Tenacity 2.0 – Emulating Threat groups
Introduction
The previous article: Tenacity – An Adversary Emulation Tool for Persistence, walked us through the working of Tenacity, techniques it supports, and how it can help organizations and individuals to validate the risk posture. As with the second installment of the series, this post will be covering adversary emulation with Tenacity to demonstrate emulations of threat actor campaigns. As an update to Tenacity, we have added emulation steps for Threat Actor campaigns associated with active APT groups such as APT29, Carbanak, Fin7, etc. We now also have extended Tenacity to other techniques than just persistence.
Changes in Tenacity 2.0
- Added group commands and emulation plan for 6 threat actor groups for APT campaign emulations.
- Extended to other MITRE ATT&CK tactics and techniques.
Now, let’s look at how the above mentioned changes look like in Tenacity 2.0.
Demo
We demonstrate the usage of our tool through emulating APT29 campaign.
To show available groups for testing we can use the list command. The syntax of the command is list groups.
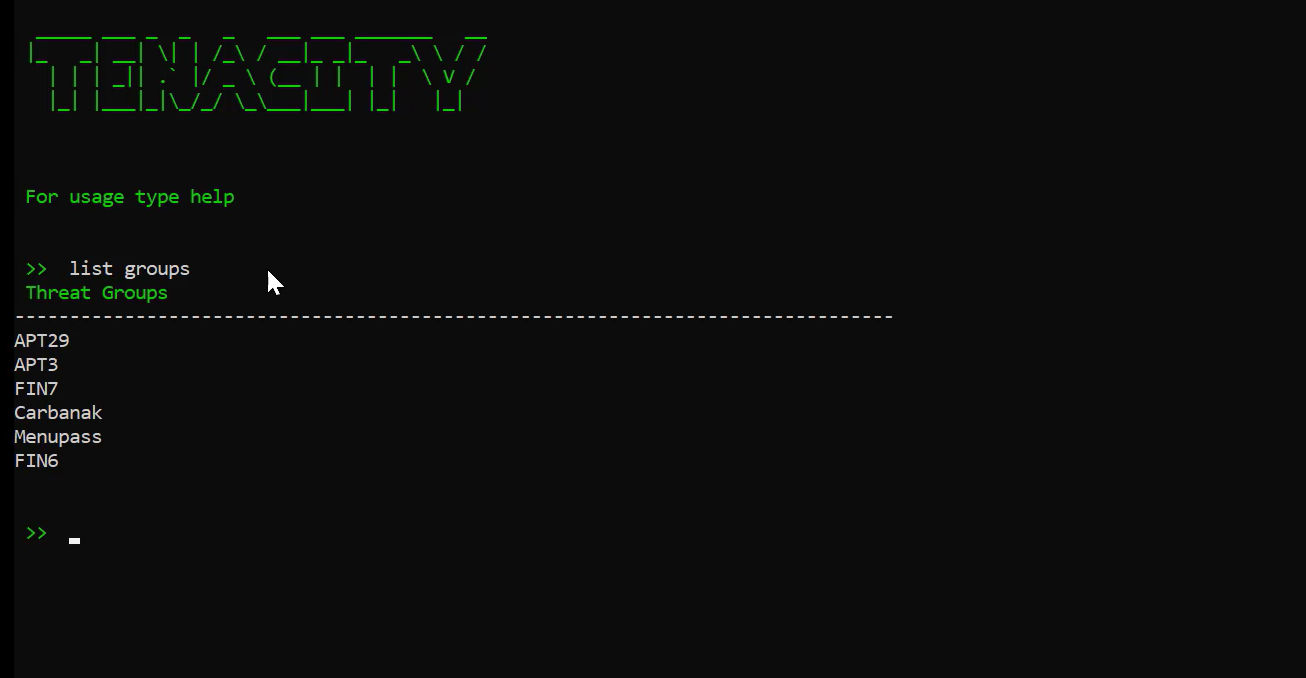
Currently 6 groups are supported. All the group commands and emulation plan are taken from the Center for Threat Informed Defense GitHub repo.
To select the group APT29 for emulation, we need to employ the use command. The syntax for the command is use APT29.

As we can see the prompt has changed and APT29 has been selected.
To check all the available techniques in APT29, we can run show techniques command.
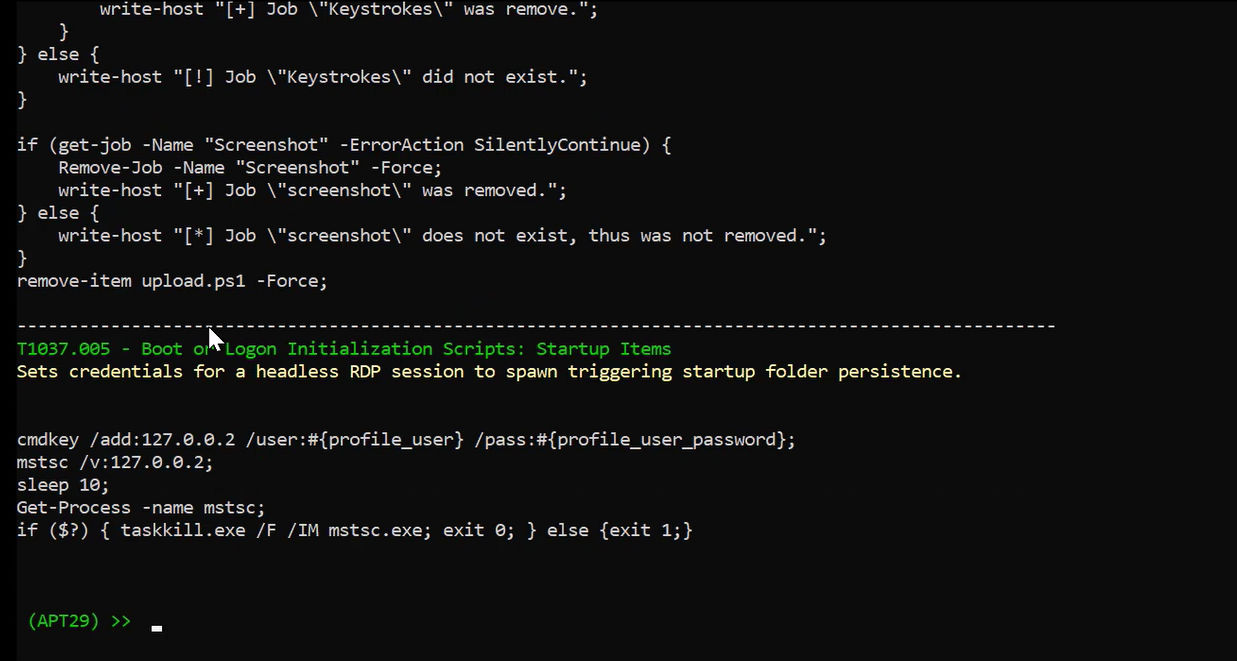
It lists down technique name, description and the command that is run.
Tenacity makes use of PowerShell or cmd to run these commands
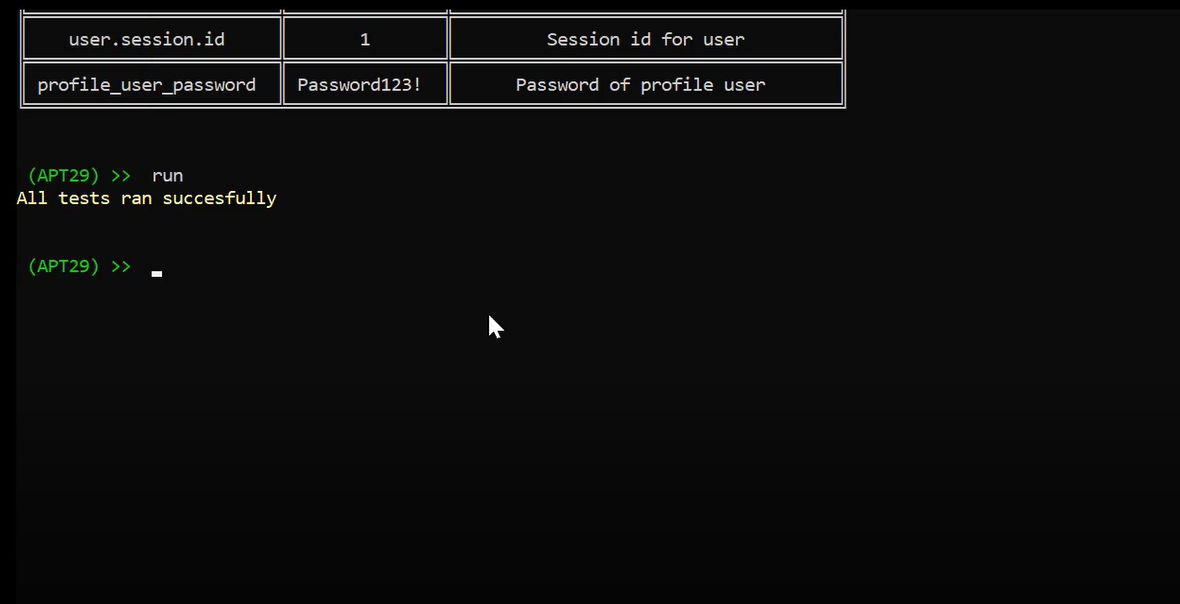
To run the emulation correctly, first we need to set some values used by the commands shown above. To see all available arguments, we need to run show command. The syntax for the same is show arguments.
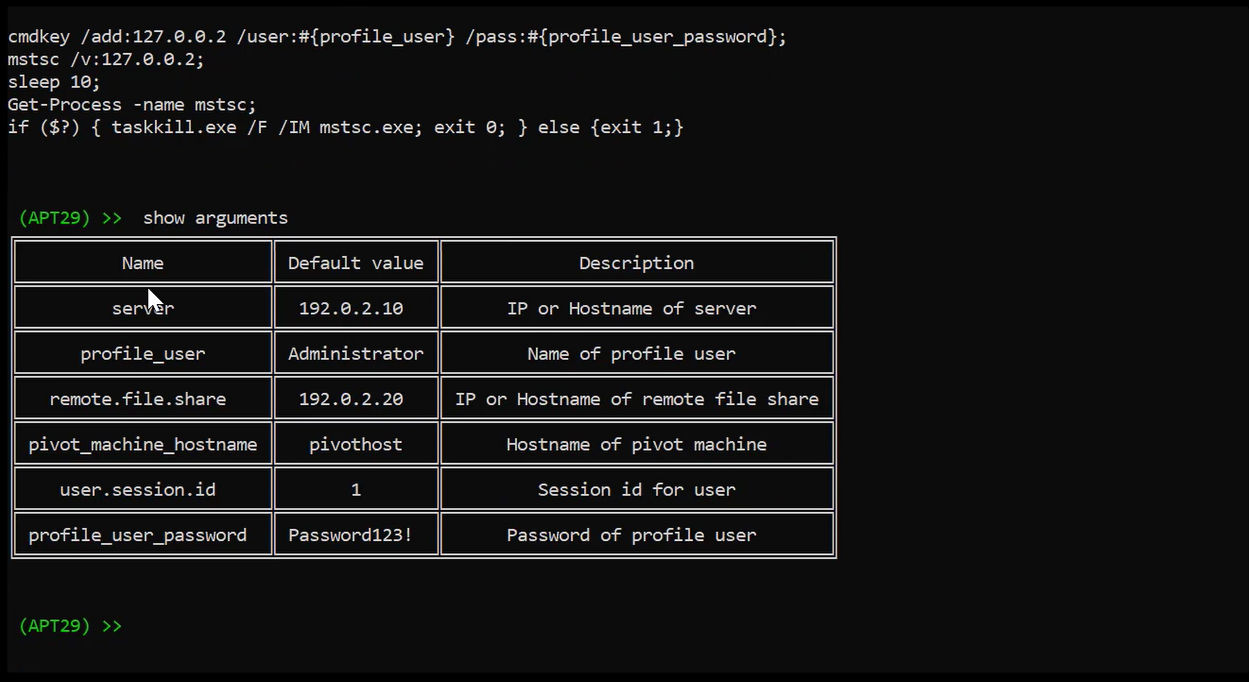
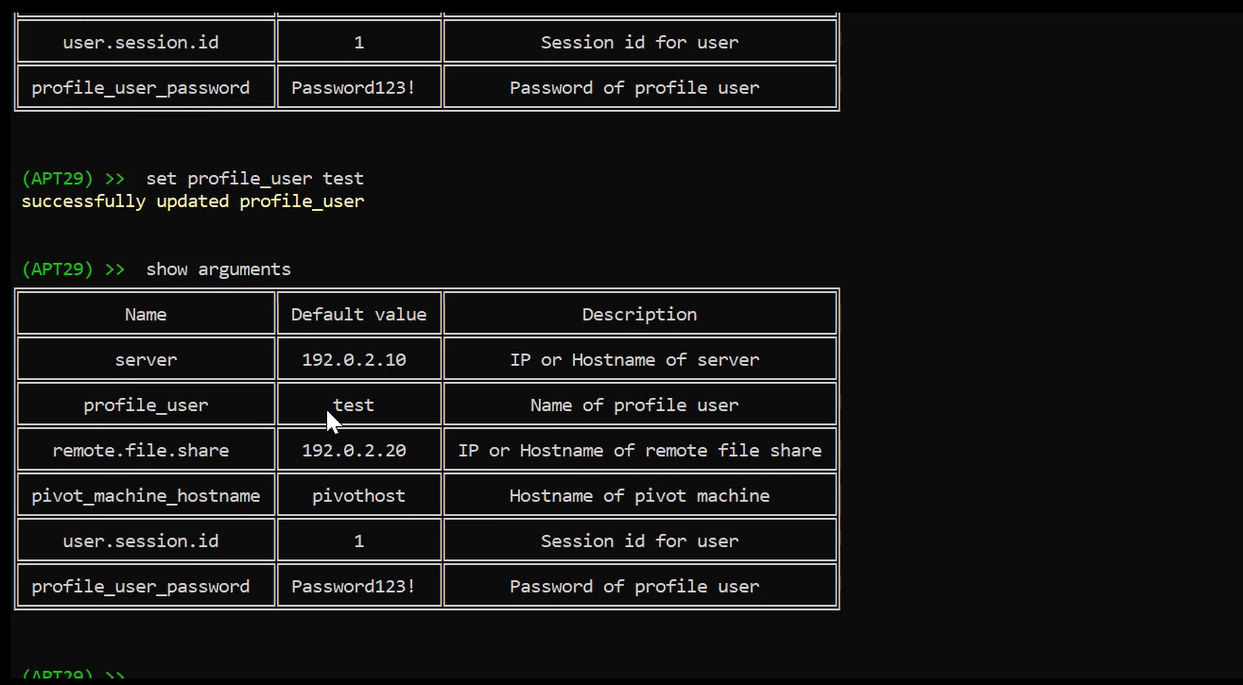
Arguments have a default value already set, to change these values we can run the set command. For example, to change the profile_user from Administrator to test, we can use the set profile_user test command.
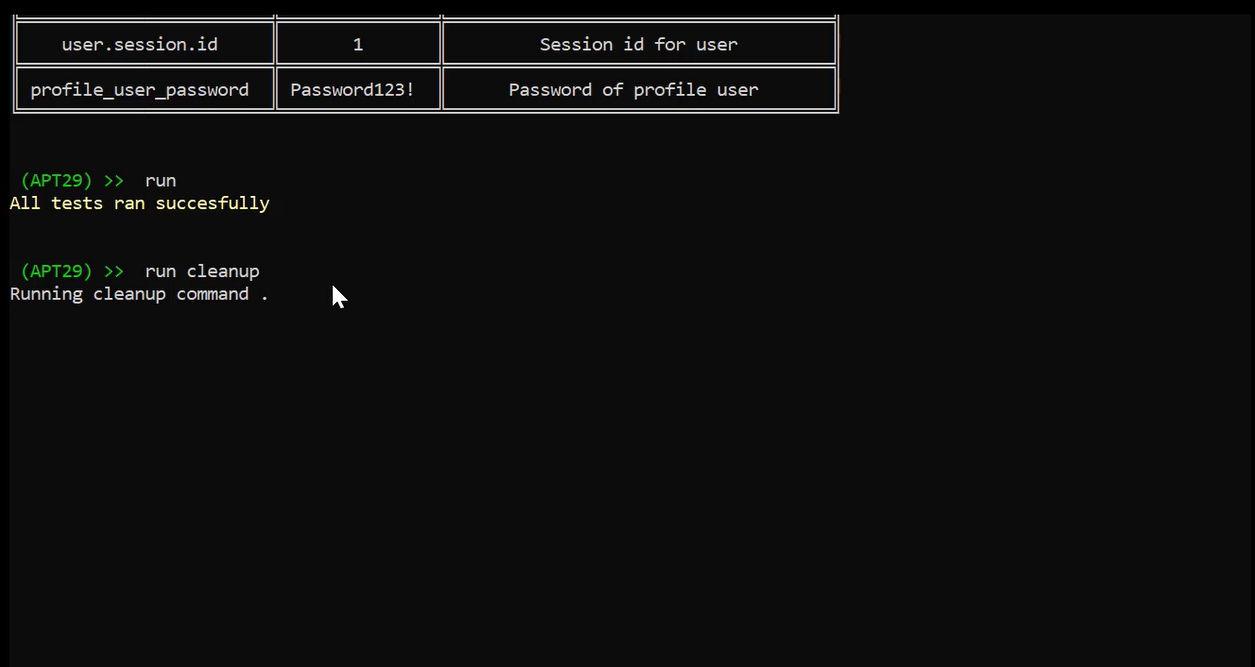
Finally, we run the emulation using the run command.
The commands run during the emulation might change up some settings or generate some artifacts. We can run the cleanup command to restore the system back to its original state
Conclusion
Tenacity 2.0 will be revealed in ROOTCON15 which is an annual hacker conference.
Well, we’ve reached the end of this series of update for Tenacity. It builds on the previous post to show not just that Tenacity can help you to emulate techniques and procedures, but also for emulation of active threat actor campaigns. We are actively working on adding new features to the emulation tool as stated earlier.
The threat landscape keeps on changing day in day out, as new groups and malware advance their functionalities. We are making active efforts to create and update plans based on ever growing threats and adversaries.