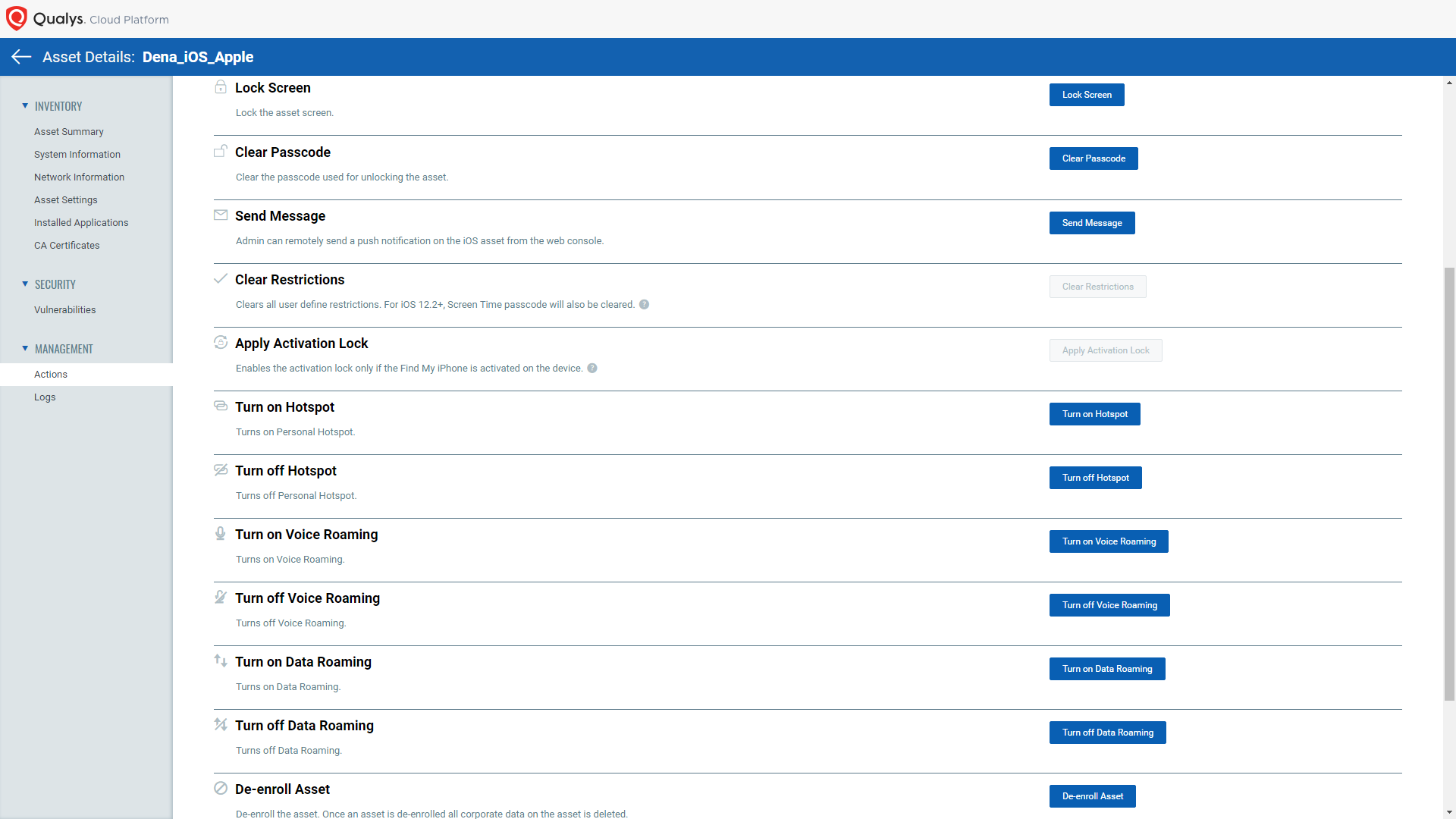
Remote Response Action
You can perform the “Send Message” action to inform the end-user to update the devices to the latest OS version. Also, you may provide step-by-step details to update the security patch.
We recommend updating to the latest iOS and iPadOS version for the assets where vulnerabilities are detected as “Confirmed”.
Qualys VMDR for Mobile Devices is available free for 30 days to help customers detect vulnerabilities, monitor critical device settings, and correlate updates with the correct app versions available on Google Play Store. You can try our solution by registering for the free 30-day service.