Securing Databases with Qualys Policy Compliance
Data is the most valuable asset that an organization holds, and the most common target for malicious attackers. According to Forbes, in the first six months of 2019, data breach incidents exposed an astounding 4.1 billion records worldwide. Hackers successfully attacked government agencies as well as private corporations, keeping everyone under a constant threat of exploit. Although data breaches are not a new phenomenon anymore, what stood out in this year’s attacks was the sophistication in which these attacks were carried out. Learned users as well as experienced officials fell prey to the traps, resulting in massive information leakage.
If trends are to be followed, data theft has a proven record of being a lucrative business in the world of cybercrime. As people have become increasingly aware of their right to privacy, the way data is handled and secured has reached the peak of discussions globally.
In the current digital era, securing databases is one of the most crucial and highly challenging aspects of security for any enterprise.
Before we go to the subject of database security, let’s find out about the primary reason that leads to these malicious attacks. What is it that leaves the databases vulnerable enough for them to fall prey to hackers?
Research shows that the most common reasons behind database security breakdowns are unpatched vulnerabilities and configuration errors. All organizations, no matter how small, need to be vigilant about the security posture and ensure that all their databases are protected.
Qualys’ Support for Database Security
Qualys helps you secure your databases with the industry’s most advanced and scalable solutions for vulnerability, risk management and compliance. It provides you with the tools to gain global visibility into your databases, their current vulnerabilities and what you must do to protect them.
Qualys Policy Compliance (PC) automates the labor-intensive process of checking settings and misconfigurations in your environment. It helps you identify vulnerabilities and violations before they get out of hand and makes remediation easy. Qualys PC, with its support for a wide range of platforms and out-of-the-box library content, enables you to fast-track your compliance assessments.
Let’s take a look at the various ways how Qualys PC helps you ensure that your databases are never exposed to vulnerabilities and malicious threats.
Extensive Platform Support
Considering the fact that databases hold extremely valuable and sensitive information, Qualys offers its support for an extensive range of platforms. Apart from the currently supported platforms, Qualys continues to add support at frequent intervals.
With the wide range of platforms, it ensures to extend instant and comprehensive compliance visibility to your databases with ease.
Following is the list of database platforms that are currently supported. Qualys continues to add new technologies to the current list to ensure an extensive platform support.
| Platform | Version |
|---|---|
| IBM DB2 | 9.x, 10.x, 11.x |
| IBM Informix | 11.x, 12.x |
| MariaDB | 10.x |
| Microsoft SQL Server | 2000, 2005, 2008, 2012, 2014, 2016, 2017 |
| MongoDB | 3.x, 4.x |
| MySQL | 5.x |
| Oracle | 9i, 10g, 11g, 12c |
| PostgreSQL | 9.x, 10.x, 11.x |
| SAP ASE | 16 |
| Sybase ASE | 15 |
Content Library for Database Policies
The library policies provided by Qualys can be customized to meet your organization’s security and compliance requirements. Whether you use the library content for strengthening a handful of control requirements or for building a comprehensive technical standard, Qualys’ control library provides coverage of the most common critical security control objectives out-of-the-box.
Refer to the list of database policies.
System-Defined Controls for Databases
Controls are the building blocks for policies that are used to scan the security posture of your assets. Qualys provides system-defined controls (SDCs) that you can use to scan your databases. These out-of-the-box controls are generic and ready to be used for security and compliance evaluation of databases on any of the supported platforms.
As a part of its continuous effort to extend its current capabilities, Qualys continues to add new system-defined controls.
User-Defined Controls for Databases
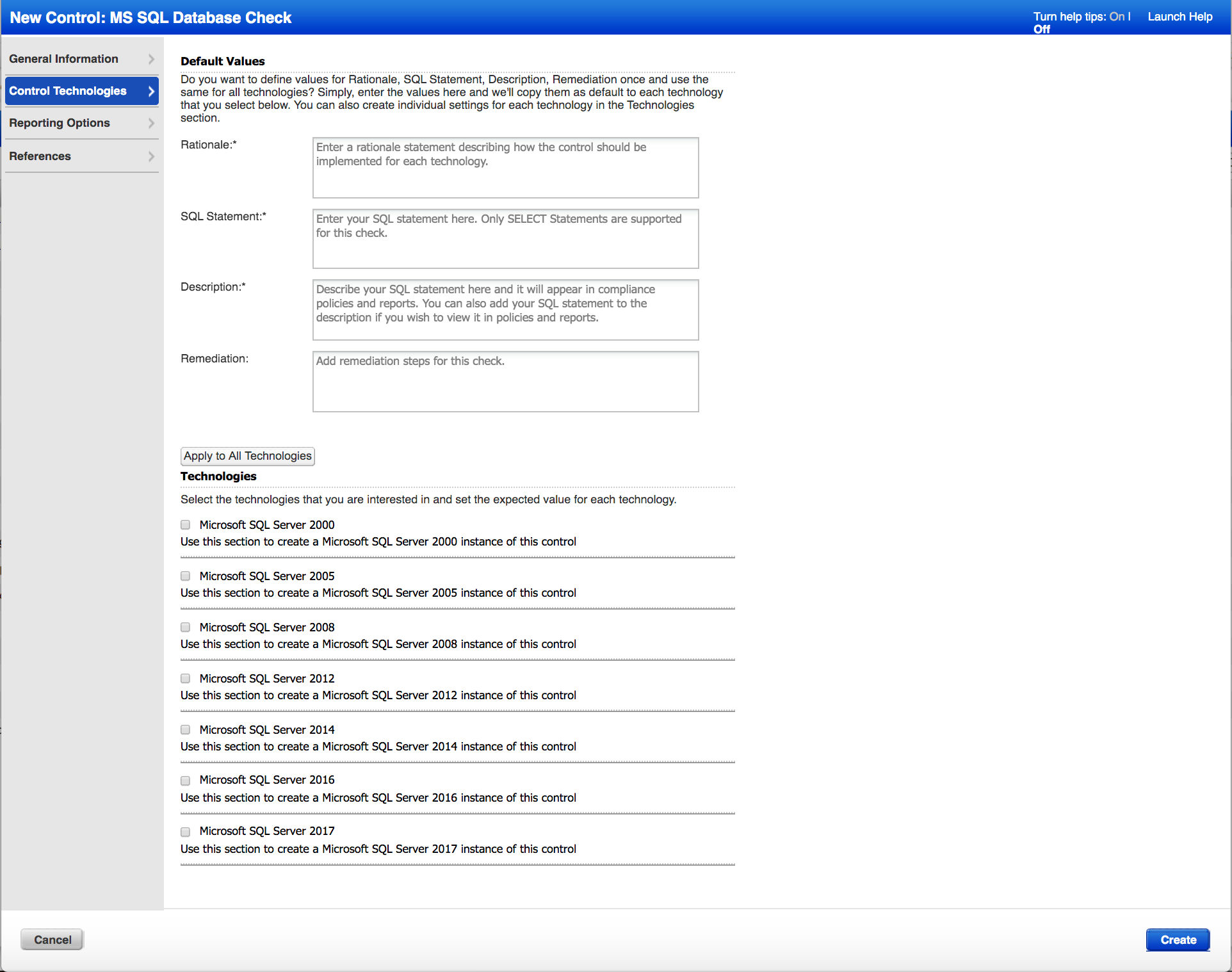
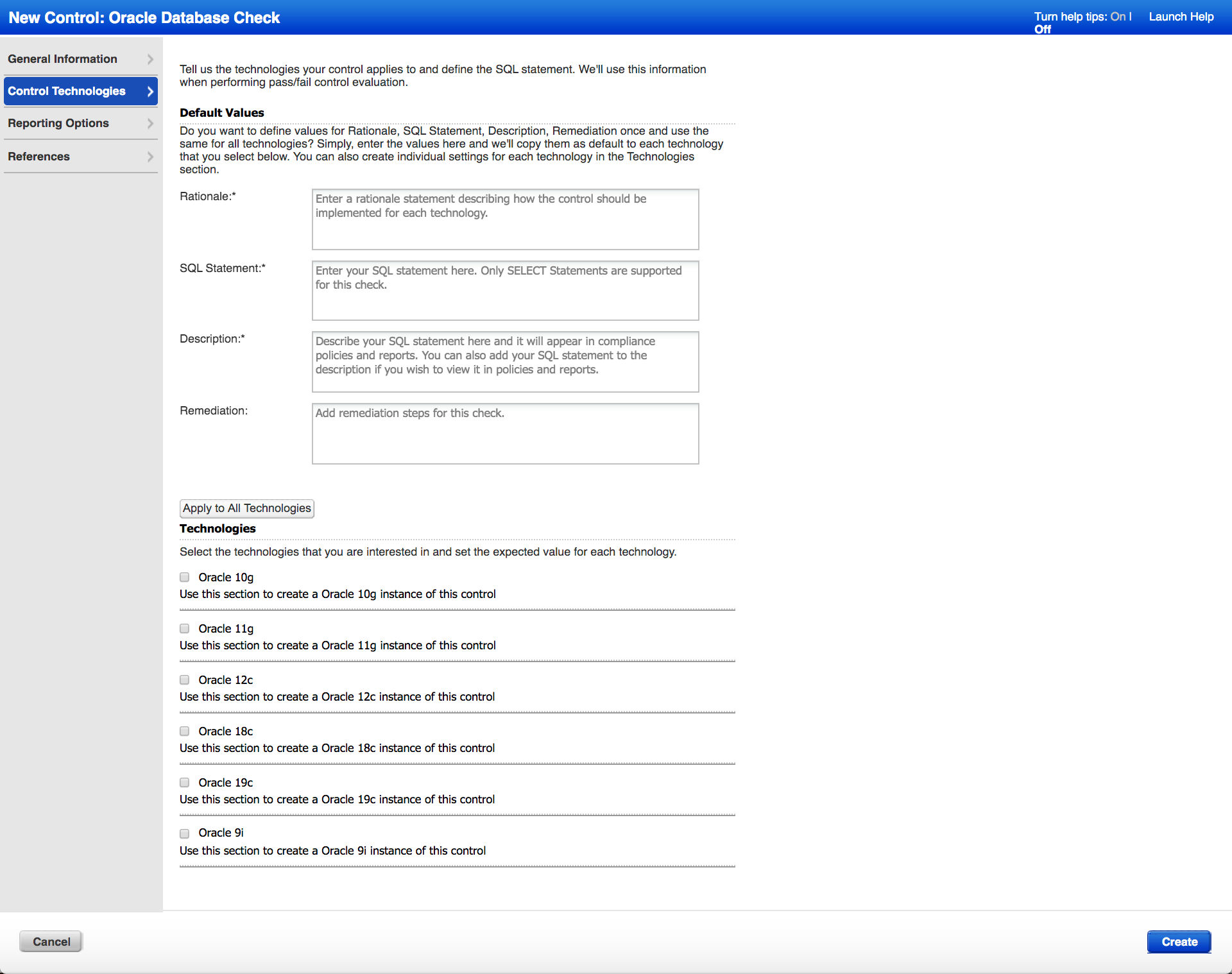
Qualys PC recently expanded its support for controls and has added the flexibility of the user-defined controls (UDCs) for databases. UDCs, as opposed to the system-defined controls, are the controls that customers can create on their own. They allow customers to easily extend the Qualys controls without complex programming to meet unique internal needs and to assess databases on supported platforms. UDCs can be added to compliance policies and subsequently be included in compliance reports just like system provided controls. UDCs are supported on Windows as well as Unix platforms for databases.
Following are the two types of user-defined controls for databases that Qualys supports:
- MS SQL Database Check
- Oracle Database Check
UDC Example
When you use database UDCs, for each control, provide an SQL statement to execute on your databases for obtaining the expected output.
For example, to check the status of the ‘BadPasswordCount’ for the SQL Server authentication login accounts, use the following SQL query:
select p.name, p.is_disabled, cast LOGINPROPERTY p.name,'BadPasswordCount' AS varchar 10 as BadPasswordCount from sys.sql_logins p where p.name NOT LIKE '##%%'
Type: Select sub query with CAST function
DB results:
| Name | Is_disabled | BadPasswordCount |
|---|---|---|
| as1 | 1 | 8 |
| QUALYS_SCAN | 0 | 0 |
| bulump | 0 | 0 |
| sa | 0 | 0 |
| ahu_scan | 0 | 0 |
| test | 0 | 0 |
| test123 | 0 | 0 |
| mlqa | 0 | 0 |
Conclusion
Being well acquainted with the fact that enterprises usually do not have the visibility into the vulnerabilities that their databases are exposed to, Qualys has efficiently devised its Policy Compliance solution with granular details. The primary aspect of maintaining a robust and secure enterprise lies in gaining visibility. Qualys helps enterprises gain deeper knowledge into the current state of their database security with the help of the extensive library of controls and policies. With an extensive support for database instances on a wide range of platforms, CIS-certified policies, system-defined and user-defined controls, Qualys ensures that your databases are never exposed to security vulnerabilities and threats.