Microsoft Misfires with Meltdown Patch, while WannaCry Pops Up at Boeing
In our weekly roundup of InfoSec happenings, we start, as has often been the case this year, with concerning Meltdown / Spectre news — this time involving Microsoft — and also touch on a password hack at Under Armour, a WannaCry infection at Boeing, and a severe Drupal vulnerability.
Microsoft patches its Meltdown patch, then patches it again
In an instance of the cure possibly being worse than the disease, a Microsoft patch for Meltdown released in January created a gaping security hole in certain systems in which it was installed.

It took Microsoft two tries to fix the issue, which affects Windows 7 (x64) and Windows Server 2008 R2 (x64) systems. The company thought it had solved the vulnerability (CVE-2018-1038) with a scheduled patch last Tuesday, but then had to rush out an emergency fix two days later.
Security researcher Ulf Frisk, who discovered the vulnerability, called it “way worse” than Meltdown because it “allowed any process to read the complete memory contents at gigabytes per second” and made it possible to write to arbitrary memory as well.
“No fancy exploits were needed. Windows 7 already did the hard work of mapping in the required memory into every running process,” Frisk wrote. “Exploitation was just a matter of read and write to already mapped in-process virtual memory. No fancy APIs or syscalls required — just standard read and write.”
As Qualys’ Director of Product Management for Patch Management Gill Langston wrote in this blog, there are no current active attacks against this vulnerability but there is proof-of-concept code. “Opportunistic actors could weaponize this exploit by using a multi-stage attack to gain access to an affected asset,” he warned.
Langston recommends that organizations install Thursday’s out-of-band patch if they installed any of the security updates in January of this year or later. “Also ensure that other layers of protection (anti-malware, email security, web filtering) are up to date to minimize your risk profile,” he wrote.
Qualys created QID 91440 in Vulnerability Management. Detection requires authenticated scanning or a Qualys Cloud Agent installed on the asset.
Under Armour’s MyFitnessPal app passwords swiped
Cyber thieves stole usernames, email addresses, and hashed passwords from 150 million accounts of Under Armour’s MyFitnessPal app at some point during February. Those affected must change their MyFitnessPal app passwords immediately, and should do the same on any other online account in which they’ve used that same password.
They also should be vigilant about suspicious activity on all their other online accounts, and about unsolicited requests to provide personal information, visit webpages, click on email links or download attachments.

Under Armour, a sports apparel maker, made no mention in its breach notice of how the hackers were able to access the data. The company discovered the hack last week.
Over at Sophos’ Naked Security blog, Mark Stockley points out that the hackers had at least a month “to send targeted MyFitnessPal phishing emails, to crack the stolen password hashes, and to try any cracked passwords on other services (such as social media accounts).”
“Since the information at risk can be used to log in to your MyFitnessPal account, all the data you see when you log in to your account is also at risk,” he added.
Writing in Wired, Lily Hay Newman makes a thorough analysis of the hack, and of what Under Armour did well (quick disclosure, system segmentation, use of “bcrypt” hashing function) and not so well (use of SHA-1 hashing function).
WannaCry infects Boeing systems
If you thought WannaCry was oh so 2017, think again. The notorious ransomware grabbed headlines again last week when news broke that it had cropped up at giant airplane manufacturer Boeing.
When it was first detected, Boeing leaders feared the worst, including manufacturing process disruptions, but when the dust cleared it seems the damage was quickly contained and pretty limited.
“We’ve done a final assessment,” Linda Mills, the head of communications for Boeing Commercial Airplanes, told The Seattle Times. “The vulnerability was limited to a few machines. We deployed software patches. There was no interruption to the 777 jet program or any of our programs.”
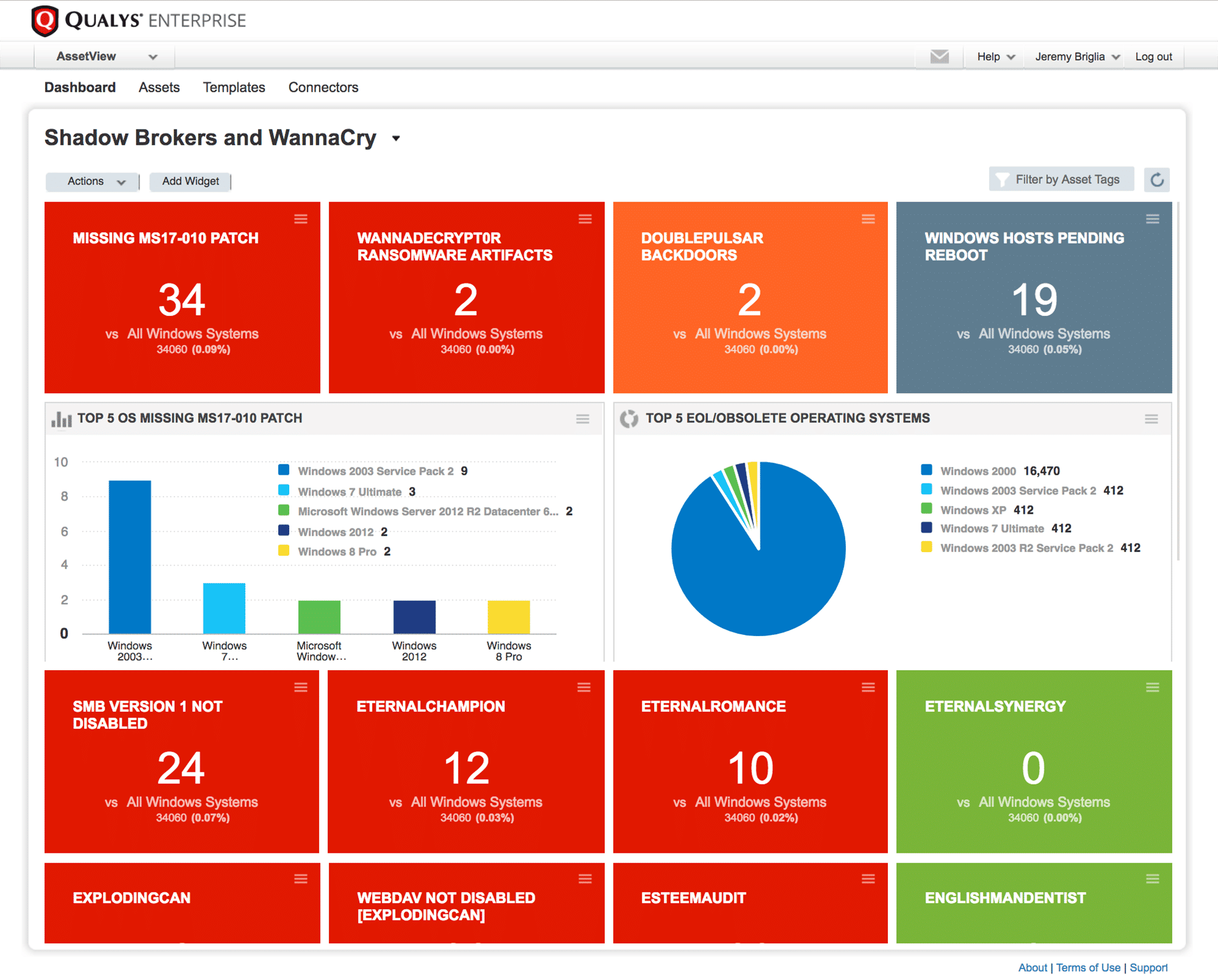
Still, the incident serves as a good reminder that WannaCry — formal name WanaCrypt0r 2.0 — spreads using an exploit called EternalBlue for Windows OS vulnerabilities that Microsoft patched in March 2017, so more than a year ago now.
The vulnerabilities, in Windows’ SMB (Server Message Block) protocol and described in security bulletin MS17-010, were rated “Critical” at the time by Microsoft due to the potential for attackers to execute remote code in affected systems.
Writing in Sophos’ Naked Security blog, John E. Dunn suggests that systems remain unpatched for WannaCry because remediating these vulnerabilities isn’t always straightforward.
“One reason for this persistence is that WannaCry doesn’t just affect regular desktops, laptops and servers, but also spreads to and from unpatched Windows 7 systems of the sort widely used in manufacturing as Windows Embedded,” Dunn wrote.
Here’s more information on how to detect and address the MS17-010 vulnerabilities with Qualys products.
Other WannaCry resources from Qualys include:
- Detailed walkthrough of how to report on it for those new to Qualys.
- Detailed walkthrough of how to build WannaCry dashboards in AssetView. Also available as a webcast.
- De-duping WannaCry detections
- On-demand WannaCry webcast, summary and transcript of participant Q&A showing how to identify at-risk assets and institute threat-prioritized remediation processes for current and future risks.
- First-hand perspective of how one company kept the threat under control (via TechRepublic)
- Technical Resources and Detection Methods for WannaCry related QIDs are found in the WannaCry Support Article: Qualys response for Global Ransomware Attack (WannaCry)
Drupal: Highly critical vulnerability affects 1M+ websites
As it had recently promised, Drupal last week released a patch for a remote code execution vulnerability it rated as “highly critical” that affects multiple subsystems of Drupal 7.x and 8.x.
“This potentially allows attackers to exploit multiple attack vectors on a Drupal site, which could result in the site being completely compromised,” Drupal warned in its advisory.

In a companion FAQ, the Drupal security team pegged the scope of affected systems at 9% of sites using its CMS (content management system) platform, or more than 1 million sites.
While Drupal has no knowledge of successful exploits of this vulnerability, it nonetheless recommends immediate remediation because “site owners should anticipate that exploits may be developed and should therefore update their sites immediately.”
The solution: Upgrade to the most recent version of Drupal 7 or 8 core.
Specifically, those running 7.x should upgrade to Drupal 7.58, or alternatively apply this patch on systems that can’t be immediately upgraded. Meanwhile, those running 8.5.x should upgrade to Drupal 8.5.1, or apply this patch on systems that can’t be immediately upgraded. The FAQ states that Drupal 6 is also affected and points users of that version to its long term support page.
Writing in the Qualys Community site, Dave Ferguson, Director of Product Management for Web Application Scanning at Qualys, called the vulnerability (CVE-2018-7600) “very dangerous.”
According to Ferguson, customers using Qualys Web Application Scanning (WAS) to scan all their websites on a regular basis can quickly find out if they’re running a vulnerable Drupal version without having to run additional scans.
“Simply open WAS and go to Detections. In the search field, enter “150183” (this is the WAS QID reported when Drupal CMS is detected). If WAS has identified any web apps running Drupal, you will see QID 150183 listed in the detections. Open each detection and look at the Results section to see the version of Drupal running on that site. If necessary, start the patching process,” Ferguson wrote.
In other infosec news …
- The city government of Atlanta, which recently suffered a serious ransomware attack that disrupted operations, was warned months ago that its IT systems were riddled with “severe and critical vulnerabilities” that put them in serious danger of cyber attacks, according to CBS46, the local CBS affiliate.
- Hackers breached a Baltimore city government server, impacting the city’s 911 system, as reported by The Baltimore Sun.
- Cryptocurrency Monero may not be as private as previously thought, according to a research report published last week. Sophos’ Naked Security blog has a take on the research, as does Wired, while Coindesk dismisses the findings as “old news.”