Slash Vendor Risk and Sharpen Compliance with Policies, Standards and Regulations
As we continue our Qualys Top 10 Tips for a Secure & Compliant 2017 blog series, we zoom in on the all important area of compliance and risk monitoring, a key element of any comprehensive security program.
IT compliance and risk managers don’t have it easy. You face an increasingly complex regulatory landscape, constantly evolving industry standards and a technology environment that’s changing at a dizzying pace. It falls on your shoulders to make sure your organizations follow rules, regulations, laws, standards and practices in areas of IT across all business functions.
In this post, we’ll offer tips 5 – 7 on our list, to help you:
- Ensure internal and external IT compliance
- Assess procedural and technical controls among vendors to reduce the risk of doing business with them
- Comply with the Payment Card Industry Data Security Standard (PCI DSS)
Tip #5: When Regulators Come Calling, Be in Compliance
Organizations must conform and adhere to myriad IT compliance requirements mandated by government regulations, industry group standards and their own internal rules and policies.
Ensuring that IT systems, processes and employees comply with this bevy of complex requirements remains a major challenge with very high stakes. Failure to comply can trigger heavy fines, crippling penalties, costly litigation, staff unrest, customer backlash and other misfortunes harmful to the business.
Here are some tips for successfully managing your IT compliance process:
- Make sure the scope of your assessments is both broad and deep, encompassing your entire IT environment — on premises, in cloud instances and at mobile endpoints
- Align your internal policies with the nature of your IT environment, your business and its industry. Based on that, generate criteria for the rules, controls and settings you establish regarding, for example, employee use of personal mobile devices and of consumer apps at work.
- Don’t give short shrift to the importance of employee education and training. You can have all technology controls and configurations buttoned up, but employee carelessness and ignorance can ruin your compliance efforts.
- Stay on top of the frequent changes in government regulations and industry standards that apply to your organization. Otherwise, it’s very easy to inadvertently slip into non-compliance.
- Likewise, monitor closely developments in technology your company is using, especially emerging which may draw new regulatory scrutiny.
- Assign compliance monitoring roles and responsibilities so that people — regular employees, department heads, IT staffers or CxOs — understand who is accountable for what.
- Continuously monitor for compliance issues, and prioritize remediation of issues according to the risk they represent to the business.
- Regularly revise your IT compliance program to make sure it’s current, relevant and effective
- Generate reports that detail your compliance efforts
Start your free trial of Qualys Policy Compliance.
Tip #6: Excel at Your Security Assessments
Many organizations entirely overlook or insufficiently monitor the risk involved in giving their vendors and other third parties privileged access to IT systems and data.
But if your network of vendors, partners, suppliers and contractors are careless or negligent with security and compliance, they could be a conduit for cyber attacks against your organization.
Just ask Target. After stealing login credentials for a Target system from one of its contractors, hackers swiped personal and financial data from tens of millions of customers a few years ago.
In another high-profile incident, hackers snatched 15 million T-Mobile customer records stored on a server belonging to Experian, which was providing credit check services to T-Mobile.
You must assess how compliant these third parties that have access to your systems and data are with information security standards, your internal policies and government regulations.
It’s not just third parties. Organizations should also check that employees and department heads are complying with company policies and procedures, and with external regulations.
These business-process control assessments are conducted via surveys and poll third parties on things like business continuity plans, regulatory compliance and data
security safeguards.
When you have sent out thousands of surveys for multiple internal and external campaigns, all running simultaneously but each with a different timetable, the logistics can get complicated.
Here are some tips for ensuring a smooth survey workflow and comprehensive results:
- Adopt a uniform, company-wide third-party assessment process that every department will follow for survey design, management, distribution, tracking and collection
- Automate as much of the workflow as possible, including design of questionnaires, distribution of surveys and tracking of campaigns, because manual processes — emailing respondents, aggregating results on spreadsheets — don’t scale, waste time, are labor intensive and cause errors
- Stay current with ever-changing regulations and update survey questionnaires to reflect new requirements
- Generate charts, reports and graphs to help various stakeholders — executives, compliance officers, auditors — can visualize survey results and drill down to details as necessary
- Establish a schedule so that assessments are conducted with the proper frequency for different vendors
Read more about conducting cloud-based vendor risk assessments with Qualys SAQ, and start your free trial.
Tip #7: Protect cardholder data — and your business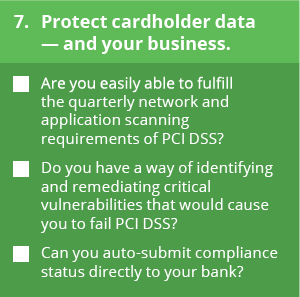
Any business that accepts credit card payments must be in compliance with the Payment Card Industry Data Security Standard (PCI DSS). Administered by the Payment Card Industry Security Standards Council, PCI DSS seeks to ensure that organizations properly protect the collection, storage, processing and transmission of cardholder data.
If they lose PCI DSS compliance, businesses can get hit with fines and even be expelled from credit card approval programs.
The PCI DSS assessment process is rigorous and complex, and demands a comprehensive, accurate audit of many technical and operations elements involved in credit card data protection.
However, backers of PCI DSS credit it with promoting healthy security practices over the past decade with substantial benefits for organizations that adopt its guidelines and requirements.
“PCI may not be perfect, but its widespread adoption has dramatically improved card security. And the need for PCI is not going away anytime soon,” wrote Tracy Kitten, Executive Editor of Bank Info Security in August.
Here are some tips to help you remain PCI DSS compliant:
- Approach PCI DSS compliance as a continuous process of assessment, remediation and reporting, not as a mandated quarterly scan or annual evaluation. PCI DSS is very much about having good, basic security practices, policies and processes always in place.
- If you’re just embarking on the PCI DSS journey, don’t get overwhelmed. Draft a sensible plan of attack, or follow recommendations and best practices on how to get started, such as the Council’s “Prioritized Approach to Pursue PCI DSS Compliance.” As consultant Ben Rothke noted recently in CSO magazine, a prioritized approach helps organizations new to cardholder data security “triage their often limited staff and budget to achieve compliance in the most expeditious manner.”
- Only collect and store credit card data that you need to keep. Many organizations capture an unnecessary amount of information during the transaction.
- Establish a lifecycle for the type of data that you do store, so that you only retain those pieces of information for the amount of time necessary, not longer, and then dispose of it.
- Devote specific IT resources for card payment processing so that you can narrow the scope of compliance assessment
- Look for vendors whose products or services the Council has determined as “qualified” for PCI DSS.
- Draft a detailed remediation plan for mitigating or patching the discovered vulnerabilities and generate detailed reports that document your compliance with all requirements
Start your free trial of Qualys PCI Compliance.
We’ll continue this series next week with the last three tips in our series, which focus on securing your web applications.
In case you missed them, below are links to the first two posts in this series:
Information Security and Compliance: New Year’s Resolutions You Can Keep
Overwhelmed by Security Vulnerabilities? Here’s How to Prioritize