The State of Cloud & SaaS Security: Essential Statistics and Insights
Twenty-eight percent of organizations experienced a cloud- or SaaS-related data breach in the past year—meaning more than 1 in 4 enterprises were impacted. Even more alarming, 36% of those affected faced multiple breaches within a single year.
This is just one of many cloud security pain points that over 100 security and IT practitioners shared in a recent study by Dark Reading and Qualys. The picture that emerged is clear: the rapid pace of cloud-native adoption—from AI services to containerized apps—is outstripping many organizations’ ability to manage security risk.
Download the full Dark Reading report today to see everything the research revealed.
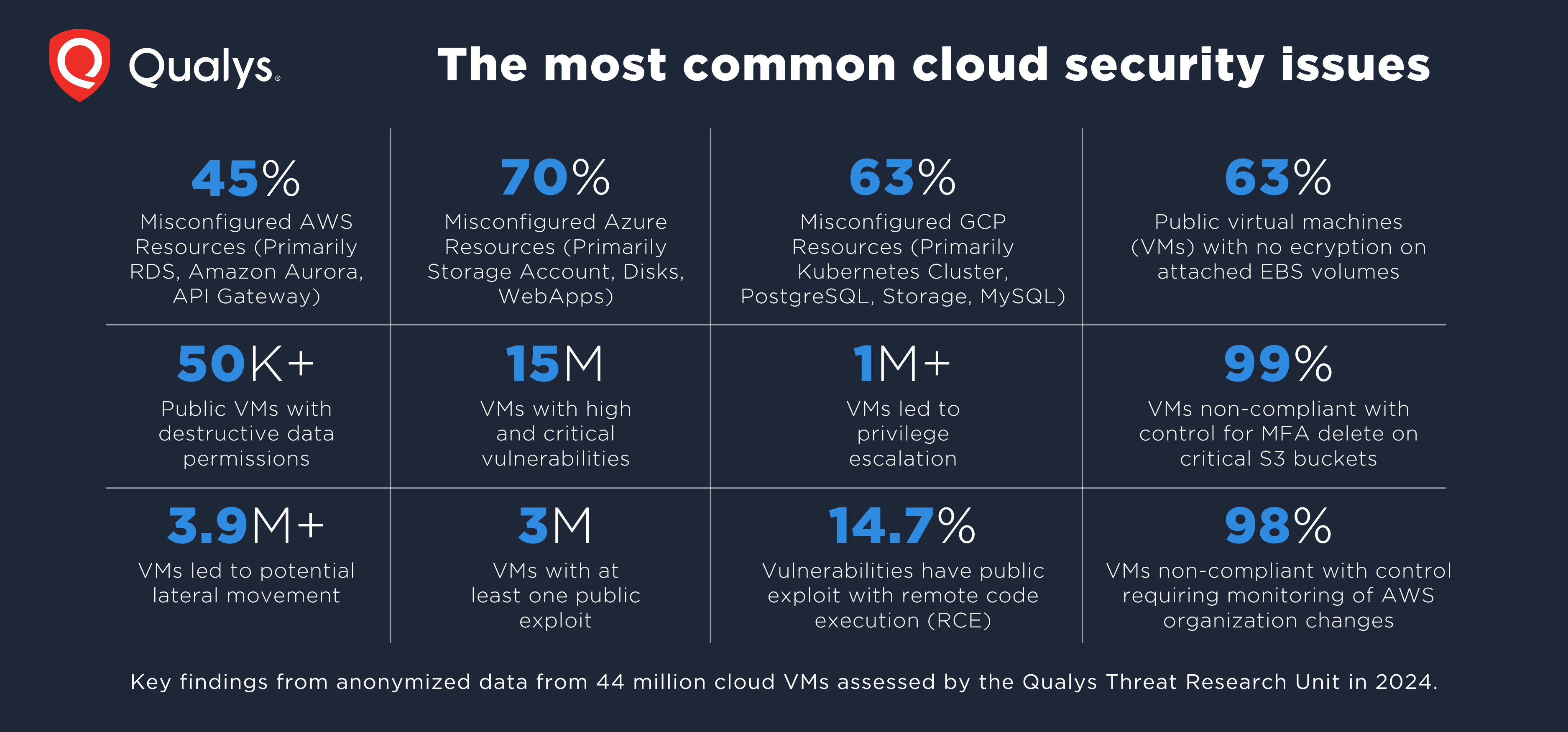
When the Qualys Threat Research Unit (TRU) correlated these practitioner insights with our own telemetry, the findings highlighted a pattern of recurring challenges: misconfigurations leading to exfiltration risk, vulnerable assets exposed to the public internet, persistent ransomware threats, and compliance drift.
Let’s dive into three key insights from the research:
Insight 1: Self-Inflicted Cloud Wounds
Despite rising sophistication in attacker tactics, the number one risk remains surprisingly basic — human error at 30%. Misconfigured cloud services continue to open doors for data breaches, and the rise of infrastructure as code (IaC) and AI-generated configurations is amplifying this risk.
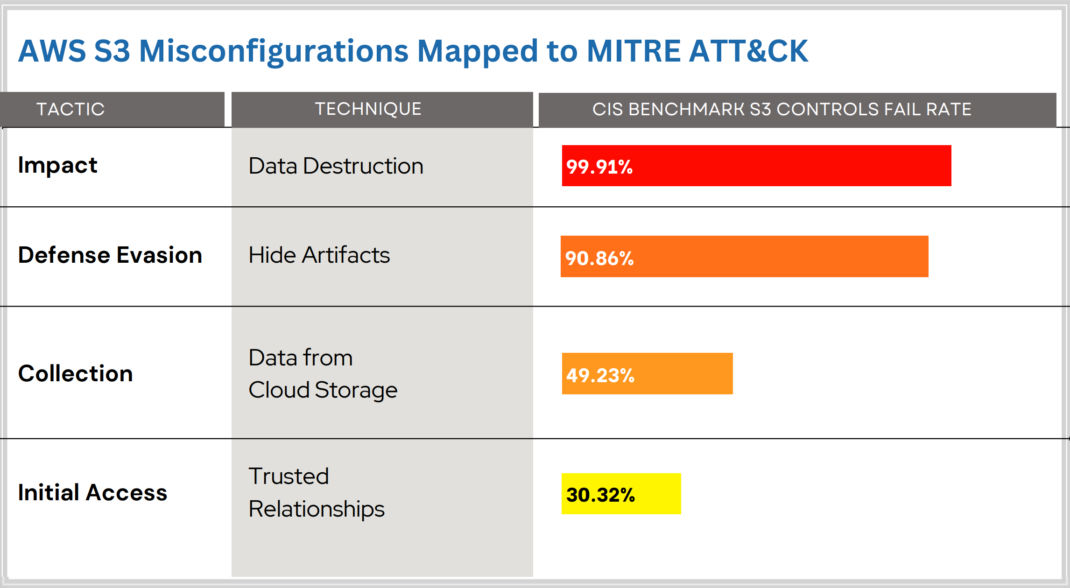
One stark example: a misconfigured AWS S3 bucket led to the exposure of 4,600 passport scans. These kinds of mistakes—whether manual or automated—are precisely why continuous misconfiguration scanning, supported by policy-based enforcement (e.g., CIS Benchmarks), remains a must-have. In fact, as seen in the data above, 99% of Virtual Machines are non-compliant for MFA delete on Critical AWS S3 Buckets in the cloud!
Moreover, these security lapses are often exploited through social engineering. Deceptive phishing emails or malicious links prey on the human element, leading to compromised credentials or unauthorized access. The bottom line: reducing the cloud attack surface starts with proactively managing misconfigurations and educating users on phishing risks.

Insight 2: Skill Gaps in Incident Response
Even with security tooling in place, organizations are struggling to respond effectively to breaches. It’s not the tech—it’s the talent. Cloud-native environments bring new variables—containers, AI workloads, multi-cloud networks—that overwhelm traditional incident response (IR) playbooks.
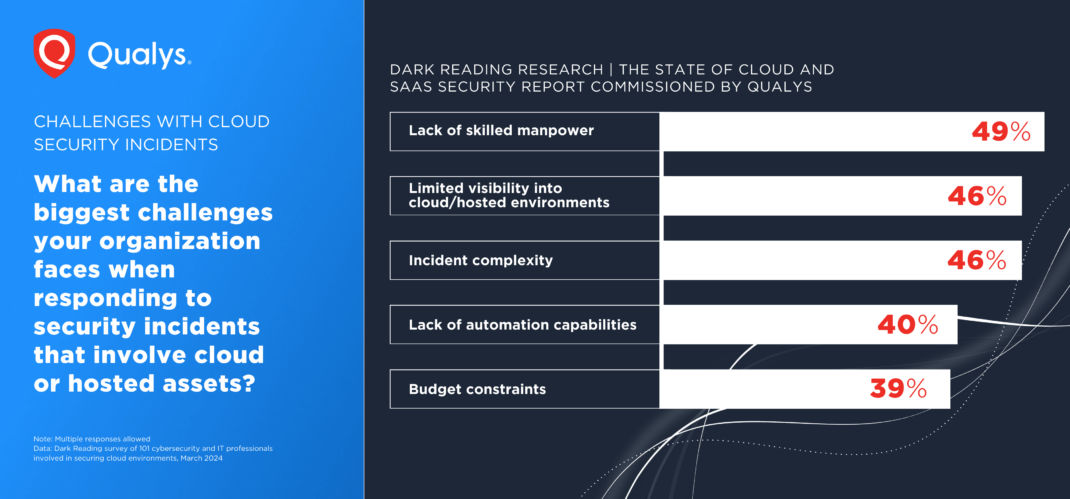
As attackers automate initial access and lateral movement through exposed APIs and credentials, security teams need deeper visibility and smarter automation. For example, in a recent Qualys TRU analysis of a cloud extortion attack, exposed API keys were used to exfiltrate sensitive data — all without tripping standard detection.
As seen in the data in the beginning of this blog, more than 3.9M+ VMs led to potential lateral movements. Security teams must start thinking like attackers. Mapping potential exploit paths from misconfiguration to compromise and integrating response playbooks directly into risk insights, is essential. The report explores how security operations can incorporate this mindset through automation and guided remediation.

Insight 3: The Increasing Cloud Conundrum of WebApps and Containers
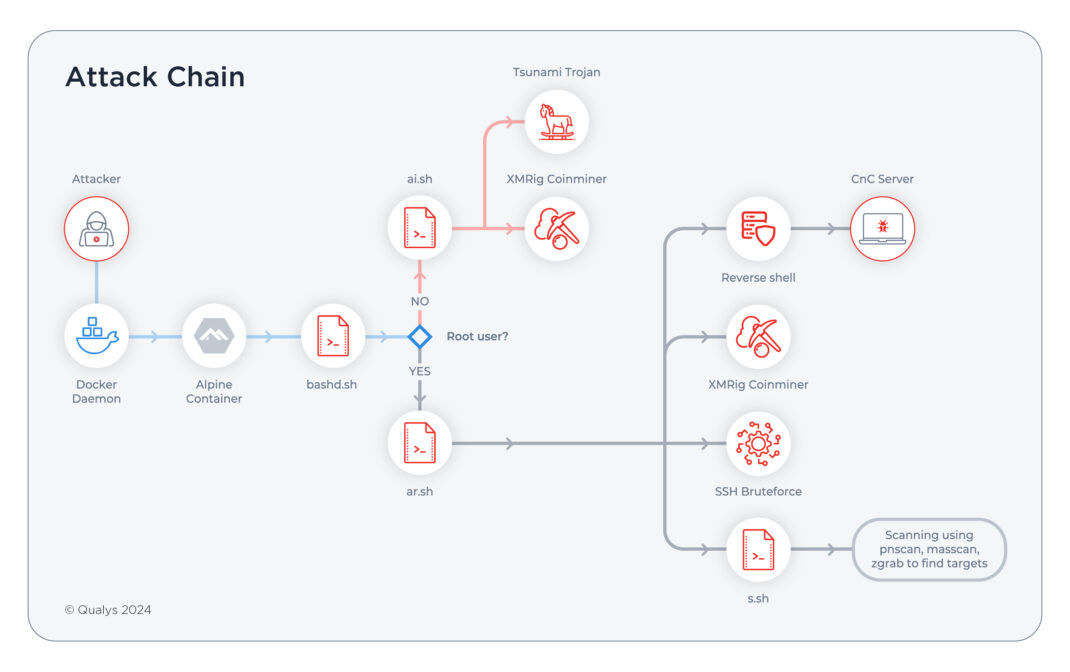
Containerized workloads and modern web applications are becoming foundational — but they’re also bringing complex, ephemeral risks. Containers introduce more inter-process communication, expanded network exposure, and rapid lifecycle changes that make traditional controls obsolete.

For example, Qualys TRU recently uncovered Docker daemon ports exposed in production environments, a misstep often stemming from dev/test habits making their way into production. These ports were exploited in crypto-mining attacks, underlining how misconfigurations can quickly become monetizable vulnerabilities.
Add to that the widespread use of third-party dependencies, and the result is an attack surface that’s constantly shifting and often invisible to traditional scanners. The report dives into practical strategies to lock down container environments and enforce policies before workloads go live.
Read More
Want to know the biggest risks to your multi-cloud and container environment? Get a custom TotalCloud TruRisk Insights report
Conclusion: Cloud Risk is Rising—But So Is the Opportunity to Get Ahead
Modern cloud environments are growing more complex, dynamic, and—when mismanaged—dangerous. From misconfigurations in infrastructure as code to skill gaps in incident response and container security blind spots, the risks are clear.
But here’s the thing: these are just three of the key insights uncovered in the new Dark Reading research, developed in collaboration with Qualys. When combined with threat intelligence from the Qualys Threat Research Unit (TRU), the report offers a deeper look at how security teams can better understand—and act on—their cloud and SaaS risk exposure.
Want the full picture?
Download the full report to get the latest data, trends, and actionable takeaways that will help you secure your cloud stack with confidence.
Interesting in learning more about Qualys?
Join us at a Qualys Security Conference (QSC) near you.
Speak to a Qualys expert.
Contributors
- Abhinav Mishra, Product Management Director, Container Security, TotalCloud CNAPP